Chances are that you lock your doors as you leave your house to prevent any unwanted visitors from entering while you’re gone. Although it isn’t foolproof, locking your doors presents a challenge for strangers without authorized access to enter. As a result of your efforts, an unwanted visitor—such as a burglar—would need to jump through a few hoops to enter your house.
In much the same way, you probably have at least a few preventive systems in place to keep threat actors out of your IT environments. From antivirus and firewalls to endpoint monitoring and regularly updating your software and systems, you have quite a few options to try to keep hackers at bay.
But what happens when a burglar gets hold of a copy of the key to your house? Or when a threat actor sneaks her way into your environment by bypassing your preventive tools?
Unfortunately, it happens more often than you might think. And once a threat actor goes through the hassle of bypassing preventive security measures, she’ll do anything to keep her access.
That’s where persistence comes in.
What Is Persistence?
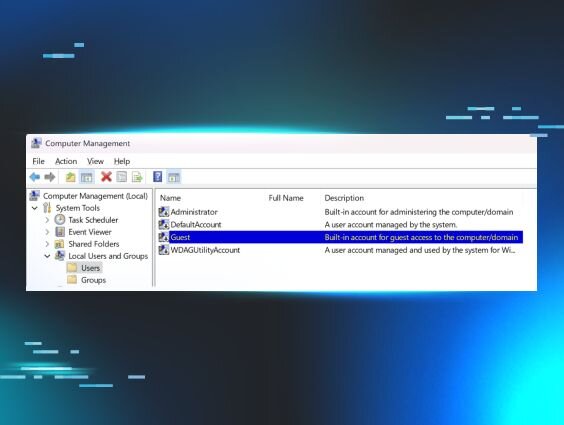
At its core, persistence is when a threat actor places malware—either a stub or fully loaded malware—into your environment, and then retriggers that malware after any disruptions take place—like when a user shuts down the operating system or logs off. In other words, persistence ensures that hackers who gain access to your environments can keep it—oftentimes without you knowing they have access in the first place.
Persistence is a hacker favorite for a reason. It acts as a copy of the key that allows a burglar to access your house any time he wants to. With today’s cutting-edge preventive tools, hackers usually have to work hard to gain access to their desired environment. It makes sense that they’d want to keep that access, and they do that through persistence.
How Hackers Remain Undetected With Persistence
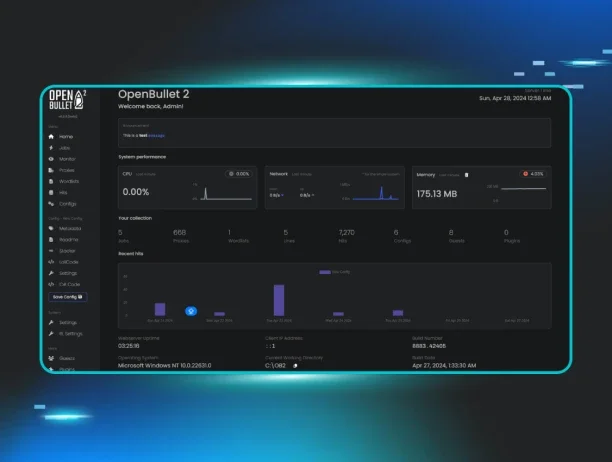
The problem with persistence—at least for defenders—is that it’s designed to be stealthy. It typically hides within legitimate applications and processes, meaning that antivirus software and other preventive security tools are unlikely to catch it. Even worse, hackers have already figured out how to bypass several preventive security measures at once to plant a persistent foothold into an environment.
That means that even a layered approach to prevention may not be enough to stop a hacker from making herself at home in your protected environments.
Even if you have the right preventive tools, prevention itself only goes so far. As hackers grow smarter, so must the tools that defend against them. And unfortunately for defenders, focusing strictly on prevention is fighting a losing game. There will always be a hacker who is able to bypass prevention—if not today, then tomorrow.
Persistence: The Smoking Gun at the Crime Scene
Persistence isn’t all bad news for defenders, however. What hackers use to hide in plain sight and dwell in your environments, defenders can use to hunt them down.
If you know what to look for, persistence can lead defenders directly to the hacker causing havoc within their environments. As a result, defenders can go beyond the malware or stub in question, reaching the source—the hacker—to evict her.
It’s important to note that persistence isn’t a problem that we can automate away. Hackers are humans who gain access to environments to cause someone to have a particularly bad day. They’re unpredictable, and for a fair fight to ensue, we have to meet hackers where they are and fight back with humans, not automation.
Human Threat Hunters Are Key to Addressing Persistence
Automated tools are great when it comes to analyzing large sets of data based on predefined rules and methods. However, persistence is anything but based on predefined rules. That’s why it’s a hacker’s favorite attack tactic. Persistence hides in plain sight, and oftentimes, only a human with contextual awareness can spot—and eliminate—a persistent foothold.
Thinking back to our intruder metaphor at the beginning of this blog, human threat hunters act like a guard on duty. Once a hacker bypasses automated preventive measures and plants a persistent foothold in your environment, human threat hunters can spot the foothold and sound the alarm—and burglars tend to run when they hear an alarm.
This is why no security stack is complete without humans. Only they have the contextual awareness and expertise to meet hackers where they are—and beat them at their own game.
Learn More
Want to learn more about persistence and why it’s so dangerous? Download our eBook below.