Cookie Logger Explained for Cybersecurity Pros and Learners



A cookie logger is a tool or process designed to capture or record browser cookies from a user’s system. These logs can store sensitive data, such as authentication tokens, which threat actors can exploit to hijack sessions or steal identities.
Read on for a clear, accessible breakdown of cookie logging—from what it is, to why it matters, typical attack methods, and the best ways to protect yourself and your organization.
What is a cookie logger?
A cookie logger is a piece of software, script, or malicious code that snags cookies (small pieces of data stored in your browser) and sends them to someone else, usually a cybercriminal. These cookies can include authentication tokens, browsing preferences, and other session data that allow attackers to access web services as if they were you.
Put plainly, cookie logging is spying on your browser snacks and saving the leftovers for hackers. 🍪
Cookie logging in cybersecurity
To get technical for a second—but without all the jargon headaches—a cookie logger is mostly used by cybercriminals to pull sensitive authentication info stored in browser cookies. With this info, attackers can slip right into secured accounts or company portals without a password reset or login prompt. They stroll in, undetected, as you.
Why does this matter?
Even top cybersecurity pros deal with cookie theft attacks. Tools like Evilnum, Vidar, and RedLine Stealer are infamous for plundering browser cookies. Stolen cookies = compromised sessions = a data breach fast track.
How does cookie logging work?
Here’s how cookie logging usually plays out:
Initial Compromise: A victim is tricked into downloading malware or clicking a phishing link.
Installation: The malicious code quietly installs on the system. No fireworks, just silent trouble.
Harvesting: The logger scans browser storage for cookies, especially those used for authentication (like access tokens for Microsoft 365, Google, Slack).
Exfiltration: The logger sends the stolen cookie data to the attacker’s remote server.
Abuse: The attacker uses the cookies to "become" the victim online. Think account hijacking, accessing email, or poking around sensitive company dashboards.
Important: While there are legitimate uses of cookie logging for troubleshooting and debugging, unauthorized logging is almost always a privacy and security violation.
Why Cybercriminals Want Your Cookies
Cookies are tiny, but they can pack a punch:
Session hijacking: Authentication cookies keep you logged into your accounts. If an attacker steals these, they can skip passwords altogether.
Identity theft: Cookies often store enough data for attackers to piece together your profile and run social engineering attacks.
Persistent access: Many cookies remain valid for weeks, so attackers get a long window to exploit their access.
Bypassing MFA: With an authentication cookie, attackers often bypass multi-factor authentication (MFA). No more one-time codes protecting you.
Why should security pros care?
Cookies are everywhere—from cloud platforms and CRMs to SaaS apps and banking portals. If you’re a security practitioner, cookie logging should trigger a red alert for both potential credential theft and compliance violations.
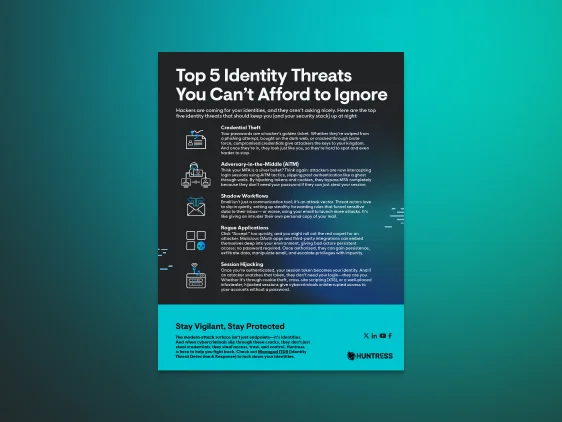
Top 5 Identity Threats
Cookie loggers steal session tokens from browsers so attackers can impersonate authenticated users without a password and bypass even MFA protections through session hijacking, so download the Huntress Top 5 Identity Threats report to see the most dangerous identity-based attack methods we are tracking and how to protect your users.

