
What is Dark Web Monitoring?


Businesses, individuals, and organizations share one common enemy in this dark layer of cyberspace: the potential exposure of sensitive information. Dark web monitoring steps in to act as a safety net for your business’s critical data.
Are you curious about how it works, why it’s important, or how it can help protect your business? You’ve come to the right place, because we’re breaking down what dark web monitoring is and why it’s an important cybersecurity strategy in an increasingly murky digital world.
Key Takeaways
Proactive Threat Detection: Dark web monitoring acts as a digital detective agency, scanning hidden ".onion" domains and illicit marketplaces to identify if sensitive data—such as credentials, PII, or corporate intellectual property—is being sold or traded before it can be used in an active attack.
Continuous Scanning vs. Manual Search: Because the dark web "never sleeps," effective monitoring must be a 24/7 automated process. This allows businesses to receive near real-time alerts and take immediate action, such as freezing accounts or rotating credentials, the moment a leak is detected.
Strategic Intelligence Gathering: Beyond just finding leaked data, monitoring provides insight into "attacker chatter." This helps organizations understand trending attack vectors (like Ransomware-as-a-Service) and gain intelligence on what hackers are planning, allowing for a more informed defense strategy.
Mitigation Over Removal: The guide emphasizes that once data is posted to the dark web, it is nearly impossible to remove. Therefore, the value of monitoring lies in "leveling up" security—specifically through the immediate implementation of Multi-Factor Authentication (MFA) and identity restoration steps to render the stolen data useless.
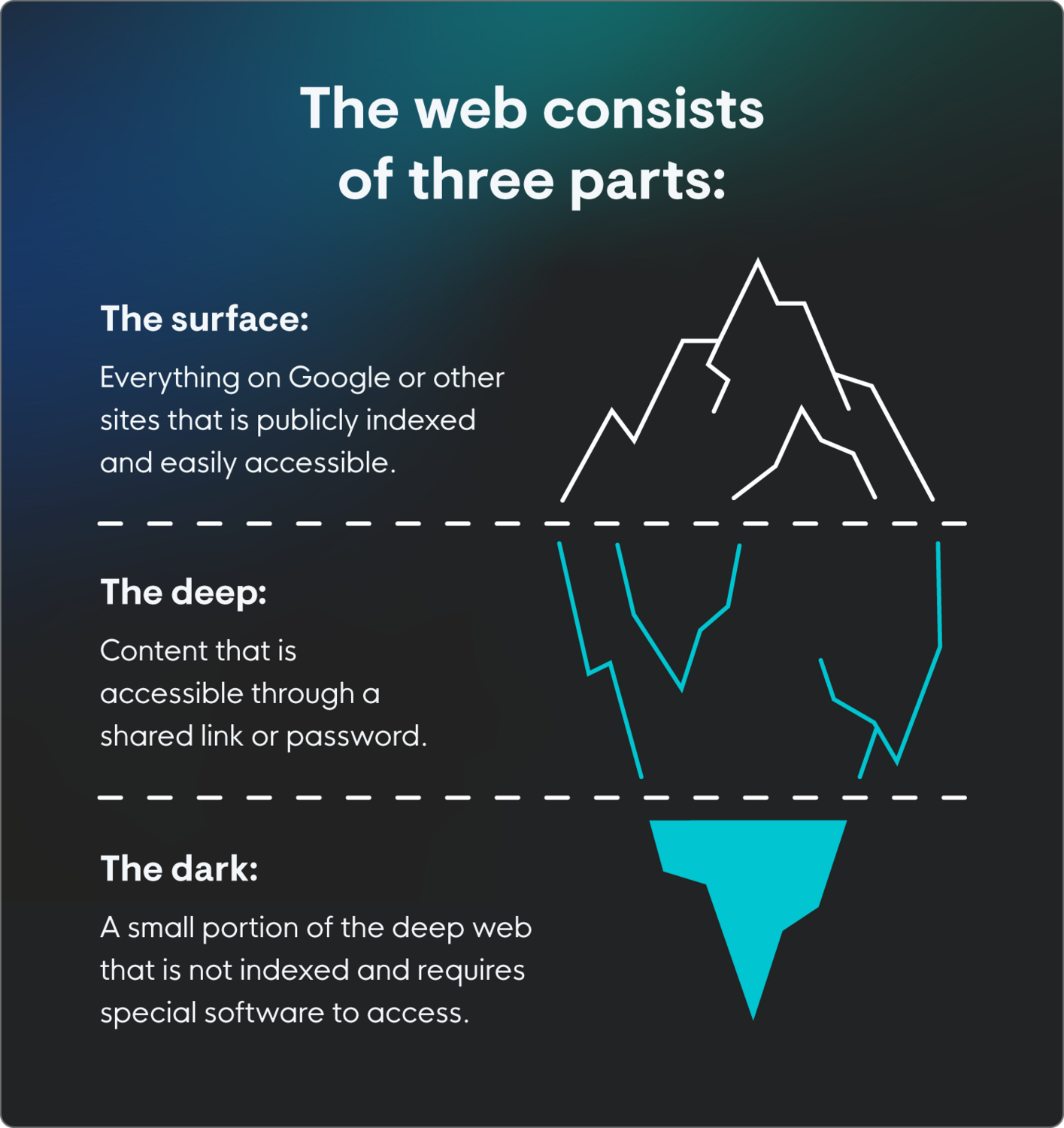
The surface web, deep web, and dark web
The internet isn’t just surface browsing we do every day through platforms like Google. It has three distinct layers that each do their own thing, depending on what you’re looking for and how much privacy you want.
Dark web monitoring tracks the layer where cybercrime goes down. It’s the deepest, most anonymous layer of the internet that most people never need to access—a digital marketplace for illicit goods and services, including cybercriminal offerings like stolen data and credentials, malware, and cyberattacks.
Here’s how it works:
Surface web: Everything you can access with a browser (think blogs, news, weather, or Google). It’s also what Google indexes and roughly 4% of the internet. Nothing shady, nothing hidden, the majority of what people use the internet for.
