All too often, I blindly 'Accept' Terms & Conditions without reading them. Guilty! Yes, it's come back to bite me before, but I can't be the only one who does this with some regularity.
As someone who spends the majority of their day on a computer, one "feature" that can accelerate a person's descent into madness is notifications, alerts, and prompts. Whether it's a Reminders alert that won't leave the top-right corner of the screen, or even the bright red, alarming badge icon showing me how many unread emails I have in my inbox, it is difficult to stay focused on one thing with everything else vying for its user's attention. With Apple's most recent operating system release, macOS Ventura, it also released some new transparency features, which does indeed involve yet more notifications. However, it is of paramount importance to note that these notifications, especially anything related to security, is a purposeful design by Apple.
Not only can the amount of Notifications a user receives be a bother, but it can lead to alert fatigue, which is when someone receives so many alerts, that they become desensitized to them. This can then lead to potentially missing/overlooking important and/or vital alerts.
In addition to an end user's alert fatigue, notifications can cause frustrations around deploying software, whether for the engineers developing it, the IT professional, the MSP attempting to deploy it to a handful of devices, or even at the MDM-level.
macOS Notification Mechanism
Notification Center
To the end user, Notifications that stem from the Notification Center are delivered by their respective process. For example, if you set a reminder within the Reminders application, the cfprefsd process, along with the remindd XPC event will work together to send the alarm sound to the user, as well as respond to any interaction the user has with the notification. This applies to other third-party applications that leverage the Notification Center, like Slack or Zoom.
Apple's own services, as well as developers that desire to tie into the Notification Center, leverage the Apple Push Notification service (APNs). Interestingly enough, one of the newer features that was released with macOS Ventura is insights into Launch/Login Items (Launch Daemons, Launch Agents). Since this is strictly a visibility notification, Apple sends these through the Notification Center, as opposed to the traditional security prompt.
These Launch/Login Item Notifications are designed to provide insight and transparency to the end user as to what persistence has been installed by which software. For more information on persistence, further reading is available in Insistence on Persistence.
All of these Notification Center notifications have the ability to be served quietly, using something like Do Not Disturb. This will keep the notification from being presented on the user's screen but will instead be silently delivered to the Notification Center. This can help tamper some of the chaos around the Notification Center.

In my opinion, it is important to find a balance for which you have the mental bandwidth. In this day of modern technology, a huge amount of tech and apps are designed to capture your attention and hold it as long as possible. This is something that even I've observed with *OS badge color (that little red dot with a number in it indicating the number of unread emails, overdue Reminders, unread iMessages, etc., etc.). For years, I've advocated for the ability to change the badge color. It has been documented that blue is a calmer color, whereas red (the only possible badge color) is designed to be alarming. Now this is fine for some applications, but overall, this just seems to heighten my own anxiety.

Security Prompts
As we pivot over to security prompts, they are generally served up from the CoreServicesUIAgent. It will give the users a little context around the prompt details, as well as a few actionable buttons that allows the user to take some form of action against it. These prompts extend to TCC, File Quarantine, Launch Items, and more.
