There are lots of myths surrounding macOS and Apple devices. It's time to set the record straight. Read on as we break down five of the most common macOS myths.
1. Macs Don't Get Viruses
Back in the early 2000s, Apple released a series of television commercials—the "I'm a Mac, I'm a PC" ones, which featured a person, as the depiction of "Windows,” plagued by "viruses."
At the time, this wasn't wholly inaccurate, as macOS (or OS X then) hadn't seen much outside of some potentially unwanted programs (PUPs). This sowed a sentiment into the minds and hearts of many early Mac adopters that their machines were impervious to malware, or even adware.
Fast-forward 20 years, and unfortunately, the same still rings true for many users. They think their devices are safe strictly because it's an Apple computer. However, what started as a few PUPs and some generic adware in the early-to-late 2000s has given way to nation-state-sponsored malware, advanced infostealers, and spyware, like LightSpy. And this malware has even started leveraging Apple-specific tools and languages.
Since Apple stopped pre-installing the Python programming language on macOS, the lure of leveraging a different language has increased. Because of this, we've observed an uptick in threat actors using AppleScript, a scripting language that comes pre-installed on every new Mac. Although it's ugly to read, uncommon, and not enjoyable to write, having a scripting language ready and available for use makes it a great opportunity.
Although Apple sowed the seeds of doubt years ago that their devices are impervious, Macs can indeed get viruses.
2. macOS Is (Inherently) More Secure than Windows
Apple has gone to great lengths to make their devices secure. I could talk ad nauseam about Apple's built-in security features, such as Gatekeeper, TCC, or XProtect, which in and of itself can lead to other hardships like management and such. But do these features truly make it more secure than its Windows counterpart?
It's hard to say, as the nuances between macOS and Windows are vast. Additionally, even though 57% of users believe that malware doesn't exist on macOS, 50% of users have been affected by it.
Even with the built-in macOS security features, many of the past sentiments have led to a false sense of security, making users more susceptible to attacks via phishing, fake browser ads and extensions, cleaning software, etc. As we see macOS adoption across enterprises increase, the devices become a more viable target for threat actors.
3. Ransomware Is a Large Threat to macOS
Although there’s been lots of talk about ransomware and the threat of ransomware on Windows, we just haven’t seen the same push to get ransomware executed on macOS.
We've seen a short laundry list of ransomware that’s attempted to execute on macOS, but nothing has successfully run.
If we look strictly at VirusTotal, we’d be led to believe that ransomware is running rampant on Macs, namely the EvilQuest/ThiefQuest ransomware, which was first uncovered in mid-2020. However, if we dig deeper into the details of the surging numbers of supposed EvilQuest hashes seen in the wild, it appears that, due to the encryption of the ransomware, the VirusTotal macOS sandbox was essentially being "fork" bombed. The thought was that there was a massive ransomware attack on macOS, but it turned out to be a bug.
We can see other attempts to deploy ransomware to macOS, such as the LockBit or Turtle ransomware, but again, with the addition of Apple's TCC checks, most attempts to encrypt user data are rendered moot.
4. macOS Faces the Same Threats as Windows
With the differences and nuances of the platforms come the differences and nuances of the threats. With scripting languages that only run on macOS, like AppleScript, it means that detections have to target Apple-specific threats.
Where Windows sees much more in the way of nation-state activity, macOS observes items like PUPs, adware like search engine hijacking and clickbait, or Shlayer, which leverages social engineering techniques to get the user to override Gatekeeper to execute. So though we see some similarities, they’re few and far between—as macOS and Windows face vastly different threats.
5. Enterprises Only Run Windows
Back in the day, most enterprise businesses only used Windows. Although the Windows operating system is still the primary driver for the vast majority of businesses, macOS adoption has been increasing rapidly, to where now 22% of devices in the enterprise are running macOS.
Over the last handful of years, immediately following the pandemic, there was a drastic increase in working from home (WFH). The WFH culture spurred BYOD, or Bring Your Own Device, which allowed employees to use their personal machines for work. This typically meant enrolling their device with their work MDM, or at the very least a VPN, so that they could log into their employer's Slack instance and use other business resources. Simultaneously, this meant that employees had more choice over what devices they used, so in turn, they picked the operating system that they were most familiar with. So instead of being forced to use a Windows machine even though macOS was their preference, they could now use Macs. Between WFH, BYOD, and general business adoption, the use of Macs in the enterprise is increasing at roughly 20% YoY.
This increase is primarily felt in specific fields, such as education, the creative arts, software development, or the entertainment sector (e.g., photography, videography, music production, film/TV). All of this to say, now 22% of all business devices are running macOS. Employees are getting more choices in what devices they use, and they're choosing macOS.
So What Does This All Mean?
As we see macOS adoption increasing, it’s important to address the common misconceptions that come with the platform. Some of the misconceptions reach back 20 years, while others have surfaced in the last few, but the important point to remember is that the macOS platform differs from Windows in many ways. You can take solace in Apple’s approach to end-user privacy and security, but that doesn’t mean it’s impervious. As always, keep your software up to date, patch early and patch often, use a reliable security solution on your endpoints, and leverage discretion regarding suspicious emails or links.
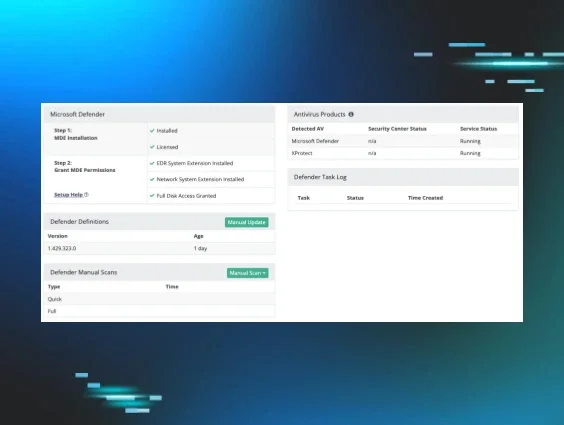
Put simply, macOS needs security too. Huntress Managed EDR for macOS can help. Start your free trial today.