What is a 419 Scam?



When you hear the term “419 scam,” you might immediately think of an infamous email from a so-called Nigerian prince offering you a share of unimaginable wealth. While the stereotypes are humorous, the real-world impact of these scams is no laughing matter.
A 419 scam, named after Section 419 of the Nigerian Criminal Code, is a type of advance-fee fraud that entices victims to pay upfront fees in exchange for promises of vast rewards. Though the tactics are often simple, the damage can be complex, ranging from financial loss to identity theft. These scams remain a global cybercrime issue, costing individuals and organizations millions annually.
This guide will break down what 419 scams are, how they work, and how you can protect yourself or your organization from falling victim to one of these scams.
What Is a 419 Scam?
At its core, a 419 scam is a financial fraud scheme that tricks victims into sending money or sharing sensitive information under false pretenses.
Here’s how it often plays out:
The hook: Scammers claim you’ve won a lottery, inherited a fortune, or been chosen for a lucrative investment or charity opportunity.
The catch: There’s always an “advance fee.” This might be framed as a legal fee, tax, processing cost, or transportation expense.
The vanish: Once the payment is made, the scammers disappear or continually ask for more excuses as to why you must pay further fees.
Common delivery methods:
Scammers employ a variety of platforms to reach their targets, including:
Email (the classic “Nigerian prince” scenario)
Text messages
Social media direct messages
Traditional letters
How 419 Scams Work Step by Step
Many 419 scams follow a step-by-step framework designed to exploit trust and emotions.
1. Initial Contact
Scammers typically send unsolicited messages that include emotional appeals, such as urgency or financial desperation. Examples include:
"I am a diplomat unable to transfer my $10 million inheritance without your help."
"You are the only one who can claim this uncollected fortune from a deceased relative!"
2. The Bait
To pull victims in, scammers promise large sums of money or significant rewards for small sacrifices. They often:
Fake credibility with official-looking documents, stamps, or seals.
Exploit emotions like greed, sympathy, or urgency.
3. Trust Building
Fraudsters often introduce layers of false legitimacy by creating:
Fake lawyer profiles
Pretend bank agents
Elaborate backstories complete with staged phone calls and official-looking forms
4. Advance Fee Request
Next comes the scammer’s “ask.” They’ll request upfront payments for tasks like:
“Processing fees”
“Customs clearance”
“Lawyer’s services”
5. Escalation
Once trust is established, scammers exploit it further by:
Enforcing secrecy (“No one else must know about this deal!”)
Introducing repeated fees or blaming delays on unforeseen legal hurdles
6. Ghosting the Victim
Eventually, the scammers disappear, leaving victims unable to recoup their losses.
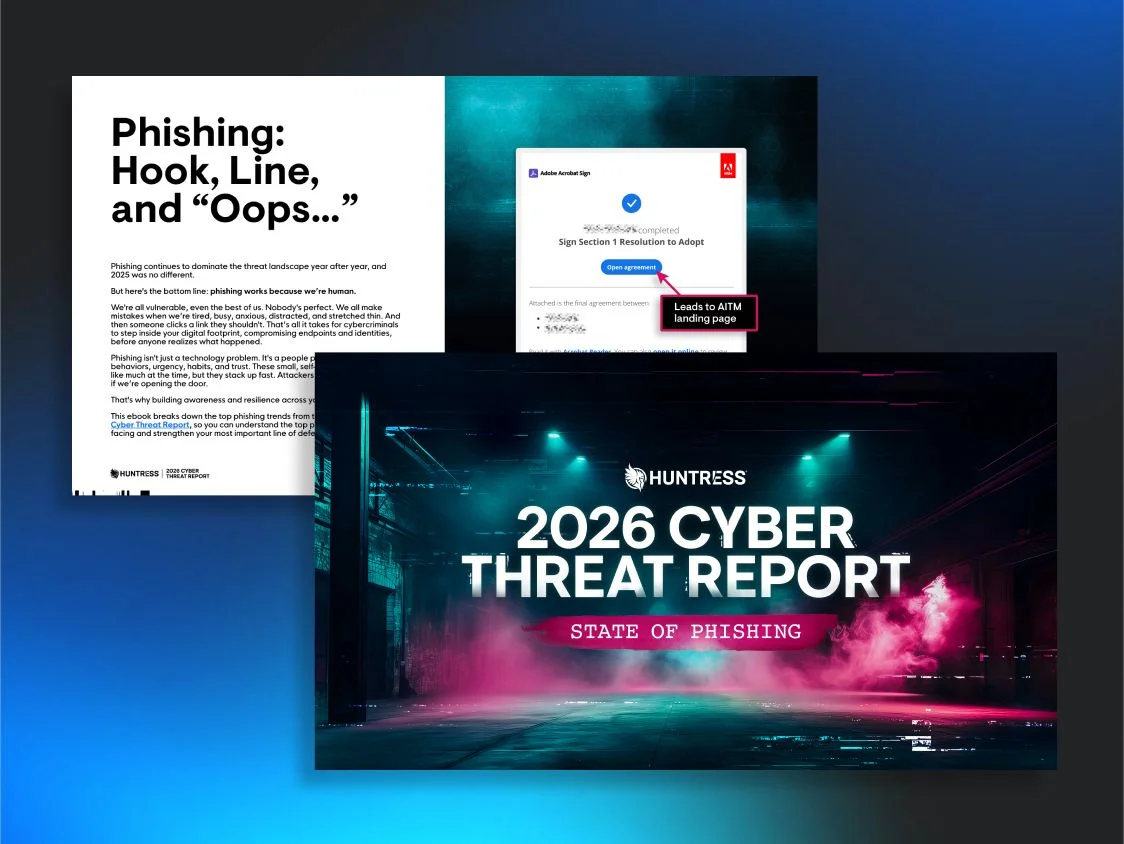
Mind the (Security) Gap: SAT in 2025
