What Are Managed IT Services? The Practical Guide for 2025
Written By: Brenda Buckman
Last Updated: February 6, 2025



| Managed IT services are a way to outsource a company’s IT needs to a dedicated team rather than relying on in-house IT specialists. These services provide comprehensive IT support that is often more thorough and affordable than in-house IT teams. |
|---|
Threat actors don’t pull punches when targeting small businesses. In the third quarter of 2023, Huntress analysts found that 40% of the incidents they responded to were critical or severe threats. That's why having comprehensive IT services in place is so important. But hiring an in-house IT team is out of reach for some businesses.Managed IT services are a simple way for businesses to outsource their IT needs to a dedicated team through a vendor or managed service provider (MSP) who manages the process. Doing so can help companies like yours maintain compliance and prevent security threats that could impact operations. Let’s look at how managed IT services can help your organization.
10 Types of Managed IT Services
Managed information technology services provide ongoing support for day-to-day needs like troubleshooting, updates, and user assistance. There are multiple types of managed IT services that can benefit different businesses. It all depends on the challenges you’re looking to solve.
Here are a few you’ll want to be aware of.
1. Cloud Services Management
Cloud-based services like Amazon Web Services (AWS), Azure, and Google Cloud make it easier to keep track of data without forcing your business to invest in costly on-site storage solutions. But managing the information stored in the cloud can be a challenge. With cloud services management, you’ll have a dedicated IT team to oversee your organization’s data.
Managed IT services help enhance the security of your info in the cloud, and they can monitor data for weaknesses, threats, and other risks. By outsourcing, your managed services provider can implement changes or updates as needed to ensure your data is readily available to those who need it.
2. Network Security Management
Network security management helps companies protect themselves from cyberattacks 24/7. It does this by managing firewalls, monitoring and detecting unauthorized access to internal systems, and identifying potential vulnerabilities nonstop.
When partnering with a managed IT service provider, you can outsource your cybersecurity efforts to a team of experts who are up-to-date on the latest threats and security measures, so your information will be safer for longer.
3. Data Backup and Disaster Recovery
Backing up your business’s data can reduce the impact of natural disasters, cyberattacks, accidental data loss, and other unwanted interruptions. Managed IT services help you maintain the data flow and reduce downtime by storing your data in a secure location off-site.
If anything happens to compromise your systems, or your organization loses its info during an emergency, you’ll be able to regain access to that data faster.
4. Endpoint Management
Endpoint management involves securing and managing all devices connected to your company’s network. For example, businesses using managed endpoint services can enforce strong password policies to enhance security or disable lost or stolen devices to prevent unauthorized access.
This means creating protocols to protect computers, printers, cell phones, tablets, and any other devices with access to your organization’s private network. While it’s possible to do this in-house, it can be costly, especially for larger companies.
When you choose the right endpoint detection and response (EDR) solution to oversee your endpoint management, you’ll save money and bolster security for all of your teams’ devices. Dedicated service providers have access to tools, programs, and equipment at a larger scale that individual businesses may not be able to afford on their own. On the other hand, if you choose unmanaged (or self-managed) EDR for your organization, you could leave vulnerabilities in place, which may increase your risk of security issues down the line.
5. IT Consulting
Even if an organization has an in-house IT specialist, they may not know how to address every possible threat or concern. Managed IT services provide expert guidance on IT-related issues like strategic planning, IT budget optimization, technology selection, and more.
This’ll help ensure your business invests in the right tools, programs, and equipment to keep your data as safe as possible. IT consultants can also help you identify common cybersecurity threats, so you can develop a plan to protect against them in the future.
6. Server Maintenance
Properly maintaining servers, monitoring hard drives and performance, and backing up data keep your network running smoothly. By outsourcing server maintenance, a team of experts can keep your servers working 24/7, and they’ll be available to address any slowdowns or issues as soon as they come up.
This can help reduce downtime and keep your systems running the way they should.
