DragonForce, a recent but virulent ransomware group formed from ex-members of RansomHub, suggested forming a “Ransomware Cartel” with LockBit and Qilin on the dark web. Shortly after, LockBit seemed to accept the offer, which allowed the groups to coordinate and share resources.
During 2025, ransomware-as-a-service (RaaS) competition has been extremely volatile. The rise and fall of groups has been dramatic. Groups’ payouts have gone up even higher to reflect this, with LockBit offering the highest at 90%, their top tier.
With the recent unification of DragonForce, LockBit, and Qilin, we believe this could lead to more coordinated efforts and unified attack strategies. For instance, LockBit, which is believed to have a very reliable pipeline of Initial Access Brokers, could share that privileged access to help Qilin and DragonForce gain access to a broader set of targets. More importantly, LockBit has proven that its infrastructure is extremely robust and operates even after takedowns. With the latest release, this will be LockBit’s fifth major restructure. By offering the other groups access to their infrastructure, money laundering, and financial systems, it could help make them more resistant to takedowns from law enforcement.
Similar to illicit cartels in Mexico, the current ransomware landscape has been fighting with each other at an escalating pace this year. Groups like BlackLock have been targeted by other groups, including DragonForce. Chatter amongst the dark web has indicated smaller groups might be looking to join forces as well, making the landscape extremely dynamic and unpredictable.







