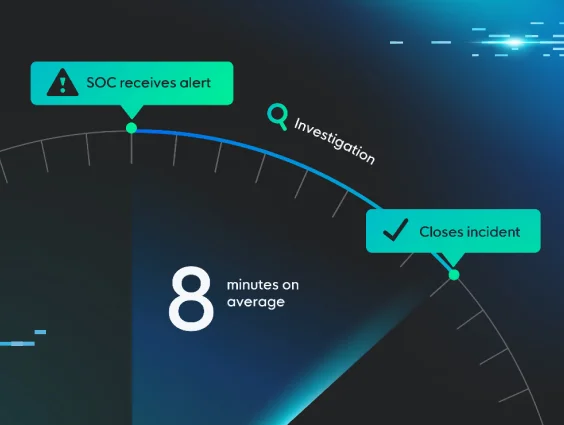
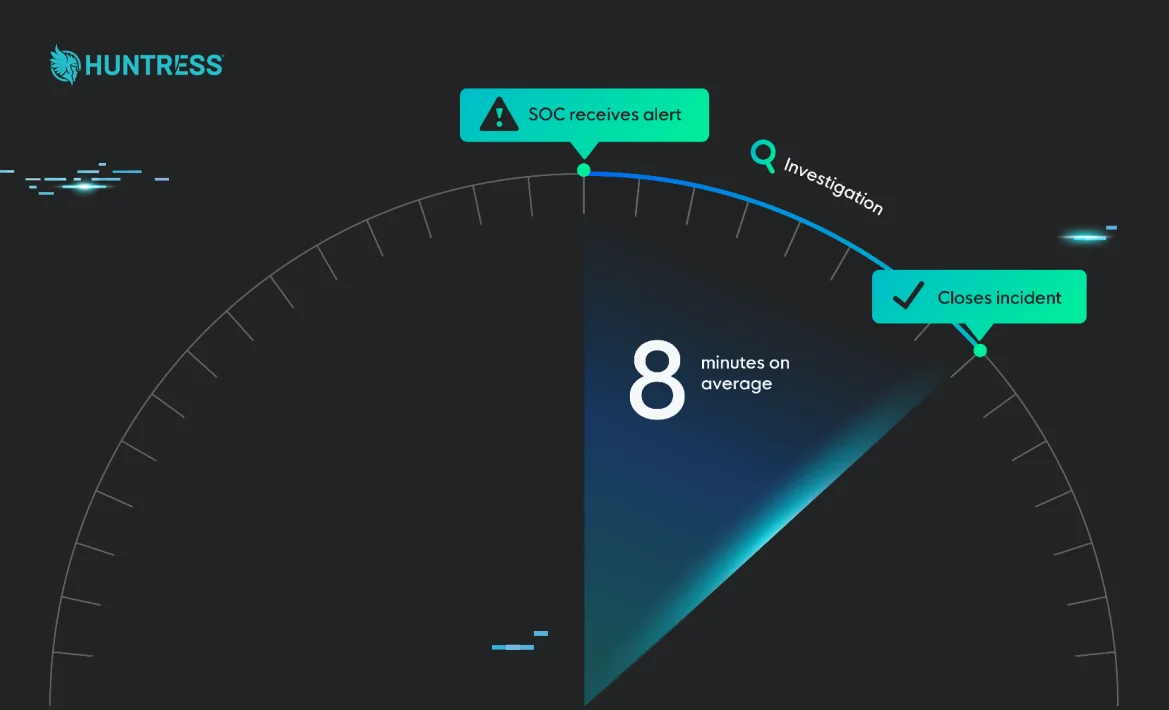
When it comes to cybersecurity, speed can make the difference between blocking an attacker at the front door and finding out they’ve helped themselves to the crown jewels. This is why we're so proud of our Mean Time to Respond (MTTR) of just 8 minutes.
Yes, you read that right.
We measure MTTR as the average time it takes for our Security Operations Center (SOC) to investigate a threat—from receiving an alert to sending an incident report (or closing the alert).
Let’s look at the key advantages that enable our SOC to respond with exceptional speed and accuracy, why MTTR matters, and how we strike a balance between efficiency and precision to deliver real protection for your business—not just engineered metrics.
Why Does MTTR Matter?
