In the past month, several high-profile cybersecurity busts have targeted notorious threat actors, bringing key victories for law enforcement. On July 8, the U.S. Justice Department arrested Xu Zewei, a 33-year-old Chinese national affiliated with the Ministry of State Security, for orchestrating the HAFNIUM campaign that exploited vulnerabilities in over 60,000 Microsoft Exchange servers worldwide. This campaign was the precursor to stolen COVID-19 research from multiple U.S. universities. Zewei is facing charges of wire fraud and computer damage, with up to 20 years in prison.
In mid-July, the UK's National Crime Agency arrested four young suspects, aged 17 to 20, linked to ransomware and data theft operations against major retailers, including M&S, Co-op, and Harrods. They’re being charged under the Computer Misuse Act and for blackmail. This arrest included alleged members of the Scattered Spider (UNC3944) group, and has momentarily shut down their phishing and ransomware campaigns against North American sectors. This group used tactics like push bombing and Raccoon Stealer malware, and several copycat operations continue to cause problems.
And finally, towards the end of July, Operation Checkmate, a collaborative effort involving U.S. agencies, Europol, and other international partners, seized the .onion extortion sites of the BlackSuit ransomware group. This disrupted their data leak and negotiation platforms, though the actors announced they may reemerge under the Chaos brand. Authorities stated that this was part of a multiple-phase takedown, with additional arrests and takedowns scheduled to occur in the next couple of months.
