Early in 2024, the United States healthcare sector was rocked by a devastating cyberattack on Change Healthcare, a pivotal player in health technology processes nationwide. The attack completely disrupted Change Healthcare's operations and sent shockwaves throughout the healthcare sector, impacting millions of Americans who rely on services powered by the affected providers—particularly pharmacies.
And it all stemmed from just one attack.
Months later, the repercussions still reverberate throughout the industry, highlighting the urgent need for robust cybersecurity measures in healthcare infrastructure. So, where do we go from here?
Key Takeaways
- The 2024 Change Healthcare ransomware attack disrupted pharmacy operations nationwide, cost providers over $100 million per day in losses, and ultimately resulted in nearly $2 billion in advances paid to affected healthcare organizations.
- Cyberattacks on healthcare organizations now affect nearly 6 in 10 providers, and the threat continues to grow more sophisticated and frequent into 2025.
- Pharmacies are uniquely vulnerable because they sit at the intersection of sensitive patient data, financial transactions, and critical prescription workflows — making them high-value targets for ransomware groups.
- Proactive defenses — including risk assessments, employee training, endpoint protection, and incident response planning — are the most effective tools pharmacies have to avoid becoming the next headline.
What Happened in the 2024 Pharmacy Cyberattack?
The Change Healthcare attack did not happen in isolation — it unfolded over weeks and months, with consequences that rippled across every corner of the healthcare system. Here is a breakdown of how events unfolded:
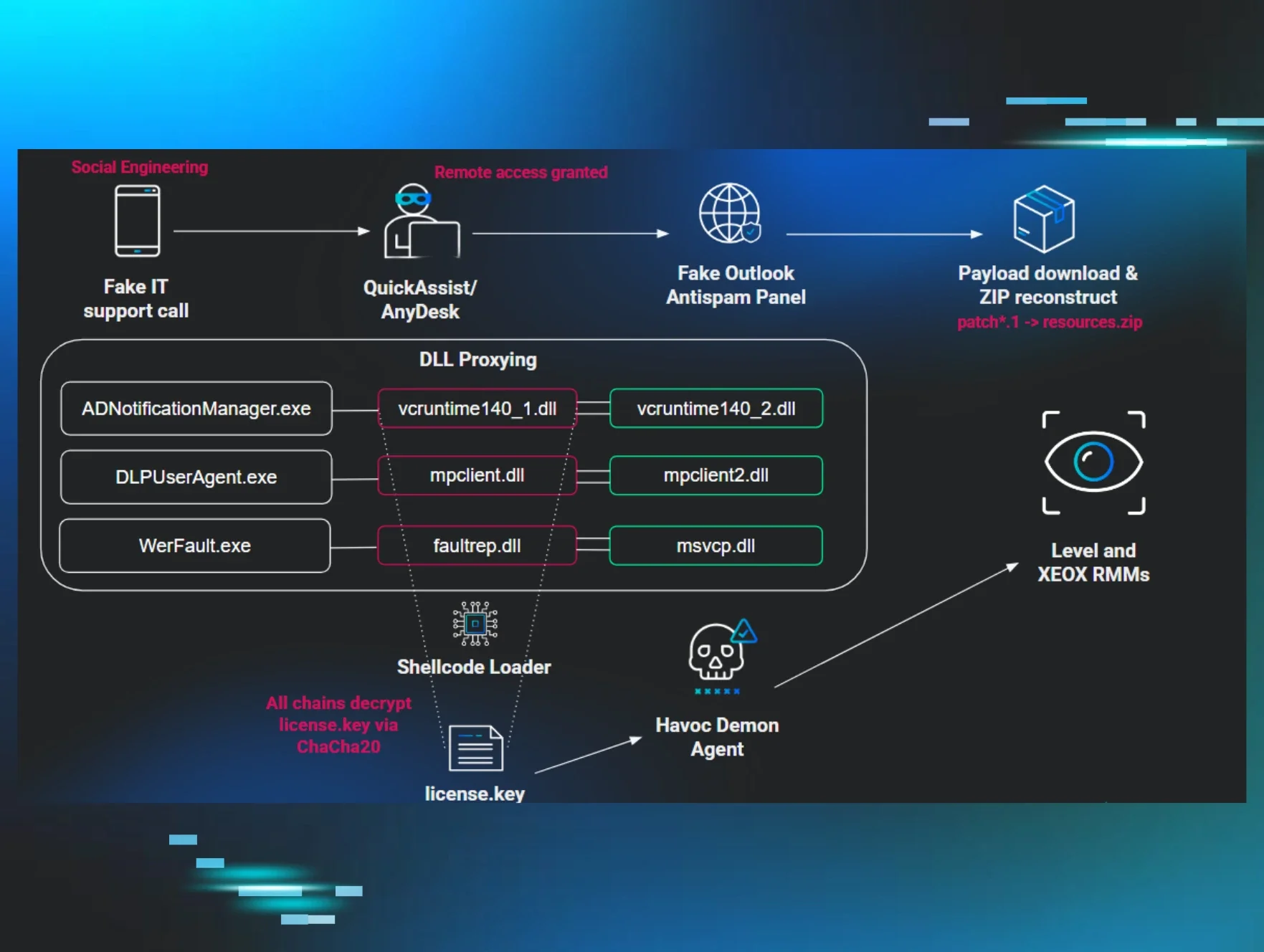
February 21, 2024 — The Attack Begins. Change Healthcare, the technology division of UnitedHealth Group responsible for healthcare billing and data systems, fell victim to a ransomware attack orchestrated by the cybercriminal group ALPHV/BlackCat. Upon discovery, UnitedHealth Group moved quickly: "Once we became aware of the outside threat, in the interest of protecting our partners and patients, we took immediate action to disconnect Change Healthcare's systems to prevent further impact."