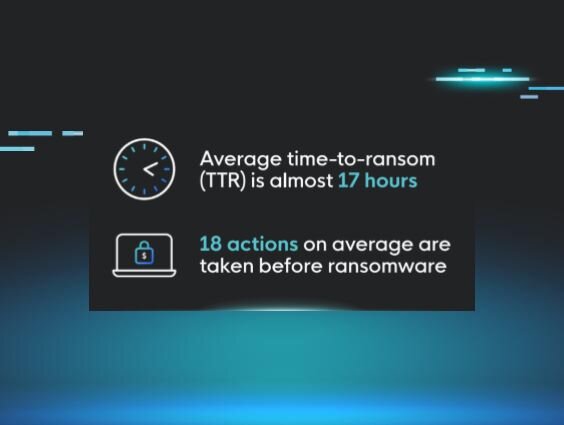
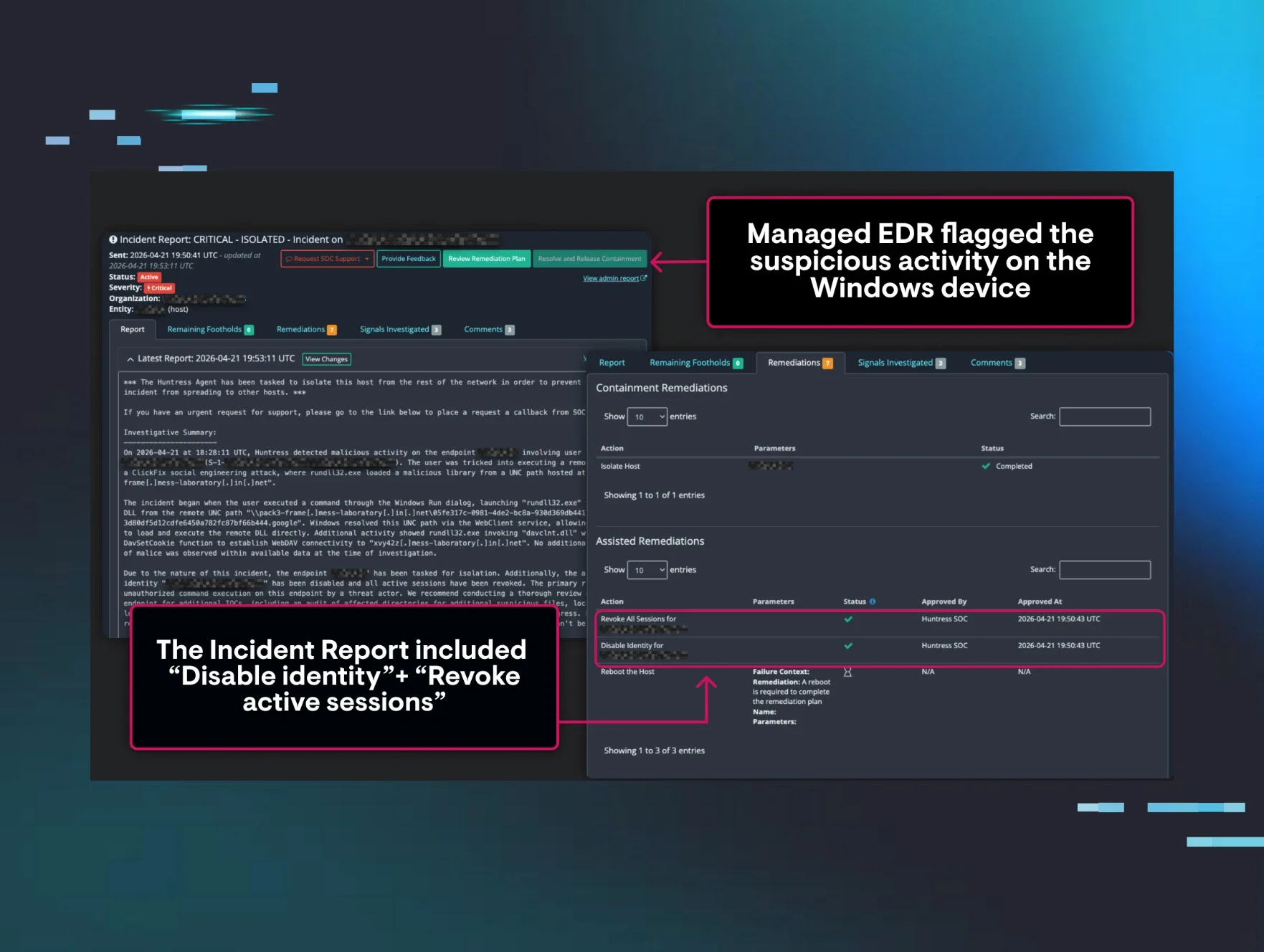
You've heard the cliche, "When you're under attack, every second matters"? (I'm guilty of using that one more often than I care to admit). Well, it’s a cliche for a reason. When an active attack is happening, you only have a few minutes to understand what’s happening and less than an hour to do something about it.