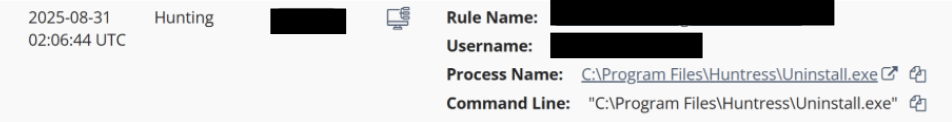 Threat actors attempting to uninstall the Huntress agent
Threat actors attempting to uninstall the Huntress agent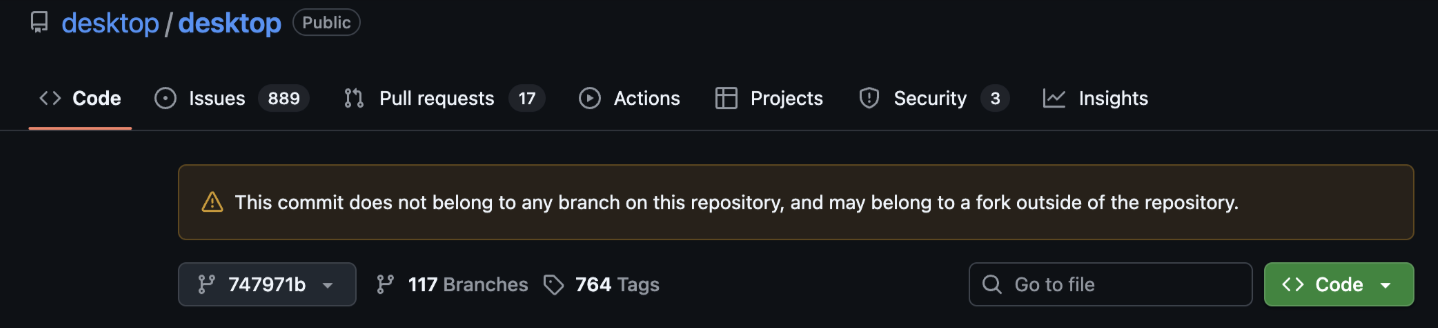 GitHub’s warning that the commit does not belong to the repo’s branch
GitHub’s warning that the commit does not belong to the repo’s branch
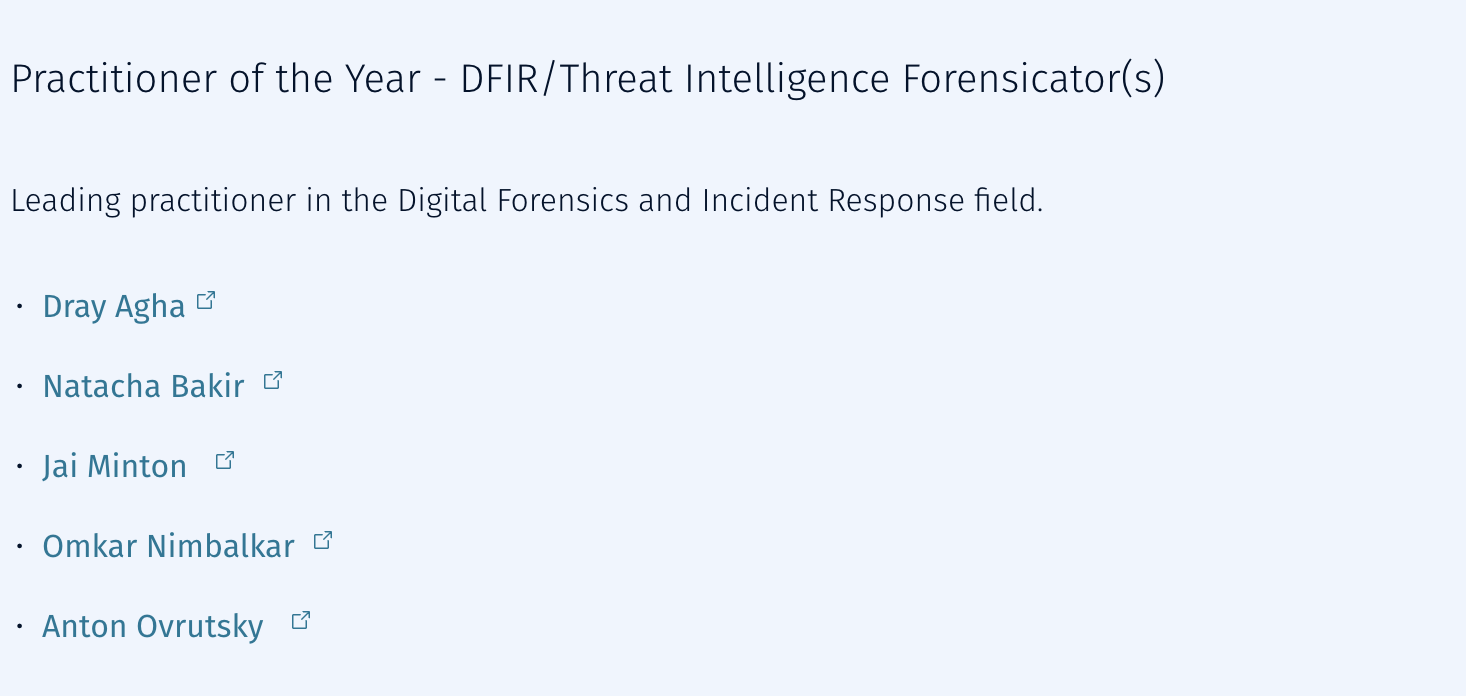 Huntress dominated this year’s SANS Difference Makers Awards
Huntress dominated this year’s SANS Difference Makers Awards
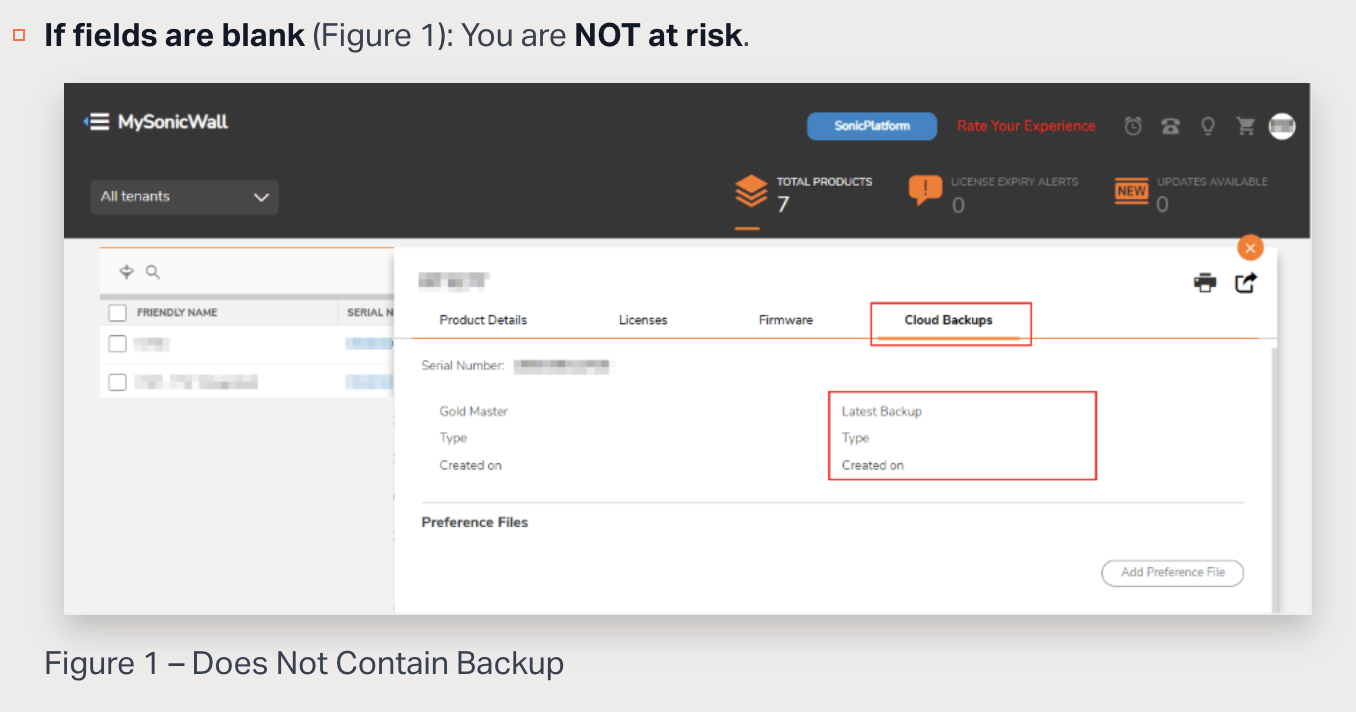 SonicWall guidance on checking for Firewalls with preference files backed up in MySonicWall.com
SonicWall guidance on checking for Firewalls with preference files backed up in MySonicWall.com

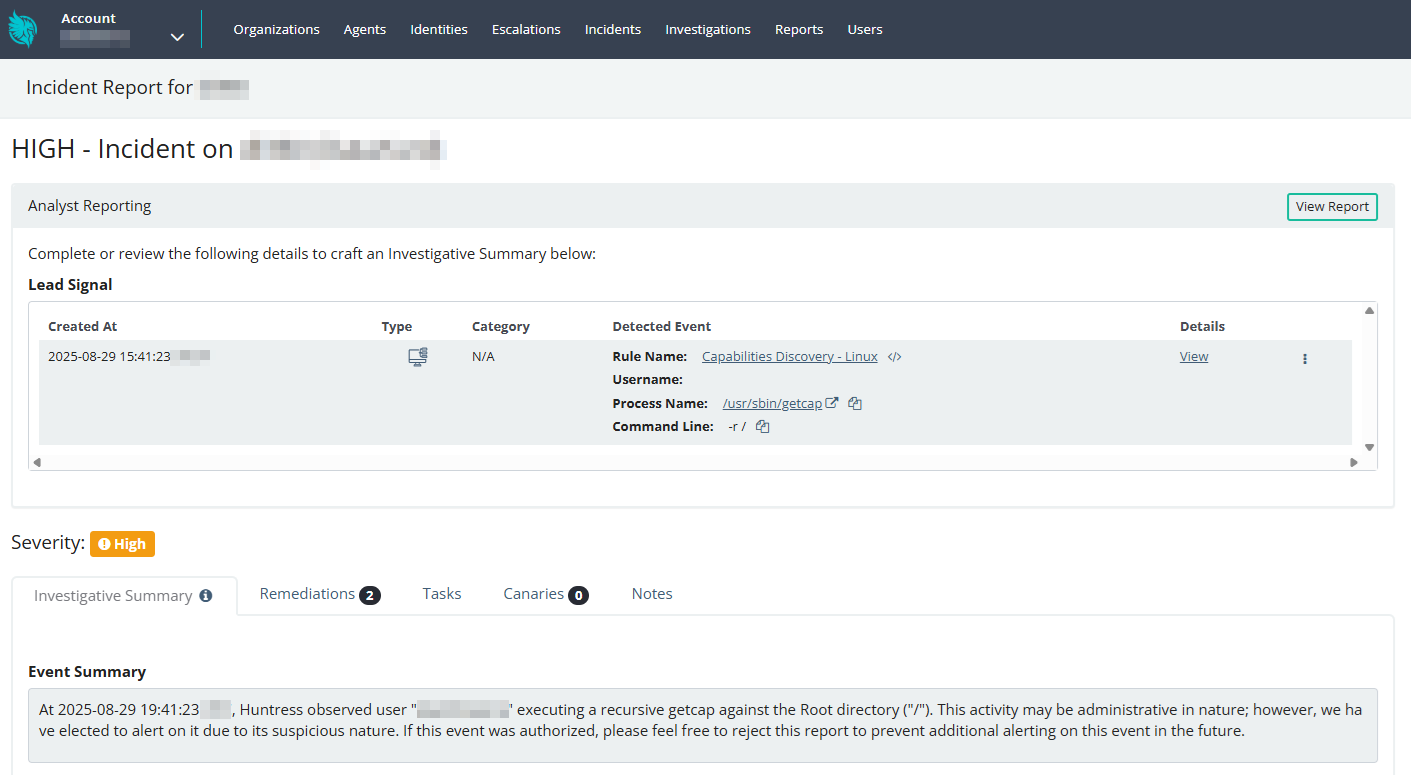 Incident report for an EDR detection on Linux
Incident report for an EDR detection on Linux