Deep web: Password-protected areas like email accounts, banking portals, or academic databases. It’s not always shady, just private behind a closed gate.
Dark Web: The digital cybercriminal hangout spot. It’s a small part of the internet that can’t be accessed without special tools like the Tor browser, aka The Onion Router. The dark web is where anonymity becomes dangerous, and illicit activity takes center stage.
Here’s how Tor keeps things shady on the dark web:
Routes internet traffic through a series of volunteer-operated “relays” instead of connecting directly to a server like normal internet traffic does
Data gets encrypted multiple times, and each relay decrypts only one layer to send the traffic forward to the next relay in the chain, keeping things private and anonymous between different relays
The result is that the end user’s IP address and location are hidden from relays and the dark web site they’re trying to reach
“Normally, we’re accustomed to using the Internet with a domain that’s pretty much human-readable. But when you get the Tor browser for accessing the dark web, the URLs or onion addresses are long, random strings of letters and numbers. This keeps things hidden for end users and the operators of illicit cybercriminal marketplace sites,” says John Hammond, Principal Security Researcher at Huntress.
How does dark web monitoring work?
Dark web monitoring sifts through the dark web to hunt down stolen or compromised information exposed by cybercriminals. It’s a service or tool designed to scan, track, and detect whether your information has been shared, sold, or traded on the dark web.
Think of it as an advanced digital detective agency but for your data. It looks for your digital fingerprints (email addresses, passwords, Social Security numbers, credit card numbers, bank account details, etc.) across dark web forums, black markets, and illicit websites.
Let’s break down how dark web monitoring works:
Scans hidden domains: The dark web has its tricks for staying hidden, like heavily layered encryption and unique URLs (think ".onion" rather than ".com"). Advanced monitoring tools scan these domains to hunt for activity with your sensitive information.
Content indexing: Just like how Google indexes the surface web, dark web monitoring services archive and analyze attacker chatter and files to identify trends or threats
Keyword Matching: These tools search for specific data, like your credentials, credit card details, or company files
Alerts and Notifications: If and (unfortunately) when your data shows up on the dark web, you get alerts so you can take action ASAP, like changing passwords or freezing accounts
Dark web monitoring tools are categorized into commercial and open-source options.