The 419 scam has been upgraded with convincing phishing emails and spoofed identities that make advance-fee fraud harder to spot than ever, so download the Huntress State of Phishing report to see which psychological triggers and impersonation techniques are most effective in 2026 and how to stop them before they fool your team.

Examples of Common 419 Scam Themes
419 scams come in different flavors, each tailored to exploit a victim’s specific vulnerabilities. Here are some of the most prevalent themes:
Nigerian Prince/Diplomat Scams: The is a classic one involving a “wealthy Nigerian royal” who needs your help transferring money. (I bet you’ve received a few of the emails at some point.)
Inheritance Scams: Victims are told they’re the only heir to an unclaimed fortune but must pay to release it.
Job Offer Scams: These scams offer fake employment opportunities requiring upfront “application” or “visa” fees.
Romance Scams: Scammers build emotional connections before leveraging trust to request money. These often prey on older people who are looking to make new relationships.
Charity Scams: Requests for donations in emergencies, such as natural disasters, often tug at victims’ hearts.
419 Scam vs Phishing and Business Email Compromise
It’s easy to confuse 419 scams with other types of cybercrimes. Here’s a quick comparison to clarify the differences:
Attack Type | Goal | Method | Common Targets |
419 Scam | Financial gain | Advance fees, deception | Individuals |
Phishing | Credential theft | Fake logins, malicious links | Individuals and businesses |
Business Email Compromise (BEC) | Financial fraud | Email spoofing, impersonation | Enterprises |
Why 419 Scams Are a Cybersecurity Concern
While 419 scams seem outdated compared to sophisticated malware, they remain relevant to the modern cybersecurity landscape for several reasons:
They bypass traditional security measures like spam filters by relying on social engineering tactics instead of malware.
They’re often connected to broader fraud networks and organized cybercrime rings.
They can serve as learning opportunities in cybersecurity training programs, particularly in enhancing phishing awareness.
Bolster your team’s awareness of 419 scams with security awareness training. Huntress Managed Security Awareness Training offers episodes covering Phishing, Social Engineering, Smishing, Business Email Compromoise, and Phishing Defense.
Tactics Scammers Use
Here’s how scammers get victims to fall for their deceitful schemes:
Social Engineering: Playing on emotions like greed, fear, or loneliness.
Impersonation: Claiming to be lawyers, diplomats, or bankers to gain credibility.
Urgency and Secrecy: Pressure to act quickly and keep the transaction confidential.
How to Detect and Prevent 419 Scams
Look for these warning signs:
Offers that sound too good to be true.
Emails with grammar errors or unfamiliar sender addresses.
Requests for urgency or secrecy.
Demands for personal details or upfront fees.
Prevention tips:
Educate yourself and your team. Cybersecurity awareness training is critical to spotting scams.
Enable robust spam filters. Keep scam attempts out of inboxes.
Verify sender identities. Always cross-check unknown contacts.
Report scams. Tools like the FBI’s Internet Crime Complaint Center (IC3) allow users to report fraud.
