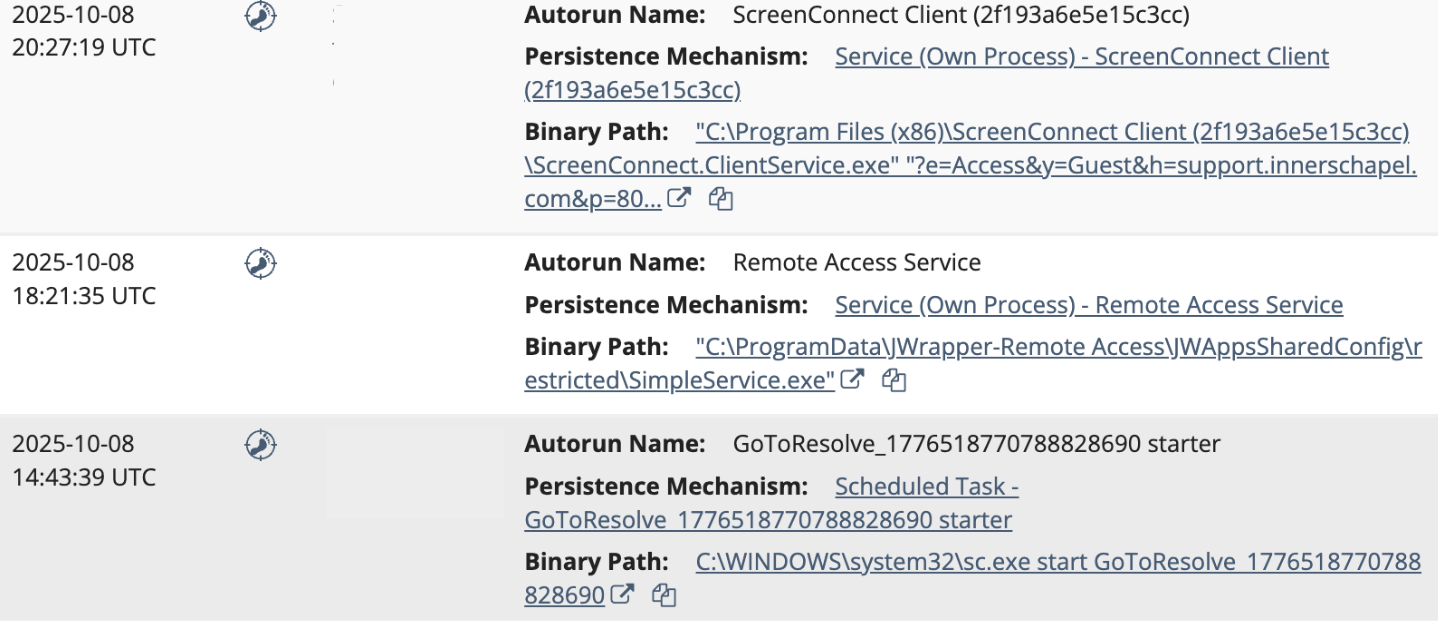
Threat actors have consistently used remote monitoring and management tools (RMMs) in their attack chains this year. But an interesting twist has recently emerged: threat actors use PDQ or GoTo Resolve initially and then deploy secondary RMM tools, like ScreenConnect or SimpleHelp. Deploying multiple RMM tools helps threat actors maintain longer term access, especially if the first tool is blocked. Below are a few examples we’ve seen recently:
- On October 7, an employee at a real estate company received a phishing email through Outlook, which led to them install