Commercial dark web monitoring: These services use automated tools to continuously scan the dark web for leaked information
Typical advantages include:
Near real-time alerting to suspicious activity
Analysis and prioritization of alerts to help focus on critical issues
Integration with other security tools, like security information and event monitoring (SIEM), to streamline detection and response
Disadvantages: A steep price tag and having enough resources for detection and response
Open-source dark web monitoring: Publicly available tools and resources to scan the dark web for potential threats or compromised data
Advantages: free and accessible to all
Disadvantages: limited capabilities compared to commercial options, higher rates of false positives, less access to specific private and encrypted channels
Not all tools are created equal, so do your research to make sure you’re investing in better security.
Dark web monitoring is a living, breathing, continuous process with real-time visibility into what adversaries are doing in the darkest shadows of the internet.
Why is dark web monitoring important?
The dark web is a treasure trove for cybercriminals, and your data is their loot.
Picture this: an attacker gains access to your company's customer data through a breach and sells it on a dark web marketplace. Without any monitoring in place, you’d probably find out too late or even not at all. By then, your business reputation has taken a major hit with customers and investors.
Dark web monitoring is crucial for a few key reasons:
Preventing future attacks: Monitoring activity helps identify breaches early for proactive actions
Safeguarding revenues and reputation: Nobody wants their brand name linked to a public data breach. Protect your business from PR nightmares.
Thinking like an attacker: See for yourself what’s flying off the shelves of dark web marketplaces. Check out the latest go-to malware and trending attack vectors: infostealers, Ransomware-as-a-Service (RaaS), exploit kits, botnets, etc. More awareness is always a better defense.
Compliance regulations: Certain industries, like healthcare and finance, are held to strict data protection regulations. Ignoring security risks isn’t an option for closely regulated industry verticals, so comprehensive attack surface monitoring is critical.
Stronger incident response (IR): Helps organizations understand the scope of a breach
“People think they have anonymity and privacy because they’re operating within the dark web behind Tor services. But if you have something monitoring and listening, you can get intelligence on what hackers are scheming about and what they’re talking to each other about. It’s super important to get insights into knowing where threats are, how to protect for the future, and prevent attacks on the horizon,” says Hammond.
The dark web never sleeps, and neither do attackers. Make sure your security strategy is ready for that.
Data on the dark web
Buckle up, because the dark web is a wild ride! If you’re wondering what lurks in this part of the internet, here’s a (somewhat terrifying) list of things you’ll find:
Personally identifiable information (PII): Names, addresses, Social Security numbers, contact details
Financial data: Credit card numbers, payment processing services, bank account information, crypto wallet keys
Credentials: Email addresses, passwords, login details, two-factor authentication bypass methods, hacked services, and social media
Corporate data: Intellectual property, trade secrets, source code, customer databases, and employee records
Medical records: Protected health information (PHI), insurance information
Marketplace goods and services: Counterfeit documents (passports, driver's licenses, utility bills), hacking tools, and even illegal substances
Government and military information: Classified documents, personnel information, strategic plans
Security information: API keys, RDP passwords, cloud infrastructure logins, and other things to get access to IT systems
Distributed denial of service for hire (DDoS-for-hire): Access to disrupt or shut down website operations. For example, get into an unprotected website with 10-50K requests per second for 24 hours.
Data prices on the dark web vary a lot depending on how complete the data set is, supply and demand, and how easily cybercriminals can make money from it. Marketplaces are constantly being updated with new items and prices.
Here’s a great reason to stop recycling your passwords: credentials for consumer accounts like a streaming service are worth more on the dark web when you reuse them for a work account or business platform. A set of credentials starts at a five-dollar price point and increases to hundreds or even thousands of dollars if it gives an attacker initial access to an enterprise business account.
If it’s valuable to you, it’s likely valuable to cybercriminals, and they’ll want to sell it for a quick, untraceable buck in this digital black market carnival.
My information is on the dark web: what does this mean?
Unfortunately, once data is available on the dark web, it is nearly impossible to remove it. But don’t panic! There are steps you can take to block attackers if they buy their way into your accounts and networks:
Change passwords: Update your login information ASAP for any accounts available on the dark web. This is your friendly reminder to brush up on security hygiene.
Put up more barriers: Turn on MFA. No exceptions. It makes your accounts tougher to compromise, especially when you set up biometrics as an authentication method.
Monitor transactions: Carefully watch financial accounts. Report any suspicious activity to your bank.