A faster MTTR means attackers have less time to move laterally, escalate privileges, gain persistence, and complete their attack. We've all got the need for speed, but speed alone isn’t a recipe for wrecking hackers. Closing tickets quickly just to hit performance goals isn’t our style.
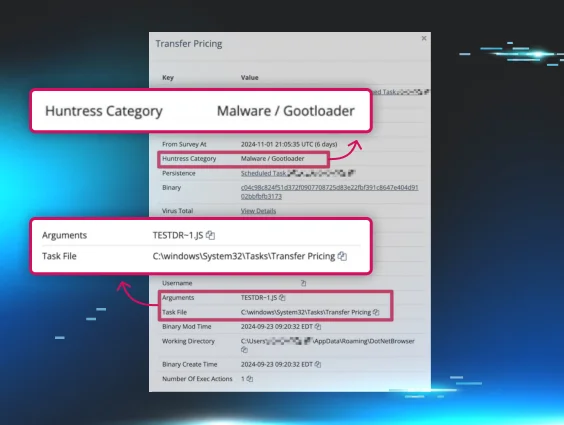
Our eight-minute MTTR doesn’t come from cutting corners or “auto-closing” minor alerts. We investigate alerts thoroughly and ensure we’re delivering real security outcomes. That means understanding the scope and impact of a threat, how attackers got in, and what’s needed to keep them from coming back.
Here are some key details about our MTTR:
- 8-minute average MTTR: Measured from when our SOC receives an alert until sending an incident report or closing the alert.
- Our MTTR is, on average, 12 minutes when we issue an incident report, and 4 minutes if we don't.
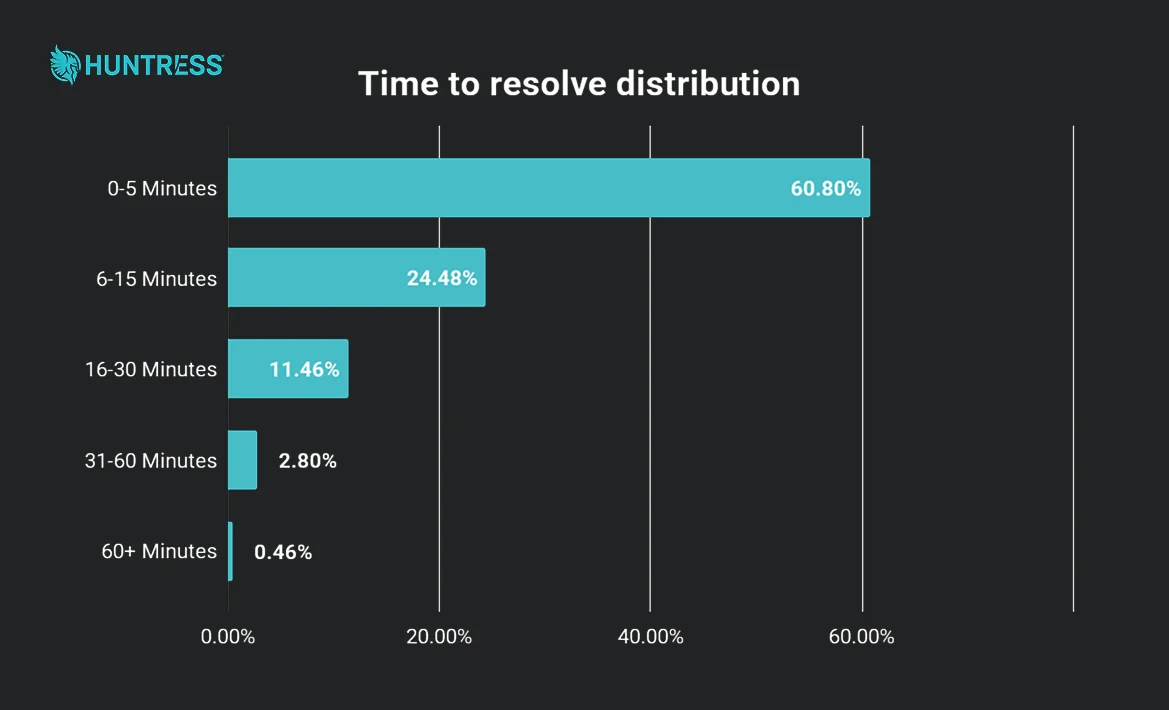
- 85% of alerts were resolved within 15 minutes.
