In late May 2023, customers running the popular MOVEit file transfer software faced multiple, unexplained intrusions. As previously documented by Huntress, MOVEit customers found themselves the victim of an actively exploited zero-day vulnerability, since tracked as CVE-2023-34362. Following the initial discovery, the criminal entity typically referred to as cl0p took credit for the widespread exploitation of MOVEit instances.
After initial reports of the MOVEit vulnerability and active exploitation, security practitioners and network owners observed a steady release of victims, via the cl0p leak site. Superficially, this would appear to indicate that the vulnerability is under continued, active exploitation even after a patch for CVE-2023-34362 was released. However, closer analysis indicates something potentially more troubling: initial, widespread success in compromising vulnerable, accessible MOVEit installs, followed by a slow and steady adversary follow-up on compromised activity.
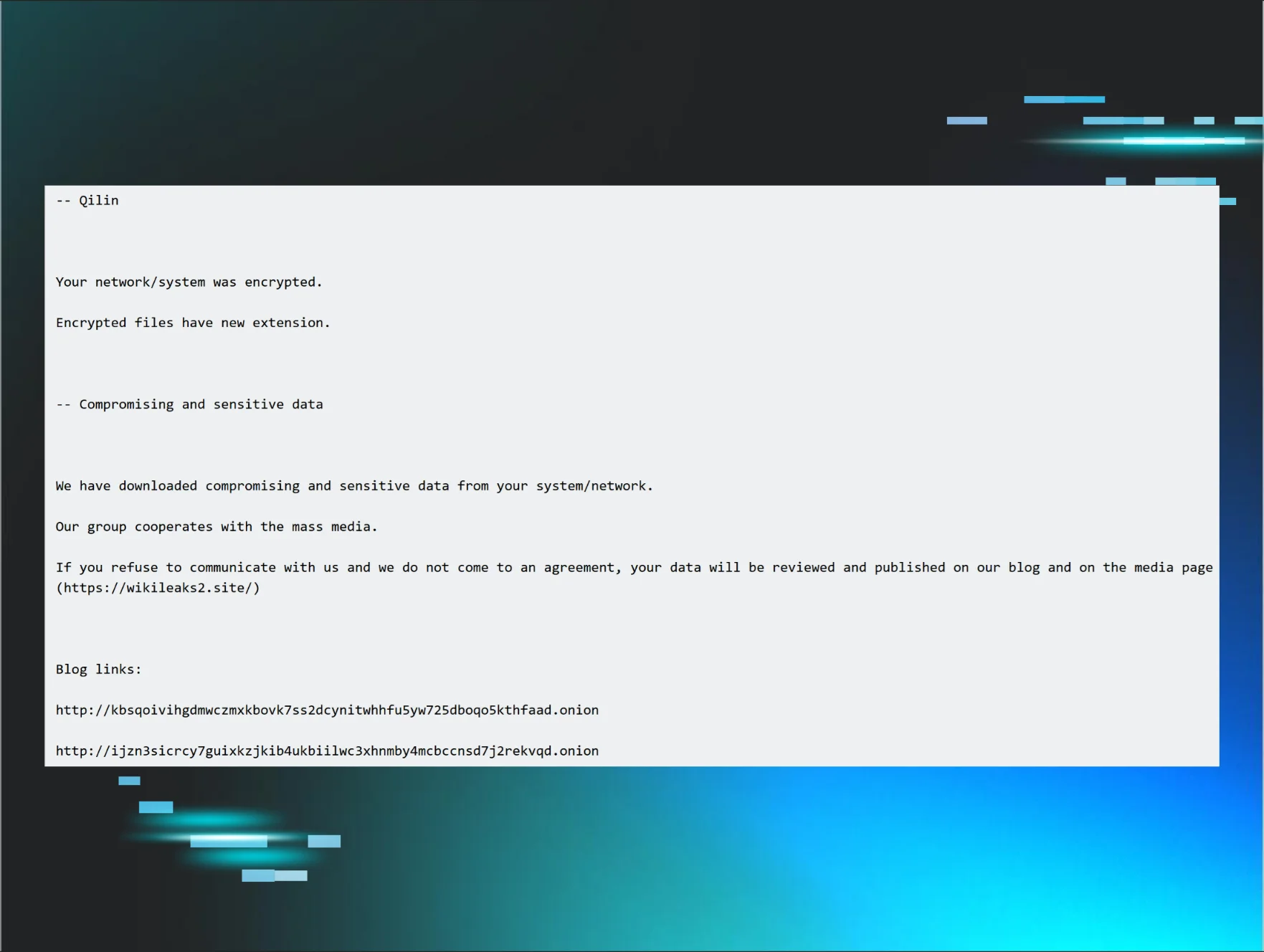
Notably, MOVEit exploitation linked to cl0p has not resulted in the deployment of ransomware or the compromise of entire organizations. Instead, identified tradecraft thus far, as documented by Huntress and others, indicates initial access was used to deploy a web shell. This web shell could be used, within the context of the exploited service, to copy and exfiltrate files—but as of this writing, no known instances exist where cl0p attempted to leverage this initial access to “break out” for full network compromise.
