Phishing Defense Coaching: From Compromise to Crushing It
Ph*sh happens. It’s the recovery that counts. Phishing prevention tools are everywhere. But here’s the harsh truth: most aren’t built for IT folks like you, managing users with widely different skill levels. That’s where we’re different: our tech is purpose-built for admins managing the fallout so users don’t just “get trained”—they actually get better.
Phishing happens, and it’s not a matter of “if,” it’s “when.” And when the fun ends, the work lands on you, usually on your weekend. But these slip-ups can actually be goldmines for learning. With the right recovery training, you flip the script on phishing recovery training.
Here’s what makes Huntress different and why you’ll want to watch:
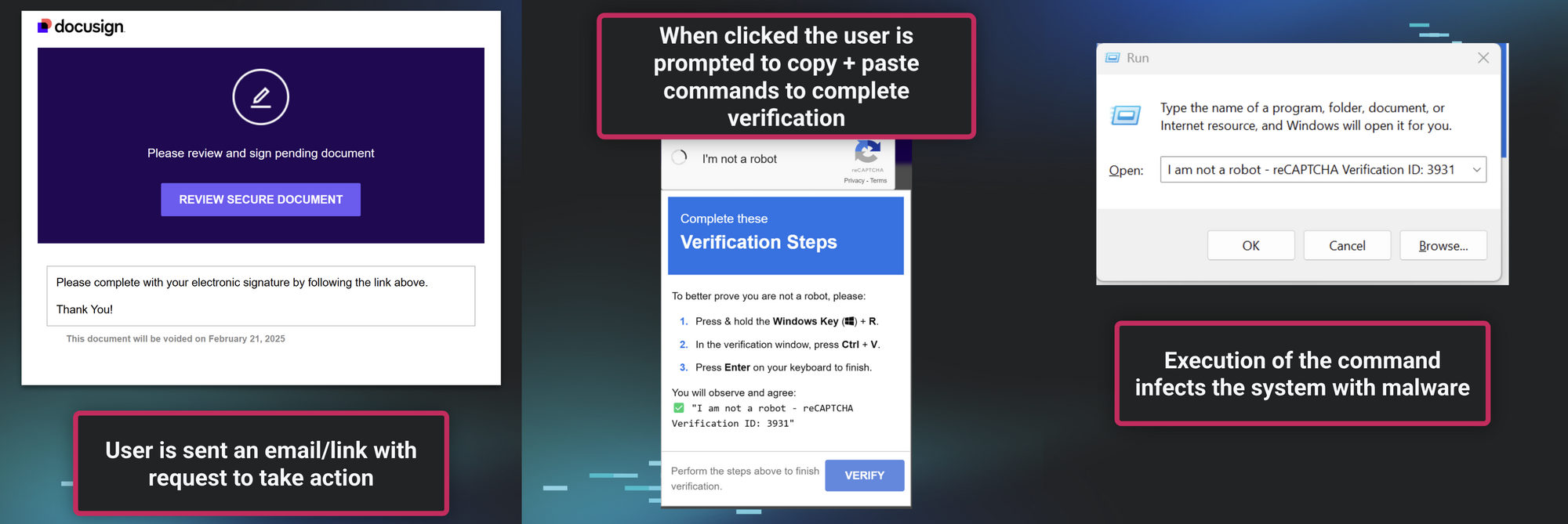
- Fake CAPTCHA Lure Demo: We are pulling back the curtain on our latest phishing scheme—one so clever, even savvy users won’t know what phished them.
- Phishing Defense Coaching: Clicked the link? Made a mistake? No shame. We’re humans, not bots. We are here to help educate and rewrite user behavior.
- Redefining Recovery Training: Boredom is the real enemy. Our approach hooks learners with hands-on, impactful lessons that actually stick.


Watch the Webinar