Huntress vs. Petra Security
See why businesses choose Huntress over Petra Security
Real-time threat detection with human-backed response
Comprehensive Microsoft 365 visibility
Flexible, customizable, and built to scale
Experience the difference of enterprise-grade security and expertise. Request a demo today or experience it yourself with our free trial.

Purpose-Built, Expert-Backed Cybersecurity


24/7 identity monitoring, session hijacking detection, malicious OAuth detection

Real-time identity threat detection and response


Detections are reviewed by expert analysts to reduce false positives

Relies on automation; small scale and unproven at volume


Fine-grained control with access rules, travel exceptions, and alert suppression

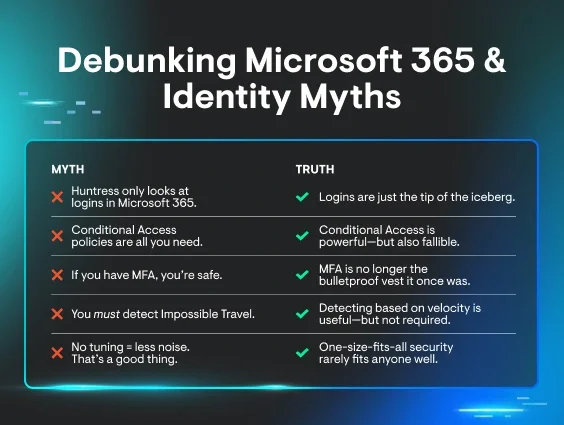
No tuning available; one-size-fits-all approach


Built for scale currently protecting thousands of tenants and millions of identities

Claims faster speed, but unproven at enterprise scale


We don’t just detect, we rapidly contain threats with an industry-leading 3min. MTTR

No published MTTR


Purposeful roadmap driven by customer needs and threat landscape

Frequent changes, but little evidence of real-world efficacy


Purpose-built EDR that delivers high-accuracy threat detection, <1% false positive rate, 24/7 monitoring with fast response

Do not have their own Endpoint Detection and Response (EDR) solution


Built from the ground up to reduce the complexity and cost of log collection, analysis, and storage. ITDR data stored in SIEM at no extra cost for one year

No SIEM offering


Training that is simple to manage with engaging, expert-backed training content built on real-world threat intelligence to reduce human risk, while helping build a security culture

No security awareness training offering


Get Next-Level Outcomes with Huntress
Purpose-built Technology, Never Bolted Together
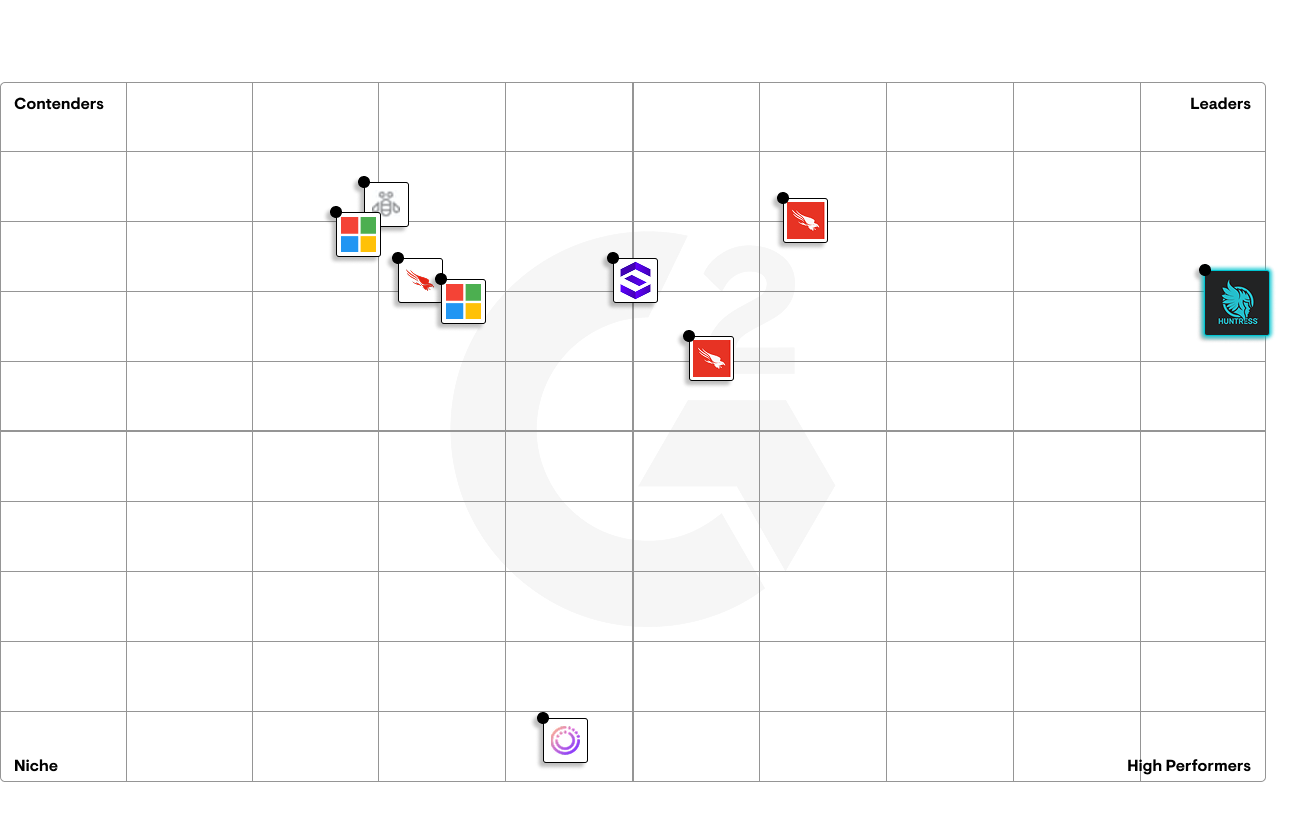
Industry-recognized Human Expertise
Fully-managed, 24/7 Coverage

Testimonials


The Huntress Managed Security Platform







Less fog, more facts