IT and security teams are increasingly spending more on security awareness training (SAT). But is this investment improving SAT effectiveness?
Our latest research report, Mind the (Security) Gap: SAT in 2025, digs into the question of whether organizations are really getting the results they need from their increasing SAT spend. And the answers are…a little uncomfortable.
We surveyed over 500 admins and learners of SAT solutions across the market to get the real story on SAT. And what we found is a huge disconnect between what organizations think their training is achieving and the results they’re actually seeing.
Let's break down the cognitive dissonance.
The big budget, big problem paradox
Here’s the deal: Security teams are throwing more money at SAT than ever before. A whopping 93% of SAT admins say their SAT budgets have gone up in the last three years, and 83% say that securing additional resources for SAT is relatively straightforward. So if it’s easy to convince their leadership teams to give them more budget, you’d expect that they've been seeing improvements to their human risk levels, right?
WRONG!
During that same period, 94% of those same admins reported that security incidents caused by human error are on the rise. Even more telling, 62% admit their organization’s human risk exposure increased after rolling out a SAT program.
While correlation doesn’t equal causation, and we wouldn’t claim that SAT is actually making their security postures worse, it’s clear that increased investments in the same old SAT programs aren't producing the results these teams need to see. Something isn’t adding up.
Despite this, everyone seems pretty happy with the status quo. Over 90% of SAT admins and 88% of learners believe their current SAT program is effective. This could mean we’ve completely lowered our standards for what an effective SAT program could be, or it shows that teams have unknowingly developed a dangerous false sense of security thanks to ineffective training.
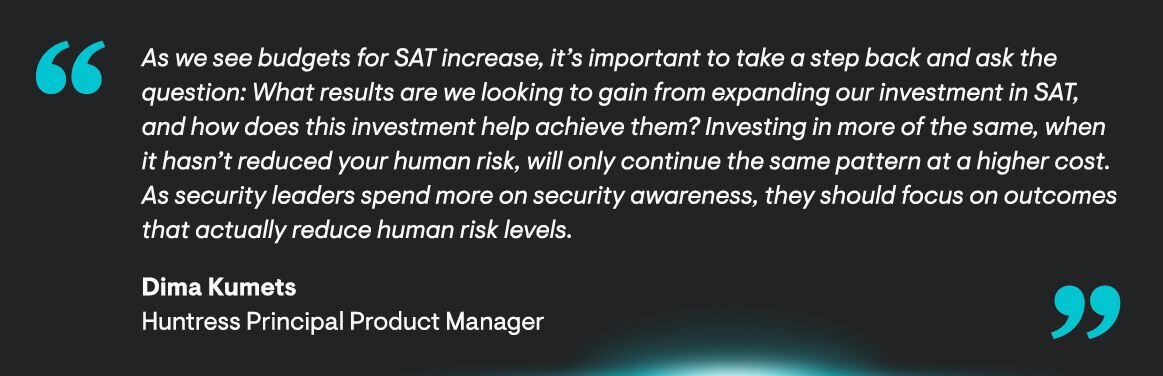
As our Principal Product Manager for Managed SAT, Dima Kumets, puts it, “Investing in more of the same, when it hasn’t reduced your human risk, will only continue the same pattern at a higher cost. As security leaders spend more on security awareness, they should focus on outcomes that actually reduce human risk levels.”
Confidence is high, but reality bites
Another major finding from the report reveals yet another gap between perception and reality: while admins and learners are confident in SAT effectiveness, the data tells a different story.
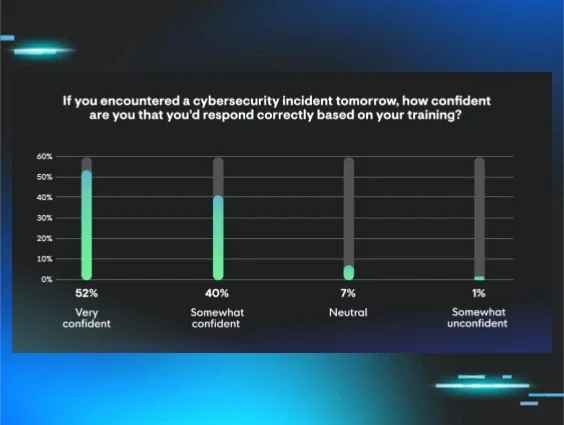
For instance, 86% of employees claim their SAT has helped them recognize or avoid a real threat. And 92% feel confident they'd respond correctly to a cybersecurity incident. That sounds great on paper.