Open Revised Contract (2).exe. This executable file was actually a renamed GoTo Resolve instance signed by GoTo Technologies USA, LLC – which was then used to install the ScreenConnect RMM - In October, an employee at a car dealership executed the
OPENINVITATION.exefile, a rogue GoTo Resolve RMM installer. The threat actor then used their access via GoTo Resolve to install a rogue SimpleHelp RMM (SimpleService.exe) on the host. But it didn’t stop there: they then installed a malicious ScreenConnect instance, configured with the domainsupport[.]innerschapel[.]com







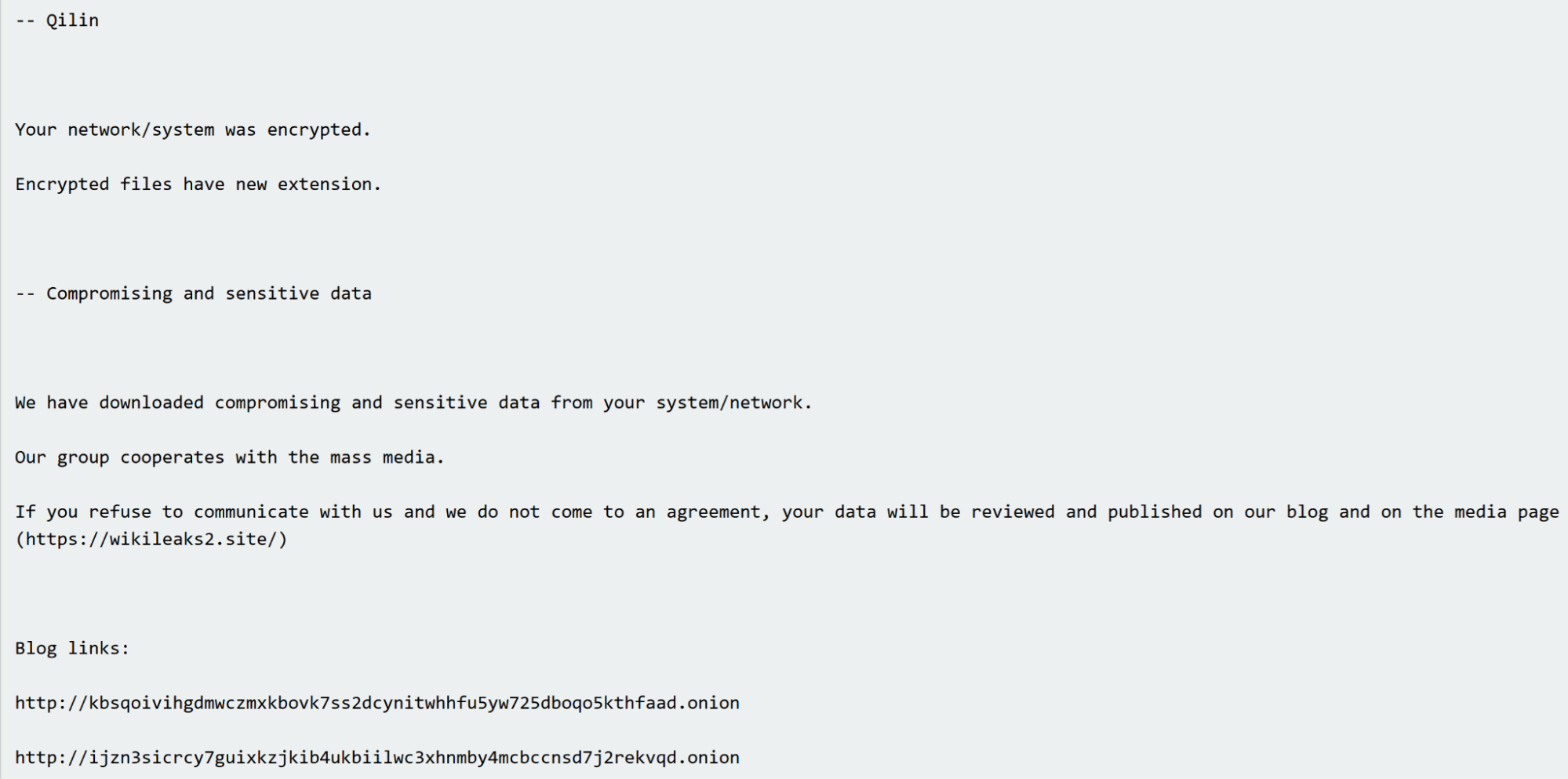 Qilin ransomware note
Qilin ransomware note


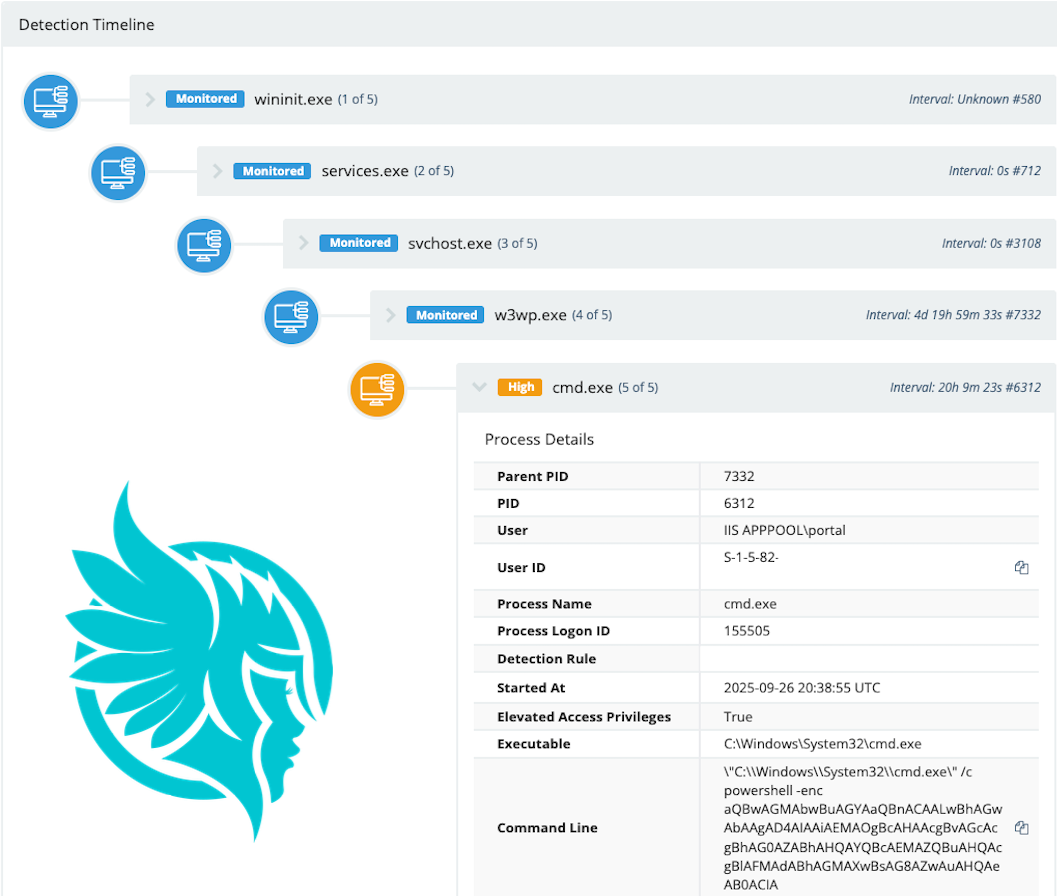 Detection timeline for observed exploitation activity
Detection timeline for observed exploitation activity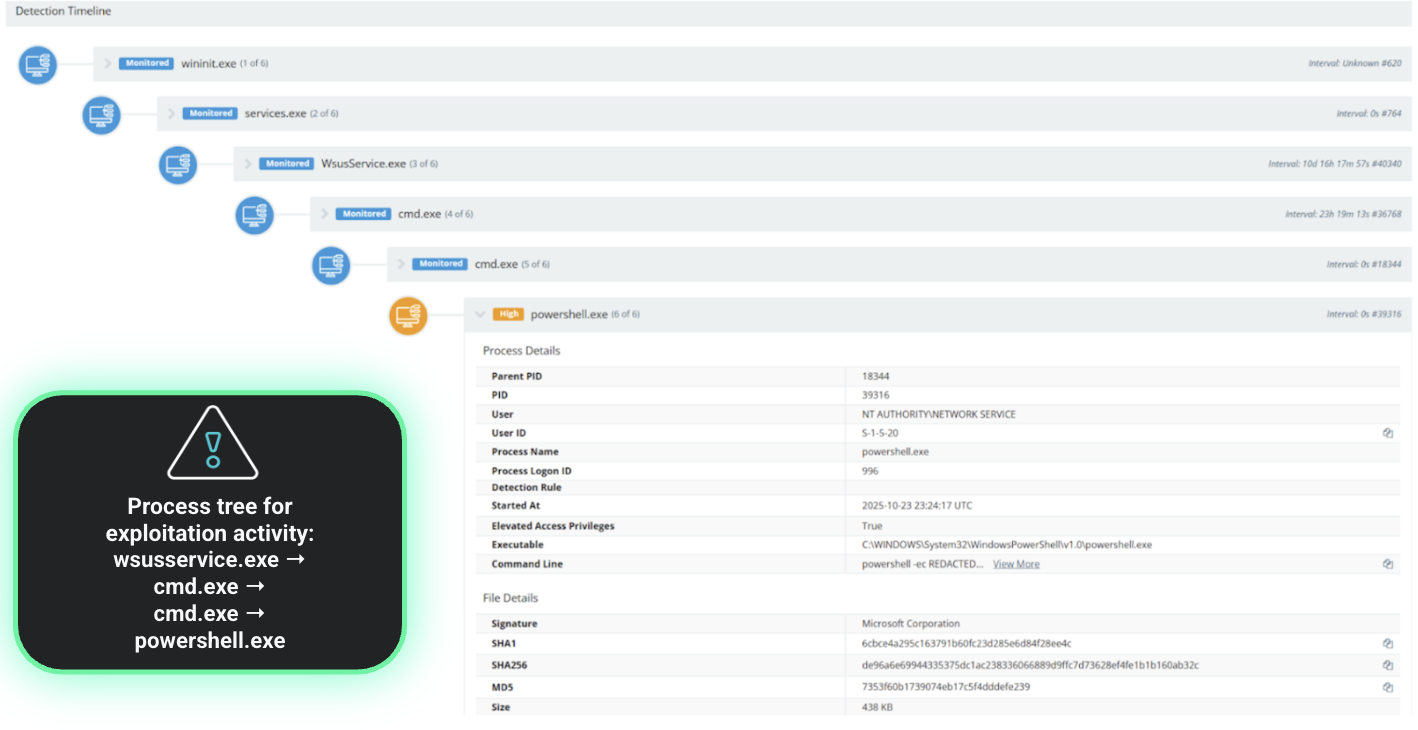 Process tree for the exploitation activity for CVE-2025-59287
Process tree for the exploitation activity for CVE-2025-59287
 A behind-the-scenes look at the design of the Economics of Cybercrime, from October’s Product Lab
A behind-the-scenes look at the design of the Economics of Cybercrime, from October’s Product Lab