Cyber Threats Explained
Written by: Beth Robinson
Published: 8/17/2025



Being dialed into cyber threats is like bracing for a storm you know is coming, but instead of rain, it’s malware, phishing scams, and ransomware pouring down. Cyber threats aren’t just hitting big enterprises or government systems anymore. Businesses and organizations of every size and industry vertical are in the crosshairs of shady hackers. So being aware is your best baseline defense against cyber threats.
In this blog, we break down all the things you need to know about cyber threats: what they are, the motivations and attackers fueling them, and how to stay savvy against them.
What are cyber threats?
A cyber threat is any shady move in cyberspace to damage, disrupt, steal, or get unauthorized access to computer networks or systems. It’s any potential danger posed by hackers, viruses, insider risks, or badly managed software that compromises security controls. Think of cyber threats like digital burglars lurking in shadows, waiting to pounce on your vulnerabilities.
This might sound scary (and it should!), but tuning in to understand these cyber pitfalls is the first step in getting your organization to shut them down fast.
Cyber threat vs. cyberattack
A cyber threat is the potential for an attacker to exploit a vulnerability in your systems and networks. You know it can happen, but you’re not dealing with an active threat (yet).
On the other hand, a cyberattack is when attackers target a vulnerability, whether it be with malware, adversary-in-the-middle (AiTM) attacks, ransomware, or something else. This is when a cyber threat becomes a reality.
Understanding both of these concepts helps your organization rack and stack proactive defenses. When you piece together the right security controls, you’ll identify cyber threats early and prevent full-blown cyberattacks.
Threat actors: the bad guys behind cyber threats
A threat actor is a person or group that is behind cyber threats or attacks. They’re the bad guys in the dark digital alleyway.
There are different types of threat actors. While some may fall into multiple categories or have more than one goal, here are the common types that we see:
Cybercriminals: Hack for money
Hacktivists: Hack for ideological or political goals
Nation-State Actors: Hack for governments, usually running sophisticated and long cyber espionage campaigns
Breaking down threat actors’ motives and behaviors helps you build a stronger, smarter security strategy from the ground up.
Threat actor motivations
Understanding threat actor motivations can help uncover how they operate and why they’re breaking into networks:
Cybercrime
These attacks by cybercriminals are financially motivated: identity theft, credit card fraud, phishing, and ransomware attacks
Cyber Espionage
This involves stealing confidential or sensitive information, like proprietary corporate data, for political or financial advantage. Cyber espionage is often used by state-sponsored attackers like Advanced Persistent Threat (APT) groups.
Hacktivism
Hacktivists disrupt systems, steal data, and deface websites to promote political or social agendas
Cyber Warfare
This refers to cyberattacks on a nation-state level to disrupt and destabilize infrastructure, economies, and governments
Top cyber threats to watch out for
Threat actors have a lot of tricks up their sleeves, and cyber threats can come from any direction.
Here are some of the top (but not all) cybersecurity dangers you need to keep on your radar:
Malware
Malware or malicious software is a broad term that includes viruses, trojans, ransomware, infostealers, and spyware. It gives threat actors the power to compromise systems and networks, steal data, persist in infrastructure, and log keystrokes.
Phishing attacks
Phishing is a type of technique where attackers pose as a trusted entity, like a bank, a legitimate vendor, or even a colleague, to trick you into sharing sensitive information, clicking malicious links, or downloading harmful attachments.
Ransomware
Ransomware is a type of malware that blocks access to computers, systems, and networks. Attackers encrypt or steal sensitive data, lock up endpoints, and send a ransom message demanding cryptocurrency payment within a short timeline.
Zero days
Zero day vulnerabilities are security flaws in software, hardware, or firmware that haven’t been found and patched by the vendor. A zero day exploit is a code or strategy that takes advantage of an undiscovered flaw in a zero day attack. Since attackers exploit zero day vulnerabilities before vendors have a shot at patching them, this gives them the upper hand with their targets.
