The Advanced Encryption Standard (AES) is a powerful encryption algorithm designed to protect sensitive data through symmetric keys, ensuring confidentiality and integrity. Developed by the U.S. National Institute of Standards and Technology (NIST) in 2001, it has become the global standard for securing digital information.
Introduction
AES isn’t just a technical concept, it’s the backbone of secure communication in today’s digital world. Trusted by governments, businesses, and individuals alike, AES is used to encrypt everything from classified files to everyday online transactions. But what makes it so reliable, and how does it work? Explore its history, functionality, and applications, revealing why AES remains a critical tool for safeguarding modern digital infrastructures.
A brief history of AES
The origins of AES can be traced back to the need for a stronger encryption system to replace the aging Data Encryption Standard (DES). DES, once a widely used encryption protocol, had become increasingly vulnerable to brute-force attacks as computing power advanced.
Recognizing the need for a superior solution, the U.S. National Institute of Standards and Technology (NIST) launched a global competition in 1997. The goal was to find an encryption algorithm that was not only secure but also efficient across different platforms. This competition attracted proposals from cryptographers worldwide, but after rigorous testing and analysis, the Rijndael algorithm emerged victorious. Created by Belgian cryptographers Joan Daemen and Vincent Rijmen, Rijndael was selected for its security, speed, and adaptability.
Officially published as FIPS PUB 197 in 2001, AES became the standard for encrypting classified and sensitive data. Today, it’s recognized globally as an international benchmark for encryption.
How Does AES Work?
At its heart, AES is a symmetric block cipher, which means the same key is used for both encrypting and decrypting data. This method ensures efficiency and makes the algorithm suitable for large-scale implementation.
Here’s a simplified step-by-step look at what happens during the encryption process:
-
Fixed Block Sizes
AES processes data in fixed-sized blocks of 128 bits. The data is divided into these blocks, ensuring every piece of information is encrypted individually. -
Flexible Key Lengths
AES supports three key lengths: 128, 192, or 256 bits. Each key length offers different levels of security, with longer keys providing stronger protection. -
Multiple Rounds of Encryption
-
10 Rounds for 128-bit keys
-
12 Rounds for 192-bit keys
-
14 Rounds for 256-bit keys
These rounds involve substitution, permutation, and key mixing to transform plaintext into ciphertext (encrypted data). -
Key Expansion and Substitution-Permutation
AES employs a substitution-permutation network to carry out its cryptographic operations. This structure ensures that the input changes completely after each round, making it nearly impossible for attackers to reverse-engineer the encrypted data.
Decryption follows the same process in reverse, ensuring data integrity and confidentiality.
Key Features of AES
AES’s robust design and versatile functionality make it the backbone of modern encryption. Here are some of its standout features:
-
Unparalleled Security: With multiple rounds of encryption and cryptographic principles like substitution-permutation, AES is virtually immune to brute-force attacks.
-
Flexibility: Its support for different key lengths allows users to select a level of security that aligns with their specific needs.
-
Performance Efficiency: Designed for both hardware and software execution, AES can operate seamlessly on devices ranging from smartphones to supercomputers.
-
Global Approval: AES is the first publicly accessible encryption standard approved by the NSA to secure top-secret government information.
-
Scalability: The algorithm works efficiently across various platforms, including cloud systems, mobile devices, and IoT networks.
Applications of AES
AES isn’t just a theoretical concept used by cryptographers. Its reliability and adaptability have made it a practical solution for protecting sensitive data across countless domains:
-
Government and Military: Used to encrypt classified data and secure communication networks.
-
Banking and Finance: Protects online transactions, credit card details, and sensitive financial records.
-
Cloud Storage: Platforms like Google Cloud and AWS utilize AES to ensure data at rest and in transit remains secure.
-
Telecommunications: Messaging apps, video conferencing technologies, and voice-over-IP (VoIP) depend on AES to safeguard user privacy.
-
Consumer Electronics: From securing Wi-Fi networks (WPA2/WPA3) to encrypting smartphones and laptops using tools like BitLocker, AES has become a staple in the digital devices we rely on every day.
These real-world applications highlight how AES isn’t just protecting institutions but also safeguarding our personal data in an increasingly digital world.

