Eliminate Active Threats and Fight Hackers with Advanced Mac Endpoint Security
Get Managed EDR for macOS today and handle hackers with confidence. Book a demo to see the difference Huntress can make in your security defenses.
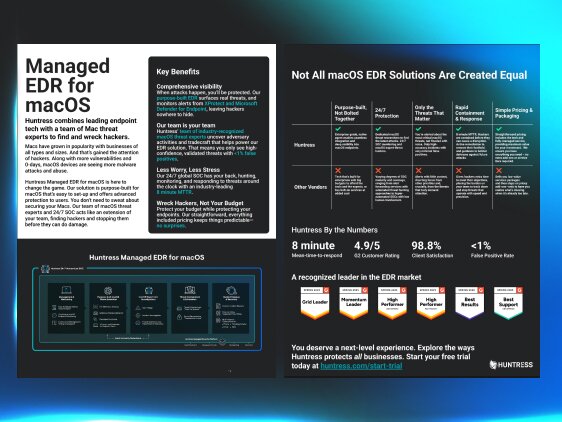
Combining purpose-built endpoint technology with a team of macOS threat experts, Huntress Managed EDR for macOS uncovers and stops adversaries before they can cause damage.



Huntress Huntress Managed EDR is tailor-made for macOS threat challenges, offering advanced protection where it counts. It's easy to set up, and with our 24/7 Security Operations Center, we're like an extension of your team looking out for hackers and keeping you safe without you having to sweat the security stuff.

We don’t believe in only playing defense. We take the battle straight to the attackers. Our team is stacked with industry-recognized macOS experts who are constantly researching and uncovering the latest macOS threats. Plus, our SOC analysts are always on their toes, ready to strike at hackers before they even know what hit them.


Take a look under the hood at the features that make protecting your systems with Managed EDR for macOS easy.

EDR for macOS is built for our SOC to quickly detect, contain, and evict attackers. Alerts from XProtect and Microsoft Defender for Endpoint are also monitored providing even more threat detection coverage.
We’re your team of macOS threat experts, protecting your endpoints from attacks. Our SOC analysts and threat hunters are watching for hackers 24/7.
With an industry-leading MTTR of 8 minutes, the Huntress SOC finds and stops hackers fast, before they can cause damage.
You're probably wondering, "What's in it for me?" We understand. Let's get straight to the point and highlight what you'll gain from our service—and just as importantly, what you won't be dealing with, like endless alerts and false positives.
Rest easy knowing your macOS endpoints are being monitored around the clock.
Swiftly pinpoint hard-to-detect threats tailored to exploit macOS blind spots.
Act only on the threats that pose a real risk to your operations.
Preemptively stop attacks before they can cause irreparable damage.
We’ll focus on the threats. You focus on other priorities.
Enhance your security capabilities without breaking your budget.

Lots of companies say they protect macOS systems, but not all of them can back it up. We're all about calling BS where we see it, let’s take a look at what really sets our solution apart.

















As the use of Macs has grown in popularity with businesses of all types and sizes, it’s gained the attention of hackers. An increased focus by hackers combined with an increasing number of vulnerabilities means Mac endpoints are ripe for attack and abuse.
Get up-to-speed on the threats Mac endpoints face, and how Huntress Managed EDR is the solution you need to protect your business and wreak havoc on hackers.