Level Up Your Security Culture
Huntress SAT isn’t built to simply check a box. It’s designed to elevate your security culture and equip your employees with the knowledge to thrive in the face of phishing attacks.
Simulated Phishing Training for Employees
Phishing accounts for over 90% of successful cyberattacks. Despite this, many organizations continue to run checkbox-style awareness programs that employees forget as soon as they exit the office doors.
Huntress takes a different approach. Our phishing training for employees is built by the same security experts who actively hunt threats across millions of endpoints and identities for 100k+ organizations worldwide. These are people who know exactly what modern phishing attacks look like because they’re stopping them every single day.

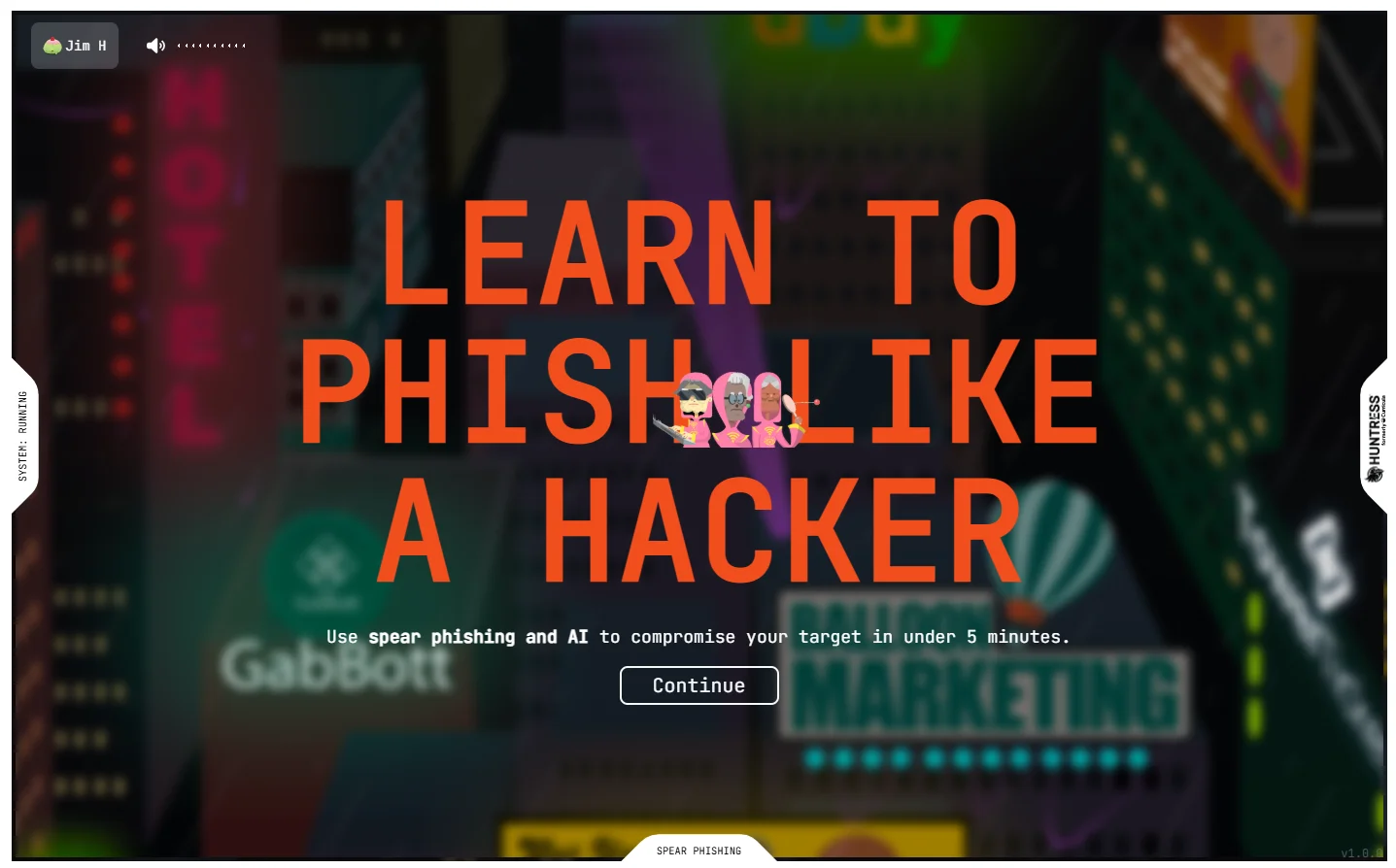
Want to see what our phishing training actually looks like? Here's a free preview of one of our spear phishing simulations—no strings attached.
