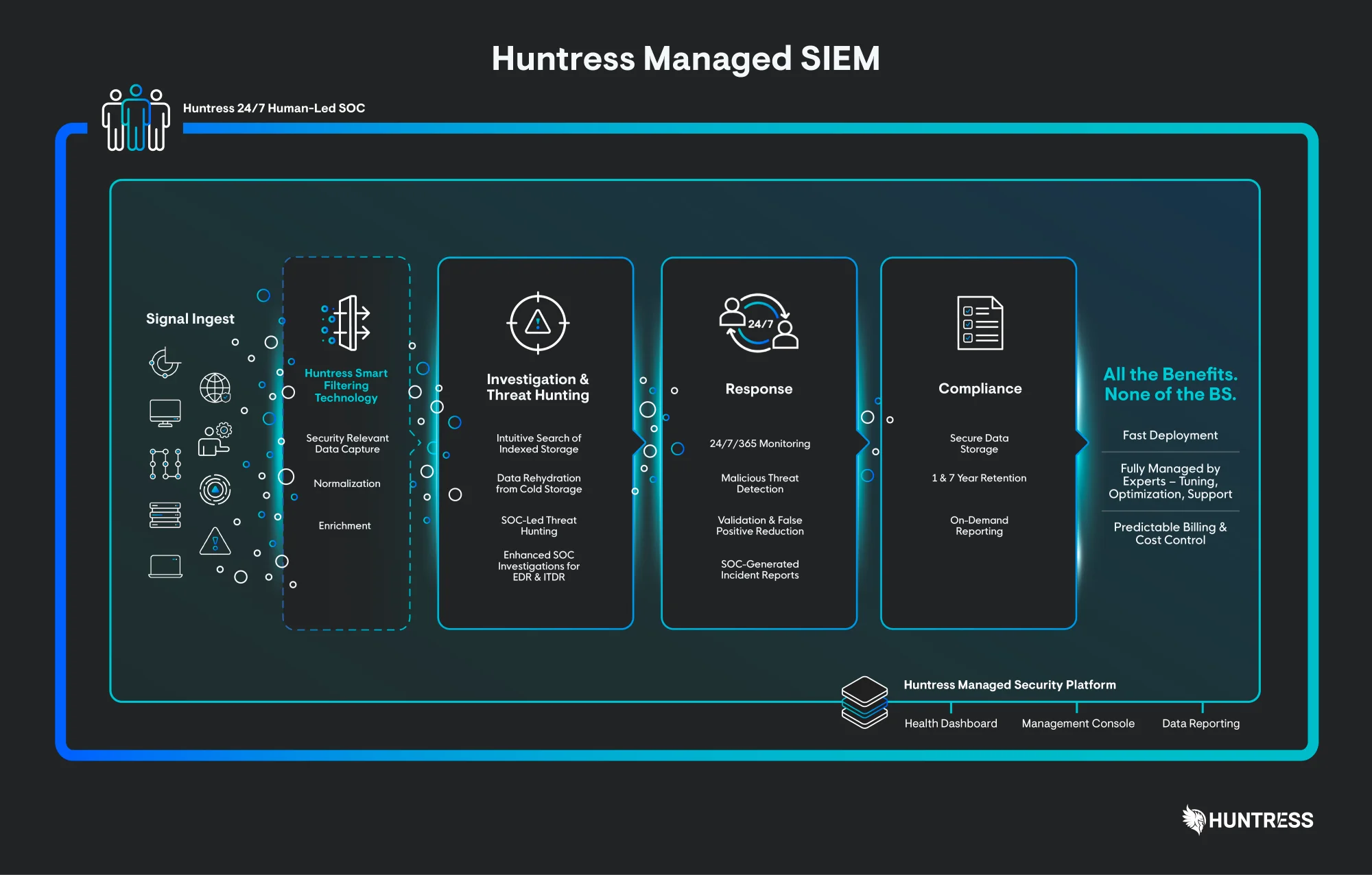
Solving the SIEM Problem
Don’t settle for a SIEM that doesn’t work for you. It’s time for a new approach.
Whether you’re grappling with excessive false positives, struggling to find the right expertise, or facing unpredictable costs, you’ll get the insights you need to make informed decisions about your security strategy.