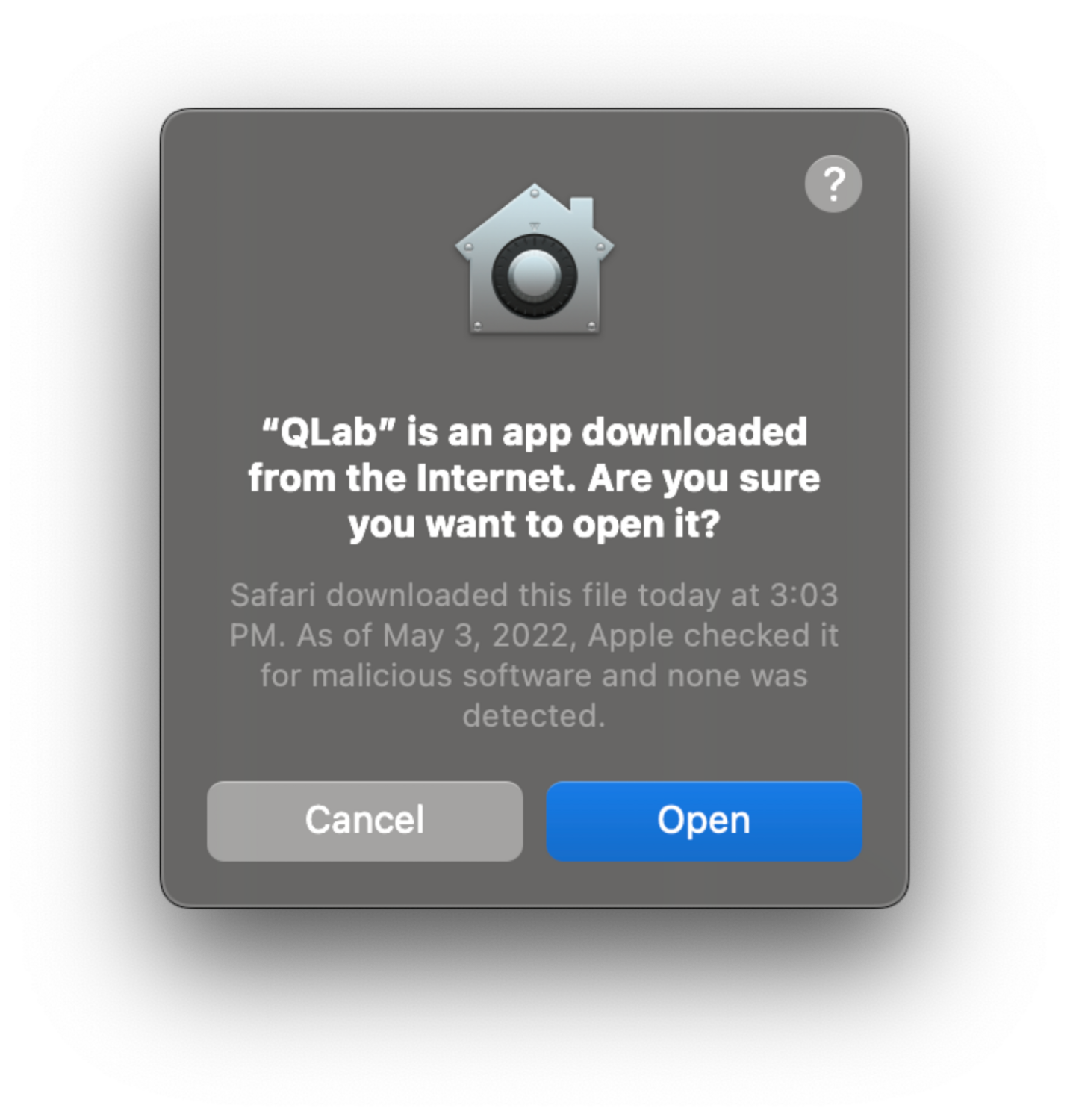
They contain typically around two or three actionable buttons and block any further activity within the application making the request until user action is taken. This type of prompt cannot be muted or ignored if you intend to use the application making the request.
