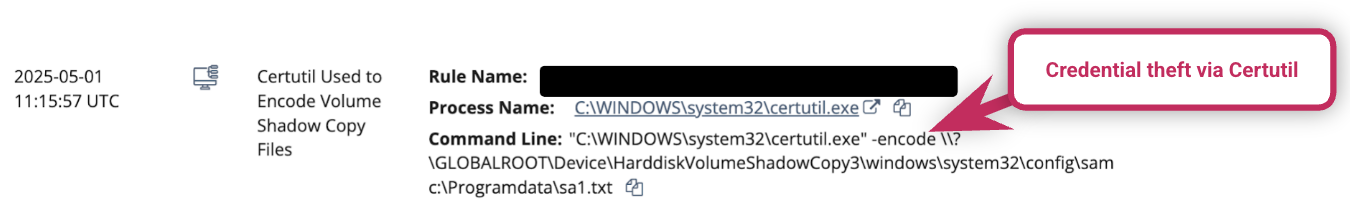
We’re seeing threat actors carry out credential theft by dumping the Windows Registry with Certutil (as seen in the May incident below). Certutil is a legitimate admin command line tool to view and manage certificates, among other things, but it’s often abused by attackers.
Threat View from the Lens of Huntress Adversary Tactics: May 2025
Welcome to the inaugural edition of the Huntress Adversary Tactics newsletter, meant to arm you with information about threats not only seen by Huntress, but also in the world externally. Since this is our first edition, the cadence may vary as we receive input from various stakeholders. This initial newsletter will also be more verbose than following ones, as we define some terms and workflows that may be unfamiliar to some. In the future, we hope to keep it short and sweet and meaningful.
The hope is that this will ultimately unify us all in our mission to mess up attackers who insist on targeting the most vulnerable population of the technical cyberspace - our customers, partners, and their customers. We welcome your input of what you’d like to see in the future.
Threats Seen in the SOC
One of the workflows that Adversary Tactics has, is to document interesting threats that are surfaced from the SOC via reports. Here are some examples of interesting trends we’ve seen in the last few weeks.
Credential Theft via Certutil
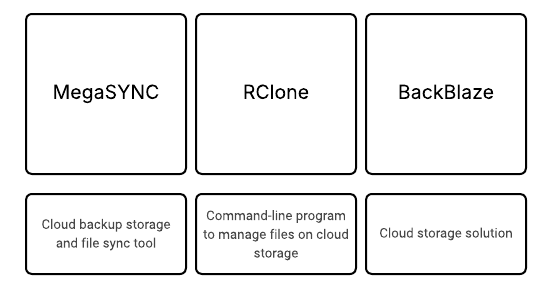
Threat Actors’ Use of MegaSYNC, RClone, BackBlaze
Threat actors are using a variety of tools for data exfiltration in attacks. Recently, we’ve observed threat actors misusing legitimate backup storage tools, such as MegaSYNC, RClone and BackBlaze. On May 2, for instance, the SOC responded to an incident where the threat actor, after logging in via RDP, attempted to use the legitimate BackBlaze cloud storage platform (along with WinRAR) to target and exfiltrate various file types.
The Upshot: Threat actors and admins use similar techniques. Huntress Managed EDR looks for suspicious activity, including processes spawning from legitimate programs that are being abused by threat actors.