- 97% were resolved within 30 minutes.
- Only 0.5% of alerts take longer than an hour. No one’s taking their sweet time here, but some threats need that extra level of investigation.
- Huntress Managed Identity Threat Detection and Response (ITDR) alerts have a super fast MTTR of only 3 minutes!
- The Huntress SOC sent 78k confirmed high/critical incident reports in 2024.
How We Pull Off the Industry’s Fastest MTTR
Achieving and maintaining an eight-minute MTTR isn’t easy. It all comes down to how we’ve built Huntress to be fast, precise, and relentless.
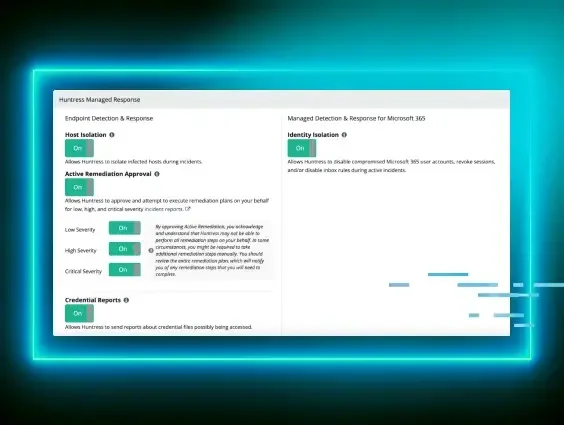
1. Tools Are Built for Our SOC
We don’t just slap a managed detection and response (MDR) service on top of a hard-to-navigate platform. Our tools are designed for our SOC from the ground up—and that’s why we move faster and get better results. This means:
- Fewer delays in transferring information between tools and people
- Efficient detection and remediation
- The ability to focus on outcomes for you
Competitors often try to retrofit their tech or outsource chunks of their operations. Spoiler alert: outsourced security services are slow.
2. We Own Our Tech Stack
Another game changer is that we own and build our entire tech stack. No third-party hand-me-downs. This allows us to:
- Fix issues faster
- Build tools optimized for speed and efficiency
- Respond to alerts with precision—every piece of tech is purpose-built for our experts to succeed in protecting you, not to cover up bad design.
When a SOC and product engineering are designed to work hand in hand, you get real results.