Simulated phishing training tests whether employees will click, download, or submit credentials, and routes anyone who falls for it into an immediate coaching moment.
The challenge for small and mid-sized businesses is that most phishing simulation software was built for enterprise security teams with dedicated staff to manage campaigns. Huntress closes that gap with two delivery options:
Fully managed phishing: Huntress security experts design, schedule, and run your phishing simulations end-to-end. You opt in, your employees start getting tested, and your team gets clear reporting, all without lifting a finger. This is perfect for MSPs and lean IT teams who need enterprise-grade employee security awareness without the operational overhead.
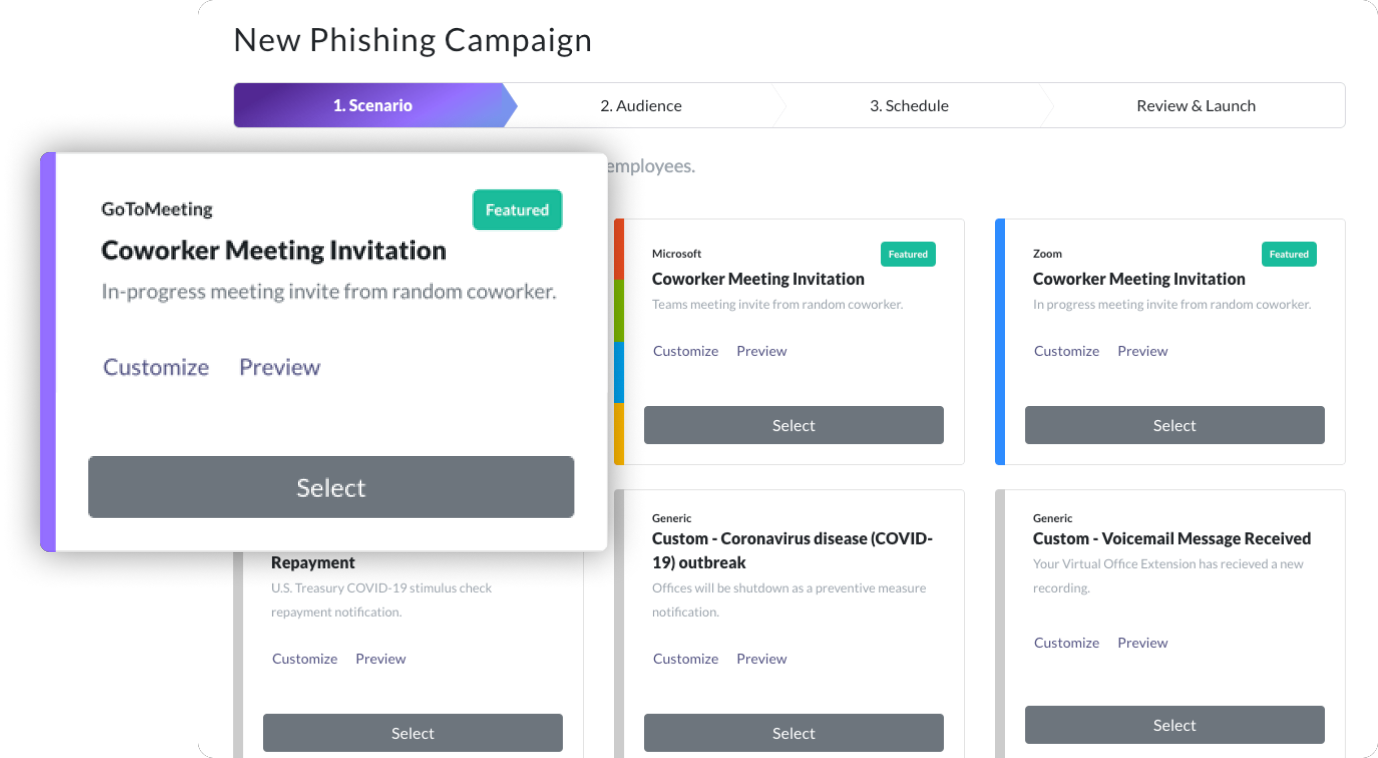
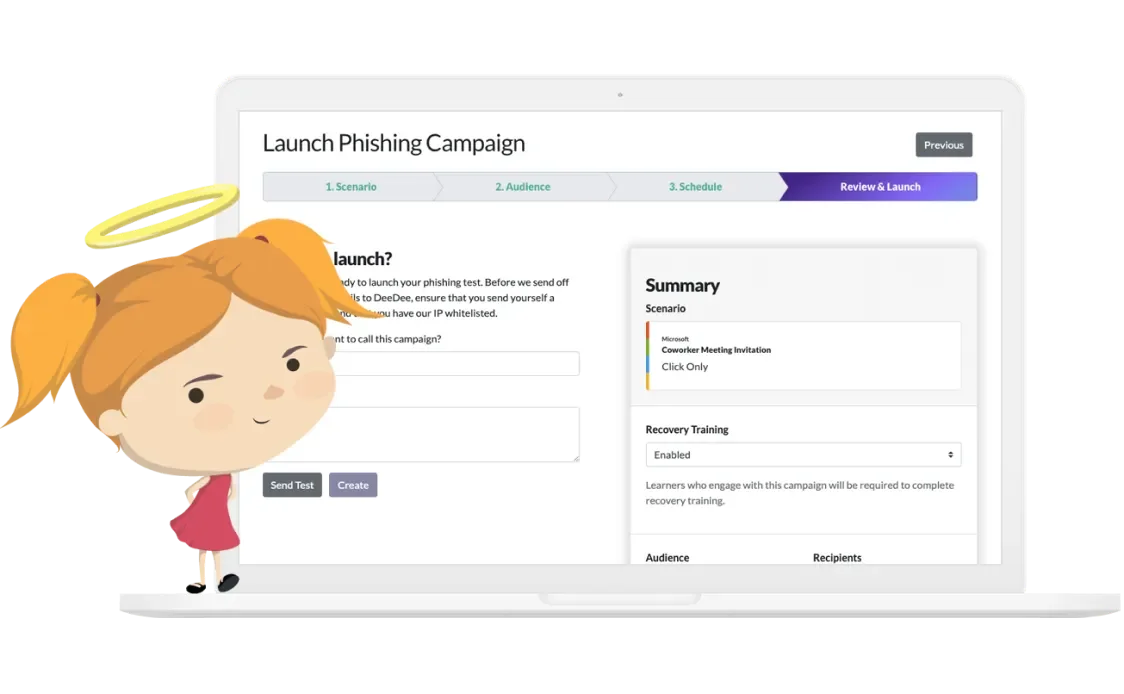
Self-service phishing: For organizations that want hands-on control, our self-service interface makes it easy to launch your first phishing simulation in minutes. Choose scenarios, define your audience, set a schedule, and let automated reporting do the rest.
Both options draw from the same library of scenarios built by Huntress threat researchers that include scenarios pulled from real attacks, not recycled templates.
One of the most common questions we get from organizations evaluating anti-phishing programs: What results should I expect from phishing simulations?
Huntress research shows how far we still have to go:
Taken together, these stats show that phishing and security awareness programs can genuinely change behavior—but only when they’re designed to reduce human risk in the real world, not just check a compliance box.
