How to Crush Cybercriminals with Managed Antivirus


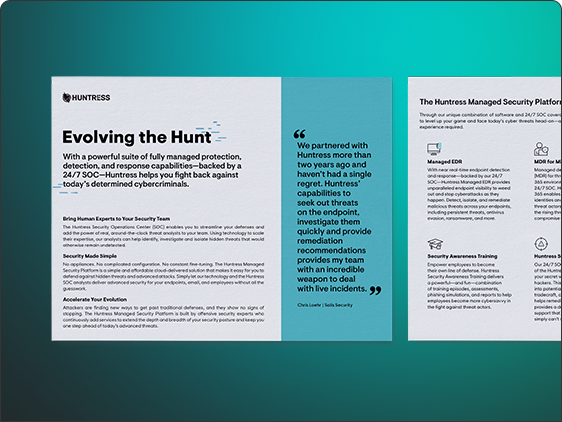
Although antivirus tools are nothing new, they may be more essential than ever when it comes to thwarting attacks aimed at SMBs. Leveraging an AV with a managed component gives an extra layer of protection against ever-evolving attacks.
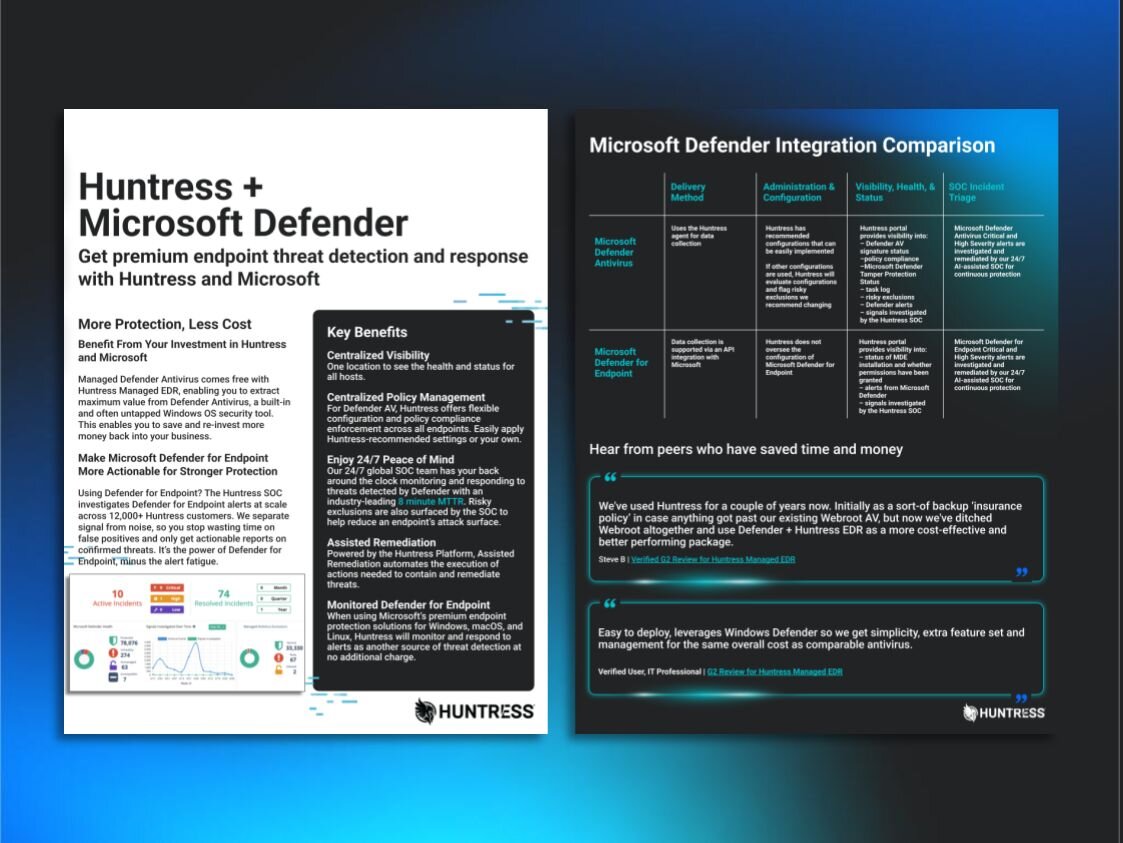
It’s been six months since we launched our Managed Antivirus service in general availability - and what a ride it’s been. Today, tens of thousands of endpoints are now protected by the top-rated Microsoft Defender and the watchful eyes of the Huntress global ThreatOps team.
Watch Kyle Hanslovan and other members of the Huntress team dive into the story of Huntress Managed Antivirus, exploring the types of threats we’ve seen in the wild, the shenanigans that have been thwarted and how IT teams are seeing more value from their Huntress investment by deploying Managed Antivirus.
We’ll cover real-world examples of how Huntress partners have made the switch to Microsoft Defender. Plus, get a sneak peek of what’s next for the platform from Huntress product owners.