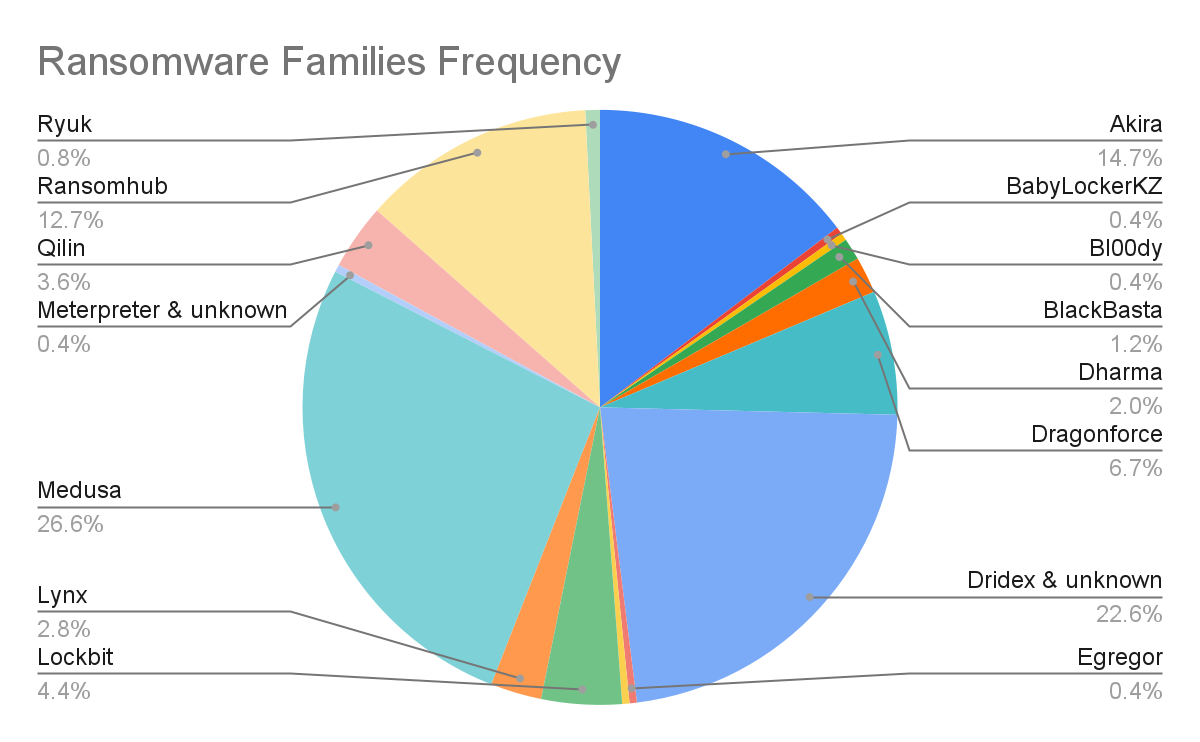
Ransomware Seen Across Our Customers
Looking over past incident reports from January 2025 - May 15, 2025 we are able to paint a picture of the most common ransomware variants that we’ve seen across our customers. Out of the 606 reports that were actually ransomware related, the most common variants were Unknown ransomware variants (not shown in the above chart), making up 58.4% of the number of reports issued this year. While some unknown ransomware reports may have just not been categorized, a sampling of these reports verified that some were, in fact, unknown samples, sometimes even poorly written ones. This seems to prove one of our previous findings from the 2024 Huntress Threat Report that showed that there are newcomers to the ransomware space trying to cut their teeth in perceived “low hanging fruit” environments.
Focusing on known ransomware variants, the most prolific ransomware family was Medusa, making up 26.6% of the number of reports from this year. Dridex malware, which is not ransomware, but ultimately led to ransomware, came in second at 22.6%, followed by Akira at 14.7%, and RansomHub at 12.7%. We also had one report that included a ransomware called Bl00dy, which is known to be used by a threat group named Storm-1305 by Microsoft. We’ve also seen incidents involving DragonForce (6.7%), which has been used by a threat group named Scattered Spider in the recent UK retailer attacks. We’ll discuss this last one a bit more a bit later in this newsletter.
Given the discord and disruption across ransomware actors this year (and discussed in an upcoming section), it will be interesting to see what will happen with ransomware across our customers. It will be interesting to see which threat actors scramble to fill the void that is left in the wake of others’ demise.

Threats Around the World
Breaking down the bring your own Installer attack
TL;DR: Attackers were recently observed using a bypass technique that disables SentinelOne so that they can install the Babuk ransomware undetected. SentinelOne now has a workaround for this type of attack, however customers who obtained SentinelOne via CW were left without recourse for a period of time.
The Details: Attackers took advantage of an issue in the upgrade process for SentinelOne’s agent. When installing the agent, the installer deletes Windows processes and overwrites existing files with the new version. Attackers were seen deploying legitimate SentinelOne installer files, letting the installer terminate the existing running processes, and then forcing the Windows installer to terminate before it completed installation, effectively disabling SentinelOne.
