
What is a SYN, and why does it matter in cybersecurity



Key Takeaways
SYN packets initiate every TCP connection. A SYN (synchronize) packet is the first step in the three-way handshake — when a device sends a SYN, the server responds with a SYN-ACK, and the client completes the exchange with an ACK, establishing the connection.
SYN flood attacks exploit this handshake mechanism. Attackers send massive volumes of SYN packets without ever completing the handshake, forcing the server to reserve resources for connections that never finish — eventually overwhelming it and causing a denial-of-service condition.
Monitoring SYN traffic is a powerful early-warning system. Unusual spikes in SYN activity can signal an active DoS attack or reconnaissance efforts, where attackers probe open ports to find vulnerable services. Knowing your network's normal SYN baseline makes anomalies much easier to catch quickly.
Defense is achievable with proper configuration. Enabling SYN cookies, rate-limiting incoming SYN packets, and deploying properly configured firewalls and intrusion prevention systems can neutralize most SYN flood attempts before they cause significant harm.
What is a SYN?
SYN (Synchronize): The very first message in the “three-way handshake” that establishes a TCP connection.
SYN packet: A network packet with its SYN flag set, used to initiate communication between two computers.
Why it matters: SYN packets are essential for connecting computers, but attackers can exploit them to disrupt networks via SYN flood attacks.
A SYN (short for “synchronize”) is a special kind of packet that computers send at the very start of any new connection using TCP, the protocol responsible for most reliable communications on the Internet. When you see the term “SYN” in cybersecurity, you’re talking about the handshake that makes data transfer possible and, unfortunately, one of the most targeted weaknesses in network defense.
If you’ve spent five minutes in IT, watched your firewall freak out, or crammed for a security exam, you’ve seen “SYN” pop up. Here’s what you really need to know about SYN packets, SYN flood attacks, and how mastering SYN visibility can keep your network a whole lot safer.
What are SYN packets?
SYN packets (pronounced “sin,” not “S-Y-N”) form the backbone of how devices start talking with each other on a network using the Transmission Control Protocol (TCP). When your laptop wants to load a website, it sends out a SYN packet to the web server that says, “Hey, I want to start a conversation.” If the server is open for business, it replies with a SYN-ACK (“sure, I’m ready”). Your laptop then sends an ACK back, finishing the handshake. This three-part process is what gets your connection up and running.
Key Points About SYN Packets
They’re the “door knock” that starts every reliable connection on the Internet.
Each SYN sets up a unique sequence number so both sides can stay in sync.
Only TCP (not UDP, for instance) uses SYN packets as part of a handshake.
How does a SYN flood attack work
Here’s where things turn nasty. Attackers use what's called a SYN flood attack to mess with services and firewalls. This Denial of Service (DoS) trick involves sending thousands (or millions!) of SYN packets to a target server but never finishing the handshake. It’s like ringing someone’s doorbell all day, every day, and running away before they open the door.
Since each SYN demands the server reserve a little space “just in case” the connection completes, too many unfinished handshakes will eventually clog up the server until it can't accept real users. That can mean downtime for businesses, lost revenue, or a perfect distraction for bigger, sneakier attacks.
Pro tip: Modern firewalls and operating systems are a lot smarter about handling SYN floods than they used to be. They use techniques like SYN cookies or rate limiting, but massive attacks can still cause trouble, especially for unpatched or misconfigured systems.
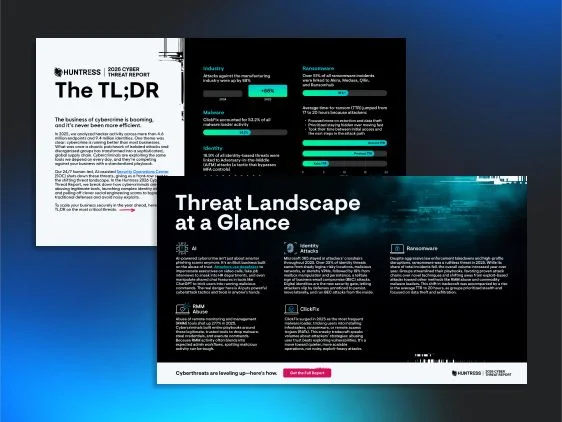
2026 Cyber Threat Report: The TL;DR
SYN flood attacks exploit the fundamental TCP handshake mechanism to overwhelm servers and knock services offline, and network-layer attacks like these are just one part of the modern threat picture, so download the Huntress 2026 Cyber Threat Report TL;DR to get a clear view of what your team needs to prioritize and prepare for.