Presumably, a notorious ransomware operator would follow “typical” tradecraft in leveraging initial access to work towards compromising the victim’s domain, following this up with large-scale ransomware deployment. Notably, this follows the same observed behavior from a similar cl0p-led campaign against managed file transfer (MFT) services: exploitation of the GoAnywhere MFT leading to data exfiltration, but no public evidence of network encryption. We have thus observed a change in aspect—from deliberate compromise of entire network environments for ransomware deployment to opportunistic exploitation of vulnerabilities for data exfiltration.
Managing Exploitation At Scale
The steady drumbeat of new MOVEit victims, whether through cl0p’s leak site or through victim notifications to users, seemingly implies continued exploitation of this vulnerability. However, within Huntress telemetry and in discussions with industry partners, no significant exploitation of this vulnerability is observed after late May 2023. Presumably, a threat actor with a viable exploit for a service that is high-availability in nature (thus not easily patched) and typically exposed externally would continue to follow up on this advantage, yet instead, the broader security community observed an initial “burst” of activity, followed by limited or no action as the calendar turned to June.
The above scenario, or lack of observed activity, may relate to a seemingly simple and somewhat embarrassing problem: lack of resources. As seen in similar widespread exploitation activity (such as the 3CX supply chain incident earlier in 2023), sometimes effective intrusion mechanisms lead to a surprising amount of success—a degree of success that becomes difficult to actively or immediately exploit given the volume of victims.
As noted in reporting from Huntress and other entities, the web shell deployed in MOVEit exploitation is essentially the same across victims aside from superficial filename changes and a hardcoded, seemingly randomly generated password. While insufficient evidence exists to definitively prove the following hypothesis, existing observations appear to indicate a threat that aimed for widespread exploitation of the given vulnerability (likely through automated means), which would deploy a foothold for the adversary to access and engage in follow-up operations.
The above model is sensible and understandable but becomes intractable when the degree of activity begins to extend beyond the capabilities (and time) of the operators at hand. The outlined scenario may also explain why post-exploitation operations linked to MOVEit all center on data exfiltration and extortion, with no publicly known cases of cl0p (or other actors) leveraging initial access for network ransomware deployment. Essentially: cl0p overloaded itself with opportunities and is working to monetize as many of them as possible until discovery or eviction.
The Long Tail Of Network Intrusions
Readers are certainly familiar with limited time and resources to handle network security concerns—what the steady beat of MOVEit victim identification reveals is a “long tail” for adversaries as well. In this scenario, the greatest volume of activity (and defender attention) centers on the early stages of discovery and use of a given capability, vulnerability or similar. As time passes, the item becomes less novel or defenders adequately adjust through controls or patching, reducing the effectiveness and prevalence of the technique. Alternatively, subsequent activity may indicate adversaries following up on points of presence gained early in the technique’s lifecycle.
