What Is Pass-the-Cookie?
Written by: Brenda Buckman
Published: 3/18/2026



On This Page

Related Terms
Read more about What is an Adversary-in-the-Middle (AiTM) Attack?

Learn how AiTM attacks bypass MFA by stealing session cookies through proxy servers. Learn detection methods and defense strategies for this evolving threat.
Read more about What Is Session Hijacking? The Silent Threat: Bypassing MFA

Session hijacking allows attackers to bypass MFA by stealing session tokens. Learn how AitM attacks work and how to detect them before damage occurs
Read more about What is Cross-Site Request Forgery (CSRF)?

Learn about Cross-Site Request Forgery (CSRF), a common cybersecurity threat, how it works, and how to protect against it.
Read more about What is a Session in Cybersecurity? Explained
What is a Session in Cybersecurity? Explained
Read more about Cookie Logging Explained for Cybersecurity Pros & Cybersecurity Beginners
Cookie Logging Explained for Cybersecurity Pros & Cybersecurity Beginners
Read more about What Is Identity Resilience? A Security Explainer
What Is Identity Resilience? A Security Explainer
Read more about What is Dangling Markup?
What is Dangling Markup?
Read more about What exactly is a Token in Computers?
What exactly is a Token in Computers?
Read more about What Are IoCs in Cybersecurity and Why Do They Matter?
What Are IoCs in Cybersecurity and Why Do They Matter?
FAQs for Pass-the-Cookie
Pass-the-cookie is a session hijacking attack where an adversary steals an authenticated browser session cookie and uses it to access cloud applications as if they were the legitimate user—without needing a password or completing multi-factor authentication (MFA).
When you log in with MFA, your browser stores a session cookie that confirms authentication has already happened. Pass-the-cookie attacks steal that post-authentication cookie, so the attacker's browser presents it as already-verified. The application sees a valid session—no MFA prompt needed.
Pass-the-hash targets on-premises Windows environments by stealing NTLM password hashes to authenticate to internal systems. Pass-the-cookie targets cloud and SaaS applications by stealing web session tokens to hijack already-authenticated browser sessions.
Any SaaS application that uses cookie-based session authentication is at risk—most notably Microsoft 365, Google Workspace, Salesforce, and other web-based tools your team uses daily. Microsoft 365 is the most common target because of its widespread use and the value of email access for follow-on attacks like business email compromise.
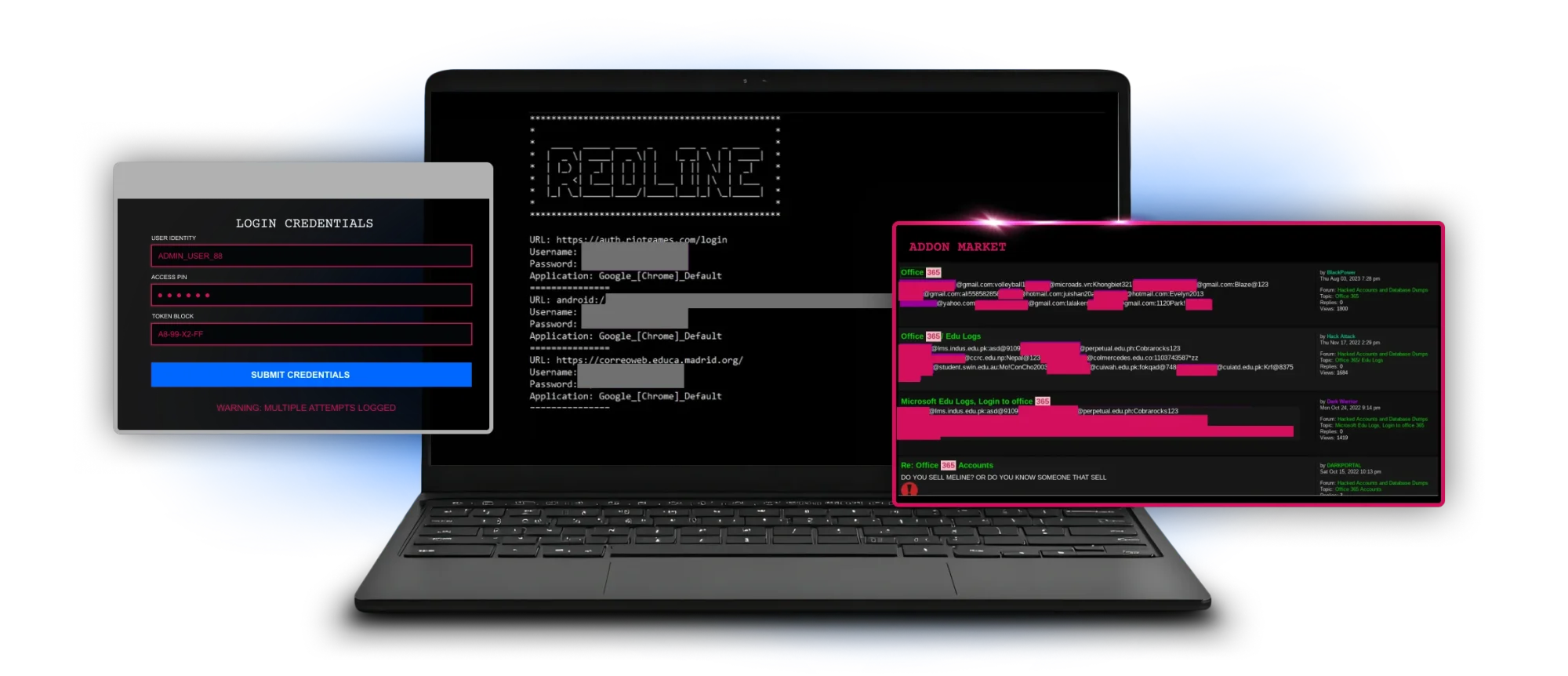
The three most common methods are: infostealer malware (like Raccoon Stealer, RedLine, or Lumma) that harvests cookies directly from the browser; adversary-in-the-middle (AiTM) phishing proxies that intercept the session in real time; and cross-site scripting (XSS) vulnerabilities that let attackers execute scripts to extract cookie values.
They help, but they're not foolproof. Conditional access policies that enforce device compliance or IP-based restrictions can flag suspicious sessions. However, attackers increasingly use residential proxies or compromised machines that already meet compliance criteria to evade these controls.
Look for sign-in events from unusual geolocations or IP addresses, impossible travel (two logins from geographically distant locations within minutes), session activity that doesn't match the user's normal hours, and risky sign-in alerts in your identity provider. SIEM log correlation is essential for catching these patterns.
Revoke all active sessions for the affected account immediately through your identity provider (Microsoft Entra ID, Okta, etc.). Reset the user's credentials, investigate inbox rules and forwarding that may have been set, check for data exfiltration, and run an endpoint investigation to find the source of the infostealer if malware was involved.
Pass-the-cookie is a specific form of session hijacking. Session hijacking is the broader concept of taking over an authenticated session; pass-the-cookie is the method where a stolen cookie token is replayed in a different browser to impersonate the victim.
HTTPS protects cookies in transit—it prevents interception on the network. But pass-the-cookie attacks typically steal cookies after they're already stored on the device, using malware or phishing proxies. HTTPS doesn't protect against endpoint compromise or AiTM attacks.