The Upshot: While SentinelOne was vulnerable to this type of attack, Huntress most likely is not. We verified with Huntress engineering that as far as how agents are installed, the potential for this type of attack is almost close to nil. The main points as laid out by Rob Noeth, Principal Software Engineer on the Huntress EDR agent are:
- We don't have a download link for [our installers] anywhere, but it's on our CDN
- We don't allow downgrades
- Our rio (agent) upgrade rollout is fairly quick, and we don't have [older] versions sitting around
- We also have tamper protection enabled in current agents
Caveat: It is theoretically possible that some of our installers may be available on VirusTotal, so we can’t discount this entirely. However, since we don’t allow downgrades, this type of attack should not be as easily successful.
Coinbase Pulls Out Uno Reverse Card on Would Be Extortionists
TL;DR: Coinbase, the leading U.S. cryptocurrency exchange, disclosed an insider threat cyberattack that began with an extortion attempt on May 11th, 2025. Cybercriminals bribed overseas customer support agents, primarily in India, to steal personal data from less than 1% of Coinbase’s monthly transacting users (approximately 97,000 accounts, given Coinbase’s stated 9.7 million user base). The compromised data included names, addresses, phone numbers, government-issued IDs, and partial Social Security numbers, but no login credentials, two-factor authentication codes, private keys, or customer funds were accessed. The attackers reportedly used this data for social engineering scams, impersonating Coinbase to trick users into transferring cryptocurrency, and went on to demand a $20 million ransom to suppress the breach.
The Upshot: Coinbase refused to pay, instead offering a controversial reverse bounty of $20 million reward for information leading to the arrest and conviction of the would-be extortionists. The company estimates remediation costs, including reimbursing affected customers, to range between $180 million and $400 million. Affected users were notified via email on May 15, and since the breach Coinbase implemented enhanced security measures, including relocating some support operations to a new U.S. hub and increasing transaction monitoring.
Ransomware Landscape and Implosions
Ransomware Groups Hacked
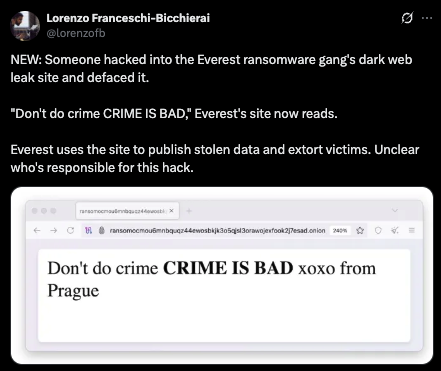
TL;DR: In late April or early May 2025, LockBit’s dark web affiliate panels were breached and defaced by an unknown threat actor. The defacement replaced the panels with a mocking message: "Don’t do crime CRIME IS BAD xoxo from Prague," accompanied by a link to a MySQL database dump titled paneldb_dump.zip. The database, analyzed by BleepingComputer, contained 20 tables exposing critical operational details:
btc_addressesTable: Included 59,975 unique Bitcoin addresses, likely used for ransom payments and laundering. This exposed LockBit’s financial infrastructure, potentially aiding law enforcement in tracking transactions.buildsTable: Listed individual ransomware builds created by affiliates, including public encryption keys (but no private keys) and, in some cases, targeted company names, revealing attack specifics.builds_configurationsTable: Detailed build settings, such as instructions to skip certain ESXi servers or encrypt specific files, providing insight into LockBit’s tactical customization.chatsTable: Contained 4,442 negotiation messages between LockBit operators and victims, spanning December 19, 2024, to April 29, 2025. These logs revealed aggressive extortion tactics, with demands ranging from a few thousand to $100,000. These are odd in the sense that LockBit was thought to be running a much more profitable scheme. This has implied that LockBit might be more closely aligned with governmental or state-ran alliances.usersTable: Exposed credentials for 75 admins and affiliates, with plaintext passwords likeWeekendlover69andLockbitproud231, highlighting poor security practices.
The defacement message matched one used in a recent breach of the Everest ransomware group’s site, suggesting a possible connection, though the attacker’s identity remains unclear.