Legal and ethical considerations
The legality of cookie logging hinges on consent and intent:
Consent: Logging your own cookies for debugging is fine. Snagging someone else’s cookies? Not so much.
Laws: Unlawful cookie logging can violate privacy statutes like theComputer Fraud and Abuse Act (CFAA) and GDPR.
Terms of service: Most platforms (e.g., Google, AWS, Office 365) ban the unauthorized capture of user cookies.
Warning: Cookie logging for hacking or espionage is straight-up illegal in many countries. U.S. government take?Here’s the DOJ’s FAQ for reference.
Real-world example
Remember the 2022 breach where attackers grabbed Microsoft Office 365 session cookies during a phishing campaign? Victims clicked a fake login link, malware stole their authentication tokens, and the attackers logged into sensitive corporate resources with full privileges. The company’s security team only noticed when unusual access patterns popped up.
If you use persistent logins (the “Remember Me” checkbox), you’re a bigger target.
Steps to reduce cyber risk
Here’s your checklist for mitigating cookie logging attacks:
Patch. Patch. Patch: Keep browsers, plugins, and operating systems up to date.
Use endpoint protection: Modern antivirus software can flag and block known cookie logging tools. Managed EDR helps your organization get full visibility into all your endpoints.
Restrict downloads and scripts: Block installation of unknown browser extensions and third-party tools.
Educate employees: Security awareness training empowers your team to spot phishing and social engineering attempts.
Regularly clear cookies: Don’t hoard session cookies; clear them, especially after using critical business apps.
Enable secure flags on cookies: Developers should set HttpOnly and Secure flags. This limits JavaScript access and requires HTTPS for cookie transmission.
Monitor for suspicious logins: Use SIEM tools to flag logins from geographically improbable locations.
Future of cookie logging and browser tracking
The game is changing fast. Google announced it was deprecating third-party cookie use in the Chrome browser. However, after several years of delays it’s not happening (yet), but it will continue to evolve. With this there will be new tracking technologies that more than likely will have security risks and privacy implications.
Adversaries will always adapt. When cookies fade, expect threat actors to pivot to fresh methods, like browser fingerprinting and access token theft.
When in doubt, stay sharp and make security awareness a routine, not reactive.
Key takeaways
Cookie logging poses serious risks to both individual privacy and the integrity of enterprise systems, making it essential to stay vigilant. By understanding its implications, like data theft and session hijacking, you can better defend against these threats. Remember that while cookie logging is often illegal without proper consent, securing your environment with regular software updates, user education, and strict policies can significantly reduce your exposure.
As the reliance on cookies diminishes, it’s vital to remain cautious and adapt to emerging tracking and data exploitation methods, ensuring a robust defense in the evolving cybersecurity landscape.
Cookie logging FAQs
A cookie logger is a tool or script that captures browser cookies, often by hiding in malware or browser extensions. It then sends them to an external server for misuse.
Cookies can store authentication credentials and personal info, allowing attackers to hijack accounts without needing your password.
Unusual logins, session expirations, or receiving account alerts are red flags. Check your login history in critical services and change passwords if you suspect a compromise.
Yes, if used without consent. Capturing someone else’s cookies for malicious purposes is a crime in many regions and violates data protection laws like GDPR and CFAA.
Absolutely! Regularly update your software, don’t download unverified files or extensions, set strong passwords, and clear cookies after using sensitive platforms.



Additional Resources
- Read more about What Is Pass-the-Cookie? Definition, Examples & PreventionPass-the-cookie is a session hijacking attack where adversaries steal authenticated browser cookies to bypass multi-factor authentication and access cloud applications. Learn how it works, how to detect it, and how to stop it.
- Read more about What is adware? How to detect malicious adware?What is adware? How to detect malicious adware?Learn what adware is, the signs of infection, removal tips, and steps to protect your devices from malicious adware. Read Huntress advice now.
- Read more about What Is a Browser Extension? How They Work & Security RisksWhat Is a Browser Extension? How They Work & Security RisksA browser extension is a small software add-on that customizes your web experience—blocking ads, managing passwords, and more. Learn how they work, how they interact with websites, and how to stay safe while using them.
- Read more about What is DES? Data Encryption Standard explained for beginnersWhat is DES? Data Encryption Standard explained for beginnersLearn what DES is in cybersecurity, why it mattered, how it works, and why it’s now obsolete.
- Read more about What is Personally Identifiable Information? | PII DefinedWhat is Personally Identifiable Information? | PII DefinedLearn more about personally identifiable information, what types of PII there are, and why it’s crucial to protect sensitive information to stay secure.
- Read more about What is a Session in Cybersecurity? ExplainedWhat is a Session in Cybersecurity? ExplainedLearn what a session is in cybersecurity, its role in secure communications, and how it impacts online security.
- Read more about What Is a Digital Footprint? Explained for BeginnersWhat Is a Digital Footprint? Explained for BeginnersLearn what a digital footprint is, why it matters for cybersecurity, and how to protect yours in simple terms.
- Read more about What Is Access Logging? How to Read Access LogsWhat Is Access Logging? How to Read Access LogsLearn what access logging is, how it safeguards your network, and why it’s a must for cybersecurity and compliance. Explore use cases, tips, and FAQs.
- Read more about What is a Grabber in Cybersecurity? Grabbers in Modern ThreatsWhat is a Grabber in Cybersecurity? Grabbers in Modern ThreatsLearn what a grabber is, how grabbers work, and how to protect against grabber attacks. Stay ahead with these cybersecurity tips.


Protect What Matters