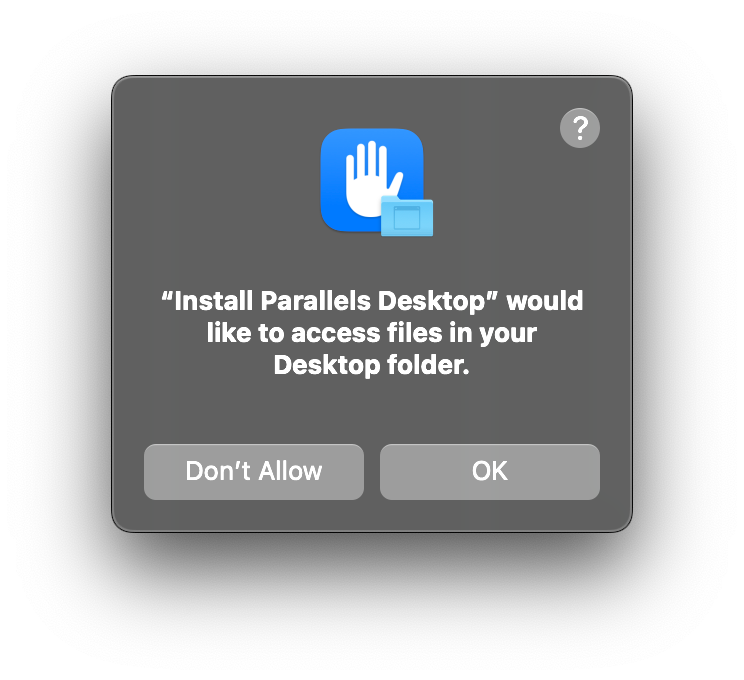
When a program attempts to access user-specific files, it will need additional permissions. This can extend to needing Full Disk Access (FDA) to perform certain operations. A huge difficulty around TCC is the inability to script any of this. Using an MDM - and therefore Apple Business Manager -, and in turn deploying a PPPC payload, makes this much easier. But if administrators either use an RMM (Remote Monitoring & Management software) or nothing at all, these prompts require interaction on the endpoint itself.
This is where difficulty deploying software tends to seep in.
Trials and Tribulation
Regardless of whether you're a seasoned security professional, an IT admin, or an accountant, the more alerts you see, the more likely you are to blindly click through them. Between the sheer volume of Notification Center alerts, plus the security prompts, you almost become desensitized to what the alert actually says, and you just click through it to go about your day.
The difficulty of alerts doesn't just apply to the end user's experience, but it extends to those developing software targeting macOS (or those deploying software). For example, if you are building a security tool, it is impossible to avoid prompts. As security tools typically leverage a system extension, or need TCC access, or if they deal in network events, each of those has its own set of security prompts that a user, or administrator, has to respond to in order for the software to work properly.
The struggles then extend to small or medium-sized businesses who maybe don't have an MDM to assist in software deployment. This can sometimes mean using an RMM to approve/deny security prompts, asking the user to click through the buttons for them, or having physical access to the machine to do it themselves. Unfortunately, due to Apple's design of protecting the end user, this cannot be automated beyond using a PPPC payload via an MDM. Although this can cause headaches, I can't stress enough that this is a purposeful design by Apple, attempting to give the user more knowledge around what programs have access to their personal information (files, location, screen sharing, etc.).
Let's walk through some of the different types of security prompts a user or admin may see when installing a new piece of software without an MDM.