The result is the technique does not go away, but extends into a cyberoperations long tail of opportunistic activity and legacy actions followed up on after the fact. Potentially such actions are limited in scope compared to the initial “burst,” but remain profitable enough to justify continued attention and investment. MOVEit exploitation linked to cl0p resembles this in that while we see this steady release of new victims on a near daily basis as of the time of this writing, all available evidence suggests the intrusions at the source took place in late May. Thus the threat actor works to monetize actions already taken place, but does so in a fashion that divorces the initial compromise from subsequent, delayed follow-up.
Other examples of this long tail exist, though, largely around lingering vulnerabilities and weaknesses in victim environments. We can look to examples such as organizations running legacy, unsupported operating systems or software no longer maintained by the given vendor. For a concrete example, we can look to critical vulnerabilities in the Windows operating system, such as MS17-010 (enabling the WannaCry event) or even MS08-67 (the infamous vulnerability enabling Conficker). While distressing at the time of their discovery, these items remain relevant for intrusions to this day. In these cases, continued use of legacy systems, lack of effective patch management, and related reasons keep these “zombie vulnerabilities” alive far longer than one would expect. Thus the long tail of adversary opportunity exists not just in the lingering effects of intrusions, but in the slow response of defenders to realities imposed by intruders.
Defender Responses & Guidance
Two lessons emerge from the above commentary. The first, and easiest to address, is that just because something is “old” does not mean it will not be used again. While the examples of MS17-010 and MS08-67 are fairly obvious on this front, we can also extend this from vulnerabilities to techniques. For example, Office-based macros for victim code execution have continually shifted historically in prevalence and frequency, with current trends largely driving adversaries away from this technique.
However, techniques reemerge and find themselves unearthed with shifts in the technical landscape and enterprise application use and configuration. What was once successful and widespread may die off, but it also may emerge again. Thus defenders need to ensure some degree of coverage or prevention against even legacy techniques, whether that be patching against seemingly long-dead vulnerabilities or ensuring visibility is maintained over tradecraft that may have fallen out of favor.
Second, defenders must think beyond the headlines and adopt a very cautious approach in light of events such as MOVEit—where impacts may not be immediately observed. In the case of MOVEit exploitation, cl0p or related entities leveraged the exploit for initial access and then siphoned data from the victimized systems for extortion purposes. Being able to identify anomalous data flows (a difficult task from a system designed to share and distribute data) is critical to determining if initial vulnerability led to compromise and impact. Given the avoidance of very obvious impacts in this campaign (e.g., deployment of network-wide ransomware), organizations find themselves in the difficult position of trying to verify that something didn’t happen in their environment.
Here, a combination of visibility (across host and network data) and retention (so that historical information can be queried once a given threat vector is identified) are critical in not just scoping, but even identifying a breach. Determining that data was exfiltrated (and hopefully just what data as well) can help an organization plan response and recovery plans, and get ahead of events rather than relying on threat actors to determine the timing and cadence of responses.
Conclusions
Threats constantly evolve and change—but older threats do not necessarily go away. This can either be through the resurrection of legacy items and behaviors as environments change, or the emergence of intrusions long passed that only get operationalized weeks or months after they took place. Irrespective of source or cause, such items emphasize several key aspects of information security:
- Ensuring awareness of adversary actions and tendencies to adapt defenses to malicious tradecraft
- Engaging in attack surface management to limit or shape what is available to adversaries to compromise the defended environment
- Maintaining visibility over the defended environment to ensure questions (“Have we been breached?”) can be answered in a reasonably authoritative fashion
- Actively hunting within defended environments to identify artifacts associated with breaches that were missed initially
While none of the above is necessarily easy, they are necessary to ensure organizations can not only attempt to prevent significant compromise in instances such as the MOVEit event, but also learn after the fact if such events really did impact the monitored environment. Threat actors may not be able to exploit all points of presence initially gained in a campaign. Therefore, being able to identify such activity or related artifacts is critical in cutting off the long tail of threat actor operations in slow-moving campaigns such as this item.
Want to dive deeper into Huntress’ MOVEit analysis? Watch this Tradecraft Tuesday episode to learn how we recreated the full attack chain, shared response and remediation tips and more.