Attackers are constantly on the prowl, scoping out vulnerabilities of network-connected devices in your systems. These devices—laptops, desktops, servers, IoT, and more—are like unlocked doors waiting for threat actors to stroll through. And here’s the kicker: many of these vulnerabilities are shockingly common and easily preventable.
Let’s break down the weaknesses we most frequently track across three million endpoints (not a bad sample size!) and what you can do to patch those holes before a threat actor sneaks in and wreaks havoc.
Remote Desktop Protocol (RDP): The open back door
Remote Desktop Protocol is a prolific protocol used for remote connectivity, but it’s also one of the most common ways threat actors gain access to endpoint devices. In fact, up to 70% of organizations have RDP exposed to the public internet. Think of an exposed RDP connection as leaving a spare key under the doormat—while not quite in plain sight, it’s a pretty obvious place to look if you want to get inside.
Here’s an example of what happens:
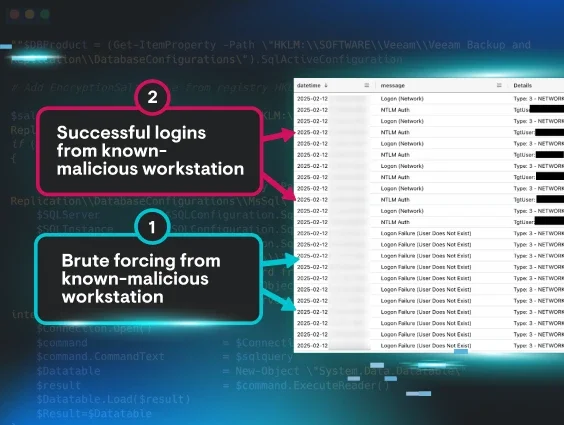
Attackers often use brute force attacks on RDP, cycling through password options until they unlock a login session. Once the initial intrusion is established, they usually don’t waste time dropping malware and trying to move laterally across your network.
An example of event logs showing a successful use of brute force
What you can do:
-
Don’t expose RDP to the public internet unless you really need to.
-
Be a stickler with admin rights. Think about who actually needs access to do their job.
-
Don’t rely on passwords—it’s old school (and way too risky). Enforce multi-factor authentication (MFA) for RDP sessions.
-
Don’t slack on Windows security configurations. Defaults won’t cut it against attackers who want a piece of your network.
-
Be vigilant for suspicious activity, like logins from unknown IP addresses.
Phishing attacks: Don’t take the bait
Email phishing is a classic cybercrime strategy, and some things just never go out of style. Every day, phishing emails land in inboxes and a staggering number of victims still fall for social engineering scams. This isn’t a new tactic by any stretch of the imagination, but threat actors continue to rely on it because it works—phishing accounts for 15% of all data breaches.
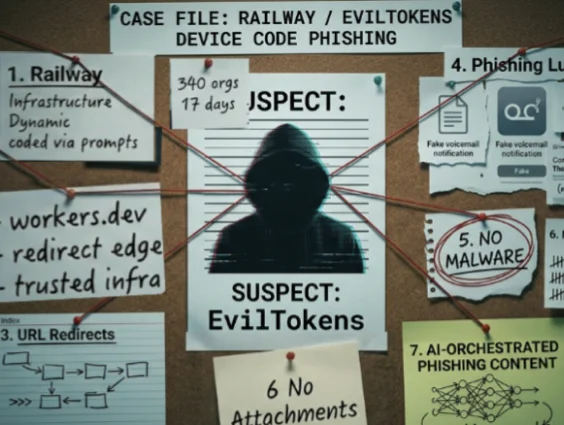
But what’s more alarming about phishing attacks these days is that they’re getting craftier, especially as threat actors turn to generative AI tools to fast-track their social engineering tactics. From expertly mimicked branding to fake invoices with urgent requests, hackers have leveled up their game to trick victims into clicking malicious links or giving up personal details to “customer service” over the phone. Phishing isn’t just email anymore—hackers will use any type of communication mechanism: email, text, phone calls, voicemail, QR codes, or any combination of these approaches.
The most impersonated brands in phishing incidents. Source.
Here’s an example of what happens:
Let’s take a look at email phishing. When an employee clicks on a malicious link in a phishing email, they might unknowingly hand over sensitive credentials to an attacker or install malware on their system. Or, even worse, they may detonate a ransomware attack. Phishing often uses pressure tactics to prey on victims’ emotions to get a quick response. The attackers walk away with access to your network and sensitive info while leaving you with the mess. It could become an even bigger mess than you’ve bargained for if the attacker gains persistence to endpoints and you don’t immediately find the damage.
Got an email asking for sensitive info? Don't respond directly to the sender to avoid falling into the attacker’s trap.
An example of a malicious fake thread email phishing attempt
What you can do:
-
Get your organization smart on phishing tactics! Regularly scheduled security awareness training (SAT) can make users less likely to jump on sketchy requests. You want their "spidey senses" tingling when weird emails show up!
-
Use MFA because it can reduce the damage if (when) credentials are compromised.
