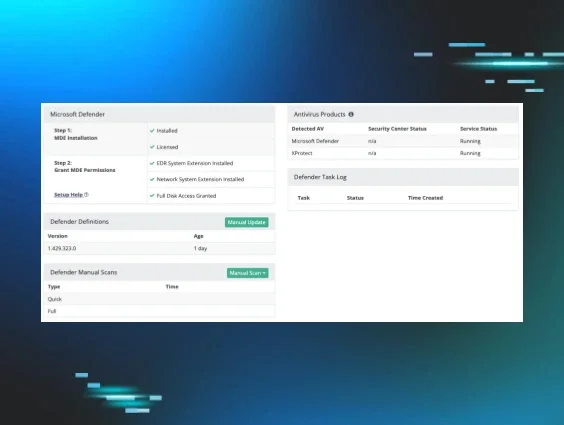
A few months ago, we announced three exciting new features of The Huntress Security Platform, including Managed Microsoft Defender, 24/7 Global SOC coverage and Host Isolation! 🥳
We’re thankful to have partners like Jeff Harlan, Manager of Network Services at United Systems, and Jennifer VanderWier, President of F1 Solutions, who are just as eager about our releases as we are.
In fact, they were so eager to give our Managed Microsoft Defender solution a try—even back in its days in beta—that they joined us for a webinar to share their experiences. 😎
Check out highlights from our conversation below to learn about their respective journeys with Huntress’ Managed Antivirus feature.
The Vetting Process
Can you tell us a bit about the history and evolution of your security stacks? How do you vet the tools in it, and how often do you re-evaluate?
Jeff Harlan from United Systems (Jeff): We plan our base offerings on those core compliance standards that the government sets forth and go from there. We rarely stop there, but those standards give us a good place to start with our stack evaluations.
Although a lot of folks live on the cloud now, we stress to our clients that we still need to be vigilant with the right tools on our own systems as well. One keylogger on the right computer can give threat actors all the access they need to break into your sensitive cloud data.
Jennifer VanderWier from F1 Solutions (Jennifer): Many of my colleagues hate having to talk about security stacks. There are just so many tools out there and it can be a pain to dive into them and talk about them—but it’s a necessary evil.
We decided to re-evaluate our stack to align to a standard—regardless of whether that standard was internal to us or an external one in the industry. That alignment helped us choose the tools, processes and procedures to put in place.
Our vetting process doesn’t stop with our security stacks. We’ve made it a habit to regularly vet our vendors, too. We ask about roadmaps, new features and their compliance standards. As an MSP, you’re obligated on behalf of your clients to regularly re-vet your vendors to ensure those partnerships still make sense.
Why Microsoft Defender?
Jeff: Microsoft Defender has definitely had its ups and downs, but it’s a solid solution as it stands now. We realized that Defender began catching the same—if not more—incidents than other AV solutions were catching. Because of that, it gained our full confidence.
From a financial perspective, the move made sense, too. It’s a solution we’re already paying for as Microsoft users. By taking advantage of a tool we were already paying for, we were able to help our bottom line without sacrificing the quality of service we provide to our customers.
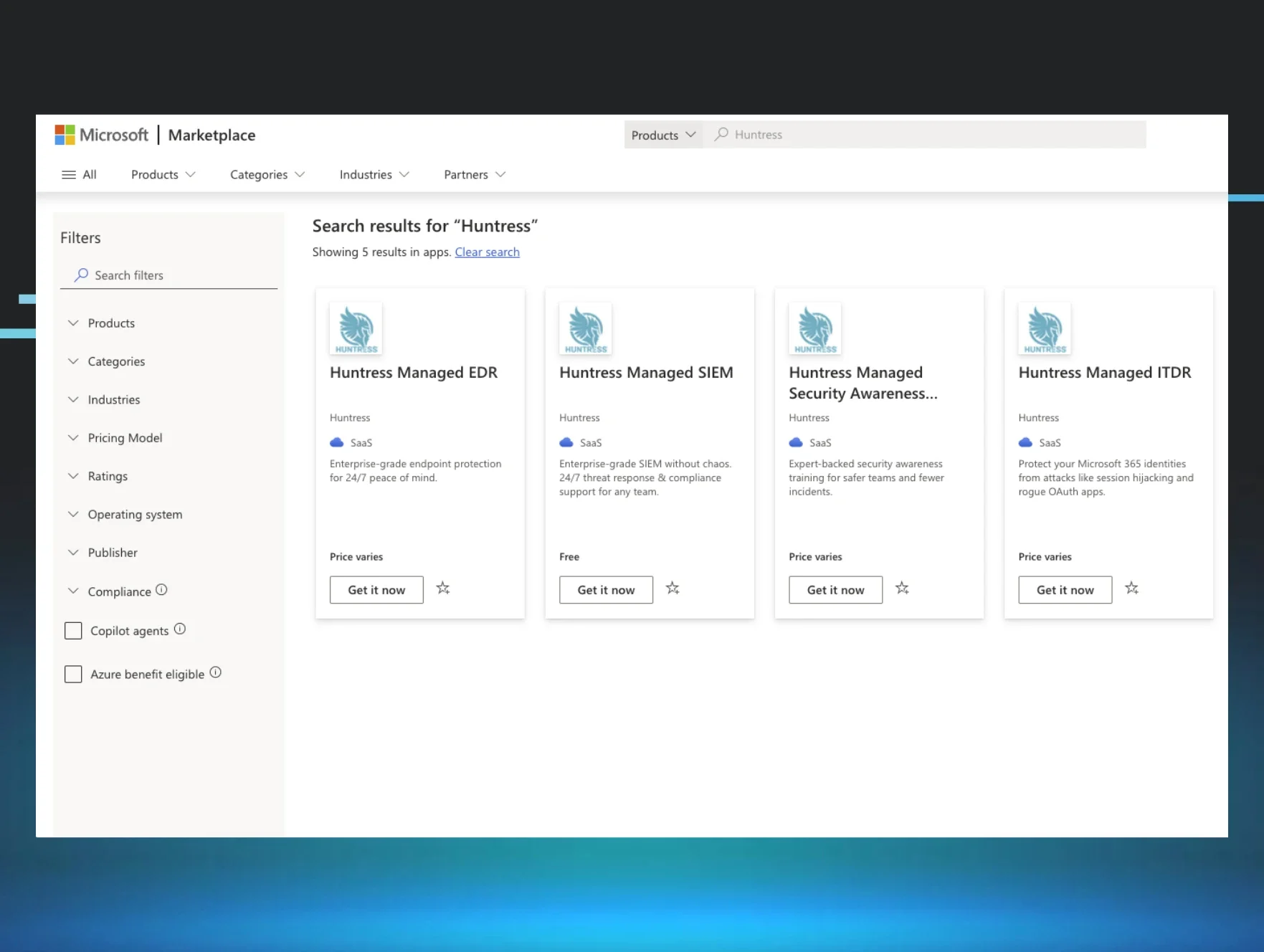
Jennifer: It was much the same thought process for us. I think, as MSPs, a lot of us get to a point where we ask ourselves, “Okay, how much of a relationship with Microsoft do we want?” We at F1 Solutions made the decision many years ago to be a Microsoft house. Once we saw the Huntress integration come in, it just clicked for us.