7. Project-Based Services
It’s normal for one-time IT projects to pop up as your business grows. These projects may involve time-sensitive initiatives that need to be put into place quickly. Managed IT services can accommodate those one-time projects with ease.
Your in-house team can focus on their daily responsibilities and core functions without spending time handling urgent situations that may be outside the scope of their regular duties.
8. Data Analytics Services
Data analytics can help you interpret the information your company collects and use that information to grow your business. With managed IT services, you can partner with a dedicated data analyst who can look at what you have and find insights you can use.
Say your organization is continually struggling to meet demands for a specific customer. You may be consistently out of stock of an item at a particular time or your inventory isn’t accounting for fluctuating demand.
Your managed data analytics provider can review the sales and trends info you’ve collected and identify problem areas so you can make the necessary changes to maintain your inventory better to fit demand.
This information can help you identify trends in your business, find ways to reduce bottlenecks, and monitor the performance of certain campaigns so you can make data-driven decisions.
9. On-Site Managed IT Services
On-site managed IT services allow you to partner with an MSP that can send technicians to your physical location to provide in-house IT support and management. This may include help desk support, proactive maintenance, and network monitoring.
Your MSP would normally oversee the hiring and managing of these technicians, sparing you the hassle of recruiting an in-house IT team that can address your concerns.
10. Managed Print Services
Managing printers and copiers, ordering replacement parts and toner, and addressing system errors can be time-consuming. Your MSP can maintain your printer network and any supply orders on your behalf. For businesses that rely on printed documents, having a dedicated provider to oversee and manage printers and copiers can save time, money, and stress.
How Much Do Managed IT Services Cost?
The exact cost of managed IT services depends on the pricing model, the size of your org, and the services you need. Generally, smaller businesses that need less managed IT support will spend less than larger organizations with more complex needs.
Pricing models can also vary from provider to provider. These are some of the more common pricing structures you may see as you start your search:
Per device: Some MSPs charge for their services on a per-device (computer, tablet, printer, etc.) basis. The more devices you have, the more you’ll typically pay.
- Per user: This pricing structure charges you by the user, regardless of the number of devices. For large organizations with hundreds of devices, per-user rates may be more affordable.
- Tiered by package: Every organization’s needs are unique. This pricing structure allows you to pay for packages that offer only the services you need, potentially helping you save money.
Consider your budget and your business’s needs when reviewing different pricing models.
Pros of Managed IT Services
Managed IT services offer unique benefits that aren’t available with in-house teams. Here are a few pros of hiring an MSP:
- Cost savings: Managed IT services can provide you with the IT support you need at a fraction of the cost of hiring an in-house team. As your business grows, your MSP can scale with you at an affordable rate.
- Increased efficiency: Building out a dedicated IT department takes time, putting your operations at risk until everyone is up to speed. With managed IT services, your MSP handles hiring, training, and scheduling. Your IT team will be able to hit the ground running from day one.
Enhanced security: Managed IT services give you access to trained IT professionals and the tools you need to protect your systems and data. These solutions can be customized to fit your business’s unique needs, whether that’s providing identity threat detection and response (ITDR) or enhancing the security you already have.
Cons of Managed IT Services
Though managed IT services offer many benefits, they’re not always the perfect solution for every business. Here are some potential cons you may experience when using managed IT services:
- Less control: With managed IT services, you’re partnering with a service provider and trusting them to provide you with the IT solutions you need. This gives you less control over the methods and programs they use to help your business.
- Limited customization: The MSP takes charge of identifying the best solutions for your needs within their existing framework. They may not be able to customize those solutions completely to fit your specific needs and goals.
- Communication concerns: Outsourcing any aspect of your business means you may need to wait to get answers to your questions. This can make it tricky to implement necessary changes and new solutions quickly.