February 22, 2024 — Pharmacy Operations Go Dark Despite the company's claims of a fast response, core functionalities — including electronic prescribing for pharmacy services — remained offline into the following day. For a company that handles approximately 15 billion transactions annually, this was just the beginning.
Late February into Early March 2024 — The Fallout Widens. The system outage blocked millions of patients from accessing vital prescriptions. Pharmacies across the country — from independent community pharmacies to major chains — could not process insurance claims or verify coverage in real time. Patients were turned away or forced to pay out of pocket for medications they depended on daily.
Mid-March 2024 — Financial Pressure Mounts. Even after systems were partially restored, many healthcare providers — especially smaller practices and independent pharmacies — continued facing challenges submitting claims and receiving payments. Giant companies like CVS Health reported ongoing issues with insurance claim processing weeks after the initial attack. Estimates suggested losses exceeding $100 million per day for healthcare providers as system problems persisted.
March 2024 — The Ransom Is Paid Reports confirmed that a ransom of approximately $22 million in Bitcoin was paid to the attackers. Despite the payment, the disruption continued, and a second ransomware group reportedly attempted to extort Change Healthcare with the same stolen data.
Through Mid-2024 — The Recovery Cost. By the time the dust settled, Change Healthcare had paid out nearly $2 billion in advances to help affected healthcare providers cover the financial gap caused by the outage — a staggering cost that does not even account for the ransom itself, legal exposure, or reputational damage. For a company serving 152 million customers, the attack was catastrophic. For the smaller healthcare entities that depended on Change Healthcare as their primary transaction and billing infrastructure, it was existential.
And it was all from just one single attack.
The Continued Fallout
As you might imagine, the system outage affected millions, temporarily blocking access to vital prescriptions. But even after systems were fully restored, many healthcare providers, especially smaller ones, continued to face challenges in submitting claims and receiving payments well into the middle of March. Even giant companies like CVS Health reported issues with processing insurance claims for weeks after the ransomware attack. Plus, the outage's financial toll was staggering, with some estimates suggesting losses of over $100 million per day for healthcare providers as the system issues persisted.
By the time it was all over, ChangeHealth had paid nearly $2 billion in advances to help affected healthcare providers—and that’s aside from the ransom amount that totaled roughly $22 million in Bitcoin. So, yes, for a company with 152 million customers, the ransomware attack was devastating. But it was also catastrophic for the huge number of healthcare entities relying on them for their main transactions and processes.
And, again, it was all from just one single attack.

The Response
It’s not a secret that cyber attacks on healthcare organizations skyrocketed during the onset of the COVID-19 pandemic. But even after the pandemic's peak, attacks have persisted and intensified, now affecting nearly 6 in 10 healthcare organizations. Cyber attacks have become more frequent and sophisticated, targeting sensitive patient data, disrupting critical healthcare services, and jeopardizing patient care.
The Change Healthcare cyberattack is yet another example, but the backlash has been much more urgent and far-reaching than previous notable attacks. The attack on Change Healthcare triggered strong responses from prominent figures like Senate Majority Leader Chuck Schumer and leading medical organizations such as the American Medical Association (AMA) and the American Hospital Association (AHA). Each issued urgent calls to action, emphasizing the breach's massive impact on physicians and healthcare delivery nationwide.
New Government Action
Unsurprisingly, ransomware attacks like the one on Change Healthcare have spurred the Department of Health and Human Services (HHS) to further intensify its evolving cybersecurity guidelines. These new directives stress proactive approaches like risk assessments, employee training, and more robust incident response plans.
