They’re saying what about us?!
We’ve seen some pretty interesting points of view on how we do what we do and why, specifics around our technology and the capabilities we possess.
With all the time we spend investigating intrusions, reverse engineering malware, hunting for bad actors and generally trying to make the security world a safer place, it may be hard – especially if you’re new here – to put your finger on what Huntress does and how we do it.
We wanted to set the record straight in true Huntress fashion – complete transparency – so here we go!
What Even Is a “Huntress”?
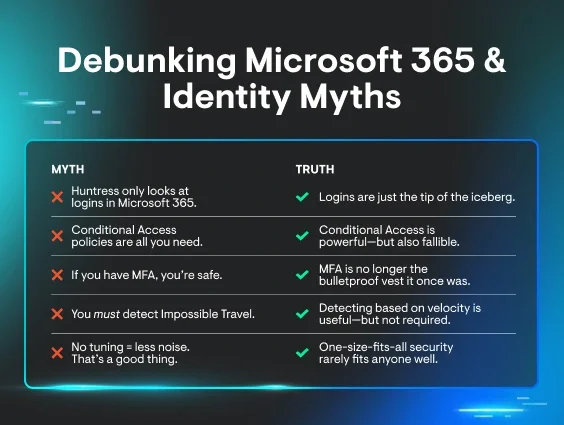
In the interest of fair play, we’d like to note some of the misconceptions and myths floating around to provide clarity on what we actually do.
Huntress exists to help secure the 99% – the small and medium-sized businesses that lack the resources to properly defend themselves against today’s cyber threats.
What We Offer
Huntress provides managed endpoint protection in The Huntress Managed Security Platform by leveraging endpoint detection and response (EDR).
We use human operators who investigate cybersecurity threats and categorize the threats. Then, our 24/7 Security Operations Center (SOC) provides granular, tailored remediation guidance that often consists of a single click of a button within the Huntress dashboard. Finally, we send a report to our partners and customers detailing the incident at hand.
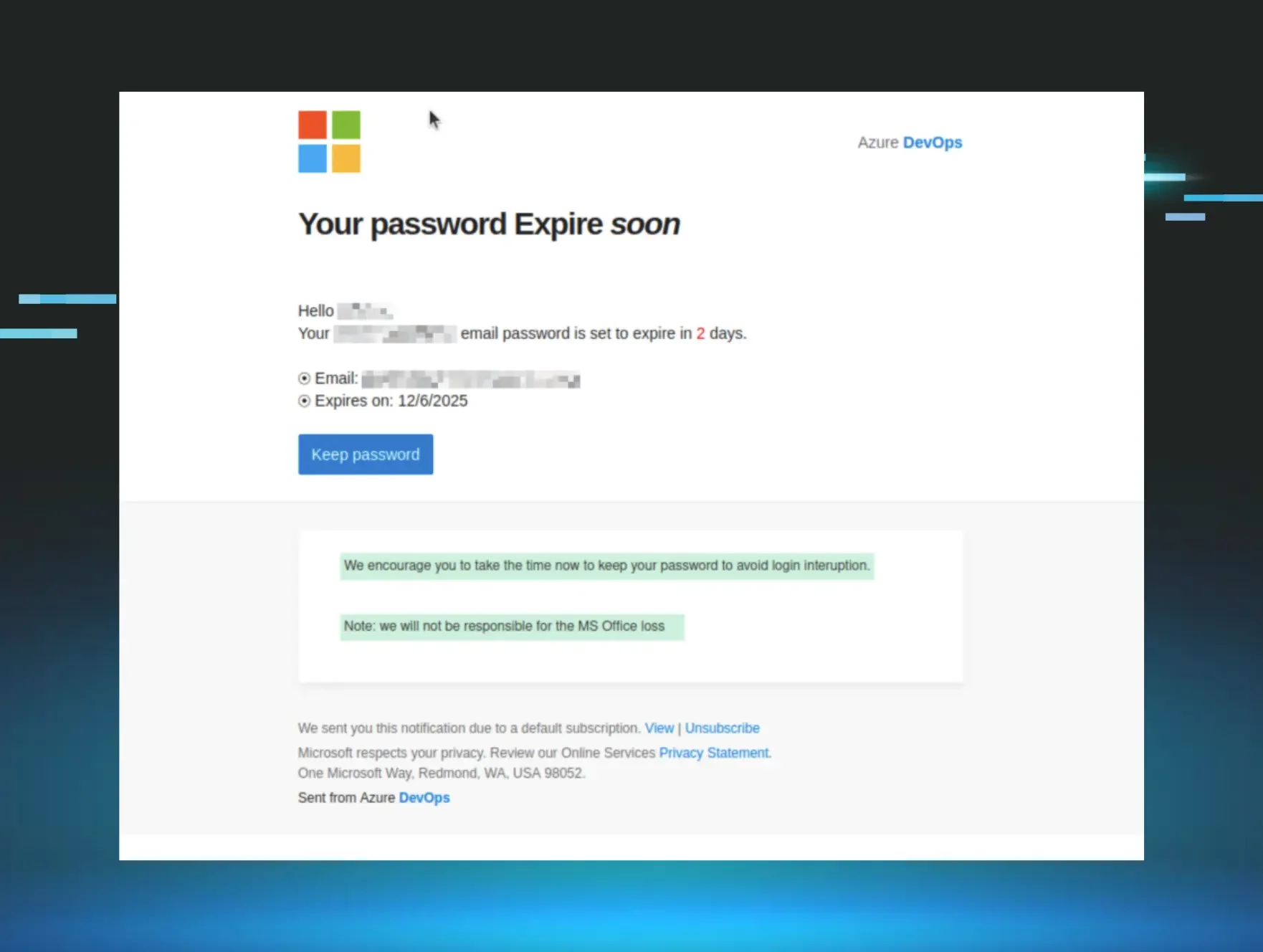
We also recently acquired a security awareness training platform to protect – and educate – the 99%.
The Myths
Now you’ve got a good idea of what it is we do, let’s take a look at some of the things we’ve heard through the grapevine.
Myth #1: Huntress can't do anything without other cybersecurity products picking stuff up first.
