What does an incident responder do?



An incident responder is a cybersecurity professional who detects, investigates, and manages the aftermath of cyber incidents to limit damage and get systems back up and running.
Simply put, incident responders jump into action when security alerts hit, figure out what happened, and help organizations contain and recover from threats like hacks, ransomware, or data breaches.
If you want to know what actually happens when “something bad” is detected in a company’s network, then you may be interested in learning more about what an incident responder does on a day-to-day basis.
What is an incident responder?
At its core, an incident responder is like the emergency team for digital disasters. When a cyber threat hits, incident responders step in to identify what happened, contain the spread, and help the business recover as fast (and painlessly) as possible.
They’re pros at handling surprises—from mysterious malware to high-stakes ransomware attacks. Their mission: stay calm under pressure, make sense of digital chaos, and protect an organization’s systems, data, and reputation.
You’ll find incident responders in all sorts of workplaces, from big banks to government agencies and small IT teams. Some work full-time inside security operations centers (SOCs), while others are called in as experts when things go sideways.
Main tasks and responsibilities
Incident responders rock a job that combines detective work, communication, and technical know-how. Here’s what they handle, day in and day out
Investigation: Collect clues (log files, emails, etc.), analyze what happened, and trace the root cause of incidents.
Containment and eradication: Move fast to stop attackers, block suspicious users or devices, and scrub systems of malware.
Recovery: Help restore affected systems, ensuring everything is clean and safe to use again. This often means working with IT to reinstall software, recover data, or change passwords.
Documentation: Write detailed reports on what happened, what actions were taken, and recommendations for closing gaps.
Communication: Coordinate with other teams and, in some incidents, notify management or law enforcement.
Why is incident response critical in cybersecurity
Incident response isn’t just “nice to have.” Without it, even small cyber incidents can spiral into full-blown disasters, costing companies money, reputation, and customer trust.
Cyber threats are a daily reality: Cyber attacks like phishing, malware, and ransomware can hit any organization at any time.
Regulations demand action: Industries like healthcare, finance, and energy are required by law to report breaches and have response plans in place.
Speed matters: The faster an attack is contained, the less damage it can cause.
Incident responders are the heroes who make sure security incidents are managed quickly and efficiently, limiting their impact on the business and (sometimes) stopping attackers in their tracks.
What skills do incident responders nee?
It’s not just about tech savvy. Here’s what great incident responders bring to the table
Technical skills
Deep understanding of computer networks, operating systems, and common cyberattacks.
Experience with forensic analysis tools and SIEM systems.
Ability to analyze logs, malware, and suspicious behavior.
Soft skills
Resilience under pressure. Incidents often mean high-stress, high-stakes situations.
Communication. Explaining complex issues clearly to both technical teams and management.
Attention to detail. Small clues are often critical for resolving incidents.
Many incident responders have degrees in cybersecurity, information technology, or computer science, plus certifications like Certified Incident Handler (GCIH), Certified Information Systems Security Professional (CISSP), or SANS courses.
How to become an incident responder
You don’t have to be a coding wizard to get your start, but a strong understanding of IT systems and networks definitely helps.
Here’s a standard path
Earn a bachelor’s degree in cybersecurity, info tech, or computer science.
Get hands-on experience (help desk, IT support, network/admin roles).
Pursue certifications (trySANS GIAC,CompTIA CySA+, or similar).
Apply for entry-level security analyst jobs or internships.
Looking to grow further? Consider a master’s in cybersecurity or specialized certs like computer forensics or malware analysis.
Incident responder career outlook and pay
Incident responders are in high demand thanks to the endless parade of cyber threats.
According to Payscale, the average salary is around $74,000/year in the US, with room to grow depending on your skills, city, and company size.
The Bureau of Labor Statistics expects IT and cybersecurity roles to grow 13 percent by 2030.
Key takeaways
Incident responders are cyber emergency responders, handling everything from detection to recovery. This role is critical for reducing the business, data, and reputation damage caused by cyber incidents. With new attacks happening daily, skilled incident responders are more in demand than ever. Starting out means focusing on IT basics, hands-on skills, and relevant certifications.
The job isn’t just technical—communication, teamwork, and a cool head are must-haves.
FAQs about incident responders