Check out AV Test to review independent rankings of top AV products for unbiased feedback on Windows Defender.
The Transition
Did your team make an abrupt move to Managed Microsoft Defender, or did you transition over time?
Jeff: We made the switch pretty immediately for all 1,100-1,200 of our endpoints. We’d done enough reading about Huntress’ Managed Microsoft Defender feature and improvements to Microsoft Defender that we were ready to take the plunge.
Jennifer: We’ve been with a different antivirus solution for many years, and it worked just fine. We never had any issues or episodes while using it. But we wanted to increase our security posture, so we shopped around.
We’d been seeing some of the publicity and reporting about Windows Defender being a top-notch solution, and when Huntress began managing it, that gave us more confidence in using it. The switch wasn’t something we chose to do lightly. The last time we switched RMM tools, it took us 800 hours to fully transition.
But we did our research and talked to other companies. At the end of the day, we asked ourselves, who’s gonna pick up the phone when I call? Who’s gonna pick up the phone and call me when the worst happens? Who’s gonna care about my business as much as I care about my business?
That piece was missing with many of the folks at other companies we’d talked to, and we felt we were getting a good level of protection across the board with Huntress. Within 10 working days, we had nearly all 5,000 of our endpoints secured with Huntress’ Managed Antivirus.
Communicating with Customers
Did you communicate the changes to your security offerings to your customers? If so, what did that look like?
Jeff: In our contracts with customers, we have a clause that states that we can change products at any time. Our customers usually don’t even know what we do—or want to know what we do—although we do explain our operations to them. We’re an all-in-one solution, which gives us the ability to make changes to stacks without having to do a lot of communicating with customers. It’s all part of striking that perfect balance between transparency and over-communicating.
Jennifer: We started by holding a three-hour conversation with our stakeholders. We checked with our peers. Our aha moment was the Kaseya supply chain attack that happened over the summer. Luckily, it didn’t impact us, but it did make us think about what else we could be doing. Are we doing everything possible for the quality of service we’re trying to deliver to our clients?
At that point, we decided to make Managed Antivirus a standard security offering for all our clients. We were a bit concerned at first about what our customers’ reactions would be, but ultimately, we ended up getting one single phone call about it. That customer wanted us to write up a policy statement so they could add it into their written policies—and that was for nearly 5,000 endpoints.
Results
And—drumroll please—how’s it going so far? Any interesting threats showing up? Is there any benefit to Managed Microsoft Defender than, say, the traditional Defender interface?
Spoiler alert: The remediate button is a crowd favorite.
Jeff: Definitely. Any time a threat is caught, it shows up on our Huntress dashboard, which is where we’re doing reviews of incidents anyway. A lot of our monitoring work happens right in that panel. If we ever have questions, we just pick up the phone and call Huntress or email them for help.
We’re avid users of the remediate button within the platform. We push the button, and incidents are automatically remediated. We once got an email about a machine that had a persistent foothold on it, and within a few seconds, our phone rang. Huntress was on the other end asking if we needed any help—on top of sending an email with the steps to remediate it.
Our antivirus at the time didn’t catch that threat, and even if it had caught it, there wouldn’t have been a “remediate this for me” button. With Huntress, we get enough information that helps us deal with events ourselves—even if that means hitting the “remediate this for me” button.
Jennifer: Absolutely. One incident off the top of my head relates to a client that’s a government contractor. Managed Microsoft Defender caught two potential landmines that we had no idea were present—and due to who the client was, we’d have had to report this incident to the government had it gone unnoticed. However, we were able to see the threat, immediately remediate it and prove that there was no exfiltration.
We pride ourselves on having incredibly clean systems. The US Missile Defense Agency did our audit two years ago, and clean systems make up a sense of pride that we have. But Managed Microsoft Defender caught things that we’d have never seen otherwise.
We also love the remediation button. Huntress catches things that other tools we have in place have missed. It truly feels like we have a partner in this.
Wrap-up
We’re grateful to United Systems and F1 Solutions for being early adopters of Managed Microsoft Defender and making this partner panel possible.
You can watch the full partner panel webinar on-demand to hear more from Jeff and Jennifer regarding their respective journeys with Managed Microsoft Defender.