One component of the Huntress suite of tools – Managed Antivirus – leverages Microsoft Defender to notify analysts of threats that have been quarantined. The other tools in our arsenal don’t have the same contingency, but let’s not sleep on Managed AV. Kyle Hanslovan, Annie Ballew and Matt Anderson have shared how Huntress’ Managed AV has thwarted advanced threat actors.
Whilst Managed AV is pretty good, it isn’t perfect. Having antivirus by itself isn’t enough; monitoring and detecting capabilities are essential in today’s security landscape. With the addition of Managed EDR – Huntress’ own EDR solution—into our platform, we can see all types of attacks and follow a threat actor as they (attempt to) progress along the cyber kill chain. Whether an adversary is in their discovery phase and attempting to enumerate the Active Directory or trying to escalate their privileges, Managed EDR sees it all.
In a Summer 2022 webinar, Ed Murphy, Josh Lambert and Sharon Martin shared the Managed EDR journey. For the curious reader, you’ll also find that this webinar shines the light on real security intrusions that Managed EDR has empowered the Huntress SOC team to solve.
And moreover, the Huntress bread and butter was and is our footholds tooling. Our detections, alerts and reports for persistence are homegrown with no dependencies on other security products. This is also true for our Ransomware Canary tools.
Our External Recon tooling reveals an organization's external network perimeter, highlighting external ports and services. Analysts can gently nudge a partner or customer when they maybe have an undesirable port open to the internet they maybe don’t want exposed (I’m looking at you, RDP!).
Myth #2: Huntress does nothing to keep RMM/IT tools safe and secure.
We served as a helping hand in a particularly nasty RMM tool vulnerability in July 2021, identifying first and working with the vendor and the MSP community to help keep systems safe.
Now, this isn’t something our toolset does as a standard. This was a moment of Huntress seeing an issue and deciding we should step in and help out as we had the expertise to do so.