HHS now requires faster reporting of ransomware incidents, imposing penalties for non-compliance. Penalties have become more of a focus for the department recently. In a notable case in late 2023, HHS settled its first HIPAA violation linked to ransomware with Doctors’ Management Services. This Massachusetts-based medical management firm faced a $100,000 fine for insufficient security measures and failure to comply with HIPAA regulations. And while that’s definitely a hefty fine, expect it to be small compared to future punishments—HHS has vowed to bolster penalties and enforcement efforts, signaling stricter consequences for compliance violations stemming from ransomware attacks.
How to Protect Your Pharmacy from Cyberattacks
Pharmacies occupy a uniquely vulnerable position in the healthcare ecosystem. They manage sensitive patient health data, process high volumes of financial transactions, and rely on interconnected systems — from pharmacy management software to insurance billing platforms — that create multiple potential entry points for attackers.
Here is what pharmacies can do right now to reduce their exposure:
1. Conduct Regular Risk Assessments
You cannot defend what you do not understand. A thorough risk assessment identifies your most vulnerable systems, surfaces gaps in your security posture, and helps you prioritize where to invest your defenses. This is not a one-time exercise — it should be conducted at least annually and after any significant change to your technology environment.
2. Train Your Staff — Consistently
Human error remains one of the leading causes of successful cyberattacks. Phishing emails, social engineering, and credential theft all rely on someone in your organization making a mistake. Regular, role-specific cybersecurity training helps your team recognize threats before they become incidents. Make security awareness training part of your culture, not just an annual checkbox.
3. Implement Multi-Factor Authentication (MFA) Everywhere
The Change Healthcare attack reportedly gained initial access through stolen credentials in the absence of MFA. Implementing MFA across all systems — including remote access tools, email, and pharmacy management platforms — is one of the most effective and low-cost defensive steps available. There is very little justification for not having it in place.
4. Invest in Endpoint Detection and Response (EDR)
Pharmacies typically run a mix of older and newer devices, many of which may not receive consistent security updates. Endpoint detection and response tools monitor devices in real time, flagging suspicious activity before it can spread. This is especially critical for pharmacies using legacy systems that may not receive regular patches from vendors.
5. Have an Incident Response Plan — and Test It
When an attack happens, the first 30 minutes matter enormously. Organizations that have a practiced, documented incident response plan contain damage faster and recover more quickly than those that are figuring it out in real time. Your plan should define who gets called, what systems get isolated, how you communicate with patients and staff, and how you engage outside cybersecurity expertise.
6. Understand Your Third-Party Risk
Change Healthcare was a third-party vendor. So was UNFI. Your pharmacy's security is only as strong as the weakest link in your vendor ecosystem. Know what third-party platforms you rely on, what data they access, and what their security posture looks like. Ask vendors about their incident response capabilities and ensure contracts address data security responsibilities clearly.
7. Back Up Your Data — and Keep Backups Offline
Ransomware works by encrypting your data and demanding payment to restore access. Organizations with clean, recent, offline backups have far more leverage in a ransomware situation — they can restore operations without paying the ransom. Test your backups regularly to ensure they are actually recoverable when you need them.
8. Stay Current on Compliance Requirements
HHS is actively strengthening HIPAA enforcement related to ransomware and cybersecurity incidents. Staying ahead of compliance requirements is not just about avoiding fines — it is about building the security foundation that actually protects your patients and your business.
Now What?
The cyber attack on Change Healthcare was not the first of 2024, and it definitely won’t be the last. In late April, Canadian pharmacy chain London Drugs was forced to close all 79 locations as a precaution after what they described as a “cybersecurity incident.” Despite the shutdown, the chain assured customers and employees there was no evidence of any compromise to their data. According to a statement, the company “undertook countermeasures to protect its network and data, including retaining leading third-party cybersecurity experts to assist with containment, remediation and to conduct a forensic investigation.” London Drugs’ prompt and proactive response likely averted what could’ve been a much different outcome.
The ransomware attack on Change Healthcare and others in the healthcare sector serves as a wake-up call to the pressing need for improved cybersecurity within the healthcare industry. After all, at this point, cybersecurity isn’t just a technological issue; it’s a matter of your health and safety. It's crucial that healthcare organizations prioritize and invest in cybersecurity defenses to safeguard patient data and critical systems. This includes implementing comprehensive risk management strategies, regular security assessments, and employee training programs to enhance security awareness.
Find out how the Huntress Security Platform can help safeguard patient data, protect critical infrastructure, and ensure the integrity of the healthcare system in the midst of constant threats.
Request a free demo to see for yourself.