Cybersecurity is no longer just an “enterprise problem.” Businesses of all sizes are now completely reliant on technology—but at the same time, the security market is largely designed with the enterprise buyer in mind.
Before Huntress was officially Huntress, our founders realized that the cybersecurity market wasn’t taking into account the needs of small and mid-sized businesses (SMBs). They witnessed how SMBs and their IT providers were getting crushed year after year because the point solutions they were using were too complicated to manage or didn’t cover all of their gaps.
And that’s how Huntress was born—to make security simple and accessible for our partners (and to make life harder for hackers).
From day one, we’ve been laser-focused on delivering a platform that addresses the specific gaps and concerns that SMBs and their IT providers are facing. We’re passionate about building world-class security products and services for the businesses who need them most—and truth be told, we really give a shit about keeping our partners and community safe.
Because of this, our approach to product development centers around the specific needs of our partners and how modern threats are evolving. But what does that look like? How do we decide which products to build and what goes on our roadmap?
To give you a peek behind the curtain, we’d like to share some of our guiding principles for product development and how we go about building security products the Huntress way.
Building Problem-Solving Products
Products are primarily built for users. But here’s the core issue with many of today’s security products: They cater to the enterprise user. These tools assume that users know exactly what to do when a potential threat is found or an alert is raised. And you know what they say about assumptions. 😉
For small and mid-market organizations, they face a unique set of challenges. These users lack much of the knowledge, resources and budget needed to effectively manage security.
Instead of making assumptions and putting unnecessary burdens on users, we’ve purpose-built Huntress around the specific needs and pain points of our partners. This means that whether we’re adding new functionality or building on features that exist today, we always keep three guiding principles in mind:
- Reducing noise and the volume of alerts
- Bridging the cyber skills gap
- Lowering total cost of ownership
Let’s dive into each of these.
Reducing Noise
When other security tools drown users in alerts and tickets, that much data can lead to missed incidents. Instead, our goal is to help our partners focus on what really matters. That means we’re not creating tools that are noisy and spit out endless streams of alerts for our partners to deal with. We combine automated detection with teams of badass cybersecurity experts who filter out false positives and ensure we’re only sending alerts for issues that actually require attention. And the cherry on top? We’ll actually include an action plan and easy-to-follow instructions—most of which can be executed in one click.
Bridging the Cyber Skills Gap
One of the biggest challenges our partners deal with is finding and retaining top security talent. It’s really hard to find the time (let alone the resources) to acquire and train these in-house experts. That’s why we do as much of the heavy lifting as possible—so security can be one less thing for folks to worry about.
We believe that lack of expertise shouldn’t hold you back. It’s why our SOC team is the backbone of our platform and fills a critical skills gap for our partners. It’s also why we make sure everything we build is super easy to use, even for users with little or no prior security experience. And we don’t just complement our partners from a technology perspective—we dedicate time and resources to helping uplevel their cyber education and knowledge across the board.
Lowering Total Cost of Ownership
And let’s not forget about the dreaded cost conversation—all of that good security must be expensive, right? Well, it wouldn’t exactly align with our mission to secure the 99% if we were creating products they couldn’t afford, would it?
This is where our meticulously crafted balance of automation, human services and enablement really shine. By zeroing in on the specific pain points and gaps found in SMBs today, we’re able to keep our costs in check and deliver a tremendous amount of value at a price that actually makes sense for the markets we serve.
These are the core problems we aim to solve in everything we do and everything we build. And this is what continues to drive us to ensure we’re addressing our partners' top security concerns and finding innovative, cost-effective solutions to their challenges.
A Brief History of Huntress

Since we opened our proverbial doors in 2015, we’ve built our services in direct response to the areas where we saw SMBs and their IT providers needed it most.
In the beginning, that was catching what other tools missed and hunting for the persistent footholds that attackers would use to hide in plain sight and lurk in environments. And then everything changed.
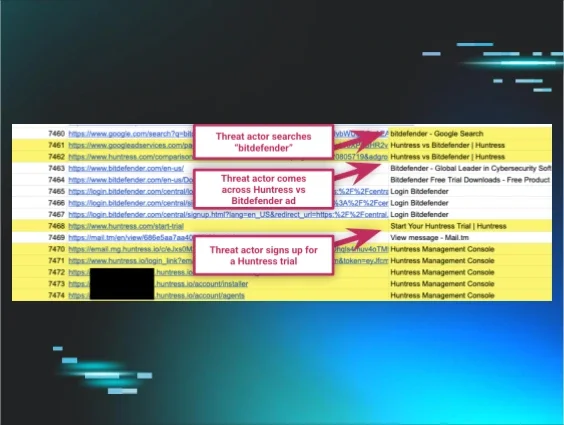
Enter ransomware. About three years ago we saw an uptick in coordinated ransomware attacks. MSPs were constantly getting hacked and all of their clients were getting ransomed. And the problem was that partners couldn’t identify ransomware until it was too late. That led us to building Ransomware Canaries, our version of a ransomware tripwire to enable quicker detection.
After that was solved, we took a step back and saw that there was a commonality: Our partners couldn’t see what attackers were seeing. They were scanning the internet looking for open ports and easy entry points. So to cut off those low-hanging fruit, we created Open Port Detection to help uncover potential entry points before hackers do.
But as always, attackers evolved their tradecraft—and in order to continue delivering on our commitment to secure the 99%, we knew we needed to expand and provide “wider” coverage across the modern attack lifecycle.
That led us to create our Managed Defender for Microsoft service, which marked Huntress’ first entry into preventive security and stopping bad actors before they had successfully infiltrated an environment. From there, we added new features like Malicious Process Behavior to ensure machines could quickly be quarantined and disconnected from a network to stop the spread of an attack as it was being carried out.