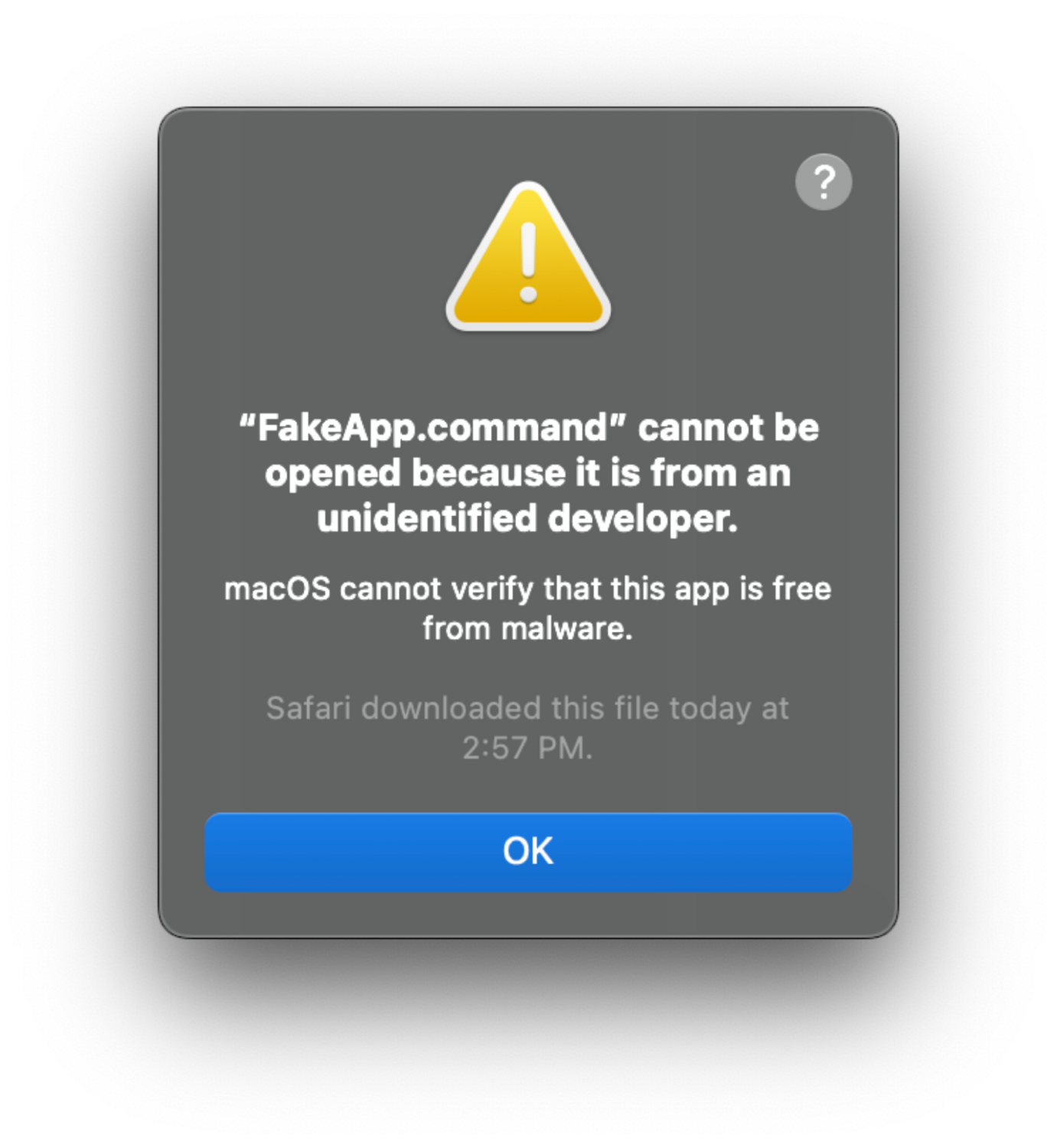
A prompt by Gatekeeper notifying end users that an application is blocked because the Developer ID could not be verified.