What is a SYN in cybersecurity monitoring
Watching SYN packets is like having a motion sensor on your front porch. Normal SYN activity just means people are “knocking” to start connections. But a flood of SYNs can signal a DoS in progress or a sneaky attacker mapping your network.
Why SYN Visibility Matters
Early attack detection: Spikes in SYN packets often show up just before an attack kicks into high gear.
Reconnaissance spotting: Attackers look for vulnerable servers by sending SYNs to random ports and seeing who answers.
Baseline building: Knowing your “normal” SYN activity helps you spot the unusual, fast.
Security professionals use tools like Wireshark, firewalls, or traffic analysis boxes on DMZ switches to keep an eye on SYN rates.
How SYN ties to network visibility
If you ignore SYN activity, you’re basically leaving your network’s front doors unlocked. By monitoring SYN packets, you gain powerful insights into:
Where connections are coming from (and going to)
Which services are getting the most “knocks”
Potential exposure to DoS and reconnaissance attacks
Getting familiar with SYN traffic is step one in detecting threats before they ruin your day.
Example scenario SYN flood in action
Your business relies on a public customer portal running on TCP port 443 (HTTPS). One afternoon, performance slows to a crawl. Your firewall lights up with SYN flood alerts, showing thousands of connection attempts per second. By monitoring SYN rates, you spot the attack early and deploy countermeasures, keeping your site online while other companies might struggle. That’s the power of SYN visibility.
Ways to defend against SYN flood attacks
Don’t want to fall victim to SYN-based antics? Start with these basics:
Enable SYN cookies on your servers to verify real clients.
Rate-limit incoming SYN packets so floods don’t overwhelm you.
Deploy firewalls and intrusion prevention systems (IPS) that filter out malicious SYN traffic.
Monitor regularly so you know your own network’s baseline and can react fast to spikes.
For more on DoS mitigation, visit CISA’s official DDoS guidance.
FAQ



Additional Resources
- Read more about What is TCP/IP and Its Importance in CybersecurityLearn the importance of TCP/IP in cybersecurity with a deep look at its layers, vulnerabilities, defenses, and tools for securing traffic.
- Read more about What is Pacture Capture? Benefits of PCAP in Network SecurityWhat is Pacture Capture? Benefits of PCAP in Network SecurityLearn what packet capture is, how it works, and the benefits of PCAP in network security.
- Read more about What is a Firewall? A Guide to FirewallsWhat is a Firewall? A Guide to FirewallsA firewall is a network security device that monitors traffic to or from your network. Learn more about how firewalls work in the guide to all things firewall.
- Read more about What Is IRSF in Cybersecurity? And How to Prevent Telecom FraudWhat Is IRSF in Cybersecurity? And How to Prevent Telecom FraudLearn what IRSF is, how telecom fraud exploits communication networks, and the best techniques to detect and prevent attacks. Reduce risk and revenue loss today.
- Read more about HTTP/2 and Cybersecurity: Risks, Benefits, and ProtectionHTTP/2 and Cybersecurity: Risks, Benefits, and ProtectionExplore HTTP/2's benefits and vulnerabilities in cybersecurity. Learn how Huntress' MDR solution tackles modern protocol threats to secure your network.
- Read more about What is an Evil Twin Attack?What is an Evil Twin Attack?Learn about Evil Twin Attacks and how attackers create fake networks to steal data. Read more about how to protect yourself from these wireless threats.
- Read more about Stateful vs Stateless Firewall | Huntress Cybersecurity 101Stateful vs Stateless Firewall | Huntress Cybersecurity 101Learn the key differences between stateful and stateless firewalls. Discover how to choose the right firewall for your network's cybersecurity needs.
- Read more about What is a Hoax Attack? How to Spot Fake Security ThreatsWhat is a Hoax Attack? How to Spot Fake Security ThreatsLearn what hoax attacks are, how they spread false security warnings, and discover proven methods to identify and stop these fake threats before they cause damage.
- Read more about What is DDoS?What is DDoS?Learn what DDoS attacks are, how they disrupt systems, and how to defend your organization against these cyber threats. | Huntress


Protect What Matters