The Upshot: The 2025 LockBit hack was a critical blow, exposing operational details and undermining the group’s reputation. While it provides law enforcement and victims with valuable tools, LockBit’s history of resilience suggests it may attempt another comeback, potentially with LockBit 4.0. Organizations should prioritize robust cybersecurity practices, such as patching vulnerabilities, securing credentials, and maintaining offline backup to mitigate risks from LockBit and other ransomware infections.
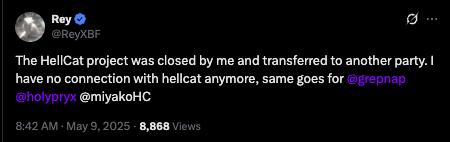
Hellcat Implosion
TL;DR: Hellcat surfaced in late 2024, quickly gaining notoriety for targeting high-profile organizations, including government agencies, educational institutions, energy sectors, and critical infrastructure. Operating under a RaaS model, Hellcat provided affiliates with ransomware tools and infrastructure in exchange for a share of the profits. The group was known for its sophisticated tactics, psychological manipulation, and aggressive pursuit of media attention.
On May 11, 2025, posts on X reported that Hellcat had ceased operations. The group’s darknet site displayed a "cryptic farewell" message, with no active leaks or files remaining, indicating a shutdown. An X post by @ido_cohen2 noted that Hellcat had attacked over 15 companies worldwide before closing. Another post by @ValeryMarchive suggested a possible reason for the disbandment: a leak by "LB" (potentially linked to the LockBit ransomware group) revealed that Hellcat affiliates had joined LockBit in January 2025, conducting five attacks under the LockBit brand without securing any ransom payments. This financial failure and exposure may have prompted Hellcat’s closure. A third post by @RFr0sty1 on May 13, 2025, categorized the shutdown as a "new event" in cyber threat intelligence, reinforcing the narrative of Hellcat’s cessation.
The Upshot: Hellcat’s rapid rise and abrupt disbandment in May 2025 reflect the volatile nature of the ransomware landscape especially for 2025. Emerging in mid-2024, the group leveraged advanced TTPs, psychological tactics, and a RaaS model to target high-value organizations, causing significant disruption. Its closure, potentially driven by financial struggles, law enforcement pressure, or affiliate migration to LockBit, marks the end of a notable chapter in cybercrime. However, the group’s tactics and the broader RaaS ecosystem continue to pose challenges, emphasizing the need for proactive cybersecurity defenses. It is to be seen what legacy the group leaves behind in the future.
DragonForce
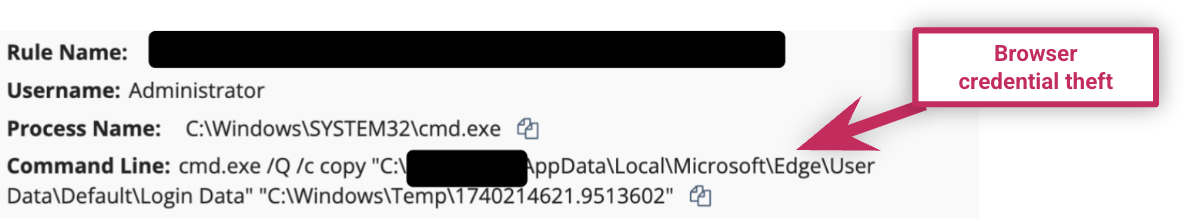
DragonForce has been in the news recently after the ransomware group claimed responsibility for a slew of attacks on UK retailers like Co-op, Harrods, and Marks and Spencer. We have observed DragonForce ransomware incidents over the past year, where customers’ files were encrypted with the extension .dragonforce_encrypted:
- Dec. 2, 2024: The ransomware deployed by the threat actor triggered canary alerts stating that files had been encrypted
- Feb. 22, 2025: Threat actors were able to access the endpoints via RDP shortly after connecting via PSExec; threat actors also stole browser credentials (see figure below) and installed a kernel mode driver that resulted in other security services on the victim endpoint (SentinelOne and Webroot) crashing
There are currently warnings that similar attacks may shift to retailers in the US and elsewhere.
As we highlighted in the 2025 Cyber Threat Report, more ransomware groups like Hunters International are shifting to attacks that prioritize data theft and extortion, rather than data encryption. Part of the reason for this change by threat actors is to evade EDR protections. The SOC has observed this trend play out in the wild, so it’s important for businesses to make an incident response plan that incorporates extortionware in addition to ransomware.

