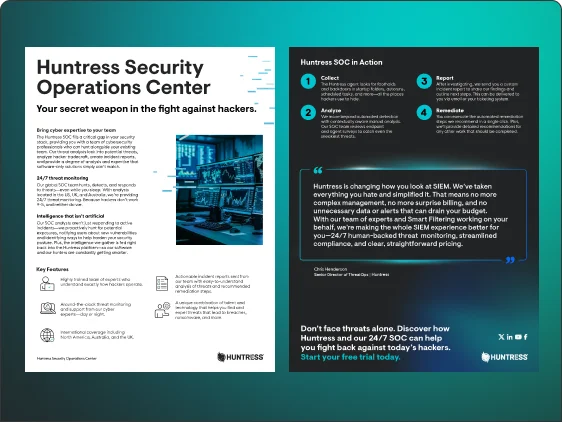
Evolving the Hunt Datasheet
See how we help SMBs and mid-market organizations fight back against threat actors.



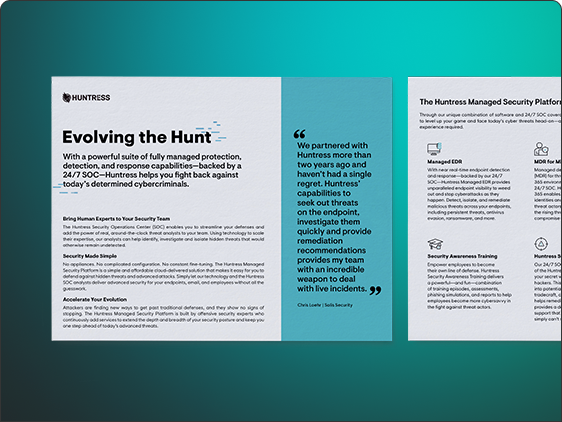
There’s a lot going on in a day – managing team operations, providing top-notch service to end users, staying on top of the latest tech news and… oh yeah.
Protecting your networks from hackers and attackers.
It’s game over when hackers get into your unprotected systems. But when you decide to fight back and play their game – the hunt evolves.
See how we help SMBs and mid-market organizations fight back against threat actors with this datasheet.
[PH] Learn More About Phishing
[PH] Huntress delivers everything you want from a security tool, all designed with the unique needs of outsourced IT and security teams in mind.
[PH] Phishing attempts can show up as messages from your bank, your boss, your utility providers, or even the government. One click from one user can compromise an entire network and inadvertently let hackers deploy ransomware, steal information, or worse.
[PH] The median time it takes for a user to click a link and enter information is less than 60 seconds. With a turnaround time that quick, it's no wonder phishing is one of the preferred methods used by hackers. (2024 Verizon Data Breach Report)