Nothing says happy Friday afternoon quite like finding a Cobalt Strike implant in your network.
Such was the case for our partners at Blue Tree Technology, a Missouri-based managed service provider (MSP). Our ThreatOps team received a Windows Defender alert for Blue Tree’s environment—and just a few minutes later, a similar alert popped up for a different partner organization.
The commonality? Hackers were exploiting Log4Shell vulnerabilities to target VMware Horizon servers.
With this observable pattern at play, our ThreatOps team jumped into action.
Gathering Data with Huntress Managed EDR
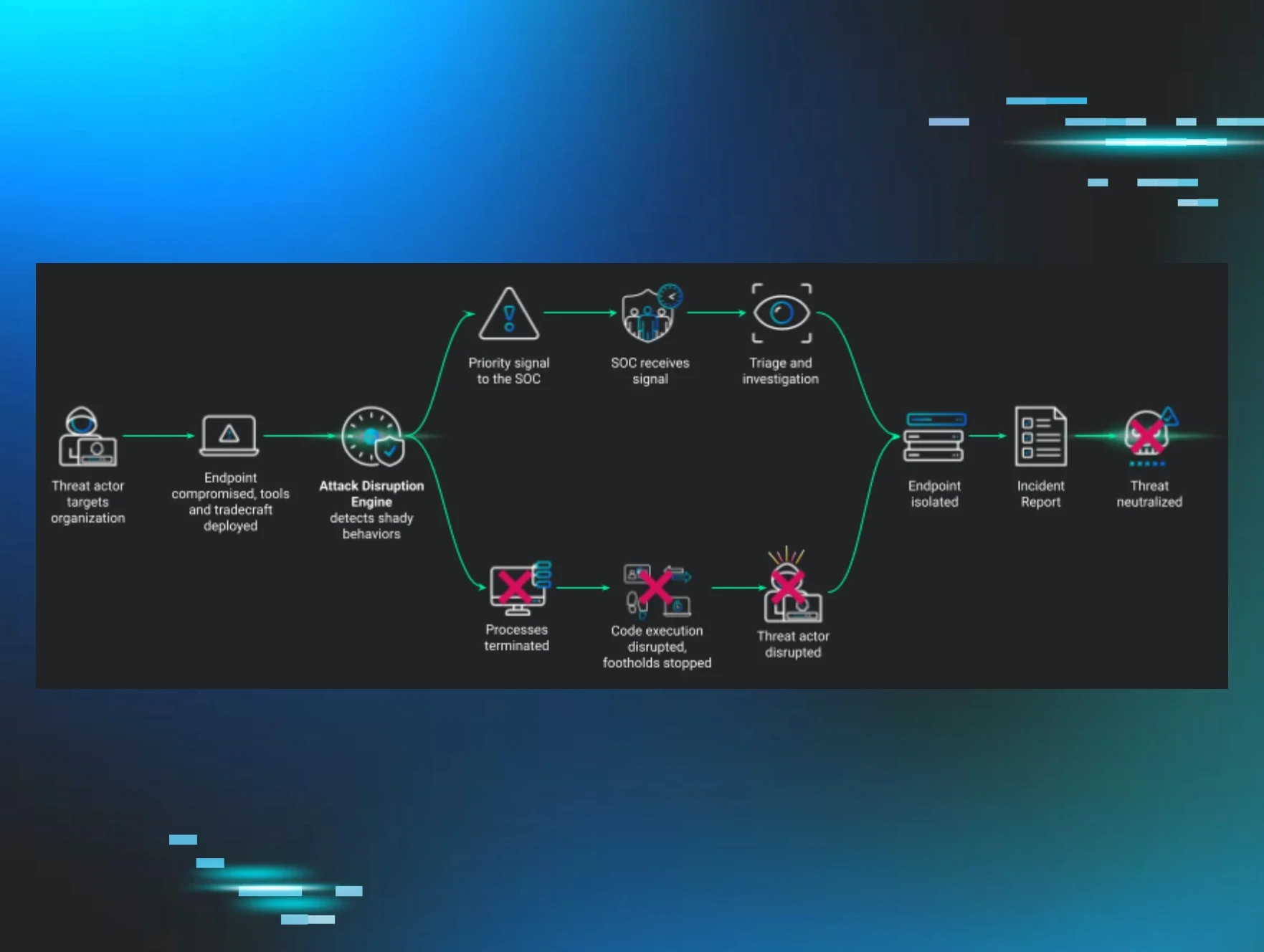
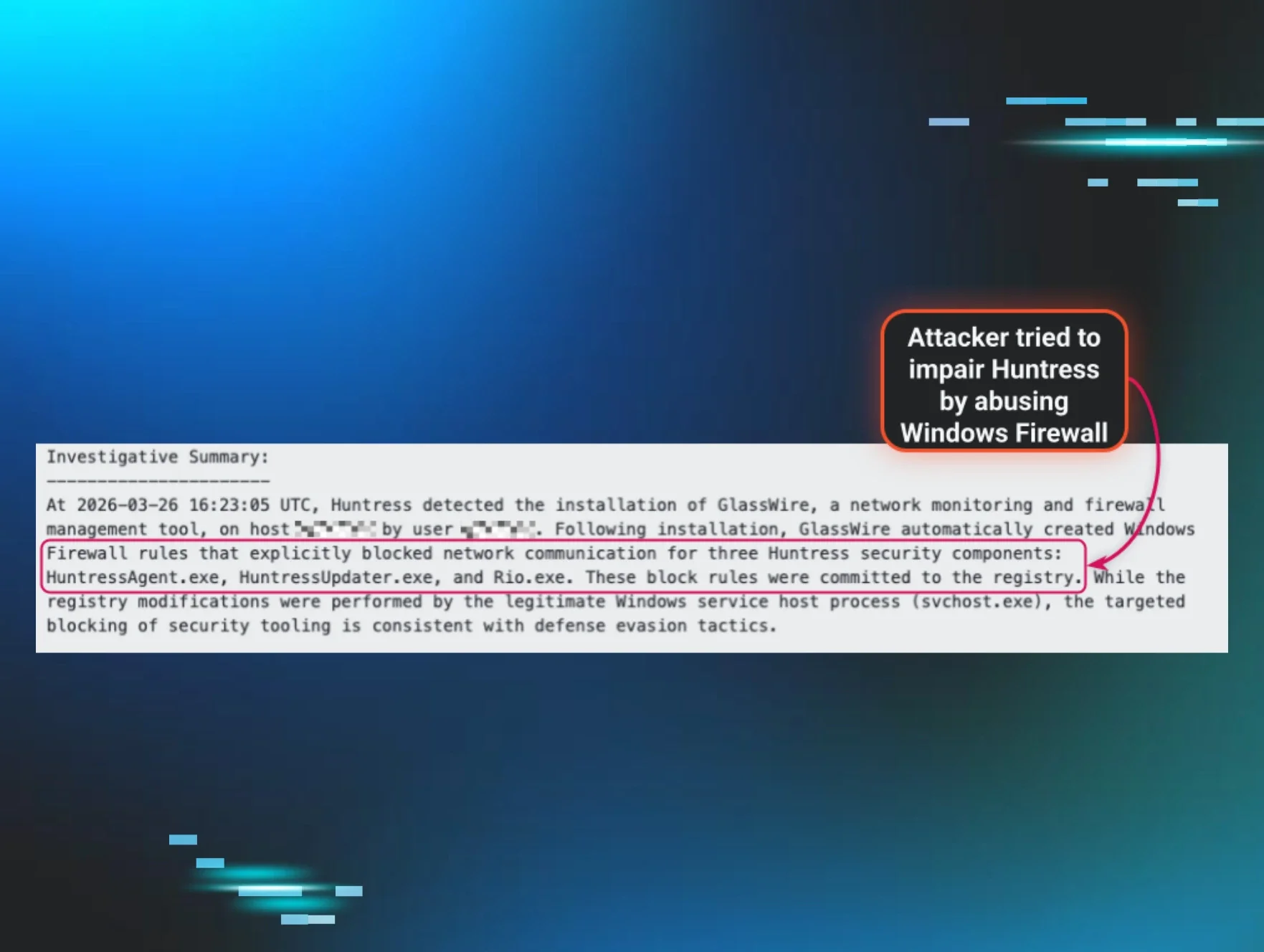
The team leaned on Huntress Managed Endpoint Detection and Response (EDR) to dig into what was happening. This feature gave our team near-real-time insights in terms of what was happening across our partners’ endpoints.