Brute force attacks
This hacking technique uses trial and error to guess login credentials or other sensitive information. Brute force attacks take advantage of computing power and automation, using automated tools to try password combinations until they hit the right one. If you catch Event ID 4625, Failed Logon Attempt, in your Windows security log, make sure to take a closer look—it could be a brute force attack.
What is an insider threat in cybersecurity?
Insider threats are grouped into three categories:
Malicious insiders: People who intentionally abuse their access privileges to hurt the organization. An employee who downloads sensitive information to a USB drive for personal gain on their final day in the company, for example. They’re usually motivated by money, revenge, or ideologies.
Compromised insider: Employee accounts and devices that are compromised by attackers, like being tricked into sharing credentials through a phishing attack. The compromised individual is an unknowing victim in these situations.
Negligent insider: People who are careless, unaware, or lazy about security hygiene. An insider who uses weak passwords exposes an organization to brute force attacks, for example.
Here are some ways to cut down insider risks:
Build security policies and procedures around the principle of least privilege for less access to confidential information
Monitor and detect to catch sketchy end-user activities
Teach the workforce about insider threats and what to look out for
What is cyber threat intelligence?
Cyber threat intelligence (CTI) is understanding what adversaries are doing and how they’re doing it, and finding ways to detect, disrupt, and gain advantages over them. Attackers constantly find creative ways to exploit vulnerable exposures in your environment and avoid detection. Threat intelligence contextualizes raw threat data from these attacks on your attack surface and transforms it into meaningful insights that organizations can use to make informed decisions about defending against cyber threats, whether those threats target networks, systems, data, or people.
Think of it as cybersecurity’s eyes and ears, keeping tabs on bad actors and their sketchy activity for early warning on potential attacks. CTI helps organizations:
Predict novel cybercriminal tactics
React faster by being aware of ongoing threats
Build stronger defenses with unique cyber threat insights to fix vulnerabilities
CTI is a game-changer for modern cybersecurity programs, especially when it’s combined with Managed Security Information and Event Management (SIEM).
What is threat hunting?
Threat hunting is a forward-thinking, hands-on approach to finding potential threats hiding quietly in your environment.
Unlike traditional defenses like firewalls or antivirus software that react to threats that’ve already happened and been detected, threat hunting actively searches for suspicious behavior that might otherwise go unnoticed.
It usually involves:
A gut feeling: Using CTI, Managed Endpoint Detection and Response (EDR), or SIEM data to scope out where threats will crop up
Investigation: Systematically searching networks for compromise red flags
Validation: Confirming and fixing threats
Threat hunters are worth their weight in gold, uncovering threats before disaster strikes.
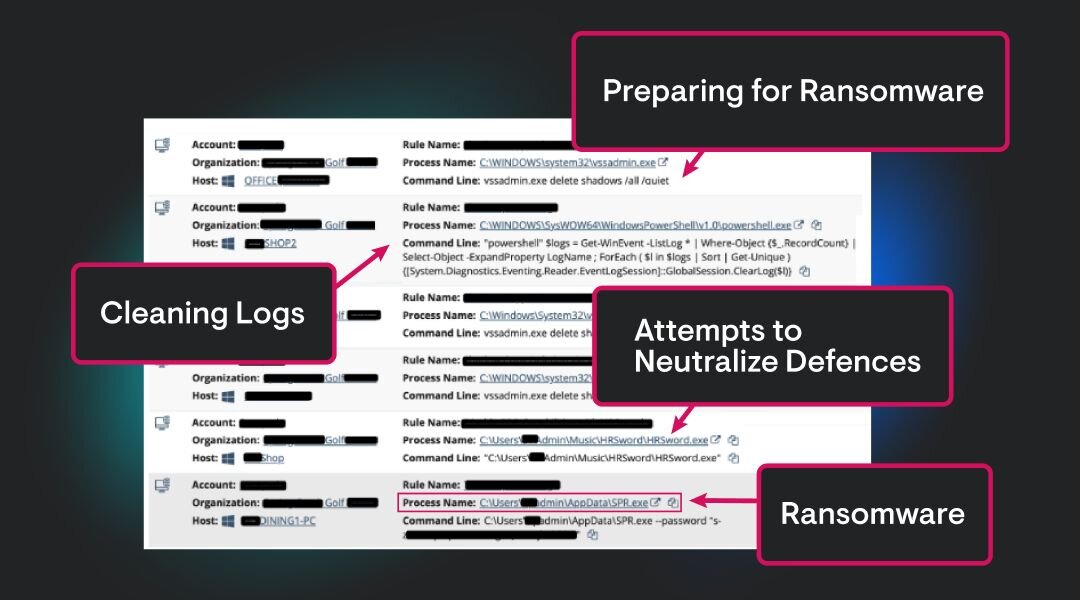
Check out this example from Anton Ovrutsky to see threat hunting in action from our Security Operations Center (SOC).