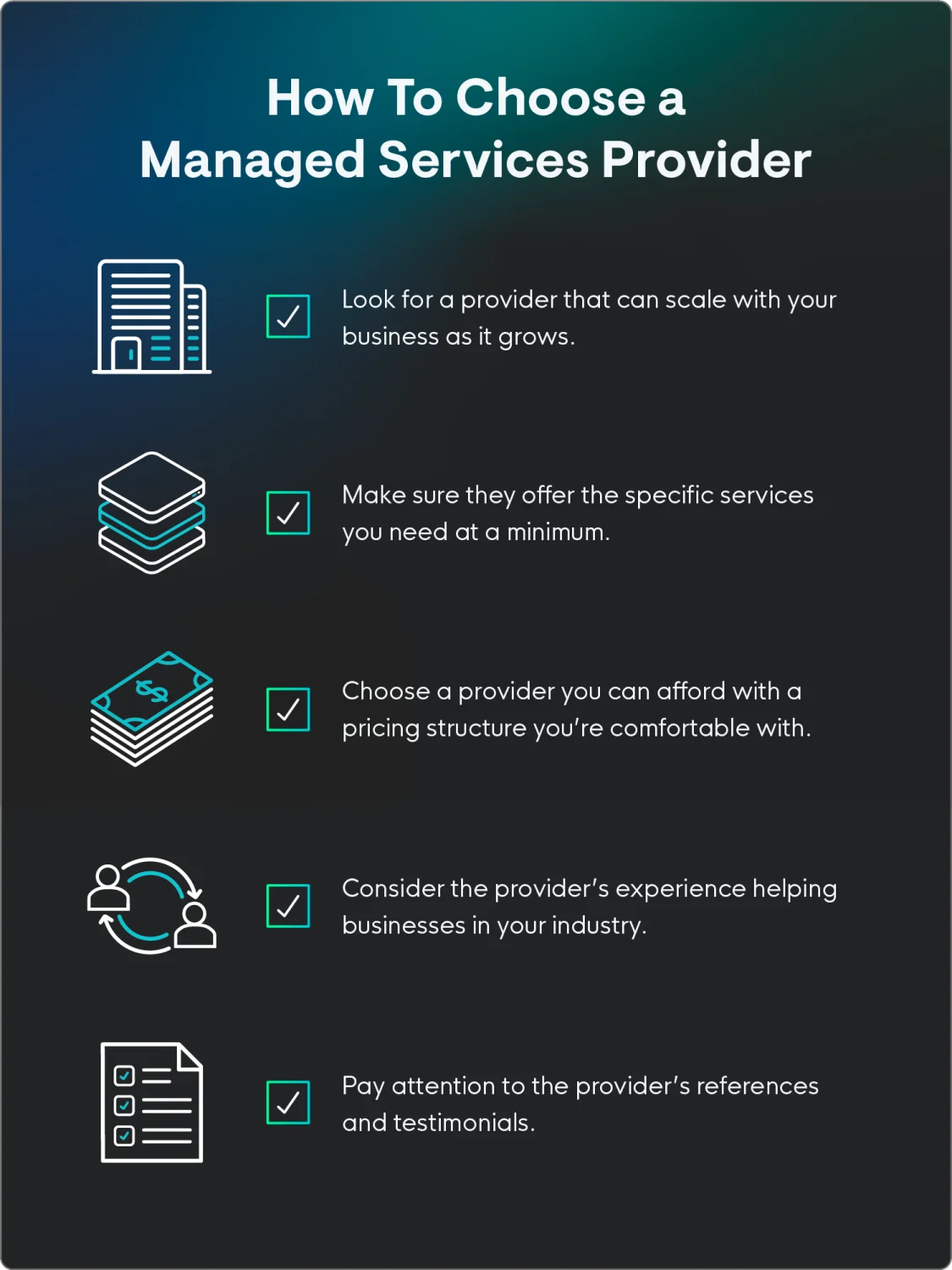
How To Choose a Managed IT Service Provider
Not all managed service providers are created equally. Choosing the right managed IT service provider can make all the difference in your company’s security and ability to grow. Here are a few considerations to keep in mind as you explore your options:
- Cost: Different providers charge different rates. Be sure to compare rates with several providers and make sure you’re comfortable with the rates and billing structure before signing on.