One thing we pride ourselves on is our community-driven mindset, so just because our tools aren’t specifically built to look into vulnerabilities in RMM/IT tools, you can bet that we’ll be right there should any future issues like the one we saw happen again. That’s just Huntress; we can’t help ourselves… Living in the shadows so you don’t have to! #ShadyByNature
Myth #3: There is no automated ransomware response built into the product.
Ransomware is all the way at the end of the cyber kill chain. A ransomware actor has to pull a ton of prior moves in a network before they make this impact. And the entire time they’re doing that, Huntress is monitoring, working with you to neutralize the security threat. Host Isolation allows us to undermine an adversarial campaign before it can materialize into a business risk.
Isolation can scale easily to include a single machine or the entire organization. In addition, partners and customers can tag specific machines so that mass isolation does not affect those tagged machines. To prevent a threat actor in the midst of deploying ransomware, for example, it has been incredibly useful to mass-isolate all machines in the domain, denying the adversary their goal of extortion.
As part of our ransomware-related suite of tools, we deploy canary files to alert us to a malicious encryption event (think of the analogy 'canary in a coal mine'—same principle).
We don’t allow anything to automatically trigger isolation. This is always instigated by a SOC analyst, who will have assessed the validity of the canary alert before quarantining the machine. Isolation denies the ransomware further propagation and ejects the threat actor from connecting to that machine.
For the curious reader, we do not automate isolation for various reasons, the chief being that false positives can trigger from the activities of legitimate, authorized encryption solutions (like Microsoft EFS). We aren’t in the business of quarantining machines for no good reason!
Myth #4: Huntress can't capture fileless attacks on endpoints.
Huntress Managed EDR once again can work on both file-based and fileless malwares, like Kovter malware, for example. Nearly everything a computer does has to be initiated through a process; we cast a wide net with Managed EDR. But let's take a step back and get a little nerdy and specific here about the fileless myth.
Whether something 'touches disk' in the form of a file, or stays in memory, it's immaterial to Managed EDR. Managed EDR is monitoring the computer's processes and doesn't rely on Windows event logs, or file system monitoring, or anything else of the kind.
And, whilst we're at it, what do members of the community mean when they say fileless?
Fileless malware may compile once it reaches the machine, or never compile and stay in memory, or use the Windows Registry as a staging ground. Harlan Carvey, a leading practitioner of digital forensics and incident response, has noted that when some in the community discuss supposed ‘fileless’ malware, they often do not realize the contradiction that the Windows Registry is still a file on the operating system.
All of this is to say, Huntress Managed EDR has your back regardless of the file form of the threat. 😉
Myth #5: Huntress just uses machine learning and AI. A real human doesn't send the reports!
What in tarnation!
Huntress definitely deploys infrastructure automation to streamline detections and evidence collection—like single-click buttons to collect Windows Event Logs when we have a really complex investigation.
However, for all of our streamlining, the 24/7 SOC team still investigates, contextualizes, drafts and sends reports. The Huntress team consists of analysts based in America, Australia and the UK, and many of the team share their very manual, very non-machine-learning approaches to security investigations:
- Detection engineer Matthew Brennan had a wildly popular post about dissecting Cobalt Strike
- Senior analyst Matt Anderson has shared firsthand real world evidence from intrusions he’s worked
- Analyst Tim Kasper has a blog post sharing his MANUAL method behind unraveling a PowerShell reverse shell
- Analyst Molly N. has shared her manual method behind unraveling Cobalt Strike in her PonchoSec blog
- Sr. Director of SOC Max Rogers has shared insight from real threat patterns we have identified in our telemetry
- Analyst and team lead Dray Agha has shared a couple of things from real-world intrusions we have manually worked [ 1 , 2 , 3, 4 ]
This isn’t to say that ML, AI or other automations are bad. They're just not how Huntress rolls. We’ve been proud to share the behind-the-scenes for the very manual, human-led investigations that Huntress is all about.
***
I hope this clears the air about some myths and misconceptions about us swirling around in the wild. Got questions? Drop us a line – we’re happy to help!
If you’re curious to gather some more technical security details from Huntress, why not check out our Tradecraft Tuesdays? These technical webinars show how hackers hack, defenders defend, and are garnished with some spicy takes from the team.