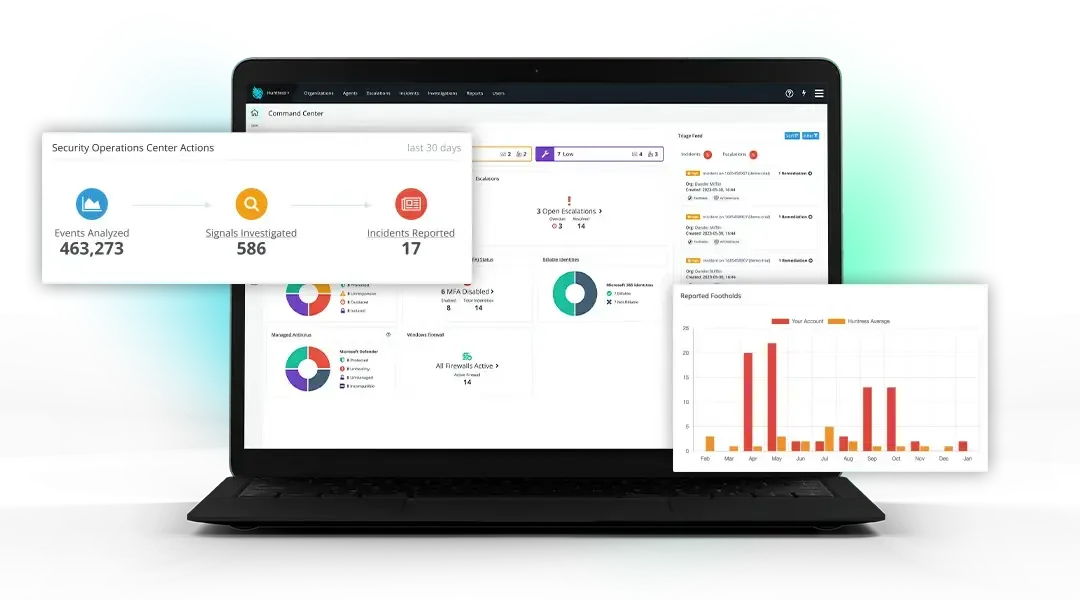
Huntress Managed EDR
Protect Your Endpoints
Endpoint detection and response (EDR) purpose-built for organizations like yours, fully managed by our 24/7 human-led SOC.
Why AES is Crucial for Today’s Cybersecurity
We live in an era where digital threats are constantly evolving.
Hackers are more sophisticated, and vulnerabilities in data security can lead to devastating breaches. AES thrives in this landscape, offering a robust defense against data theft, espionage, and cybercrime.
AES ensures:
-
Confidentiality: Data remains encrypted and inaccessible without the proper decryption key.
-
Integrity: Encryption transforms plaintext into secure ciphertext, protecting data from unauthorized tampering.
-
Compatibility: Its efficiency and adaptability work across a wide range of industries and technological platforms.
Even as cryptographic challenges, like quantum computing, begin to rise on the horizon, AES remains a critical pillar of cybersecurity. With evolving implementations and updates for greater resilience, AES continues to empower organizations and individuals to protect their most valuable digital assets.
Final Thoughts
The Advanced Encryption Standard (AES) isn’t just an encryption algorithm; it’s the foundation of secure communication in the modern world. From its creation to its real-world applications, AES demonstrates the perfect blend of security, efficiency, and usability. Whether you’re a tech giant safeguarding millions of user accounts or an individual protecting personal data, AES remains a trustworthy ally in the fight for digital privacy.

Additional Resources


Stay One Step Ahead of Attackers
Huntress gives you fully managed endpoint detection and response (EDR), so you've got 24/7 support from security experts ready to respond to threats.