
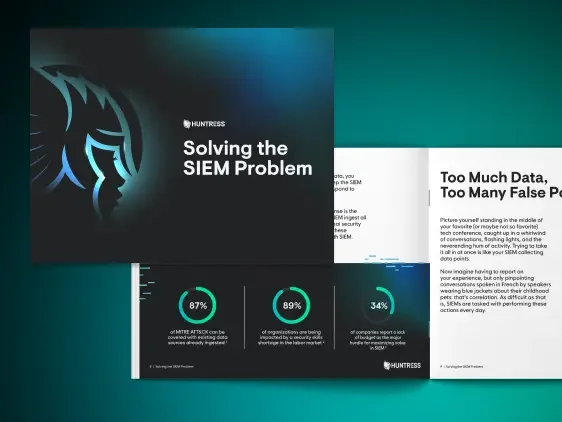
Solving the SIEM Problem
Dive into the most common problems SIEM users face and learn how to solve them. Whether you’re grappling with too many false positives, struggling to find the right expertise, or facing unpredictable costs, you’ll get the insights you need to make informed decisions about your security.


Tired of traditional SIEM solutions creating more headaches for you? You’re not alone.
While SIEMs were built to gather and correlate data and streamline your IT operations, most have become too noisy and complex to manage. From false positives to the need for specialized management—not to mention skyrocketing costs as your data intake grows—legacy SIEMs can make you feel like you’re spiraling out of control.
Don’t settle for a SIEM that doesn’t work for you. It’s time for a new approach.
Dive into the most common problems SIEM users face and learn how to solve them. Whether you’re grappling with too many false positives, struggling to find the right expertise, or facing unpredictable costs, you’ll get the insights you need to make informed decisions about your security.




