On August 13, our SOC responded to a ransomware attack involving dynamic link library (DLL) sideloading via a legitimate SentinelOne binary. DLL sideloading is a detection evasion technique that involves executing malicious code through signed executables. Because this involves trusted executables, it helps threat actors sidestep security solutions. In the incident, we saw that the threat actor loaded SentinelAgentCore.dll from SentinelBrowserNativeHost.exe. The DLL then loaded data.bin, which contained the actual ransomware code. The attacker used Remote Desktop Protocol (RDP) as an initial access vector. They also ran a series of commands to create Microsoft Defender exclusions for various file paths (C:\Windows\System32\svchost.exe and C:\Windows\Temp) and file extensions (.dat, .sss, .cache, and .tmp), in an attempt to avoid detection. The ransom note linked the attack back to a ransomware variant called Cephalus, which we recently detailed in a blog post.
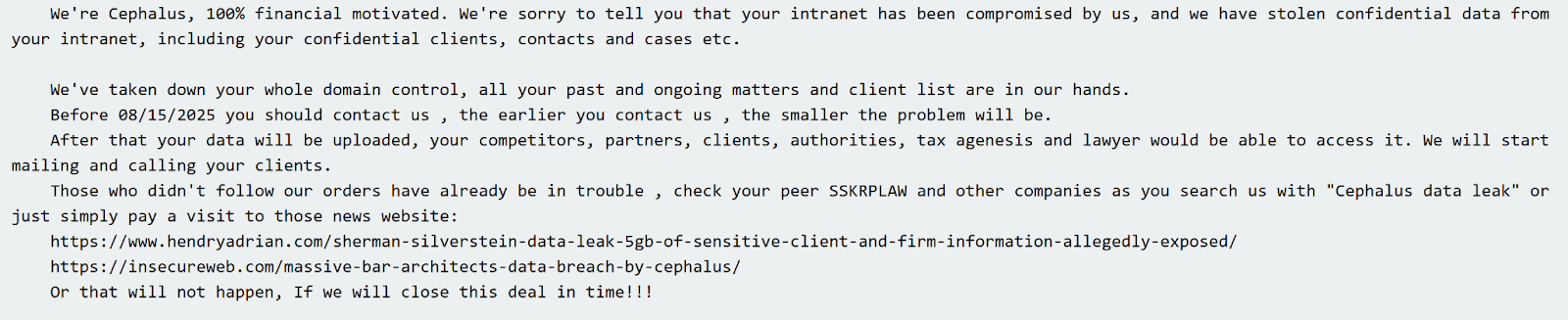






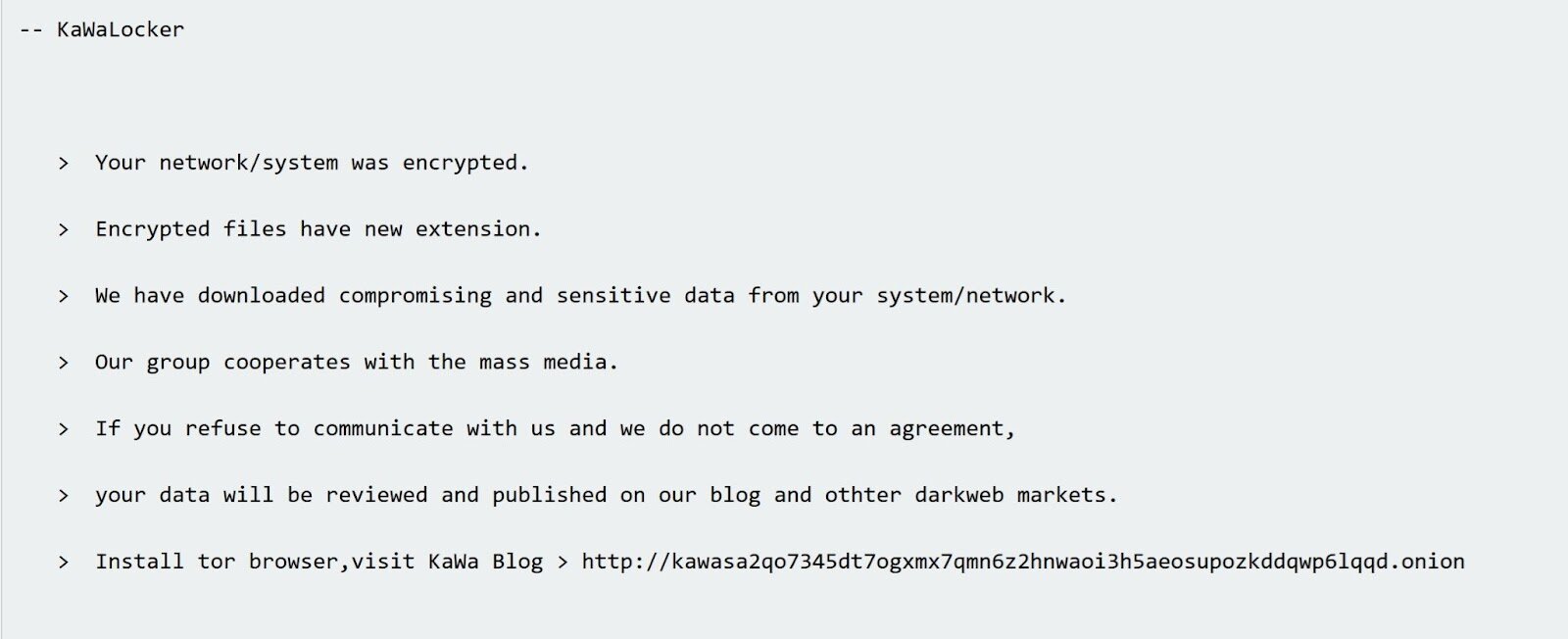 KawaLocker ransom note seen in incidents
