Help Has Arrived: Unleash Your Microsoft Security's Full Potential (APAC)
When it comes to security, Microsoft is a great ally to have in your corner. But without the right team and expertise, you might not be using its full potential. That’s where we step in. Join us for an insightful webinar to learn how our Managed Endpoint Detection & Response (EDR) and Identity Threat Detection & Response (ITDR) solutions are breathing new life into Microsoft security for organizations.


Watch the Webinar
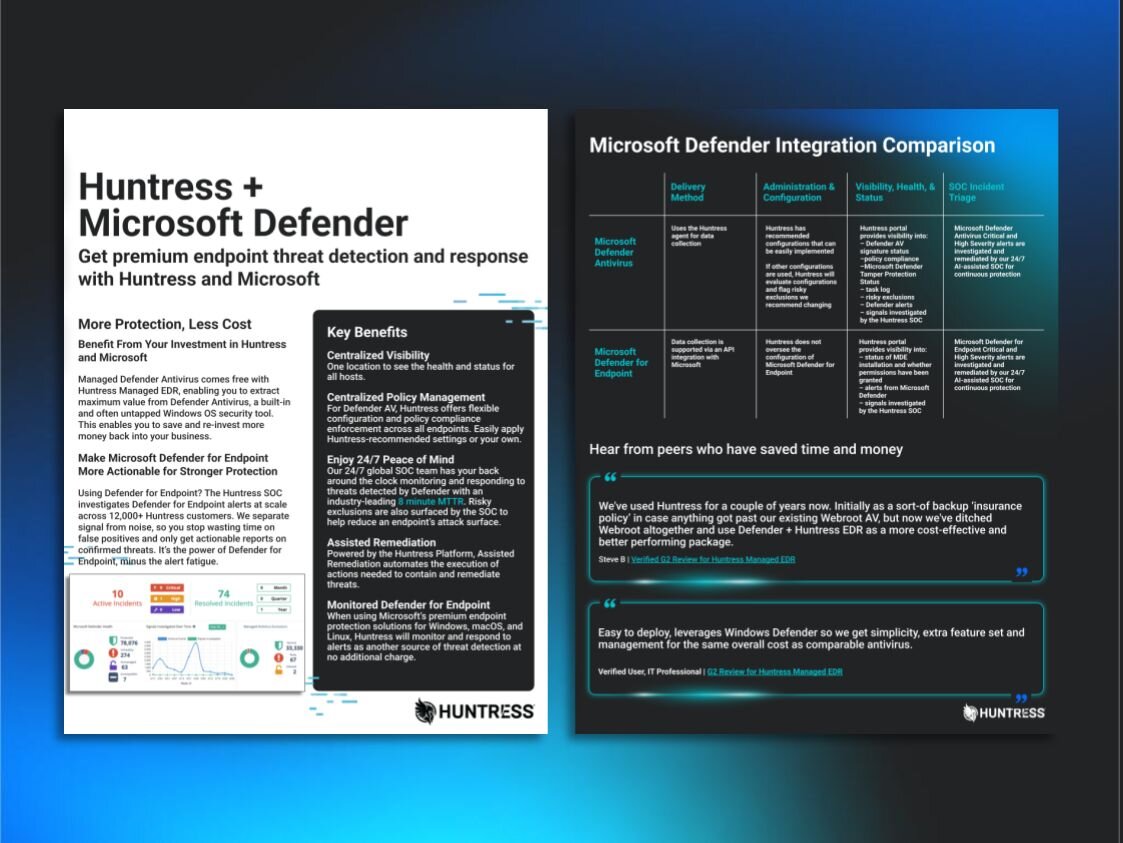
You’ll see how Huntress, now a Verified SMB solution provider within the Microsoft Intelligent Security Association (MISA), integrates seamlessly with your Microsoft security tools to bring an extra layer of real-world, 24/7 protection to your Microsoft stack.
You’ll see how Huntress, now a Verified SMB solution provider within the Microsoft Intelligent Security Association (MISA), integrates seamlessly with your Microsoft security tools to bring an extra layer of real-world, 24/7 protection to your Microsoft stack.You’ll learn about:
- Unlocking potential: Understand the hurdles organizations are facing in getting the most out of their Microsoft security tools.
- Real stories, real solutions: Explore real-world use cases where our platform has helped SMBs and MSPs maximize their Microsoft 365 security.
- Huntress + Microsoft, better together: See how Huntress integrates with Microsoft Defender for Endpoint, Windows Defender AV, Microsoft Entra, and Microsoft 365 and provides the crucial management layer.