Freeze accounts: If payment information is exposed, freeze bank accounts or cards
Get help from the pros: Some services provide dedicated identity theft restoration experts who can guide you through recovery
Once you know private data is up for grabs on the dark web, you have to level up your security game to quickly wrangle more potential damage.
Is dark web monitoring included in identity protection services?
The short answer? It depends. But some identity protection services like Norton LifeLock and Experian offer dark web monitoring as part of their plans. These services go beyond alerts, often helping with identity restoration or even financial reimbursement in case of losses.
Dark web monitoring for threat intelligence strategies
It’s like having an early warning system in your cyber threat intelligence playbook. Enterprises often integrate dark web monitoring into their threat intelligence strategies, using it to:
Proactively identify fraud risks
Sniff out potential attacks
Manage brand reputation
Dark web monitoring by industry
Any business can benefit from dark web monitoring, but some industries like these get the most out of it:
Finance: safeguarding sensitive financial data and accounts
Healthcare: PHI and PII exposure from ransomware attacks, like the Change Healthcare incident in early 2024, where a $22 million Bitcoin ransom payment led to double extortion schemes by RaaS groups.
Retail and e-commerce: Monitoring for stolen customer payment details or loyalty program fraud
Technology: Watching for exposure of intellectual property, like proprietary source code
Can dark web monitoring be integrated into a SIEM or SOAR platform?
Many large-scale enterprises integrate dark web monitoring tools directly into their SIEM or SOAR (Security Orchestration, Automation, and Response) platforms. This lets teams monitor and react to threats in real-time without delays.
How often should dark web scans be performed?
Ideally, dark web scans should be 24/7 and continuous. Since new breaches happen all the time and marketplaces are constantly being updated with new “merchandise”, real-time monitoring makes sure you don’t miss critical threats. For businesses, automated scans are a no-brainer.
Keep your data out of the dark
Dark web monitoring isn’t just a nice-to-have—it’s a critical security layer in today’s technology-driven world. The ability to monitor and respond to data breaches can save your organization from identity theft, financial loss, and long-term cybersecurity headaches.

Additional Resources
- Read more about Deep web vs dark web explained for cybersecurityUnderstand the critical differences between the deep web and dark web. Learn how cybersecurity teams monitor, mitigate threats, and secure sensitive data.
- Read more about What is the dark net in cybersecurityWhat is the dark net in cybersecurityDiscover the dark net’s impact on cybersecurity and learn how professionals use monitoring tools to mitigate risks.
- Read more about What is Dark Web Activity? | Cybersecurity GuideWhat is Dark Web Activity? | Cybersecurity GuideLearn what the dark web is, how it hosts illicit activity, and why cybersecurity pros monitor it. See how to protect your data from dark web threats.
- Read more about What Is Database Monitoring? Why It's EssentialWhat Is Database Monitoring? Why It's EssentialLearn what database monitoring is, why it’s critical for performance, uptime, and security, and how modern tools help businesses detect issues before they escalate.
- Read more about What Is Phishing? How Phishing Scams Affect BusinessesWhat Is Phishing? How Phishing Scams Affect BusinessesDiscover what phishing is, its impact on businesses, and how to protect against phishing attacks with actionable strategies and tools like Huntress.
- Read more about What is a Tor Mirror? Tor in Dark Web | Tor Cybersecurity GuideWhat is a Tor Mirror? Tor in Dark Web | Tor Cybersecurity GuideLearn what Tor mirrors are, how to safely access them, and essential security practices for using the Tor network. Complete guide for cybersecurity professionals.
- Read more about What Is a Web Server? | Cybersecurity 101What Is a Web Server? | Cybersecurity 101Learn what a web server is, how it works, and why it’s critical to cybersecurity. This beginner-friendly guide covers everything you need to know.
- Read more about What Is Server Monitoring? Complete GuideWhat Is Server Monitoring? Complete GuideLearn what server monitoring is, why it's critical for cybersecurity, and how to implement effective monitoring strategies to protect your IT infrastructure.
- Read more about What is Web Shell? A Guide for Cybersecurity ProfessionalsWhat is Web Shell? A Guide for Cybersecurity ProfessionalsLearn what a web shell is, how it’s used in cyber attacks, and the best ways to detect and prevent it.


Protect What Matters











