Sharing and reusing passwords is one of the easiest ways hackers can gain access to your online accounts. And some people aren’t making it any harder for hackers.
A Forbes Advisor survey found that 47% of users actually reuse their passwords across up to four different accounts.
Now, we’ve all heard some wild stories about poor password hygiene or the places people keep their passwords. But what are the worst offenders of them all?
We took to LinkedIn and Slack to ask the Huntress team and others to share their wildest answers for the best places to store your passwords (WRONG answers only).
People across the infosec and cybersecurity community chimed in to share their jokes and some real-life horror stories. Our team rounded up the best answers of where to NOT store your passwords. Enjoy!
Here are the top 10 worst places to store a password
1. Make the password the same as your username
One less thing to remember, right?
2. Tattoo your password somewhere. Then update it frequently.
Tattooing your password was a surprisingly common (and odd) answer.
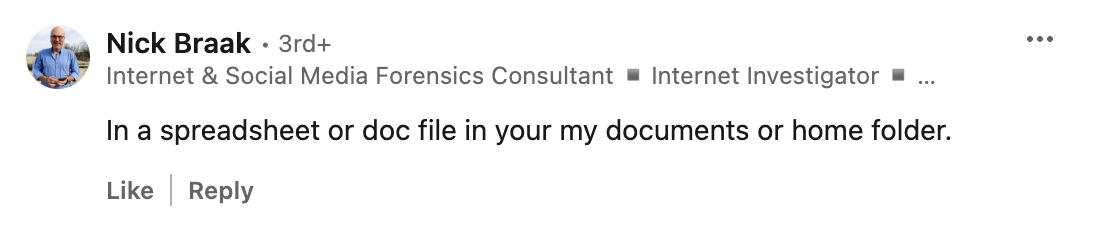
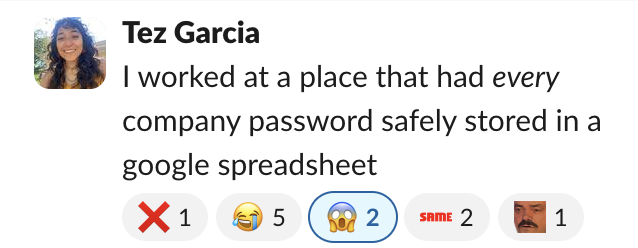
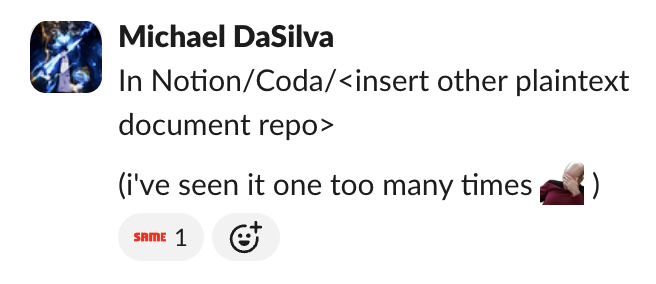
3. In a spreadsheet, doc, or .txt file
Actually, users saving plaintext passwords to their desktops is one we see quite a lot.
4. Featured in the background of a video call
With so many video calls these days, watch out for what’s in your background!
5. Store your password in a public directory
It's a big engineering slip to commit your password to GitHub. #fail
6. The classic: put your password on a sticky note.
It’s classic for a reason. Because it still happens.
7. Another classic: stored with trustworthy royals.
8. Somewhere safe in your office or home.
Basically, wherever you’d store some spare cash.
9. Or put it on your favorite mug.
Just make sure it’s dishwasher safe.
10. If all else fails, just use the same simple password for everything.
While these responses were hilarious, the reality is far less funny. Password sharing and password re-use are just some of the many ways malicious hackers can gain easy access to your online accounts.
The importance of multi-factor authentication (MFA) can't be understated. With MFA turned on, a hacker will have a difficult time trying to access your account with just your password.
Don’t let yourself or your users become another statistic (or horror story). Huntress Managed Security Awareness Training (SAT) makes learning cybersecurity best practices both engaging and effective. Through lessons designed by cybersecurity experts and brought to life by award-winning animators, your team will gain the knowledge they need in a fun and memorable way. They'll learn the importance of not reusing passwords, how to spot phishing attempts, recognize social engineering scams, and much more—making security second nature.
Huntress Managed SAT
Password Simulation
Knowing the worst habits is step one. See how Huntress SAT trains employees to actually break them.
Check out our series of memorable, story-based episodes and see for yourself how exciting learning with Managed SAT can be.