Additional Resources
- Read more about What Is Telemetry in Cybersecurity? A Simple ExplainerLearn what telemetry is in cybersecurity, what it includes, and why it's the essential data source for all threat detection.
- Read more about What Is a Digital Footprint? Explained for BeginnersWhat Is a Digital Footprint? Explained for BeginnersLearn what a digital footprint is, why it matters for cybersecurity, and how to protect yours in simple terms.
- Read more about What is an Asset in Cybersecurity? | Complete GuideWhat is an Asset in Cybersecurity? | Complete GuideLearn what constitutes a cybersecurity asset and why proper asset management is crucial for protecting your organization from cyber threats.
- Read more about Comprehensive DNS Protection Guide - Stay Ahead of Cyber ThreatsComprehensive DNS Protection Guide - Stay Ahead of Cyber ThreatsLearn how DNS protection strengthens your cybersecurity posture. Discover best practices, setup tips, and the importance of regular updates to safeguard against evolving threats
- Read more about What Is a CVE? Common Vulnerabilities & Exposures ExplainedWhat Is a CVE? Common Vulnerabilities & Exposures ExplainedLearn about CVE (Common Vulnerabilities and Exposures), a universal system for cataloging cybersecurity vulnerabilities, and why it’s essential to cybersecurity professionals.
- Read more about What is a Threat Actor? How To Spot and Avoid Rising ThreatsWhat is a Threat Actor? How To Spot and Avoid Rising ThreatsWhat is a threat actor? Learn key definitions, types, motivations, and how to detect them in your network with expert insights and Huntress examples.
- Read more about What Is a Scam Likely Call and How to Stop ThemWhat Is a Scam Likely Call and How to Stop ThemLearn what scam likely calls are, how to identify them, and ways to prevent potential scams. Take these steps to protect yourself and your data today.
- Read more about What Is Cloud Data Security? Protecting Data in the CloudWhat Is Cloud Data Security? Protecting Data in the CloudLearn what cloud data security is, why it matters, key tools, and how to secure cloud data. Step into the secure cloud future.
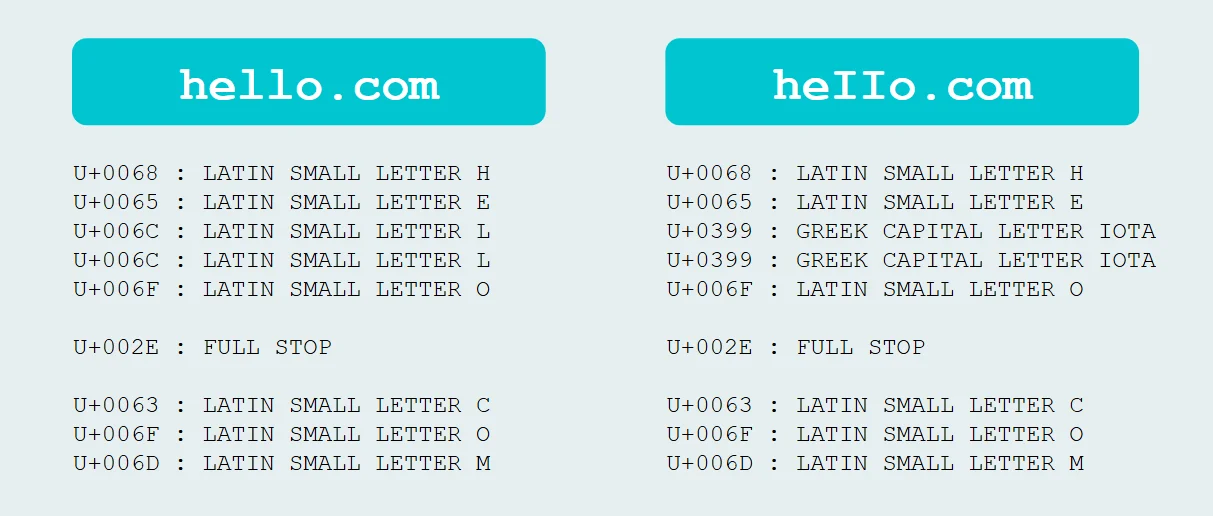
- Read more about Exploiting PunycodeExploiting PunycodeLearn what Punycode is, how cybercriminals exploit it for phishing, and the best defenses against homograph attacks in this 5-minute guide for cybersecurity pros.


Protect What Matters