How to keep cyber threats out
Staying safe from cyber threats isn’t easy, but it’s very achievable. Here are common security solutions to defend against potential cyber threats:
Cyber threat intelligence platforms (TIP): Dive deep into how adversaries are targeting your industry vertical and level up your predictive cyber threat game
Zero trust policies: Assume no one inside or outside your network can be trusted without multiple layers of authentication
SIEM: You need an early warning system, especially with ransomware constantly looming on the horizon
Managed Security Awareness Training (SAT): Make your workforce your sharpest security tool
Endpoint security: Outsource endpoint protection to Managed EDR experts who have 24/7 bandwidth to catch attackers
Closing Thoughts
To secure your organization the right way against today’s cyber threats, it's crucial to stay sharp about who is behind them, their tactics, where they’re coming from, and when they’re likely to sneak up on you.
By knowing this part of the threat landscape, you’ll build a stronger security stack to deflect and defend against cyber threats.

Additional Resources
- Read more about What is a Threat Actor? How To Spot and Avoid Rising ThreatsWhat is a threat actor? Learn key definitions, types, motivations, and how to detect them in your network with expert insights and Huntress examples.
- Read more about Understanding Today’s Threat Landscape & Mitigating Cyber RiskUnderstanding Today’s Threat Landscape & Mitigating Cyber RiskGain an understanding of what today’s threat landscape looks like with advanced cyber threats, common risks, and how to defend your business.
- Read more about What is Threat Actor Profiling? | Cybersecurity GuideWhat is Threat Actor Profiling? | Cybersecurity GuideLearn how threat actor profiling helps organizations identify, analyze, and defend against specific cyber adversaries through targeted intelligence and strategic planning
- Read more about Brute Force Attacks Explained: How They Work & How to Stop ThemBrute Force Attacks Explained: How They Work & How to Stop ThemLearn how brute force attacks work, why they're still effective, and how to defend against them. Explore real-world examples and proven prevention strategies for IT security teams.
- Read more about What is Weaponization in Cybersecurity?What is Weaponization in Cybersecurity?Learn how weaponization fits into the Cyber Kill Chain, why it’s critical, and how IT teams can defend against evolving cyber threats.
- Read more about What is DDoS?What is DDoS?Learn what DDoS attacks are, how they disrupt systems, and how to defend your organization against these cyber threats. | Huntress
- Read more about Comprehensive DNS Protection Guide - Stay Ahead of Cyber ThreatsComprehensive DNS Protection Guide - Stay Ahead of Cyber ThreatsLearn how DNS protection strengthens your cybersecurity posture. Discover best practices, setup tips, and the importance of regular updates to safeguard against evolving threats
- Read more about What Are TTPs? Cybersecurity Tactics ExplainedWhat Are TTPs? Cybersecurity Tactics ExplainedLearn about TTPs (Tactics, Techniques, and Procedures) in cybersecurity. Understand their role in threat detection and defense strategies.
- Read more about What is Password Spraying? How Cybercriminals Exploit PasswordsWhat is Password Spraying? How Cybercriminals Exploit PasswordsLearn what password spraying is, how these cyberattacks work, and proven strategies to defend your organization against this common brute force technique.


Protect What Matters