But, as the Verizon 2025 Data Breach Investigation Report showed, 60% of all breaches still involve the human element. So if everyone is so well prepared, why are these human-related incidents still so common?
“Confidence after training does not always translate into real-world readiness," says Truman Kain, Principal Product Researcher at Huntress. "Right after completing a SAT module, employees are in a clear state of mind and actively thinking with a security lens. But attackers succeed by hitting at the right time, when someone is tired, distracted, or under pressure.”
This misplaced confidence is a huge problem. Legacy SAT programs fail to keep up with modern threats or instill a lasting sense of healthy suspicion in learners. Instead, learners walk away from training thinking they’ve learned an exhaustive list of threats to watch out for, not recognizing that hackers are always innovating. But tradecraft is evolving at lightning speed. The classic "Nigerian prince" email is a joke now because today’s threats are sophisticated, AI-powered, and hyper-personalized.
If the security training can’t keep up, it’s the learners who end up suffering the consequences.
The burden of "manageable" programs
So, what's causing this failure? A lot of it comes down to how SAT programs are managed.
While 95% of security admins say their program is "manageable," 61% are still spending 10+ hours a month on it. And the top challenge they face? Keeping training materials up to date. Doing so requires a capable (read: expensive) security practitioner to own the creation, curation, and delivery of the content. That’s a ton of time and resources (we’re talking thousands in payroll alone for a junior security analyst) spent managing SAT, when their talents could be better utilized on higher-impact security tasks. Not to mention the costs it takes to upskill and retain this highly sought-after security talent.
Most SAT programs aren’t even maintained by these security experts. Instead, they’re built by generalists who can’t keep up with the threat landscape and rely on stale, repetitive content. Training is often infrequent, and many organizations are still stuck on quarterly or even annual cycles. In the end, learners are left unprepared for the threats they're most likely to face today.
What’s the fix?
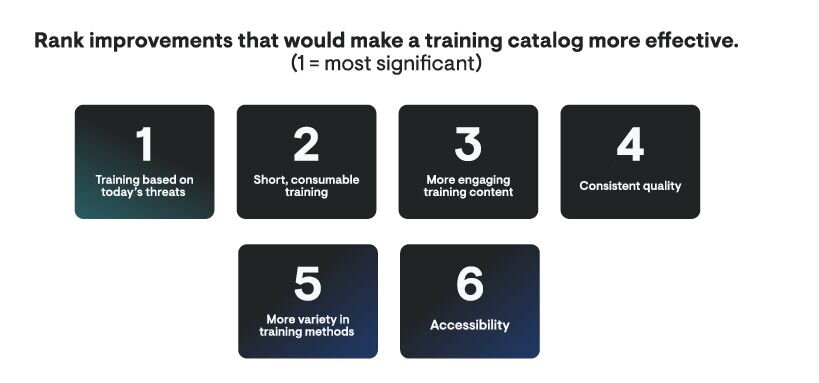
If legacy SAT is broken, what options do you have? Improving SAT effectiveness isn’t about ditching training altogether—it’s about making it smarter, more relevant, and less of a burden.
The future of SAT lies in a managed, expert-backed approach. This means:
-
Training based on real, modern threats: Content should be developed by security experts who are on the front lines, analyzing actual hacker tradecraft as it emerges.
-
Frequent, bite-sized lessons: Ditch the hour-long quarterly or annual snooze-fest. Short, engaging, and continuous training keeps security top-of-mind.
-
Interactive and personalized content: People learn differently. Effective programs use a variety of approaches, from hands-on experiences, realistic simulations, and video content that’s actually engaging.
It’s time to move beyond just checking a box for compliance and start focusing on what really matters: actually reducing human risk.
See the full picture
We've only scratched the surface here. The full report is packed with more data on the state of security awareness training and the path toward true human risk management.
Ready to see what else we uncovered? Download the complete Mind the (Security) Gap: SAT in 2025 report now.