Battling Business Email Compromise
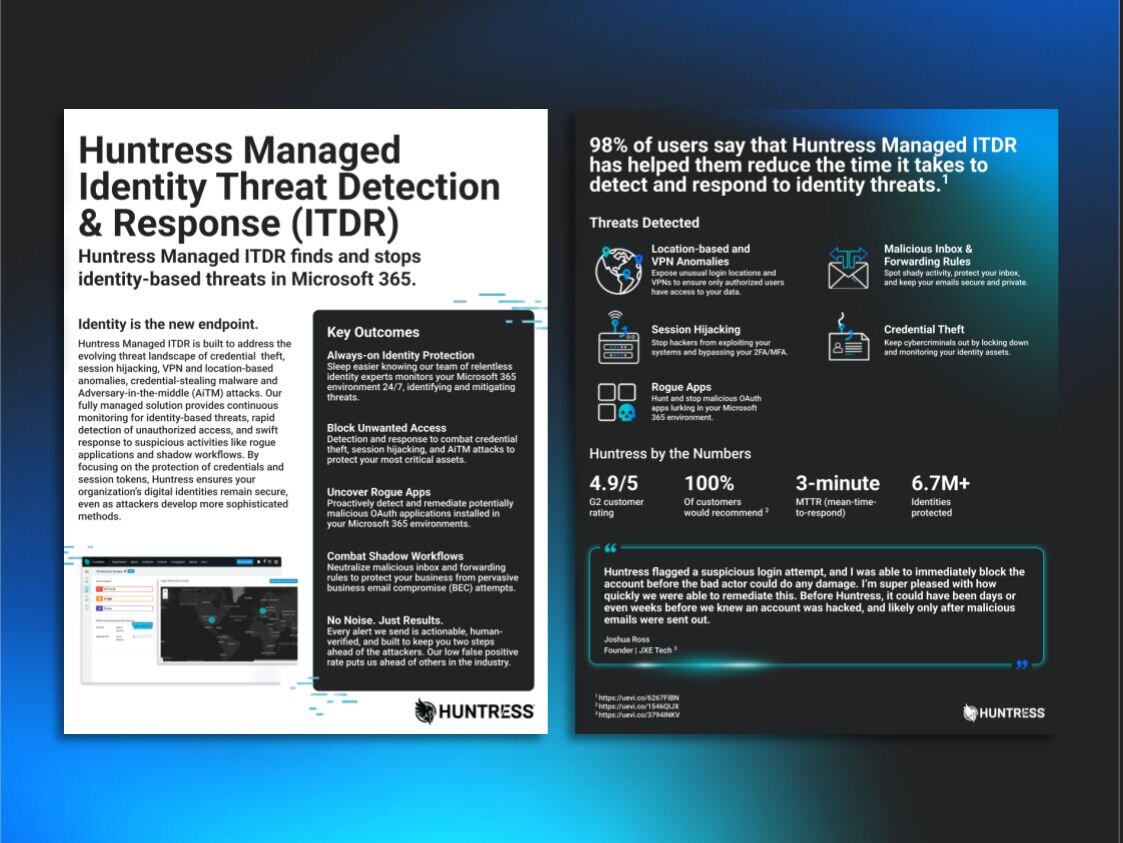
Attackers have a ton of ways to break into Microsoft 365 mailboxes—but they love the hell out of business email compromise. That’s why we’re teaming up with Mesh Email Security to see how these sketchy tactics work.
Mesh will cover techniques for detecting, blocking, and deleting impersonation emails, and we’ll go over the ways to detect compromised Microsoft 365 accounts before they do any damage. Plus, we’ll be getting into the details of all the ways payment redirection scams can play out.
Sound like a good time? Watch now.


Watch the Webinar
[PH] Learn More About Phishing
[PH] Huntress delivers everything you want from a security tool, all designed with the unique needs of outsourced IT and security teams in mind.
[PH] Phishing attempts can show up as messages from your bank, your boss, your utility providers, or even the government. One click from one user can compromise an entire network and inadvertently let hackers deploy ransomware, steal information, or worse.
[PH] The median time it takes for a user to click a link and enter information is less than 60 seconds. With a turnaround time that quick, it's no wonder phishing is one of the preferred methods used by hackers. (2024 Verizon Data Breach Report)