KawaLocker ransom note seen in incidents
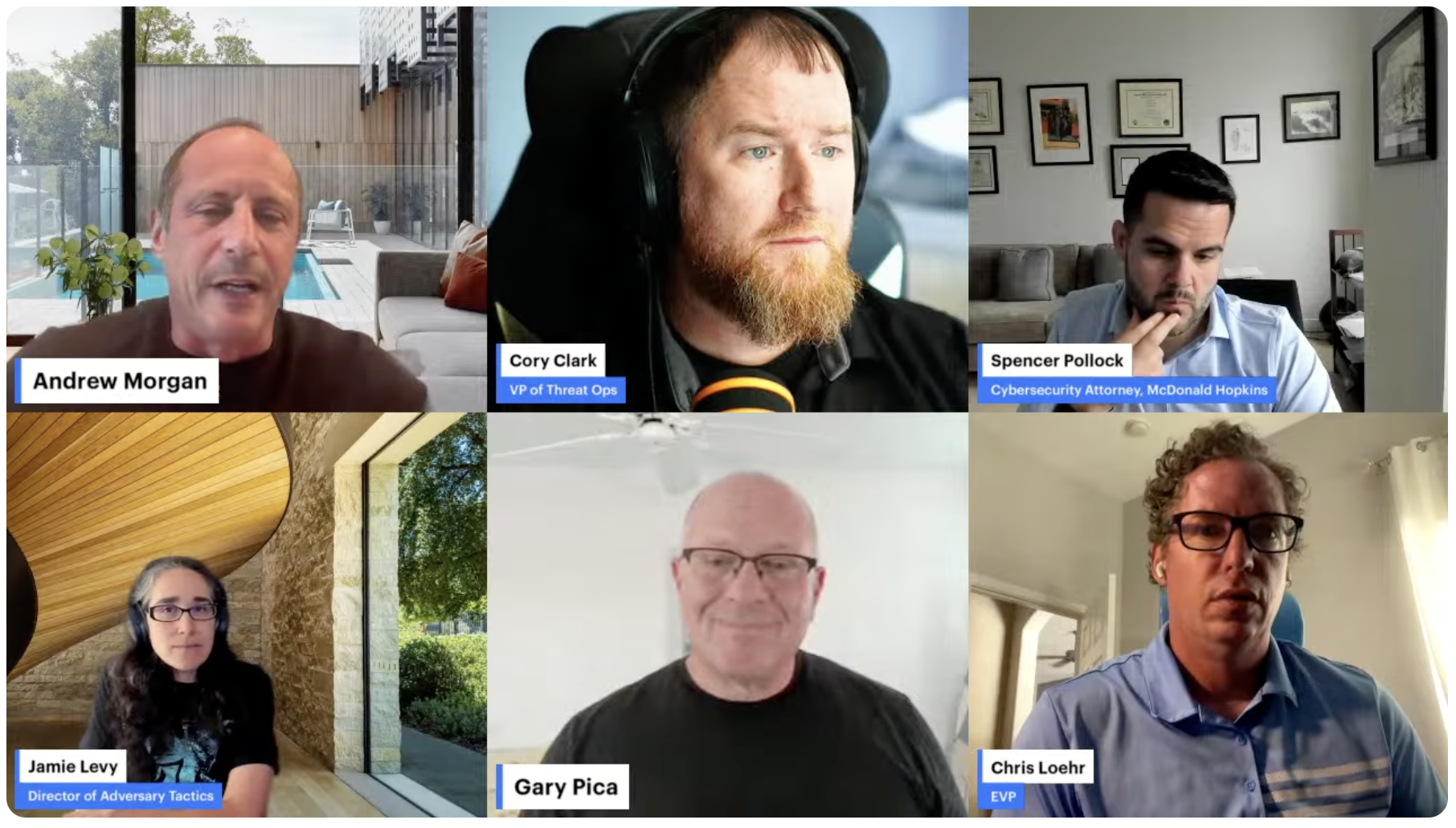
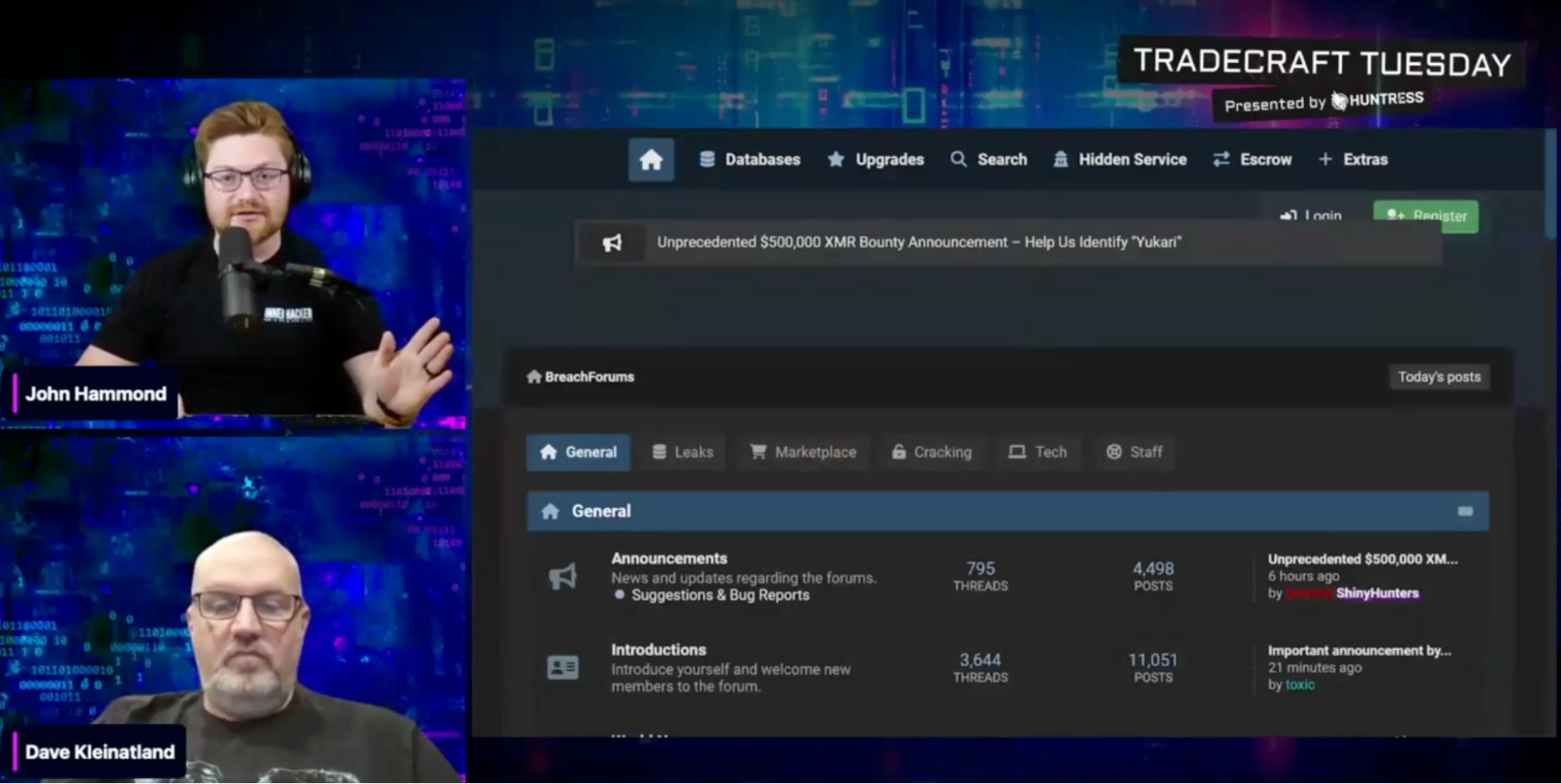
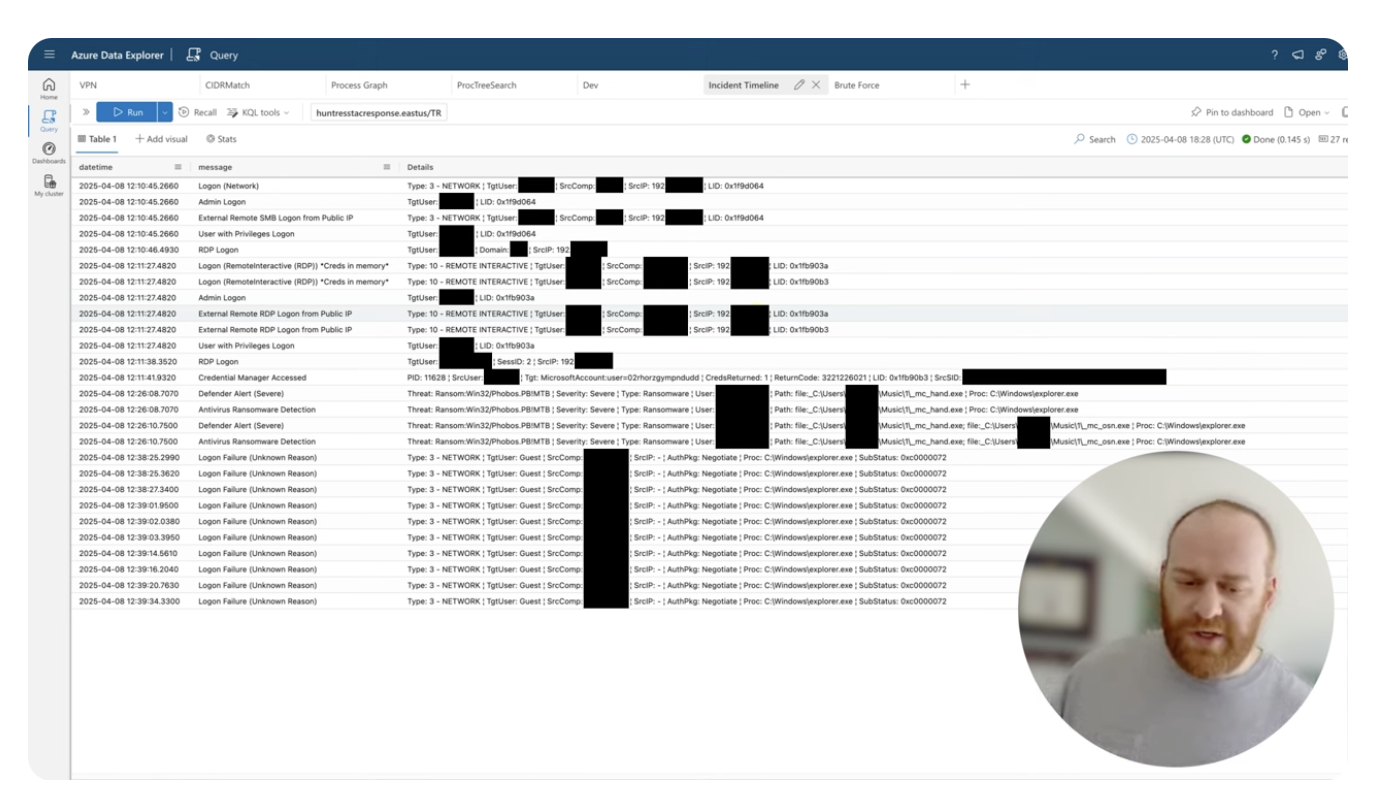 The latest SOC incident walkthrough video from Tactical Response
The latest SOC incident walkthrough video from Tactical Response