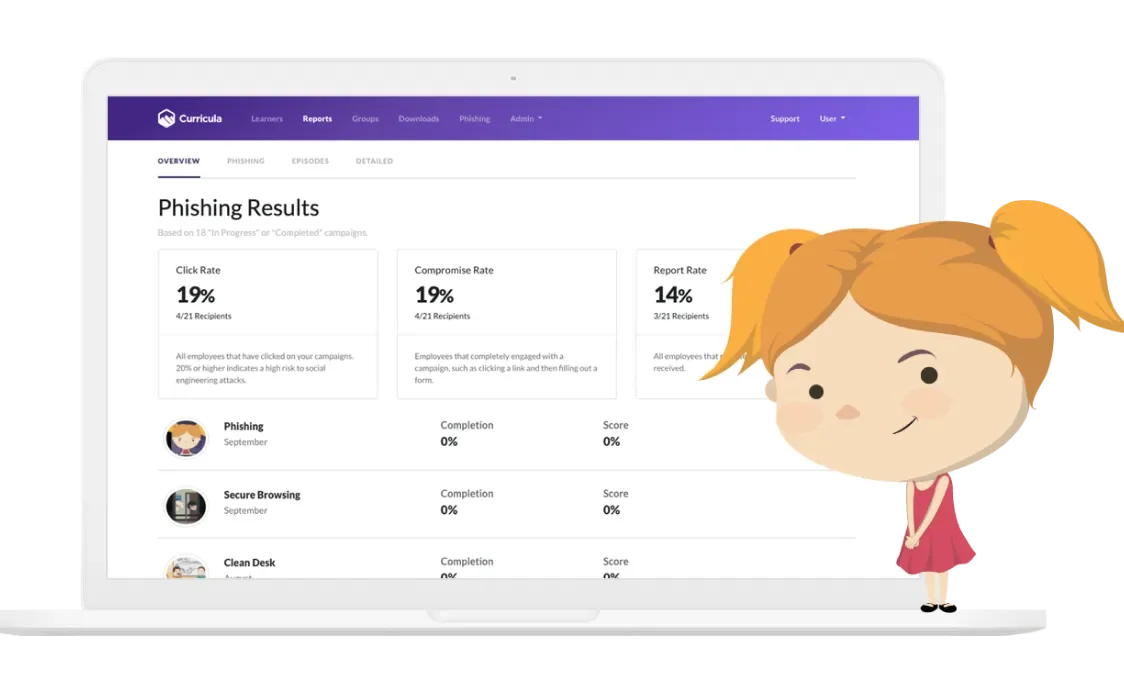
Key metrics Huntress tracks include:
Click rate: Percentage of employees who clicked the simulated phishing link.
Report rate: Percentage who recognized and reported the phish (a more valuable leading indicator than click rate alone).
Repeat offender rate: Employees who click across multiple campaigns may need additional training intervention.
Time-to-report: How quickly your employees flag suspicious emails once awareness builds.
Automated reporting with Huntress provides this intelligence at the campaign level, allowing admins to view trends over time, pinpoint high-risk departments or users, and show tangible risk reduction to executives or compliance auditors.

A common mistake many organizations make with phishing simulation is running the same scenarios on a loop. When employees see the same fake "IT department password reset" email every quarter, they're learning pattern recognition, not phishing awareness.
Huntress security experts continuously publish new simulated phishing scenarios inspired by active threats observed across our managed customer base. If a new business email compromise (BEC) tactic is circulating, or a credential-harvesting campaign is targeting a specific industry, your employees could see a version of it in training before they see it in their actual inbox.
Outside of simulations, Huntress also provides phishing defense coaching right when it matters most—after an employee clicks. Unlike having to sit through another long training module, employees are coached in context on what was suspicious about that email and how to identify similar attacks going forward. This “learn while you need it” methodology is far more impactful than having employees sit through passive, watch-this-video trainings.
The coaching style keeps things light and not punitive, so employees actually look forward to the next simulation.

What makes phishing simulation better for security awareness? Repetition and feedback. More accurately, phishing simulation becomes better security awareness when your simulation results are linked to valuable coaching, and when your reporting provides actionable insight instead of endless click reports.

Reporting from Huntress is built around empowering decisions, not recording activity. We automatically remind employees who clicked on a simulation lesson, reinforcing the teachable moment without your IT staff having to follow up manually. Campaign reports provide leadership with visibility to risk posture by department, role, or individual, all essential for demonstrating compliance to HIPAA, CMMC, SOC 2, or any other regulation or cyber insurance requirement.
Simulated phishing training is one of the most effective ways to reduce human risk and build a security-conscious culture. By combining realistic scenarios with actionable feedback, your employees can learn to spot and report threats before they cause harm.
Our security awareness training best practice is monthly simulations, at a minimum. Additional role-based campaigns are suggested for high-risk groups such as finance, HR, and Executive Assistants. Huntress Managed Phishing automatically schedules these, so you will never miss a month.
The most common mistakes include running the same scenarios repeatedly, launching simulations without any follow-up coaching, choosing overly punitive approaches that damage employee trust, and failing to track report rates alongside click rates. Many organizations also underestimate how quickly threat actors evolve their tactics.
Yes. Huntress allows you to segment campaigns by department, role, or risk profile so that your finance team is tested on wire transfer fraud scenarios while your general staff receives credential phishing simulations. Customization is available through self-service options.
Huntress tracks user activity across campaigns. This includes click history, reporting behavior, and repeat offenses. Admins can view this data to pinpoint users who may require additional training or awareness initiatives.
Yes. Huntress reporting and documented training records support compliance with HIPAA, CMMC, SOC 2, and other frameworks needing evidence of ongoing security awareness training.


