What Is Cybersquatting? A Guide for Cybersecurity Professionals
Written by: Brenda Buckman
Published: May 18, 2025


Ever seen a domain like “amaz0n.com” or “g00gle.info”? Congratulations, you've encountered cybersquatting.
Cybersquatting is one of the many sneaky threats lurking in the digital space, and combating it is now a critical part of cybersecurity. Whether it’s phishing, brand impersonation, or outright extortion, cybersquatters have their sights set on exploiting companies and users alike. For cybersecurity professionals, understanding how cybersquatting works, its variations, and what to do about it is essential for safeguarding brands and reputations in the online world.
This guide dives deep into cybersquatting—from what it is to how to prevent it. You’ll find actionable insights to detect, counter, and protect against this persistent cybersecurity issue.
What Is Cybersquatting?
Cybersquatting, or domain squatting, involves the bad-faith registration, use, or sale of domain names that closely resemble trademarks or well-known brands. The primary goal? To profit at someone else’s expense.
For instance, a cybersquatter might register a domain like “netflx.com” or “nikeofficialstore.com” to trick users, extort companies, or monetize web traffic. They leverage the brand’s reputation and customer trust as tools for fraud, and the fallout can be both reputational and financial.
How Is Cybersquatting Different from Legitimate Domain Speculation?
While domain speculation (buying domains with resale potential) is perfectly legal, cybersquatting crosses into illegal territory when domains infringe upon trademarks or are used maliciously. It’s not about a fair trade; it’s about exploitation.
The TL;DR Legal Definition
Under the Anticybersquatting Consumer Protection Act (ACPA), cybersquatting is defined as registering, trafficking, or using a domain “confusingly similar” to a trademark with bad-faith intent to profit.
Real-world Examples
-
“nasa.space” trying to sell Teflon cookware? That’s cybersquatting.
-
“supportyourmarketplace.com”—hosting online shopping ads? Legit. (Annoying, but legit.)
Types of Cybersquatting Every Cybersecurity Pro Should Know
Different cybersquatting strategies require different responses. Here's a breakdown of the five main offenders:
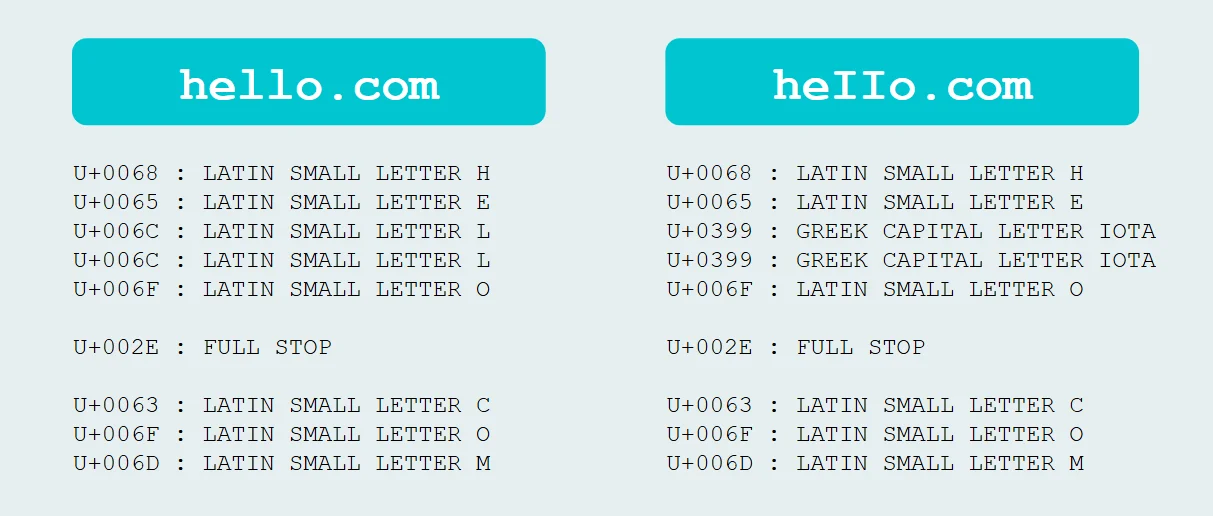
1. Typosquatting
Also known as "URL hijacking," this involves slight misspellings of domain names (e.g., “gogle.com” or “paypa1.com”).
Why it’s dangerous: Users land on fake sites, often falling victim to phishing scams or malware downloads.
2. Identity Theft / Impersonation
This entails registering domains that mimic companies or high-profile individuals (e.g., "Elon-Musk-Store.com").
Why it’s used: Often for credential harvesting, defamation, or fraudulent schemes.
3. Reverse Cybersquatting
Here, a malicious actor flips the script, falsely accusing the legitimate domain owner of cybersquatting.
What happens next: They misuse the legal process to hijack the domain.
4. Name Jacking
This involves registering a domain based on a public figure’s name (e.g., “JohnSmithCEO.com”), usually to sell it back at a premium.
Impact: Damage to personal branding and potential identity misrepresentation.
5. Domain Warehousing
Squatters scoop up lapsed domains with existing brand value and hoard them.
Result: Companies are forced to pay steep buy-back prices to reclaim their online territories.
Why Attackers Love Cybersquatting
Why do attackers go through the trouble of registering deceptive domain names? Here’s what they gain:
-
Extortion: Asking businesses to pay for their own name (“You want 'yourbrand.com'? Pay $20K.”)
-
Phishing: Tricking users into inputting sensitive info on fake sites.
-
Ad Monetization: Generating revenue by redirecting traffic to ad-filled domains.
-
Brand Sabotage: Displaying offensive or misleading content for reputational harm.
-
Malware Hosting: Using official-looking domains to deliver malware payloads.
For attackers, this is low effort with potentially high rewards.
What’s the Risk? Business Impacts of Cybersquatting
Cybersquatting isn’t just a legal headache. It’s a multi-faceted threat that can cause:
1. Financial Loss
Imagine losing potential customers because they landed on a typosquatted phishing site. Plus, the costs of litigation or buying back domains add up fast.
2. Reputation Damage
Visitors who encounter suspicious or offensive content on a squatted domain might associate it with your brand, resulting in long-term trust issues.
3. From Annoying to Dangerous
Squatted domains used in phishing or malware attacks can lead to data breaches and compromised accounts, impacting your company’s overall security posture.
4. Legal Costs
Even with tools like UDRP arbitration, pursuing legal recourse takes time and money. For larger enterprises, combating cybersquatters is nearly a full-time job.
How Managed Security Awareness Training Helps Identify Cybersquatting-based Phishing Attacks
Managing the technical side of cybersquatting is one thing, but what about the human side? This is where Managed Security Awareness Training (SAT) steps up as a key player. By arming employees with the right knowledge, you’re not just solving problems as they happen but actively preventing them.
Here’s how Managed SAT can help your team stay ahead of phishing attacks leveraging cybersquatting:
Spotting Suspicious Domains: Training equips employees with the ability to recognize fake URLs like “amaz0n.com” or “g00gle.net.” Knowing what a legitimate domain looks like reduces the chance of accidental clicks on malicious links.
Understanding Typosquatting Tactics: Employees learn how slight domain variations are exploited in phishing scams. Real-world simulations can show how attackers trick users into divulging sensitive details.
Encouraging Proactive Reporting: Staff are trained to flag and report suspicious links or emails to the IT team. Quick reporting can halt a potential threat before it escalates.
Building Phishing Resistance: A strong education program provides repeated, real-world scenarios. These practice runs empower users to make smarter decisions when faced with a phishing attempt.
Make no mistake; attackers love targeting human error. By weaving managed security awareness training into your cybersecurity strategy, you’re addressing this vulnerability head-on. Think of it like giving your team security superpowers—even the best technical defenses need informed humans to back them up.
How to Fight Back Against Cybersquatting
Feeling overwhelmed? Arm your cybersecurity arsenal with the following defensive tactics:
Detection Tactics
-
WHOIS Lookups: Use domain registries to identify suspicious domain registrations.
-
Typosquatting Scanners: Automated tools detect domains aiming to mimic yours (e.g., DNProtect or NameCheck.)
-
Brand Monitoring Tools: Tools like BrandShield flag cybersquatting trends targeting your brand.
-
Domain Registration Alerts: ICANN and registrars often provide notifications for new, similar registrations.
Countermeasures
-
Cease-and-Desist Letters: Sending one can lead to compliance without legal escalation.
-
UDRP Complaints: Submit disputes through WIPO or ICANN to regain domains. It’s faster than court.
-
Legal Action: When necessary, pursue litigation under ACPA.
-
Buy Back Domains: Sometimes, it’s just easier to pay the squatter’s ransom.
Proactive Protection
-
Register alternative domains (e.g., “.com” + “.net” + “.co.uk”).
-
Secure similar spellings or common typos of your brand name.
-
Lock down your domains with registrar-level security features.
Stay sharp, stay vigilant, and squash those squatters before they cause damage to your brand. A combination of tech, training, and team awareness is your best defense. Want to learn more about Huntress Managed Security Awareness Training? Book a demo today.