- Needs: Some managed IT service providers provide comprehensive IT support, while others offer select services. Look for a provider that offers the types of services your business needs.
- Industry experience: Look for a provider that’s helped businesses like yours in your industry. This will help you get the support you need from the beginning.
- References: Ask for references for each provider you’re considering, and see what their clients have to say about their services. If the reviews are good, you’ll likely have a similar experience.
- Scalability: You should choose a provider you can work with for years to come. Be sure to consider each provider’s ability to grow with your brand.
Choose Fully Managed Security Services for Your MSP
Partnering with a managed service provider is a simple way to protect your business and ensure you’re meeting all of its IT needs.
However, for MSPs, finding a trusted partner to manage security efforts can strengthen your offering and help you better protect your clients. With managed IT services, you can boost data analytics and security throughout your organization.
See how Huntress can help managed service providers improve their offerings. Start your free trial today.
FAQs
Managed services may be managed print services, where a company oversees all aspects of a business’s printers and copiers, or managed network security, where an MSP manages firewalls, data recovery and backups, and more.
IT support is a service that responds to incidents when they happen and typically fixes issues on a per-project or per-incident basis. On the other hand, managed services help businesses monitor their IT needs and can regulate maintenance and analysis to prevent common incidents from happening in the first place.
Every managed service provider can offer different services. However, most MSPs offer server maintenance and monitoring, data analytics, network security management, and data backup and recovery services. Consider your needs when comparing MSPs and choose the provider that offers the services you need.




Additional Resources
- Read more about What Is a Disaster Recovery Plan? Complete GuideLearn how to create a disaster recovery plan that protects your business from cyber threats and operational disruptions. Essential guide for IT professionals.
- Read more about What is Infrastructure as a Service (IaaS)? | GuideWhat is Infrastructure as a Service (IaaS)? | GuideLearn what Infrastructure as a Service (IaaS) is, how it works, and why it's essential for modern cybersecurity. Complete guide with examples.
- Read more about What is Platform-as-a-Service (PaaS)? | Cybersecurity GuideWhat is Platform-as-a-Service (PaaS)? | Cybersecurity GuideLearn what Platform-as-a-Service (PaaS) is, its cybersecurity benefits and risks, and best practices for securing PaaS environments in this comprehensive guide.
- Read more about Firewall Cost and Considerations | Cybersecurity 101Firewall Cost and Considerations | Cybersecurity 101Learn how much firewalls cost, from software to enterprise-grade hardware. Find pricing tips, key factors, and budgeting advice to protect your network.
- Read more about What Are Application Services? Cybersecurity GuideWhat Are Application Services? Cybersecurity GuideLearn what application services are, their role in cybersecurity, and best practices for securing them. Essential guide for security professionals.
- Read more about Managed Detection and Response (MDR) ExplainedManaged Detection and Response (MDR) ExplainedWhat is Managed Detection and Response (MDR)? It's 24/7 cybersecurity that combines technology & human expertise for threat hunting & rapid response. Learn more here!
- Read more about MSP vs MSSP: Understanding the Differences | Huntress Cybersecurity 101MSP vs MSSP: Understanding the Differences | Huntress Cybersecurity 101Confused by MSP vs MSSP? Learn the key differences between IT management and cybersecurity providers to decide which service your business actually needs.
- Read more about What Is Platform Consolidation? Why It Matters for ITWhat Is Platform Consolidation? Why It Matters for ITLearn what platform consolidation is, why businesses are moving toward fewer tools, and how it helps streamline IT, boost security, and cut costs—especially for SMBs and MSPs.
- Read more about What is Recovery Point Objective (RPO)?What is Recovery Point Objective (RPO)?Learn about recovery point objective (RPO)—a key metric in data recovery that helps minimize data loss, protect critical assets, and support strong cybersecurity strategies.


Protect What Matters