In a world of many noisy tools, Huntress has always been mindful of how real people are fighting against cyberattacks every day. Our goal is to make life easier for you (and harder for hackers). So to do that, we’re excited to kick off this new year with a new UI for the Huntress platform!
To empower your workflows, we knew we needed to bring things together into a single pane of glass. So how did we decide on what updates were needed? We performed user research at every level—CEOs, admins, SOC analysts, MSPs, security engineers, solution architects, and the techs who are “down in the trenches” doing this work day in and day out. We wanted to know what really mattered to each of you and how we could make the Huntress platform work better for everyone. And you answered.
Know What Your SOC Is Doing
A common question we get is, “What has Huntress done for me lately?” so we wanted to show you all the work that Huntress does behind the scenes. While other tools prove their worth with lots of noise, leaving you to sort out the mess, we do the heavy lifting for you.
The Security Operations Center Actions is a new part of the platform homepage that shows you the massive amount of events that we comb through to find the signals that need to be investigated, and then from that smaller pile, the short list of reported incidents you actually need to worry about.
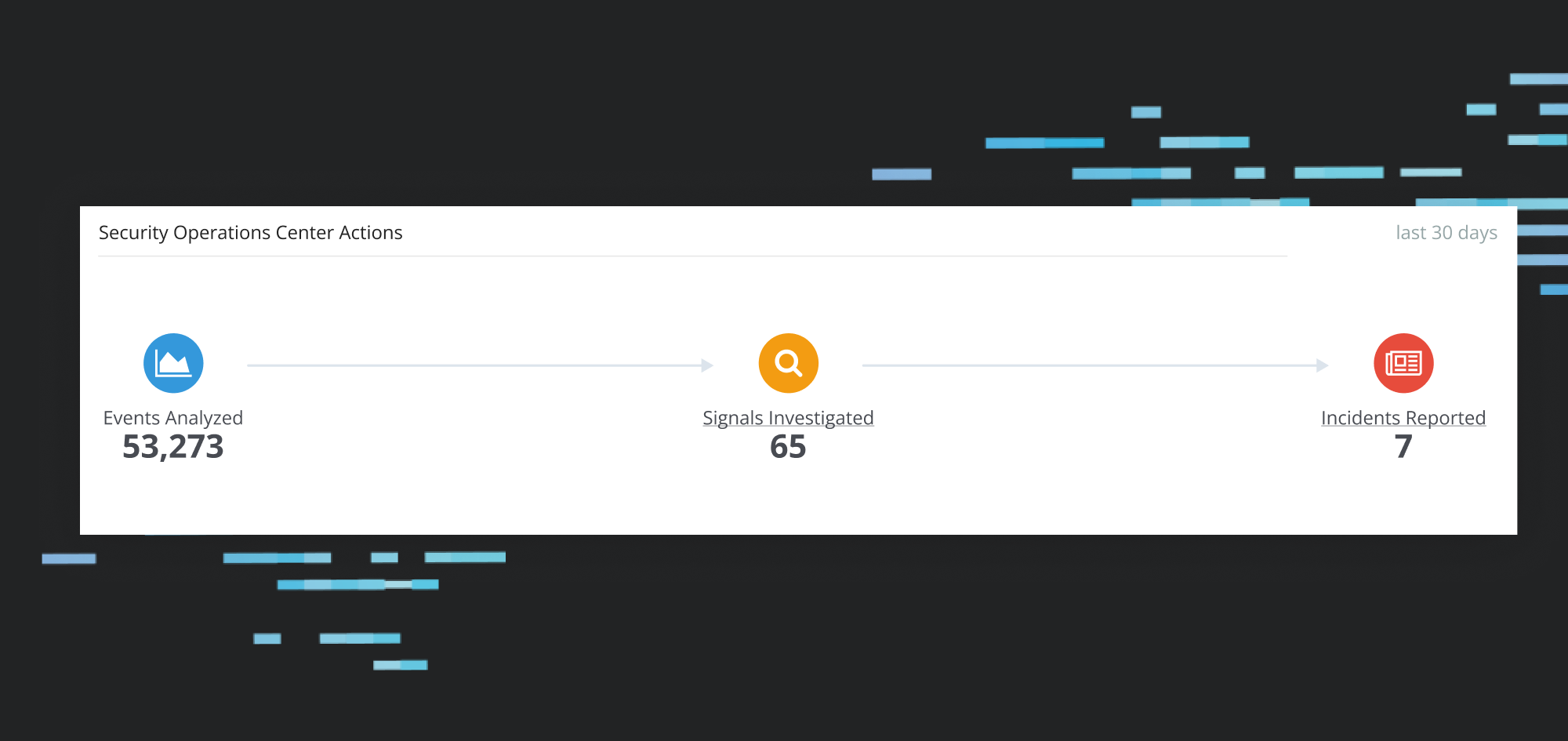
So what is a Signal anyway? Among all the events happening within a network, SOC analysts find some events more interesting than others. Alone, these events are not a security threat, and most of them do not require investigation. However, when these events happen in context with other suspicious behaviors, they do need more investigation. The Huntress SOC goes through thousands of these signals each month to find the reportable ones.
