
The Cyber Threat Landscape: A Simple Guide



Hidden just under the surface of every click, email, or online transaction is a fast-moving cyber threat landscape buzzing with cybercriminal activity.
Whether you’re a global, sprawling enterprise or a one-person business that relies on mobile application point-of-sale (PoS) transactions, it’s nearly impossible to avoid having digital assets anymore. Document-filled filing cabinets are practically extinct. To understand cyber risks, you have to first understand the threat landscape where your digital assets and data live.
In this simple guide to the cyber threat landscape, we’ll break down what it means and how to build a successful cybersecurity strategy against common threats within it.
What is the cyber threat landscape?
Think of the cyber threat landscape as a snapshot of all potential cyber threats and vulnerabilities at any given time. It’s an overall look at the possible risks your organization faces in cyberspace, including the threat actors, their motivations, and methods behind cyberattacks. From fast-moving ransomware attacks to phishing scams tricking users into credential theft, the cyber threat landscape is constantly changing as attackers adapt to exploiting new technologies and evading increasingly complex defenses.
The cyber threat landscape is a combination of:
Emerging risks: New attack methods or exploits for vulnerabilities that threat actors develop as new technologies materialize
Active cyber threat campaigns: Ongoing threats targeting specific industry verticals, technologies, or people
Global trends: Cyberattacks tied to geopolitical events, technological breakthroughs, or economic shifts
Understanding the threat landscape is your first step toward staying protected. Whether you're safeguarding personal data or a business securing sensitive customer information, awareness is the first step to making sure you’re safe from modern threats.
The threat landscape for cybersecurity
The cybersecurity threat landscape is focused on defending against the tools, vulnerabilities, and methods that malicious threat actors use to compromise digital systems or data.
While the general threat landscape calls out risks that organizations deal with, the cybersecurity threat landscape is where proactive and reactive strategies against these risks come in. Essentially, the cybersecurity threat landscape is all about how cybersecurity professionals watch, analyze, and develop defense strategies to reduce threats on attack surfaces.
For businesses, the cybersecurity threat landscape often centers around:
Protecting sensitive company and customer data, like personally identifiable information (PII)
Monitoring systems, networks, endpoints, and identities for potential compromise activity
Managing the fallout from successful cyberattacks: reputational damage and financial loss
Cybersecurity teams look at the threat landscape like a constant game of cat and mouse, with adversaries that are persistent, quick, clever, and ever-adapting.
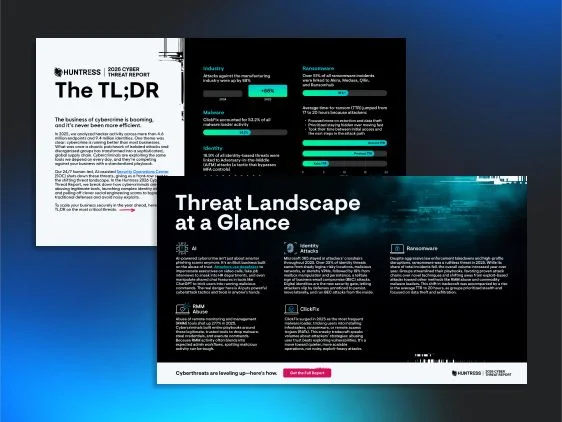
2026 Cyber Threat Report: The TL;DR
Instead of piecing together an accurate threat picture from fragmented sources, start with real data from real incidents and download the Huntress 2026 Cyber Threat Report TL;DR for the most important findings from a year of incident response across hundreds of thousands of protected endpoints.

Cyber threats in the threat landscape
There are an endless number of cyber threats out in the wild at any given time, but depending on their resources, motivations, and end goals, some are more common and well-liked by threat actors.
Below are some of the main types of cyber threats businesses defend against in the cyber threat landscape:
Malware
Malware or malicious software is a broad term that includes viruses, trojans, ransomware, infostealers, and spyware. It gives threat actors the power to corrupt systems and networks, steal data, log keystrokes, or lock you out of your devices until you pay a ransom.