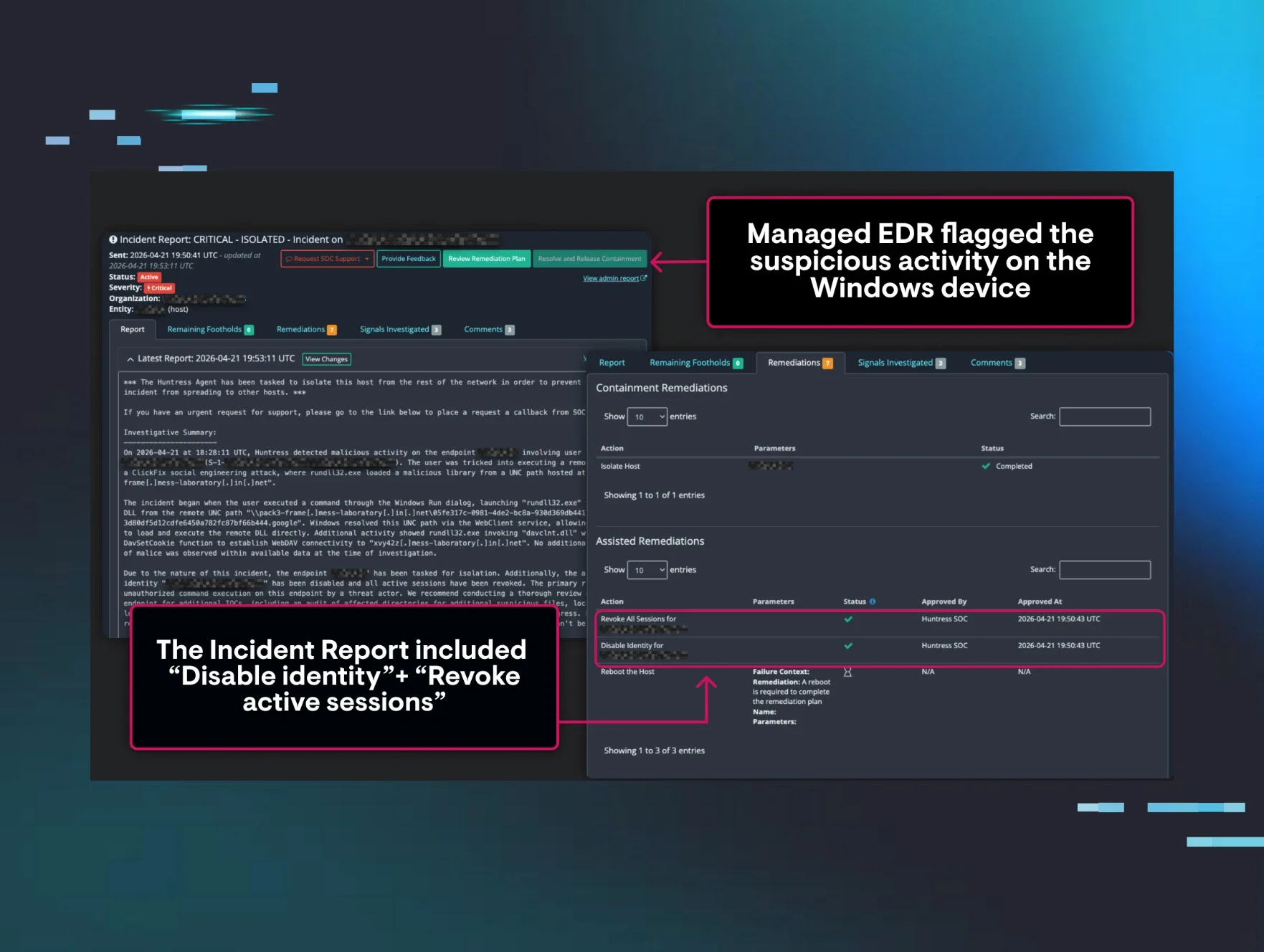
Within minutes, Huntress Managed EDR unveiled which of our partners were being targeted with malicious executable commands, which allowed our team to send out incident reports to impacted partners with information on how to mitigate the threats.
Blue Tree Technology was one of those impacted partners, as one of their machines hosted by IntelliData Solutions had been hit by hackers. Alarmingly, IntelliData Solutions had already patched their VMware Horizon servers, yet threat actors were still able to bypass those precautions and work their way into Blue Tree Technology’s machine.
Alerting Our Partners
Our ThreatOps team was able to connect with the relevant team members at Blue Tree Technology and IntelliData Solutions to provide remediation steps to get them back up and running.
Although this situation posed a real threat, traditional cybersecurity tools are notorious for raising red flags when they simply aren’t warranted. This is where the Huntress ThreatOps team is invaluable. The team analyzes logs, data and alerts to verify threats before sending incident reports to our partners. That way, our partners can focus on what actually matters and spend more time on other priorities.
Together with the Blue Tree Technology and IntelliData Solutions teams, we were able to squash this threat by the end of the day—no weekend disruptions needed.
You can watch our interview with Blue Tree Technology and IntelliData Solutions below, or read their full story.

We love a good story with a happy (week)ending.