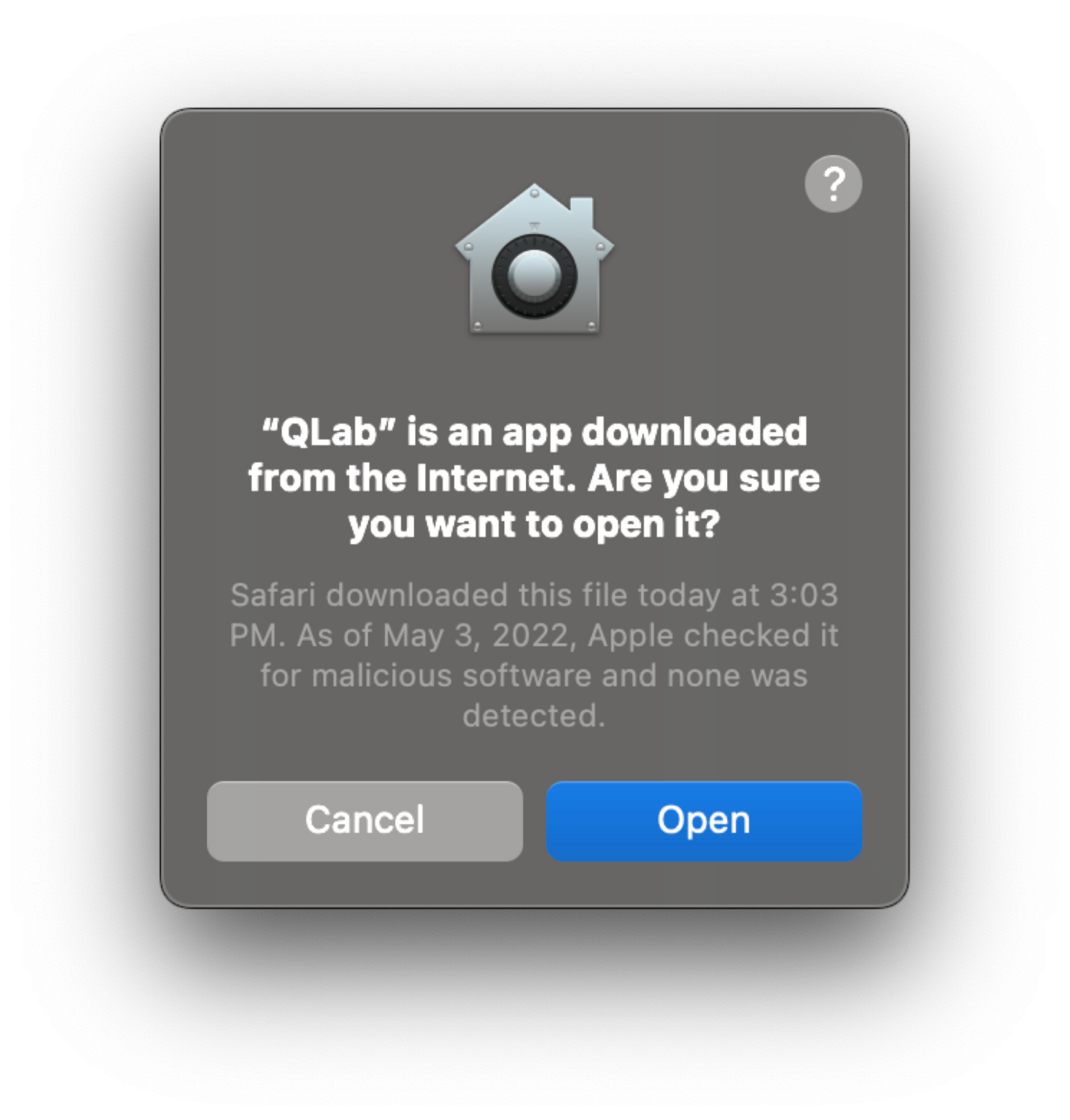
A prompt by File Quarantine advising you that your application was downloaded from the internet.