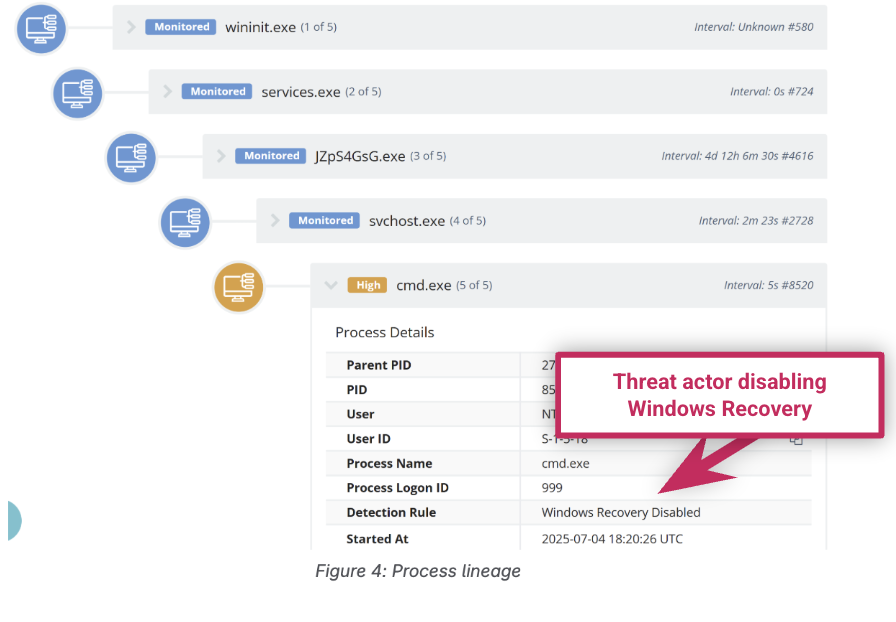







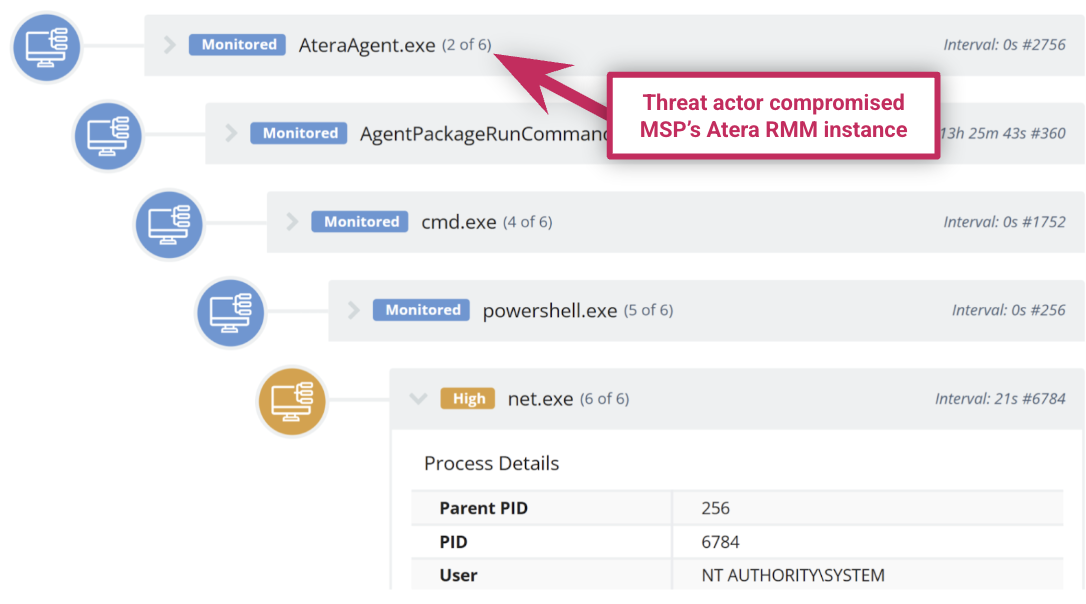 Process tree showing how the threat actor compromised an MSP Atera RMM instance
Process tree showing how the threat actor compromised an MSP Atera RMM instance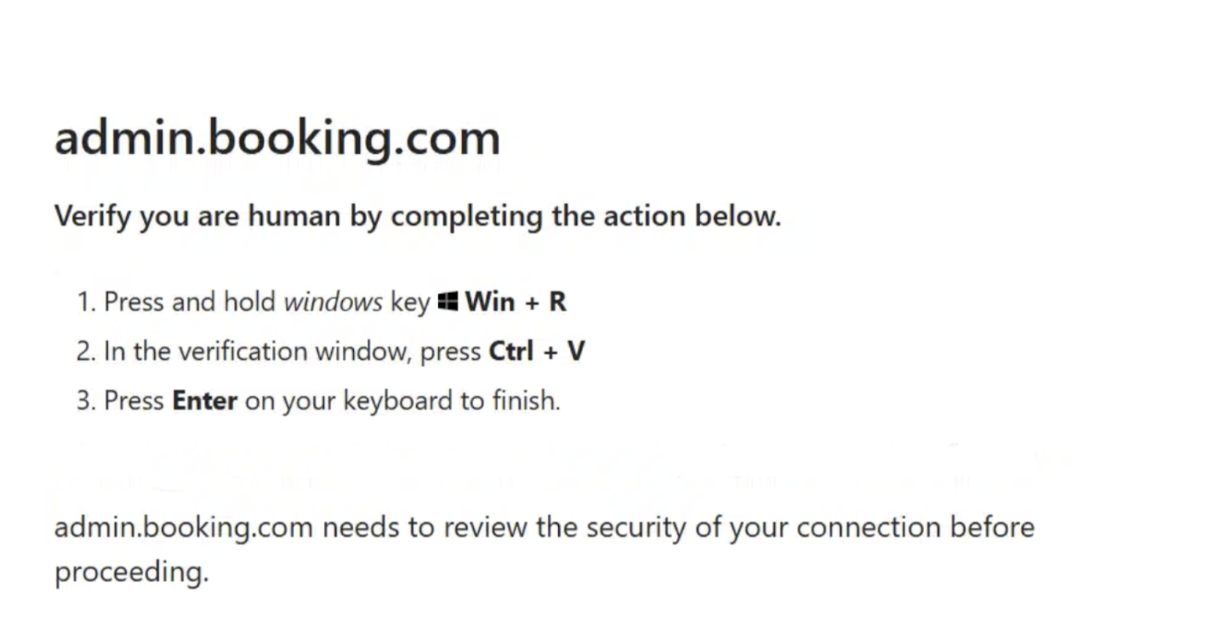 Webpage instructing the target to solve a fake captcha challenge as part of a phishing attack
Webpage instructing the target to solve a fake captcha challenge as part of a phishing attack
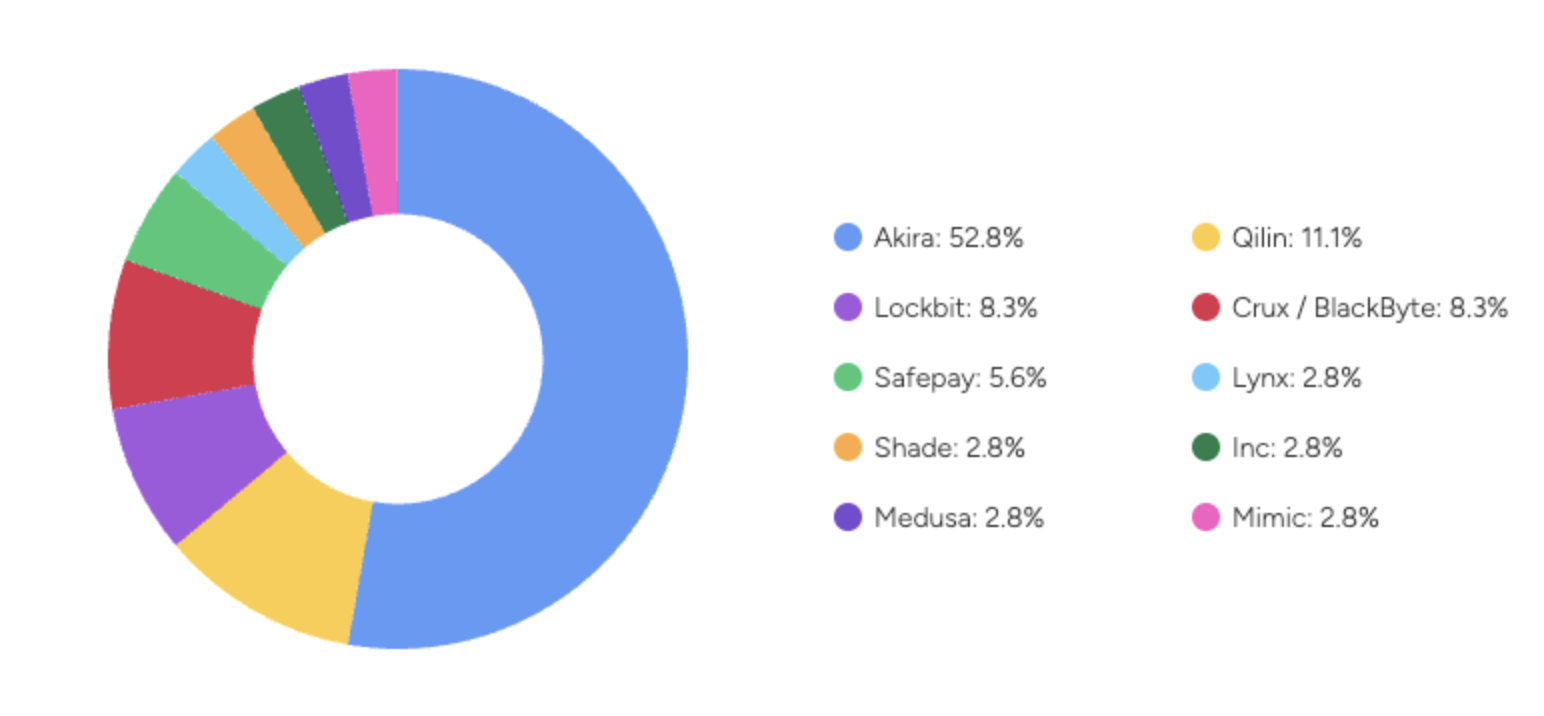 Breakdown of ransomware groups tracked by Tactical Response