Phishing
Phishing is a type of cybercrime where attackers use deceptive emails or messages to trick users into sharing sensitive information, such as passwords, credit card details, or personal data.
Ransomware
Ransomware is a type of malware that blocks access to computers, systems, and networks. Attackers encrypt or steal sensitive data, lock up endpoints, and send a ransom message demanding cryptocurrency payment within a short timeline.
Zero day
Zero day vulnerabilities are security flaws in software, hardware, or firmware that haven’t been found and patched by the vendor. A zero day exploit is a code or strategy that takes advantage of an undiscovered flaw in a zero day attack. Since attackers exploit zero day vulnerabilities before vendors have a shot at patching them, this gives them the upper hand with their targets.
Denial of service (DoS) attacks
These attacks flood a server or network with traffic, overloading it and making it useless for the business. Cybercriminals use these attacks to disrupt businesses or demand a ransom to bring normal operations back online.
Brute force attacks
This is a hacking technique that uses trial and error to guess login credentials or other sensitive information. Brute force attacks take advantage of computing power and automation with automated tools to try password combinations until they hit the right one. If you catch Event ID 4625, Failed Logon Attempt, in your Windows security log, make sure to take a closer look—repeated failed logon attempts could signal a brute force attack.
Advanced persistent threats (APTs)
APTs are long-term, targeted attacks on specific organizations or governments. These cyberattacks are usually the work of state-sponsored groups motivated by cyber espionage or quick, unregulated cash.
Threat landscape versus attack surface
Both security concepts tackle cyber risks, but from different angles:
Threat landscape
This refers to all potential cyber threats affecting people, businesses, and industries. It highlights general risks that you’ll run into based on your industry vertical, geopolitical affiliation, or technology stack, for example.
Attack surface
The attack surface is the combination of vulnerabilities and potential access points a threat actor exploits to get unauthorized access to a system, network, or data. An attack surface is:
digital: software, applications, code
physical: computers, servers, operational technology (OT)
Internet of Things (IoT): security camera systems, smart appliances, smart thermostats, voice assistants
human: social engineering
Anything exposed to the Internet—even a fish tank! — can be a potential access point on your attack surface.
Cyber threat landscape trends
Exploitation trends like these have far-reaching impacts, so it's smart to keep a watchful eye on threat landscape patterns like these:
Ransomware-as-a-service (RaaS)
Cybercriminals are now "renting out" ransomware tools. This is geared towards amateur hackers, known as ransomware affiliates, who launch ransomware attacks for a quick, unethical buck.
Supply chain attacks
Recent breaches have targeted suppliers rather than their downstream customer organizations, creating a larger attack blast radius than ever before. In 2020, the cybersecurity world was rocked by the SolarWinds supply chain attack, when suspected nation-state attackers injected malicious code into the Orion Platform, used by more than 30,000 public and private organizations, giving them potentially massive unauthorized access.
Remote work security pitfalls
While many businesses are shrinking their attack surfaces to improve cybersecurity, remote work can be an obstacle to making work safer. Variables like flimsy home network security, vulnerable personal devices, and more phishing and social engineering schemes on remote end users are abundant entry points for cybercriminals.
State-sponsored cyberattacks
Nation-state threat actors are usually in it for the long haul. Unlike petty cybercriminals, they have time, money, and resources to get what they want. For example, in one case caught by Huntress, they used a seemingly legit Zoom call with deepfakes of C-Suite executives to trick an employee at a business into clicking malicious links for access and persistence to endpoints with sensitive information.
How to defend against cyber threats in the threat landscape
There’s good news! Owning your place in the cyber threat landscape puts your organization in a smarter and safer position against cyber threats.
Here are essential steps for defending against the rising tide of the threat landscape:
Never stop learning
Human mishaps are still a major catalyst for cyberattacks. Managed Security Awareness Training helps spread the word about deepfakes, phishing scams, password hygiene, and secure browsing.
Multi-factor authentication (MFA) isn’t optional
Adding a second security layer helps stop attackers from getting unauthorized access, even if passwords are compromised.
