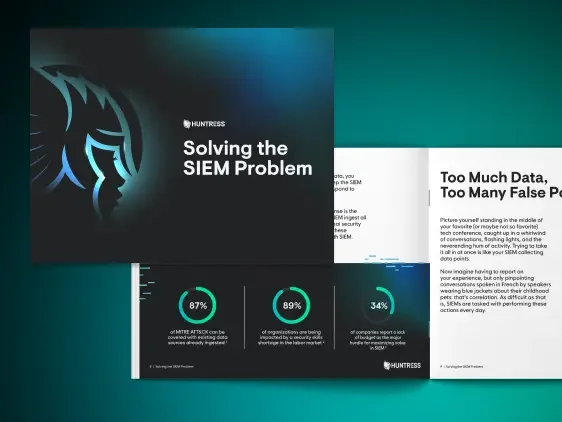
Solving the SIEM Problem: A Hard Reset on Legacy Solutions
Every day, we’re bombarded by massive amounts of information. From daily news and stocks, to the latest box scores, keeping up with it all is a full-time job. Security Information and Event Management, or SIEM for short, was designed to make sense of it all. Centralizing logs is at the heart of what SIEM was meant to do. Come join us as we explore the origins of SIEM, the challenges it faces today, and how Huntress filters out the noise without compromising security.


Every day, we’re bombarded by massive amounts of information. From daily news and stocks, to the latest box scores, keeping up with it all is a full-time job.
Your IT infrastructure is no different. Millions of logs circulate through your IT systems, including firewall data, system logs, and endpoint events to name a few.
Security Information and Event Management, or SIEM for short, was designed to make sense of it all. Centralizing logs is at the heart of what SIEM was meant to do. But does just having a SIEM and organizing your data help if there’s still too much noise to make sense of it all?
Explore the origins of SIEM, the challenges it faces today, and how we’ll filter out the noise without compromising security.
In this webinar, we'll dive into:
- How SIEM began: Get a deeper understanding of how SIEM started.
- Where it went wrong: Dive into the issues legacy SIEM models face.
- What needs to happen: Discover why most organizations and MSPs need a different approach to SIEM.
- How we’re changing things: We’ve heard what our partners have asked for—we’re breaking down what we’ve come up with as a community to solve the SIEM problem.
Watch and see how you can take another layer of hassle out of your security with our Managed SIEM.