The Shai-Hulud NPM worm is a shifting supply chain attack that exploits developer credentials to compromise hundreds of packages in the Node Package Manager (NPM) registry, affecting major organizations like Postman and Zapier. Initially in September 2025, the first version operated during the post-install phase, harvesting credentials such as GitHub PATs, NPM tokens, and cloud API keys, then exfiltrating them to attacker-controlled endpoints or public repositories while propagating by injecting malware into other packages maintained by victims. However, in the last week of November, a new variant, Shai-Hulud 2, was released, and it has evolved to execute in the pre-install phase for broader impact. It currently incorporates obfuscated JavaScript disguised as Bun installers, cross-platform support including Windows, and enhanced persistence via GitHub Actions backdoors, specifically self-hosted runners and workflows that allow code execution.
Key differences include a shift from pure theft to destructive elements, like wiping home directories upon failure, and more sophisticated exfiltration using cross-victim repositories, which has amplified the campaign's scale to over 700 packages and 25,000 malicious repositories and counting.
New adaptations in the worm show increasing sophistication, including timing changes to evade detection, what appears to be AI-assisted obfuscation, multi-cloud SDK bundling for privilege escalation, and environment-aware execution in CI/CD pipelines. Indicators of Compromise (IoCs) encompass specific file hashes (e.g., SHA1 for bun_environment.js: d60ec97eea19fffb4809bc35b91033b52490ca11), artifacts like cloud.json and discussion.yaml, unexpected GitHub repos with "Sha1-Hulud" themes, and domains such as webhook.site. As of November 26, 2025, activity persists and we’re still seeing creation of new repositories, despite mitigations, that are transitioning to private repos advertising unrelated AI services, exposing valid secrets from hundreds of entities, and enabling potential follow-on threats like ransomware.
Cybersecurity teams should prioritize dependency auditing, credential rotation, development dependency cooldown integration, and tools like Semgrep for ongoing defense against this evolving open-source ecosystem risk.







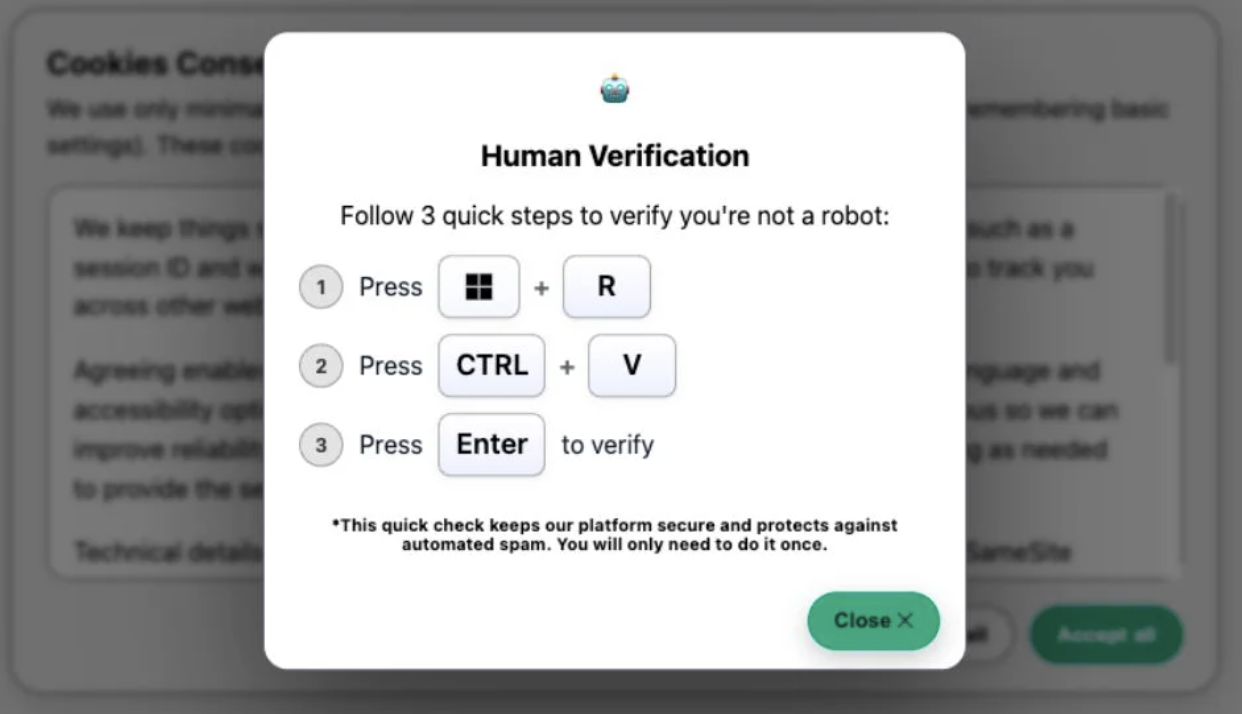 The “human verification” ClickFix lure
The “human verification” ClickFix lure