Patch it up
Outdated software is a security nightmare—it’s like wide-open doors inviting attackers to a party in your attack surface. So, prioritize patching and regular updates to stay ahead of potential threats.
Redefine your perimeter with identities
In the Huntress 2025 Managed Identity Threat Detection and Response (ITDR) Report, more than two-thirds of businesses reported a surge of identity-related security incidents over the last three years. Attackers are sneaking in undetected by using compromised credentials, session tokens, rogue apps, and overlooked configurations in Microsoft 365. Identity threats are stealthy, fast, and persistent, but you can beat them with ITDR.
Go the distance with cybersecurity tools
Firewalls, antivirus, VPNs with MFA enabled, threat intelligence platforms, encryption tools, and intrusion detection systems are essential for businesses of all sizes.
But what if you have a small security team? Or none at all? Not a problem. Look for solutions like Managed Endpoint Detection and Response (EDR) that come with built-in pros to handle your security for you.
Don’t slack on monitoring and auditing
Run audits on a regular schedule to hunt down weak points in your organization’s security stack.
Recovery plans
Getting back disrupted or lost data after an attack isn’t easy, especially when there isn’t a solid plan for that ahead of time. Here’s what businesses need to do instead:
Regularly back up data in secure locations
Keep an up-to-date incident response (IR) plan and stress test it during tabletop exercises
Look to external security experts, like managed services, to restore systems and investigate breaches
The future doesn’t have to be risky
Technology sprints ahead, and so do cyber adversaries' sketchy tactics. Keep your guard up, stay sharp, be persistent, and always be at least one step ahead.
By identifying threats and setting up solid defenses, businesses can reduce their cyber risks and keep their valuable data safe and sound.

Additional Resources
- Read more about Cyber Threats Explained: Stay Ahead of Online Threat ActorsLearn what cyber threats are, how they work, and how to defend against them. Huntress insights on top threats, threat actors, and key cybersecurity strategies.
- Read more about What is Threat Actor Profiling? | Cybersecurity GuideWhat is Threat Actor Profiling? | Cybersecurity GuideLearn how threat actor profiling helps organizations identify, analyze, and defend against specific cyber adversaries through targeted intelligence and strategic planning
- Read more about What Is Google Dorking? How Hackers Use Search Engines for ReconWhat Is Google Dorking? How Hackers Use Search Engines for ReconLearn what Google Dorking is, how hackers use advanced search operators to find sensitive info, and steps to protect your business from this cybersecurity risk.
- Read more about What is a Threat Intelligence Analyst? How Threat Analysts Shape CybersecurityWhat is a Threat Intelligence Analyst? How Threat Analysts Shape CybersecurityLearn what threat intelligence is, why it matters, and how analysts help protect organizations by detecting and stopping emerging cyberthreats.
- Read more about What is Weaponization in Cybersecurity?What is Weaponization in Cybersecurity?Learn how weaponization fits into the Cyber Kill Chain, why it’s critical, and how IT teams can defend against evolving cyber threats.
- Read more about What Is a Security Operations Report? SOC ReportsWhat Is a Security Operations Report? SOC ReportsLearn why security operations reports are essential for safeguarding your organization and learn what they include. Stay ahead in the battle against cyber threats.
- Read more about What is a Wiper Attack? Defense Guide to Mitigating Cyber RiskWhat is a Wiper Attack? Defense Guide to Mitigating Cyber RiskLearn what wiper attacks are, how they destroy data permanently, and essential strategies to protect your organization from these devastating cyber threats.
- Read more about What Is Human Risk Management? Mitigating Cyber RiskWhat Is Human Risk Management? Mitigating Cyber RiskLearn how human risk management addresses cybersecurity vulnerabilities tied to human behavior. Learn its benefits, steps, and implementation tips.
- Read more about What Is HUMINT? The Human Intelligence Side of CyberWhat Is HUMINT? The Human Intelligence Side of CyberLearn how HUMINT boosts cyber defense with real human insights. Understand its role, benefits, and risks for proactive threat intelligence.


Protect What Matters