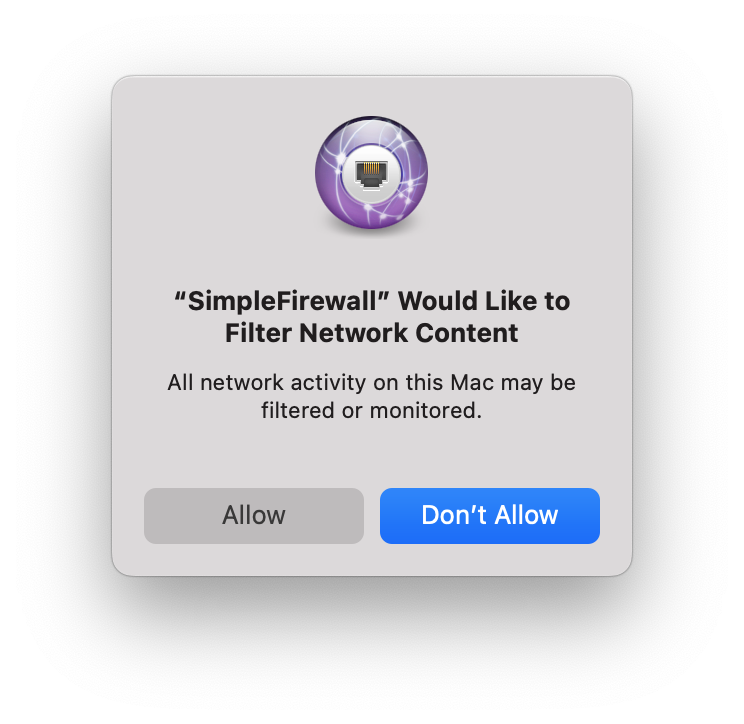
If the software you are using does any type of network filtering, the user can approve or deny the use of it on the endpoint.
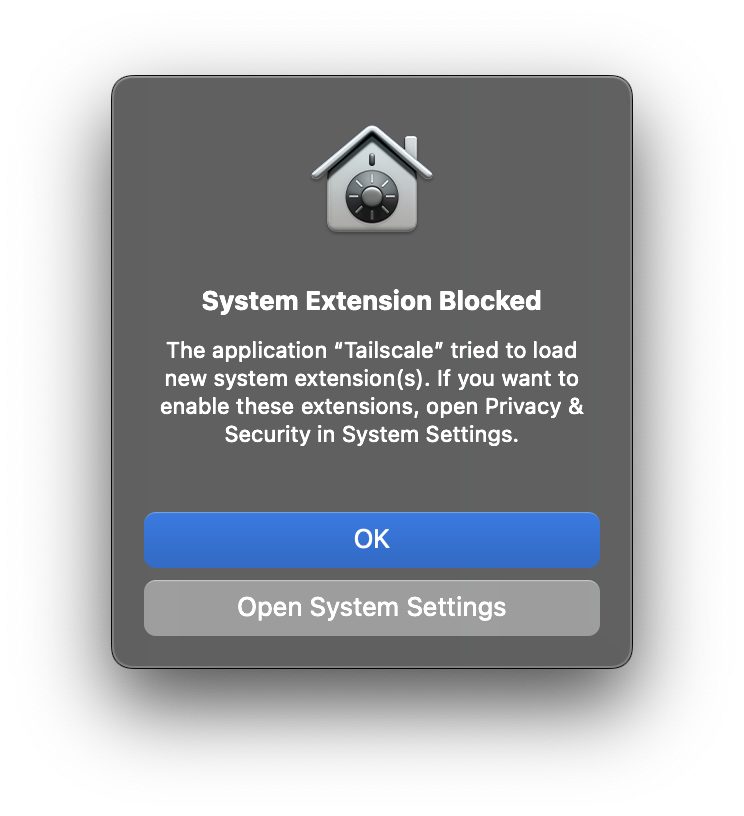
System Extensions must be approved from within the System Settings and cannot be approved directly from the security prompt.
Having an MDM can make life easier with the ability to pass down a PPPC profile that gives applications the proper permissions they need. This can extend to Login Items, using the new com.apple.servicemanagement payload.
Epilogue
Even if you're tired of hearing it, it is well worth mentioning one last time that this design by Apple is on purpose. Limiting notifications from the Notification Center are a great way to begin combating alert fatigue, or even leveraging features like Do Not Disturb. Unfortunately, as mentioned, the security prompts are here to stay. They are designed to give the end user insight into what is installed on their machine, and this is a great thing. It is important that users know what software is running, whether it’s nefarious or not, and not accessing any personal data it isn’t supposed to, however, this can be a headache for developers and administrators who are trying to deploy software to a number of devices that do not leverage an MDM.