Rapid Responses
For the unaffiliated, “Rapid Responses” spin up in the event that there is a vulnerability, or threat that attackers are leveraging in order to further their attacks at scale. When we hear of a potential vulnerability, the Adversary Tactics team collaborates with other teams across Huntress, and sets to work on figuring out the potential impact, and what new and/or novel information we can publish about it. Ultimately, we will also find potentially impacted customers and notify them, as well as publish a blog with all the juicy details to further educate the community. Here are some examples of Rapid Responses that we’ve completed within the last month:
CrushFTP (4 Apr 2025)
TL;DR: In early April, we saw evidence of exploitation of CrushFTP CVE-2025-31161.
The Details: While we saw a small handful of our customers actually impacted as a result of this software vulnerability, there were more than 100 potentially vulnerable machines across our customers. In all observed incidents, attackers leveraged the vulnerability in order to install RMMs such as MeshAgent and SimpleHelp.
The Upshot: We were more than prepared for this type of threat, and the SOC received alerts for activities surrounding these attacks well before it was reported by media outlets.
Gladinet CentreStack (12 Apr 2025)
TL;DR: In mid April, we saw evidence of exploitation of a flaw in Gladinet CentreStack and Triofox (CVE-2025-30406).
The Upshot: Not only did we clarify that CVE-2025-30406 also exists in Gladinet Triofox in addition to CentreStack (a fact that had not been widely reported), but we also prepared a PowerShell script so that customers could check if they are vulnerable.
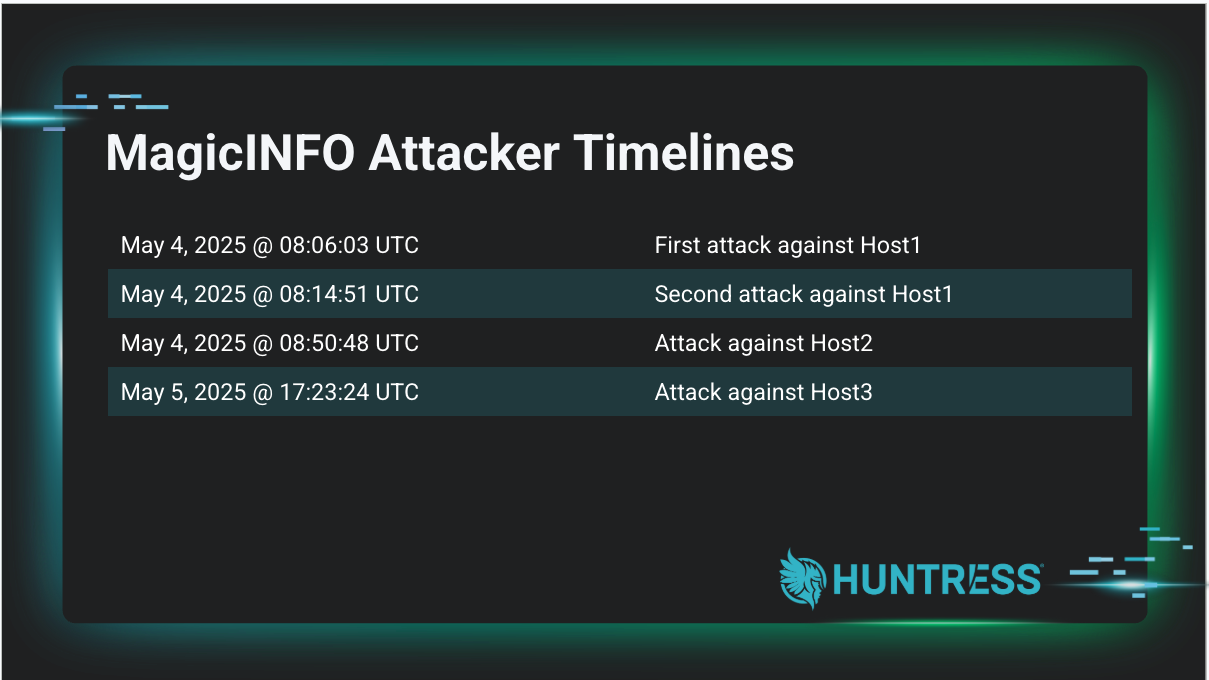
MagicINFO (6 May 2025)
TL;DR: In early May, we saw evidence of exploitation of a Samsung MagicINFO 9 Server flaw.