For more on how attackers use phishing to access your endpoints, check out Tradecraft Tuesday: "Phishing in the Fast Lane."
Remote monitoring and management (RMM) tools: The double-edged sword
RMM tools are double-edged swords. On the one hand, they help IT admins, managed service providers (MSPs), and system admins monitor, manage, and troubleshoot fleets of computers with ease. On the other hand, when left unsecured (as they often are), RMM tools are an easy entry point for attackers to hit your endpoints hard. According to Huntress' 2025 Cyber Threat Report, 17.3% of all remote access methods originated from RMM abuse. Threat actors like to blend in and hide in plain sight, and legitimate RMM tools are an easy way to do this.
Top abused remote access tools. Source.
Here’s an example of what happens:
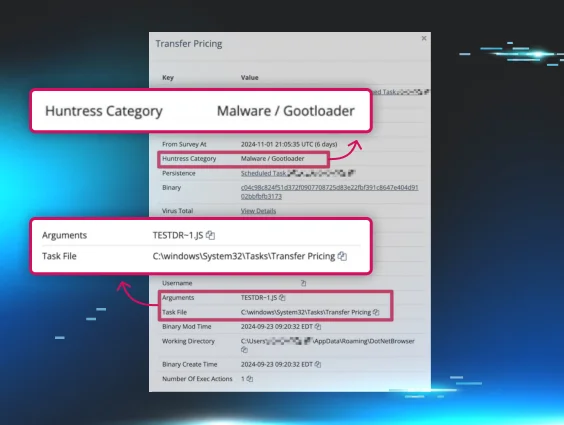
Attackers abuse RMM software and tools to gain unauthorized remote access to compromise devices. Whether they use pre-existing RMMs or install their own, they can potentially control every connected device across your organization, lurking under the auspices of legitimate software. RMM attacks are dangerous because there’s always a risk that attackers will fly under the radar of your detection systems, moving laterally and gaining persistence without even dropping malware.
There are generally two ways attackers abuse RMMs. First, they can hijack or abuse existing software by exploiting outdated, unpatched, or misconfigured tools, or by stealing credentials to log in remotely to RMM tools. Second, they can deploy and install the attacker’s preferred RMM tool via social engineering or portable executables.
Portable executables are notable for their ability to skirt around admin privileges and full software installation, giving attackers local user access. Even if a risk management control is supposed to block or audit the RMM software on the network, it doesn’t matter because portable executables don’t require admin privileges, giving the threat actor a free pass into your network. That’s the stuff of nightmares because threat actors drop into your environment undetected without using malware.
Your RMM tools should make endpoints more secure, not less. Tighten up those settings and keep potential bad actors out.
Example of legitimate RMM tool compromise
What you can do:
-
Use role-based permissions. They are king. If you’re not on the guest list, you don’t get access to the RMM software party.
-
Update and apply patches to RMM software to address vulnerabilities and bug fixes.
-
Monitor activity logs for unusual activity. Unauthorized installs or funky logins should be a red flag.
-
Know what types of RMM tools are supposed to be in your network. Audit, track, and monitor so that an unauthorized instance stands out.
For more on keeping RMM tools secure, check out:
-
Think Your ScreenConnect Server Is Hacked? Here’s What To Look For.
-
Vulnerability Reproduced: Immediately Patch ScreenConnect 23.9.8
Unpatched software: An open door to your network
Unpatched software is the cybersecurity equivalent of leaving your front door open. Yes, the breeze might be nice, but you probably wouldn’t leave it wide open most of the time. It's too risky. Your pets or kids can get loose, outdoor critters can make themselves at home (who wants raccoons in their kitchen?), and worse, thieves can just walk in.
If you wouldn’t expose your physical environment to this type of risk, why would you allow it virtually?
Here’s what happens:
Software vendors release patches for different reasons, but often to fix publicly known security vulnerabilities, usually referred to as CVEs. Attackers use this public information to target outdated software and systems. A single instance of an unpatched flaw is an opportunity for an attacker to drop ransomware or malware, or to pull off data breaches. When a new vulnerability drops, you're up against the clock to get your systems patched before a threat actor takes advantage of you.
If you’re not updating your software regularly, your endpoints are at unnecessary risk. The door is wide open for unwanted guests. It’s that simple.
Example of PowerShell script exploiting CVE-2023-27532 in outdated Veeam software.
Patch it up:
-
Set up automatic updates wherever possible. No excuses.
-
Keep a regular patch management schedule and stick to it.
-
Have a battle plan for patching prioritization, since not all vulnerabilities are created equally.
Stay proactive, stay protected
Endpoint vulnerabilities don’t have to be your Achilles’ heel—they’re manageable with the right strategies and tools. Phishing training, endpoint detection and response (EDR) solutions, RMM audits, patch schedules, and strong authentication measures are just the start.
It’s time to take action and secure your systems before attackers target them. Don’t leave it to chance. Examine your cybersecurity tools, train your team, and implement endpoint protection solutions that fit your setup.
There’s no better time than now to fire up Huntress for better endpoint security. Sign up today for your free trial.