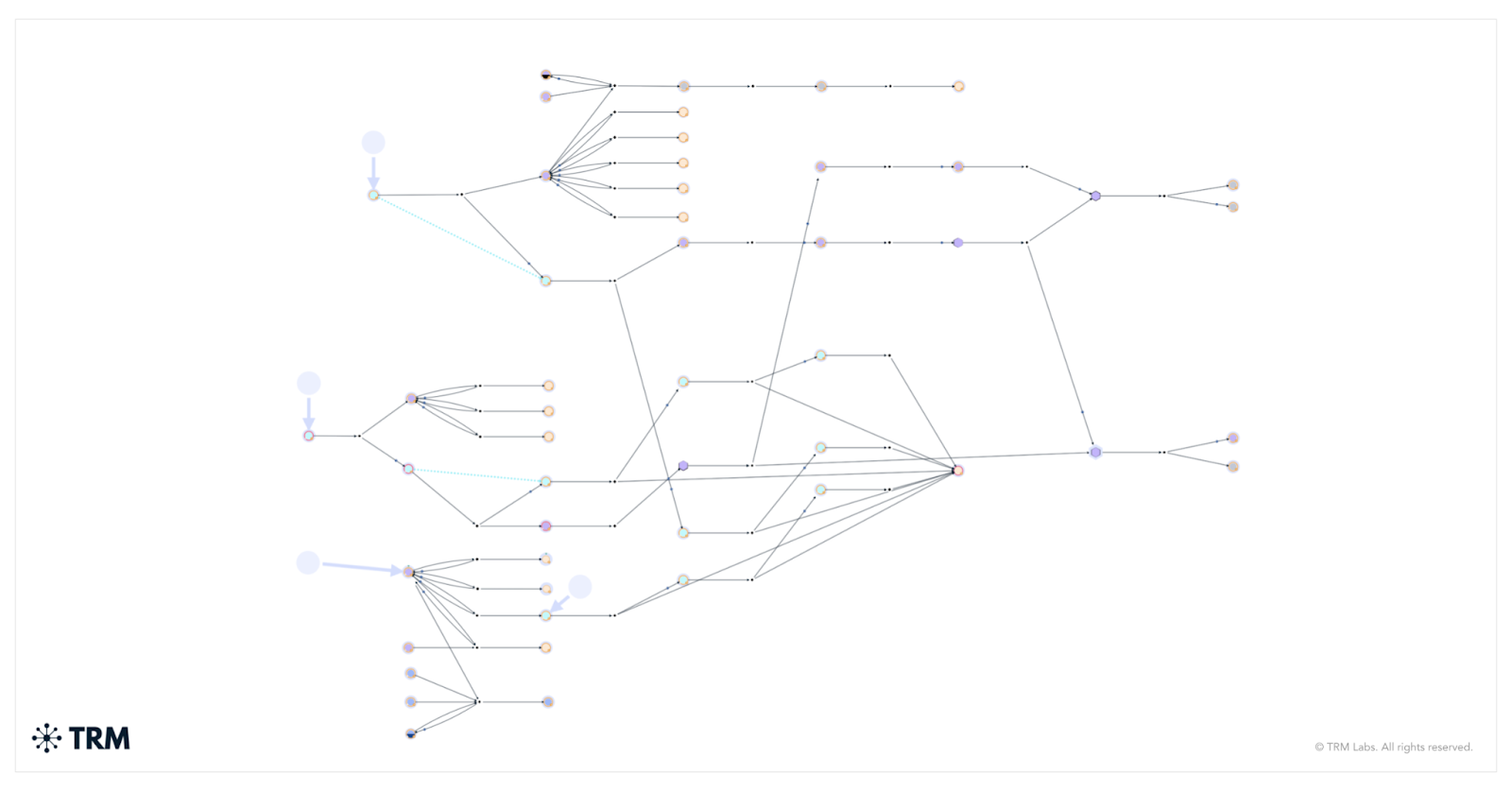 A distribution flow chart for Bl00dy ransomware groups' laundering services in Ghana
A distribution flow chart for Bl00dy ransomware groups' laundering services in Ghana An illegal power station in Angola that powered fraudulent cryptocurrency mining centers
An illegal power station in Angola that powered fraudulent cryptocurrency mining centers