The Details: We saw limited exploitation for the flaw; over 75 different machines had MagicINFO installed across our customer base, but we only saw three separate incidents involving the flaw. Because this vulnerability impacts the latest version of Samsung MagicINFO 9 Server, we urged users to make sure their servers aren’t internet facing, as no patch existed at the time of publication. After publication of the initial Rapid Response, Samsung released a software update fixing the vulnerability (CVE-2025-4632).
The Upshot: We independently verified that the latest version of Samsung MagicINFO 9 Server was vulnerable to a publicly available PoC, despite widespread reports that said otherwise.
Acknowledgements: We’d like to thank our partners over on the Hunt and Response team, Jai Minton and Craig Sweeney, for handling the bulk of the lift of the initial investigation into the MagicINFO vulnerability, recreating the exploit, and writing the original blog post. It’s a team effort, and together, we win!

Relevant Product Updates
We’d like to highlight some killer new capabilities that our partners in Product Research and Product have released to help mess up attackers. We’re excited to use this data as we continue to arm our customers against threat actors.
EDR
AiTM Phishing Detection
Huntress recently added new detections to our EDR product to help identify when users land on phishing sites designed to steal Microsoft 365 credentials—not just passwords, but full authentication tokens.
These are called Adversary-in-the-Middle (AiTM) attacks. Unlike traditional phishing, AiTM campaigns intercept authentication traffic in real-time, stealing session cookies or OAuth tokens to bypass MFA and gain immediate access to Microsoft 365 environments. Huntress EDR can now detect when a user visits AiTM phishing sites, but there’s a catch: EDR alone can’t tell us if the attack was successful.
This is where Huntress ITDR (Identity Threat Detection & Response) steps in. By combining EDR and ITDR, Huntress gains the identity-level visibility needed to confirm whether a session token was compromised—and if so, we take full action on your behalf: revoking active sessions, resetting passwords, and stopping intrusions before attackers escalate access.
Takeaways: If you want Huntress to not only detect these sophisticated phishing attempts, but also fully contain and remediate them, consider deploying ITDR today.
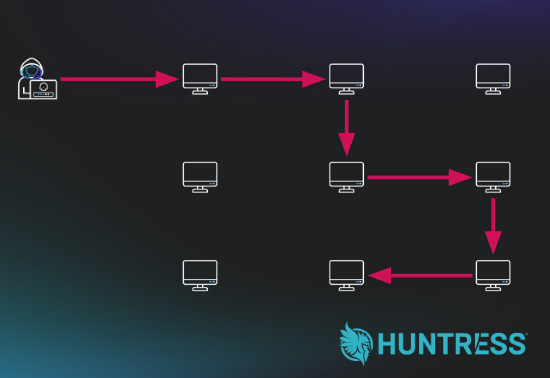
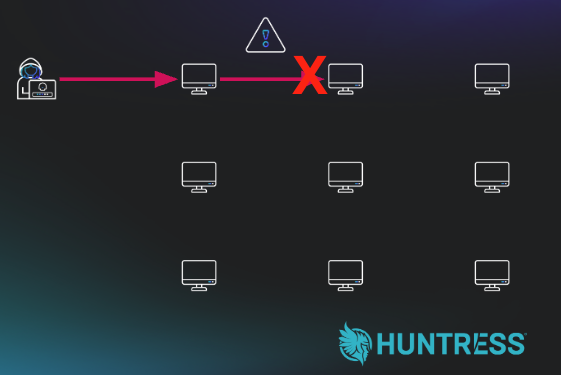
Lateral Movement Detection
Another big win on the horizon for our EDR product is Lateral Movement Detection. This will allow us to quickly pick up on attackers as they start to move from machine to machine within a victim’s environment. This is a huge differentiator - and we’ve already used it to ruin the plans of ransomware actors! The following two pictures show unhindered lateral movement, while the second picture shows alerting on lateral movement as it happens:
|
|
|
If threat actors are still moving around in the environment, it is likely that they are still early in the process of reconnaissance and exfiltration - before more damaging actions have taken place. Anytime we can get an early drop on threat actors, we have a chance to shut down the attack before damage is done.
