In 1982, a 15-year-old high school student named Rich Skrenta made history when he wrote the code for the world’s first known computer virus released into the wild. The virus, Elk Cloner, was a harmless virus copied onto game disks that Skrenta shared with friends. On the disk's 50th launch, a poem would appear on-screen instead of the expected game.
Today, viruses and other malicious software are much more sinister. Threat actors often use them to exploit computer systems, steal data, disrupt business productivity and damage businesses’ reputations.
Not only are these threats growing more sinister, but they’re also becoming more costly every day. Experts predict that cybercriminals will cost the world a staggering $10.5 trillion annually by 2025. This will make cybercrime the third-largest economy in the world.
While small to mid-sized businesses (SMBs) and their managed service providers (MSPs) are beginning to invest more in cybersecurity, much of their focus is on preventive tools. Of course, preventive tools are an important component of any security stack, but prevention is only part of the solution.
As hackers get smarter, they’re bound to slip past these preventive tools. What happens then? This is where threat detection can protect you and your clients.
There’s one universal truth to adding better threat detection and response to your security offering: it has to be cost-effective. Prepping your SMB clients prior to implementing additional cybersecurity measures is essential.
Who Should Invest in Threat Detection and Response?
When you’re looking at adding or improving your security operations, you’re faced with a few critical choices:
- Do you offer security as a standalone service?
- Do you include security but increase the price of your packages to cover the additional costs?
- Do you include security but absorb the costs to provide a better offering?
The answer to this choice depends on how mature your business is.
If you’re new to the business, chances are you just want to increase the number of clients you serve. Offering standalone managed detection and response services is easier, and you can charge your customers per solution.
However, if you’re a more established MSP or managed security service provider (MSSP), you probably have standardized packages already in place. This provides better operational scalability. You can include security but offer different tier options so more regulated industries like legal, finance and healthcare can purchase more advanced options.
By offering different tiers for your threat detection services, you can scale to meet the needs of your customers while still maintaining your operational efficiency.
Selling Security as a Managed Service Provider
Selling security comes down to one thing: knowing how cyberattacks affect your IT operations. As a managed service provider, you ensure that phones are working, email is operational, documents are shared, websites are functioning and that orders and transactions are being processed.
Your internal departments within your organization depend on these things to work so they can work together to provide the service and products you’ve promised your customers and that they’ve promised their end users. Anything that impacts this ability to work together threatens to bring all that to a screeching halt.
A robust and effective threat detection and response system can help protect your customers from hackers disrupting their workflow.
Demonstrating the Value of Cybersecurity Tools to Your Clients
Let’s cut to the chase—the cost of your services is likely a top-of-mind concern for the SMBs you provide services to.
As an MSP, your customers trust you to make the necessary decisions to develop the right cybersecurity stack to keep their environments secure. However, no matter how confident you are in the stack you’ve developed, when it comes time to discuss how much the stack will cost, the conversation can feel awkward.
You have to demonstrate the value of the tools you’re implementing to show that the cost is worth the security—and the peace of mind—the stack will enable. One way to do this is to show the potential cost of not having the right security tools in place. Our Cost of Downtime calculator can help facilitate this discussion with your clients.
Adding the Human Element to Threat Intelligence Tools
No matter what security toolset you have, you’ll never be able to fully protect yourself or your customers without adding a human element to your threat detection and response.
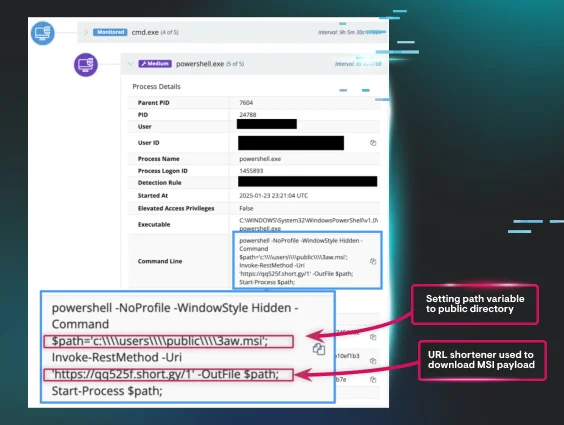
Automation certainly has its strengths. It can quickly analyze large data sets and run rapid analyses based on predefined rules and methods. However, automation lacks two important traits that only human threat hunters can offer: context and experience.
To enable the best defense against threats, you need a person or team that can
- analyze incident reports and execute the necessary remediation steps
- understand the context if the end user is using unlicensed software
- know when and when not to isolate or disable questionable software
By combining the speed of automation with the skillsets and contextual knowledge of human threat hunters, you're harnessing the best of both worlds to ensure your environments are protected.
Provide Threat Intelligence Tools for Your SMB Clients
Huntress specializes in performing detection and response at the same time. We combine automated detection with human analysis from our ThreatOps team and offer a powerful solution to prevent your MSP from being compromised by cybercriminals.
We also strongly advocate for cybersecurity education because that can often be the key to stopping a cyberattack. To increase your knowledge base, check out some of our cybersecurity education resources:
Want to know if Huntress is the solution to help you provide a better security offering for your customers? Take it for a test drive with a free trial.