Additional Resources
- Read more about What is Typosquatting? Domain-Based Deception ExplainedLearn how typosquatting works, see real-world examples, and get expert tips to detect and prevent domain-based deception in cybersecurity.
- Read more about What is a Threat Actor? How To Spot and Avoid Rising ThreatsWhat is a Threat Actor? How To Spot and Avoid Rising ThreatsWhat is a threat actor? Learn key definitions, types, motivations, and how to detect them in your network with expert insights and Huntress examples.
- Read more about What Is a Parser? A Guide to Parsing in ProgrammingWhat Is a Parser? A Guide to Parsing in ProgrammingLearn what a parser is, how it works, and why it's essential in programming. This comprehensive guide breaks down parsing stages, types, and real-world applications in simple terms.
- Read more about What is Brandjacking?What is Brandjacking?Learn how brandjacking bypasses traditional security controls to exploit your brand identity. Discover detection strategies, real-world examples, and defense tactics.
- Read more about What Is OSINT? Why Every Security Pro Should CareWhat Is OSINT? Why Every Security Pro Should CareDiscover how OSINT transforms public data into actionable cybersecurity insights. Learn tools, strategies, and why pros swear by Open-Source Intelligence.
- Read more about What is Spear Phishing?What is Spear Phishing?Discover what spear phishing is, how it works, and prevention tips to protect your organization. Sign up for Huntress’ Free Security Awareness Training today.
- Read more about What Is a Race Condition? Types, Causes & Security ImpactWhat Is a Race Condition? Types, Causes & Security ImpactLearn everything cybersecurity professionals need to know about race conditions. Discover their definition, types, causes, real-world examples, and how to detect and prevent them.
- Read more about What is an Anonymizer in Cybersecurity?What is an Anonymizer in Cybersecurity?Learn how anonymizers work to protect your digital identity, the different types available, and best practices for cybersecurity professionals.
- Read more about Exploiting PunycodeExploiting PunycodeLearn what Punycode is, how cybercriminals exploit it for phishing, and the best defenses against homograph attacks in this 5-minute guide for cybersecurity pros.


Provide an Impactful SAT Experience
Don’t just check a compliance box. Elevate your workplace’s security culture while giving your employees an enjoyable experience.