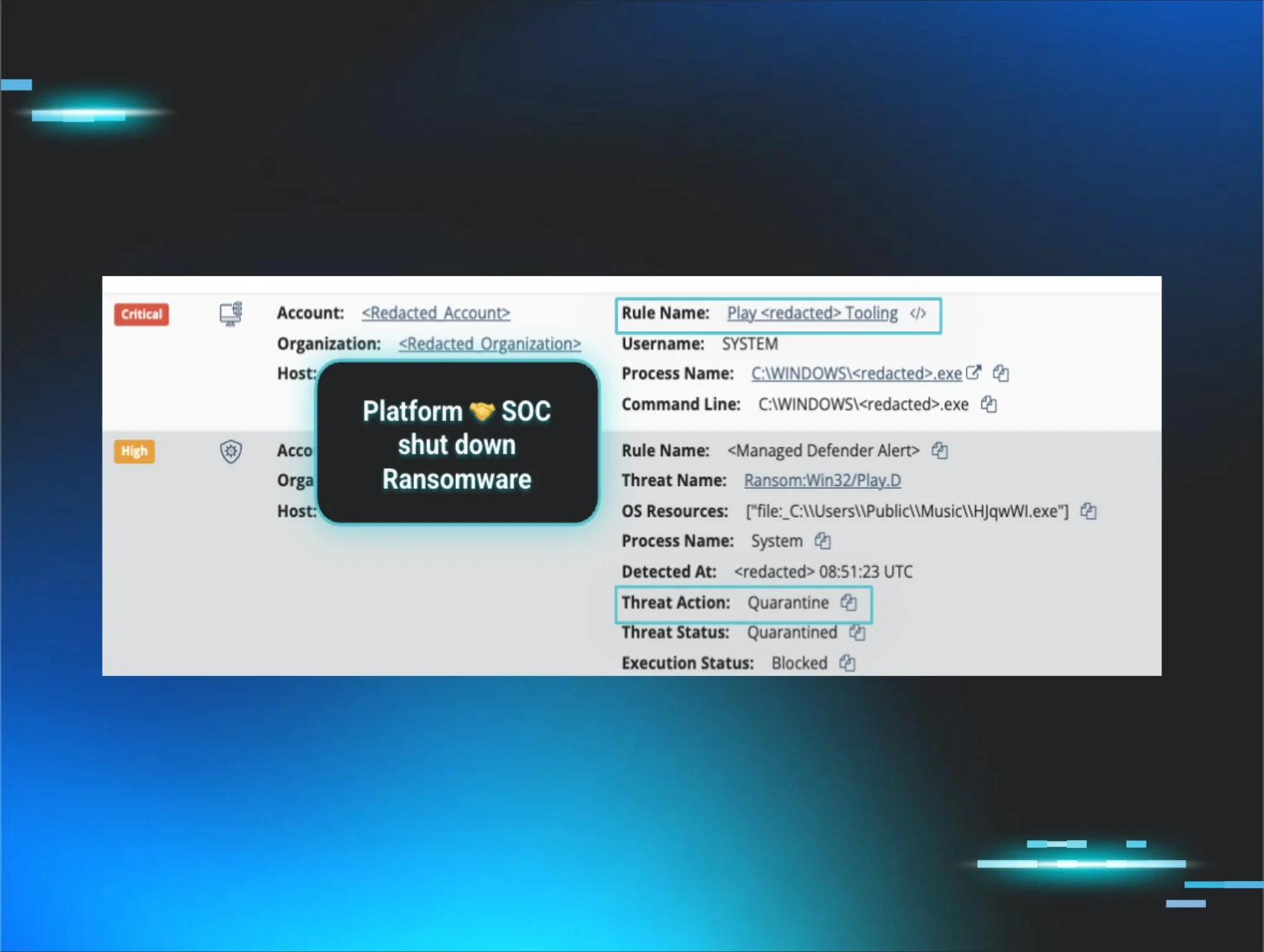
3. We’re Powered by Real People, Assisted by AI
AI is now everywhere in cybersecurity. As it should be, it’s a powerful tool. But on its own, it can’t outthink human hackers. That’s why at Huntress, AI works with our people, not instead of them. Our SOC is led by over 100 of the sharpest defenders in the industry—peer-reviewed, battle-tested, and backed by years of hands-on experience. They’re the ones steering the AI, separating signal from noise, and digging deeper when a threat hides in the shadows.
And with our follow-the-sun approach, you’re never left waiting. There’s always a well-rested, elite threat analyst keeping watch, day or night.
What Slows Down Other SOCs?
Here’s why other vendors struggle to match our MTTR:
- Not owning their own tech: Anytime you separate the tech and the people, you introduce risk and potential delays.
- Separate silos: Their SOC and products weren’t built to work together. In most cases, the service was “bolted on” to the tech because the tech was too hard to use on its own. However, building the tech for the SOC increases speed and leads to better security outcomes.
- Lack of expertise: To reduce costs, vendors often cut corners by hiring less experienced analysts whose main role is to triage alerts and pass them back to you.
Our approach is different. Huntress provides seamless integration between our products, our SOC, and our experts. This allows us to get to the heart of the problem in record time.
Why This Matters to You
With Huntress, you’re not settling for average—you’re choosing industry-leading speed and best-in-class expertise. Whether you’re safeguarding data or defending against ransomware, we’ve got your back.
Find out how Huntress can protect your business with unparalleled speed, enterprise-grade technology, and world-class experts.
Sign up for a demo today and experience the Huntress difference.