And that brings us to today. We’re always looking out for ways to provide simplified security and accessible education to the cyber community—it’s really the underlying layer of how we bring new products to life and what we decide is on our roadmap.
Product Development the Huntress Way
If you know Huntress, you know that we keep our partners and the cybersecurity community at the center of everything we do. This is why partner feedback holds an important place in our product development process.
Bringing a product or feature from vision to reality requires a mix of inputs and feedback loops. Here’s a high-level look at what this process is like at Huntress.
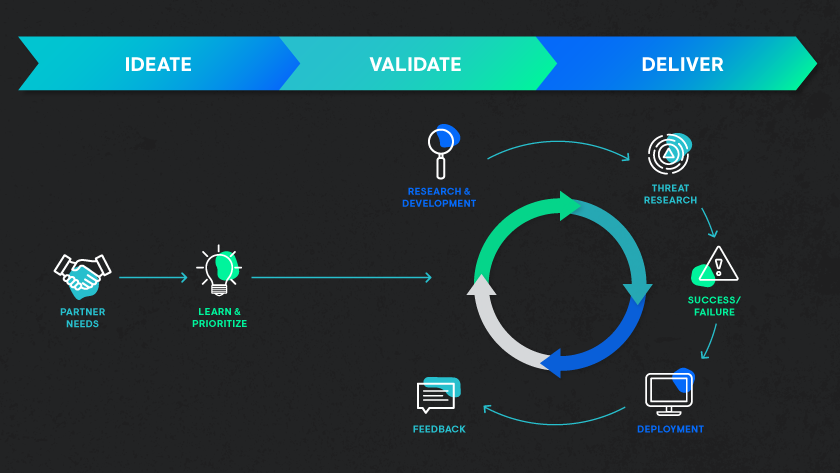
As you can see, it all starts with a need or idea. Traditionally, we pulled from our own cyber experience and what we were seeing unfold in the broader landscape—but today, our partners are our main input source.
Before we do anything, we listen. We’re always chatting with partners, whether it’s at events throughout the year, in focus groups and even through direct feedback from our platform. Our goal is to understand the security challenges they’re facing and ideate how we can solve them. And from there, we’ll hone in on the ones that we believe will provide the biggest value to our partners and make the most sense for us to solve.
After a bit of dedicated research, development and engineering, then comes the most important phase: validation. This is where we focus on feedback and iteration.
We’ll typically start with a minimum viable product that has tangible value and just enough features to ship to early users who can provide feedback for future improvement. This is also why we do beta a bit differently because we don’t want perfection to get in the way of progress—we use this stage to make sure we’re meeting needs, adapting as we go and moving toward perfection with every iteration.
Then comes delivery, the part where we share what we’ve been working on with the world! And even after delivery, we continue to validate what we’ve built to make sure we’re providing value and we’ve made the right commitments on our roadmap.
At the end of it all, what makes us the happiest is not the end result (although we're pretty damn proud of that), it’s what we hear from our partners. When we hear that Huntress has helped a partner sleep better at night or given them the confidence they needed to secure new business, what we’ve worked so hard to build is totally worth it.
Our process is driven by solving problems and making a difference. We want to make sure that we’re positioned to deliver on our promises and our roadmap without sacrificing the high bar we’ve set for ourselves, our technology, our services and our support.
What’s New and What’s Next
This year, you’re gonna see us take bigger swings and deliver a ton of new functionality that’ll help you keep pace with today’s (and tomorrow’s) threats. We’re especially focused on introducing new endpoint detection and response capabilities, enabling our partners to isolate and remediate cyberattacks in near real-time and much more.
Coming soon, you’ll see expanded coverage at each stage of the attack lifecycle. Take a look at the new Huntress Managed Security Platform and all the exciting things we’re working on in 2022 and beyond.
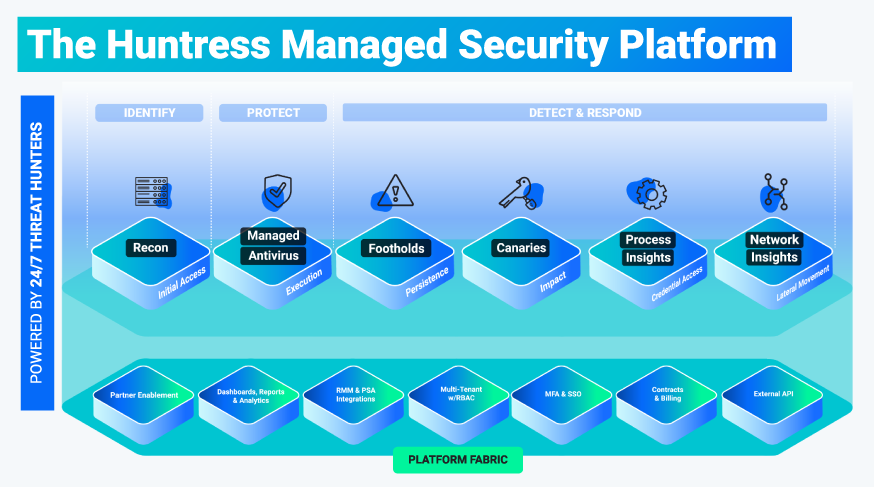
As we mentioned, our mission is to deliver world-class security to the 99%. We’ll continue to do that by increasing our coverage of attack surfaces, reducing labor costs for our partners and enabling them to keep up the good fight without burning out.
Stay tuned for more exciting news to come real soon. If you’re interested in learning more about what we’re working on right now—and how we’re building it—you’re always welcome to drop us a line.
• • •
Special thanks to Ed Murphy for helping me write this blog and share our platform vision, and of course to the entire Product and Engineering team at Huntress for their amazing work bringing this vision to life.