Breakdown of ransomware groups tracked by Tactical Response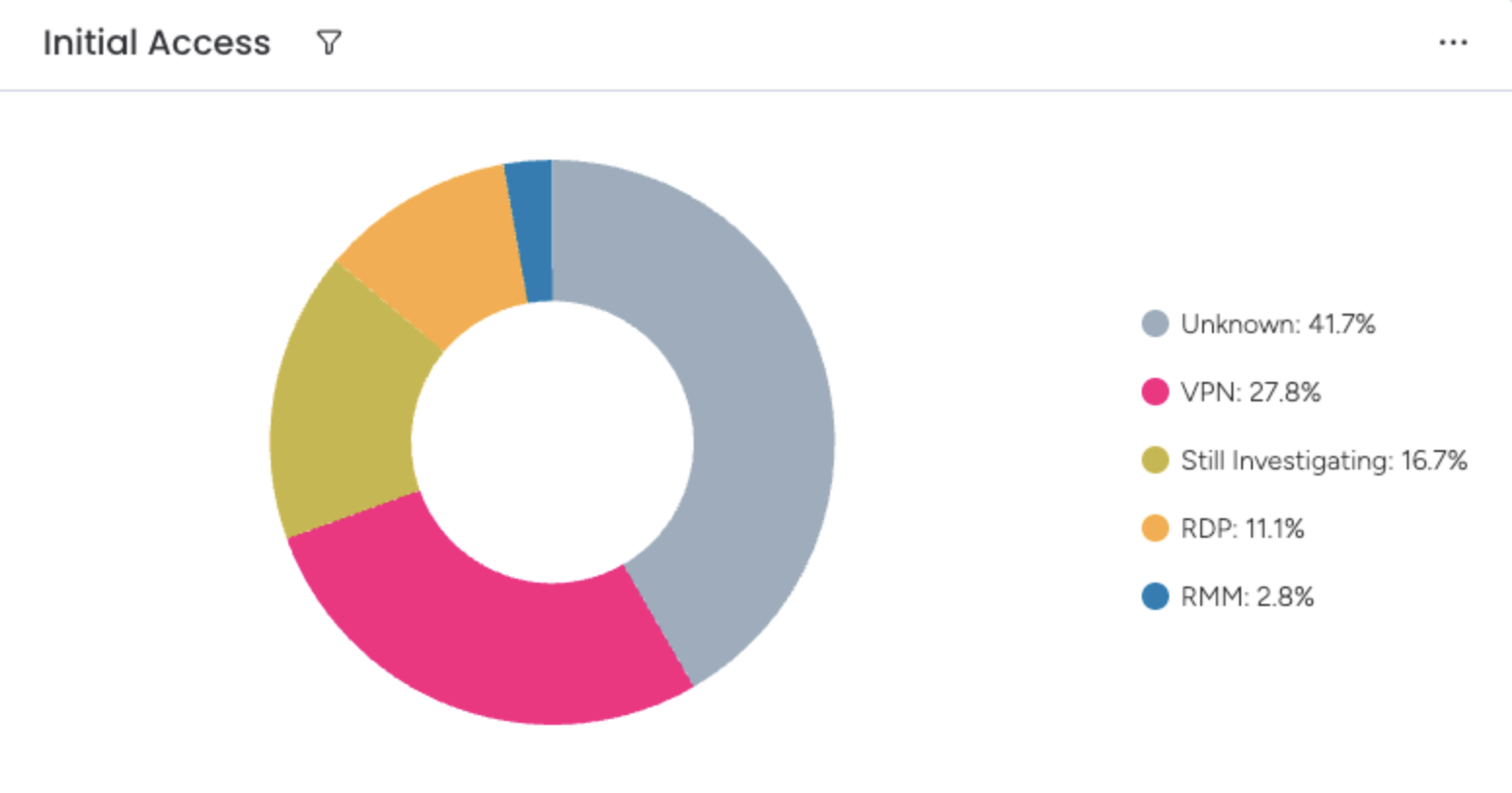 Breakdown of initial access vectors for ransomware groups
Breakdown of initial access vectors for ransomware groups
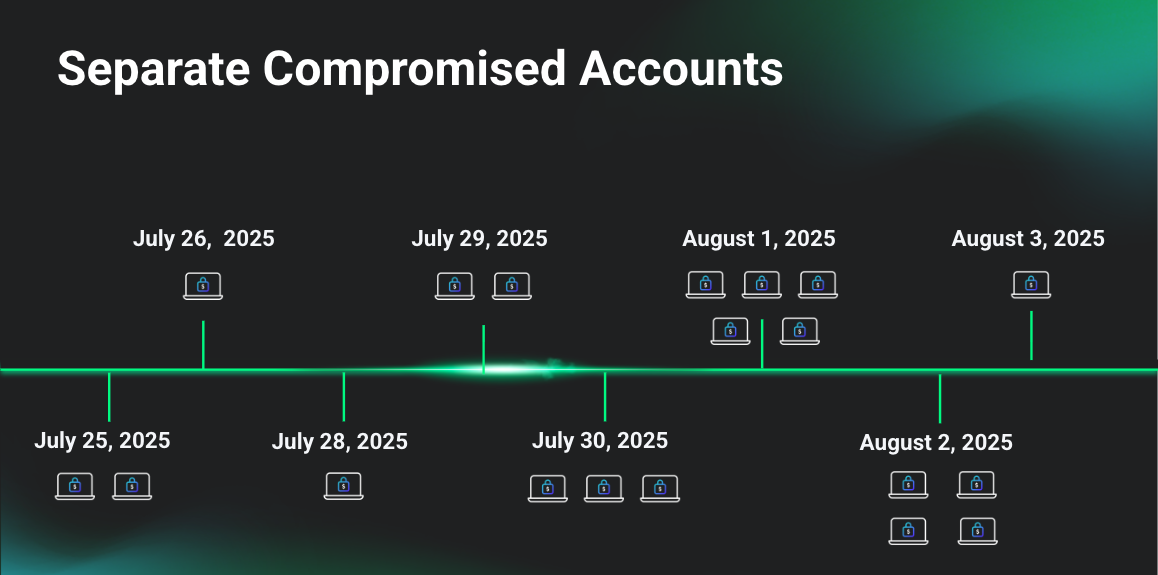 Visualization of the timeline of attacks
Visualization of the timeline of attacks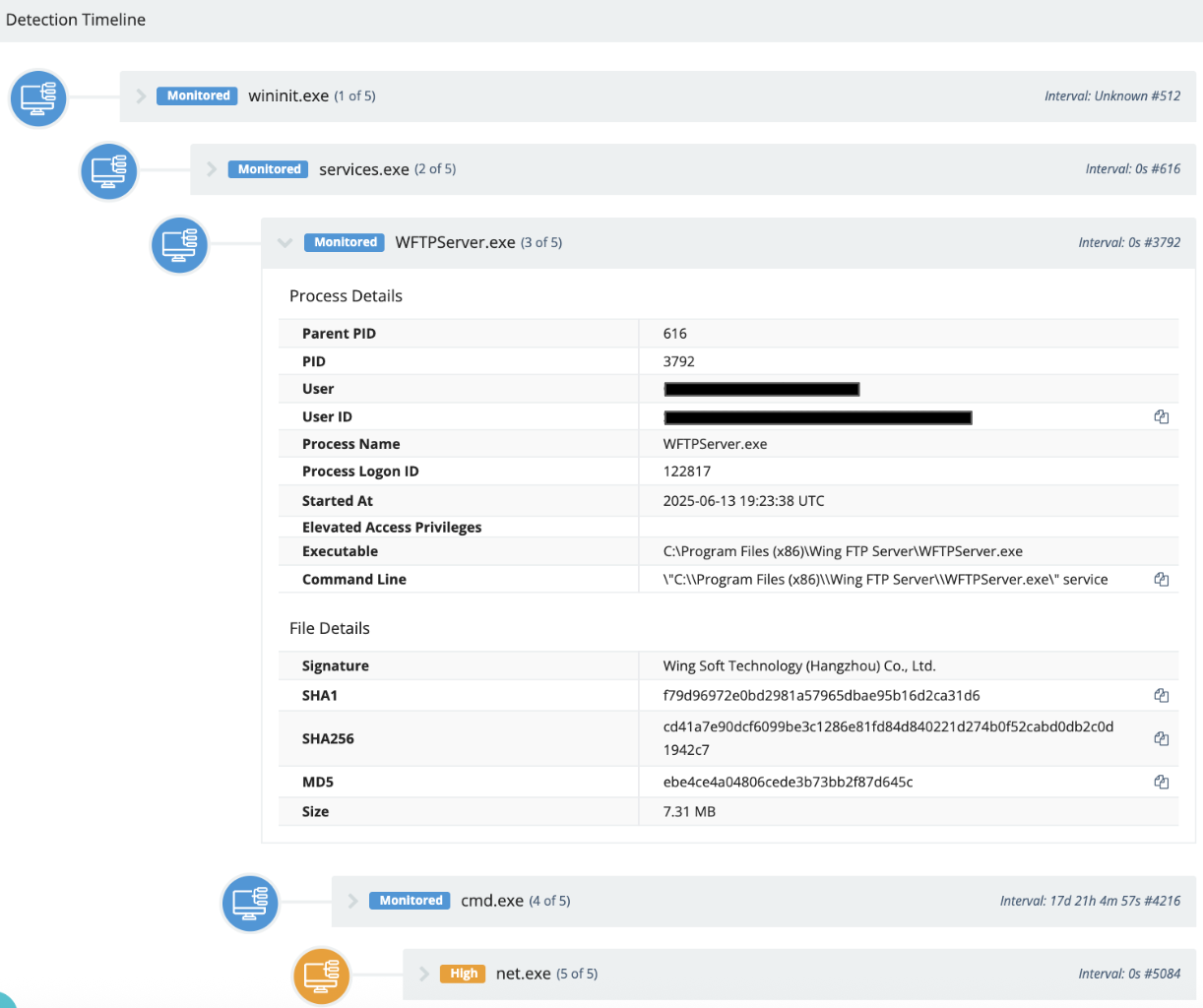 WingFTP RCE exploitation (CVE-2025-47812) seen in the process tree
WingFTP RCE exploitation (CVE-2025-47812) seen in the process tree