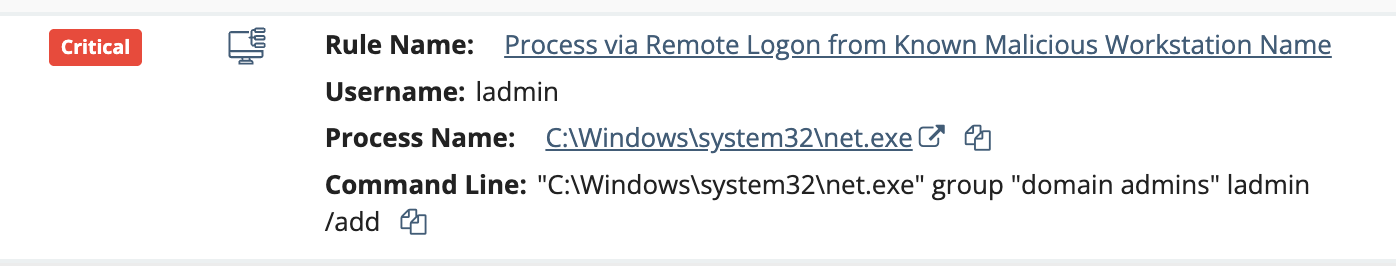
Tracking Processes Spawned from Malicious Logon Sessions
New as of mid-May is a detection capability that allows us to alert on processes that are created from the same user who logged on from a known malicious workstation name. This gives even better visibility into what threat actors are doing on a machine - meaning we can block their activity even more quickly. As you can see in the figure below, this is an alert of reconnaissance activity that was done as part of a pre-ransomware event:
Getting ahead of ransomware actors is always the goal. The sooner we can alert, the less potential damage that the threat actors can do.
SIEM
New and Improved SIEM Detections
Recently, we've added 46 net-new detections and tuned 17 existing detections for Managed SIEM. By continuously refining our detection logic and proactively hunting for threats, we're able to help our partners and customers benefit from an ever-improving security posture.
ITDR
We launched our Rogue Apps capability for ITDR. Most Microsoft 365 environments allow any user to install any app to the tenant by default. Attackers know this all too well, and are taking advantage of this with malicious or compromised OAuth apps, enabling credential theft. With Rogue Apps, we’re flipping the script. You won’t just find out about malicious apps after the damage is done - you can detect and block them from the start. Another huge win for cracking down on attackers!
Highlights
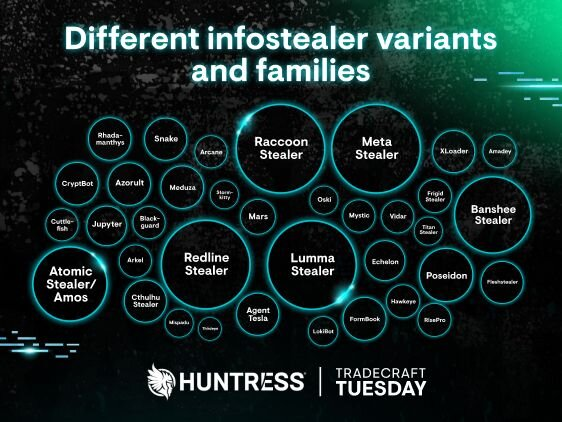
Tradecraft Tuesday
|
|
May 2025’s Tradecraft Tuesday covered infostealers, which is a threat currently plaguing the world. What was once considered a minor annoyance has now grown into a full fledged threat, enabling credential theft and identity-based attacks, and setting the stage for future attacks.
In addition to the overall view of various infostealer families, this episode also included relevant tradecraft that was exposed by reports from our SOC, much to the delight of the audience.
|
Verizon DBIR
The Adversary Tactics team lead the collaboration efforts between Huntress and the yearly Verizon DBIR Report. Huntress is uniquely positioned to have insight into threats that are actually plaguing smaller businesses, like no other company currently in the industry. Verizon was eager to collaborate, and were able to incorporate our findings into their report, and they hope to have further collaboration in the future.