Just last week, we hosted our second hack_it training event to bring actionable security education to the infosec community. This two-day event (plus a Hacking Windows pre-day) was packed with interactive exercises, malware research and technical workshops that were both shady and informative.
A few of our favorite sessions this year included a choose-your-own-adventure malware exercise, horror stories from fellow IT leaders and security professionals and a deep dive showing how attackers bypass antivirus software.
All in all, we had a blast and learned a lot—check out the video below for some of the highlights.
If you weren’t able to attend hack_it 2021, we got you covered:
- You can watch the complete event on-demand
- Or keep reading for some key takeaways
We’re a Lot Shadier Than We Think
In our Making the Malware session, we brought back the tabletop-style setting and had our attendees call the shots. The great thing about tabletop exercises is that you can validate your ability to execute a plan and work through a problem at little-to-no-cost (we even made our own tabletop-in-a-box so you can put these on yourself).
However, this wasn’t your average tabletop exercise… we had to put our own hack_it spin on it. Instead of learning how to defend against a possible cyber intrusion, we planned one. 😈
This session allowed us to take our defender hats off and put our adversary hats on. As new employees of Shady Incorporated, the dark web’s premiere cybercrime solutions provider, we donned our hacker hoodies and were tasked with planning our own cybercrime and wreaking havoc across the internet—and we did so by flipping the NIST cybersecurity framework on its head.
Instead of identifying our assets, we performed some reconnaissance to figure out who we were going to target.
- Rather than protect, we sought to gain initial access and discussed which type of phishing lure would work best for our exploit.
- While defenders aim to detect, we tried to gather their sensitive information.
- As they work to respond, we worked to exfiltrate all the data we collected.
- And when their best-case scenario is a quick recovery, our best case is maximizing our profit.
From fake invoices to DNS exploits, our gamemasters Kyle Hanslovan and Barbara Paluszkiewicz led us through each decision—showing us not only how hackers approach their attacks, but also just how shady us defenders can be.
Knowledge Sharing is Key
If there’s one thing we know for certain in the cybersecurity industry, it’s that you can’t understate the value of community building and knowledge sharing—and sharing stories is exactly what our Tales from the Trenches session centered around.
Felicia King and Matt Lee joined a panel with Dave Kleinatland and John Ferrell to shine a light on the real-world lessons, genuine advice and hard truths learned throughout their time in the IT community. Some of the stories they shared involved poor patching policies, lack of multi-factor authentication, dealing with Hafnium and so much more.
Even our audience got in on the action and shared what caused their own IT horror story and what they’d do to prevent their next one. Here are some of the more interesting facts and figures:
- For about a third of attendees, their own horror stories were caused by either a phished end user or a bad security posture.
- Another 35% of attendees said they would harden security baselines across the board in order to prevent their next dumpster fire.
You should absolutely go listen to the candid conversations that took place during this session.
AV Shouldn’t Be Our Last Line of Defense
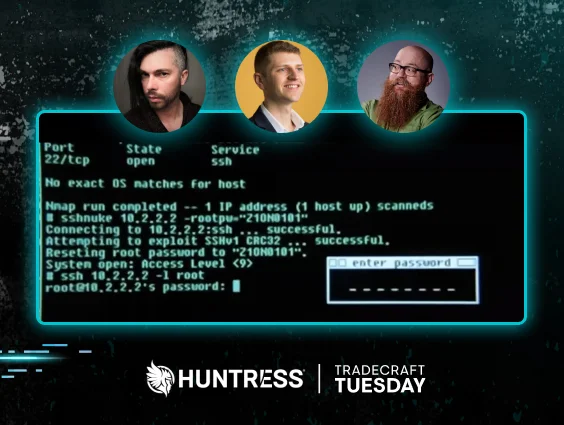
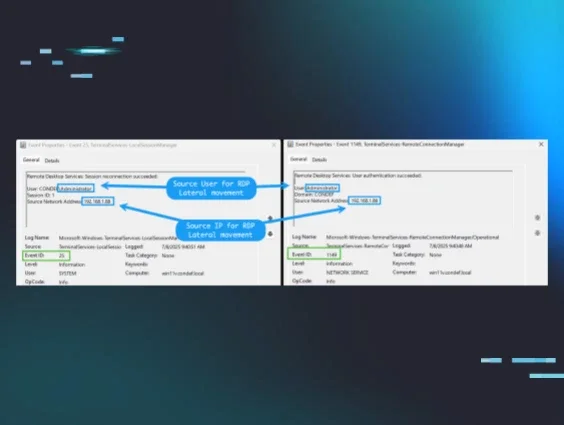
Jason Slagle and John Hammond teamed up once again to do some really cool on-the-keyboard demonstrations during our Slipping Past Prevention session. This offense-focused session took us under the hood to show exactly how the bad guys are breaking in—and based on some attendee feedback, it was definitely one of the more eye-opening sessions. Here’s what one of our attendees had to say:
“This brings a new level of awareness to how persistent hackers actually are.”
We dove into how AV and different virus scanner engines work, but the most interesting part was seeing how little effort it took to get past them. We watched as Jason and John developed their own payload and put it to the test against a series of modern AV programs.
I won’t spoil too much more for you—if you haven’t already, you should watch the recording to see all the tricks that can be used to evade antivirus.
If there’s anything that this session showed us, it’s that AV shouldn't be our last line of defense. Obviously we know that there is no silver bullet when it comes to security, but investing in multiple layers or defense in depth is likely the best approach.
As we tend to say here at Huntress, defenders have to be right all the time, but the bad guys only have to be right once. Events like hack_it are critical in ensuring that our community is continuously learning and being right as many times as we can.