Assume Malice. Assume any inbound unexpected email is malicious in nature.
The Legal Side of 419 Scams
The term "419" originates from Nigeria's Criminal Code, which criminalizes fraud schemes. However, prosecuting these scams is challenging because:
The perpetrators are often overseas, making jurisdiction complex.
Digital anonymity tools make tracking scammers harder.
Law enforcement agencies like Interpol and Nigeria's Economic and Financial Crimes Commission (EFCC) actively combat 419 scams, but global cooperation is key to taking down these fraud rings.
The Best Defense Against 419 Scams
419 scams may seem low-tech compared to modern cyber threats, but they prove that social engineering is timeless. By staying skeptical, alert, and educated, you can avoid becoming a victim.
For cybersecurity professionals, incorporating 419 scams as examples in security awareness training can better protect your company against these fraud tactics.
Remember, when it comes to unsolicited promises of easy money, if it sounds too good to be true, it probably is.
Need expert help identifying and combating scams? Try Huntress Managed SAT for free and make life harder for hackers while giving your admins and learners something to smile about.
FAQs on 419 Scams
A 419 scam is a type of fraud often involving emails or messages where scammers promise large sums of money in exchange for small upfront payments. The term "419" comes from the section of the Nigerian Penal Code that addresses fraud.
Scammers typically contact victims claiming they're entitled to inheritances, lottery winnings, or unclaimed funds. They then ask for advance fees for processing, taxes, or legal documentation. Once the fees are paid, the promised payout never arrives, and the scammer disappears.
Beware of unsolicited emails or messages offering money, especially if they:
- Promise huge rewards with minimal effort.
- Ask for upfront fees or sensitive information like bank details.
- Contain poorly written language or dramatic stories of urgency.
- Pressure you to act quickly to "secure the deal.
- Cease communication immediately.
- Do not send any money or share personal information.
- Take screenshots or save copies of the messages as evidence.
- Report the scam to law enforcement or relevant agencies.
- Visit the FBI Internet Crime Complaint Center (IC3) to file a report.
- Use the FTC’s ReportFraud site to notify authorities.
- Depending on your location, contact your local police or cybersecurity authorities for further assistance.



Additional Resources
- Read more about What Is a Romance Scam? | Cybersecurity 101Learn what romance scams are, how they work, warning signs to watch for, and how cybersecurity professionals can help protect organizations and individuals.
- Read more about What Are Common Cash App Scams? Spot & Prevent FraudWhat Are Common Cash App Scams? Spot & Prevent FraudLearn about common Cash App scams like phishing, fake support, and “cash flips." Protect yourself with tips to spot and report fraud.
- Read more about What's a Scam? Your Guide to Spotting and Avoiding FraudWhat's a Scam? Your Guide to Spotting and Avoiding FraudLearn what a scam is, how scams work, common types, and tips to protect yourself. Stay safe online with practical scam awareness advice.
- Read more about Pig Butchering Scam: Signs, Examples & How to Protect YourselfPig Butchering Scam: Signs, Examples & How to Protect YourselfPig butchering is a long-term romance scam where criminals build fake relationships before luring victims into fraudulent investments. Learn the red flags, see 2024 stats, and protect yourself.
- Read more about What Is a Scam Likely Call and How to Stop ThemWhat Is a Scam Likely Call and How to Stop ThemLearn what scam likely calls are, how to identify them, and ways to prevent potential scams. Take these steps to protect yourself and your data today.
- Read more about What Are Backdoor Attacks? Examples & How to Prevent ThemWhat Are Backdoor Attacks? Examples & How to Prevent ThemLearn how backdoor attacks work and how to protect your business with expert advice and Huntress Managed EDR solutions.
- Read more about What Are CIS Benchmarks in Security?What Are CIS Benchmarks in Security?Learn how CIS Benchmarks help reduce cybersecurity risks, improve compliance, and harden IT systems.
- Read more about What Is a CVE? Common Vulnerabilities & Exposures ExplainedWhat Is a CVE? Common Vulnerabilities & Exposures ExplainedLearn about CVE (Common Vulnerabilities and Exposures), a universal system for cataloging cybersecurity vulnerabilities, and why it’s essential to cybersecurity professionals.
- Read more about Keystroke LogginKeystroke LogginKeystroke logging records everything you type on your keyboard. Learn how it works, the risks it poses, and how to protect yourself from keyloggers.


Protect What Matters