In the past, because we only highlighted reported incidents and autorun-specific investigations, it was hard to tell that Huntress was hard at work for all the data sources that we monitor. Now you can see we’re on the job around the clock, because we want you to sleep better at night.
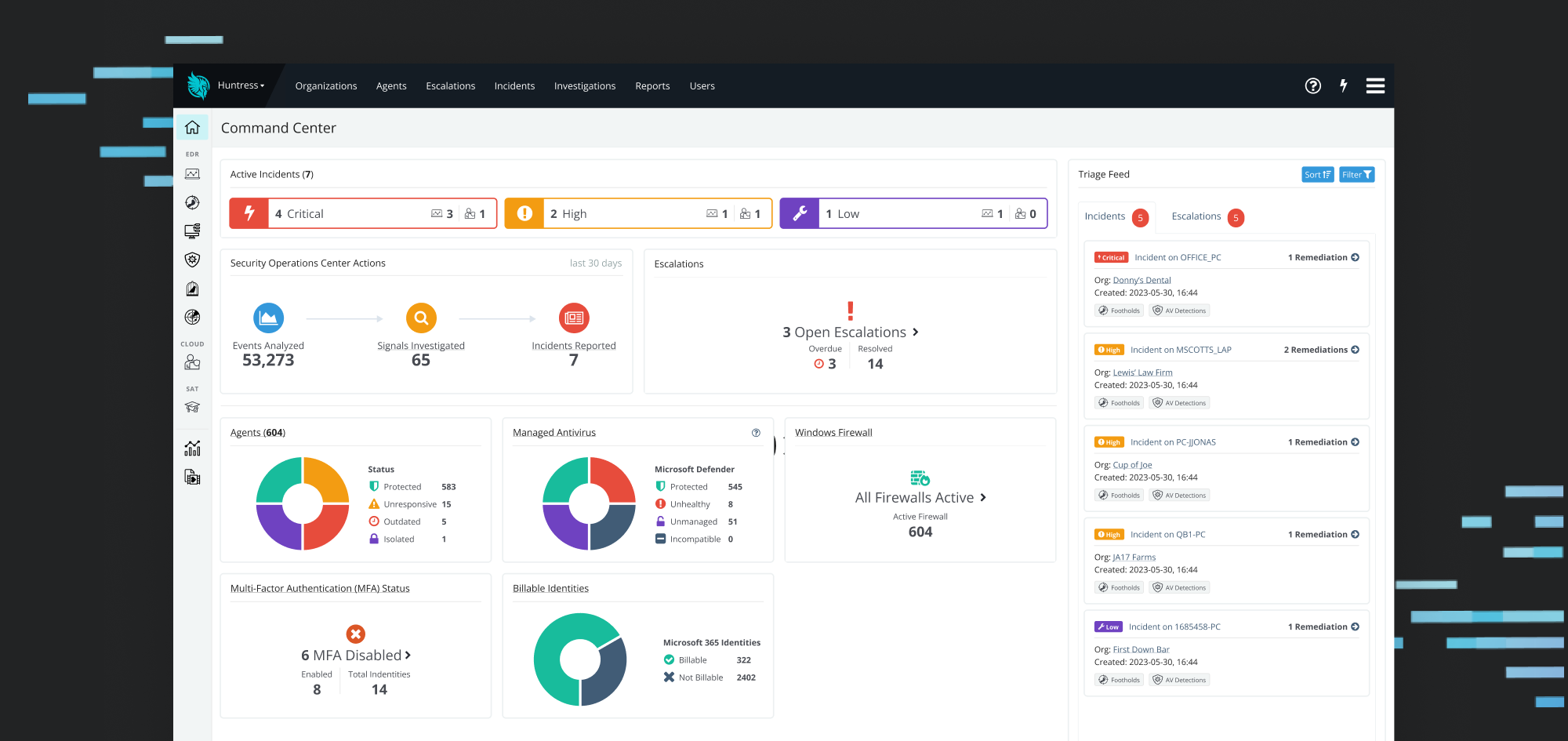
All Your Products, One Place
The platform homepage in the past was all EDR all the time, but that doesn’t reflect the services and security insights that we offer you. This new section accounts for all of the subscriptions you have and the things you’ve told us are most important to you about each of these products.

Managed EDR is the product you’ve come to know and love, now we’re adding even more goodness. The new Command Center still highlights the status of your Huntress Agents at a glance, but now, it also lets you get to what matters faster. You can see the status of the Managed Antivirus of Microsoft Defender and Windows Firewall for all of those agents.
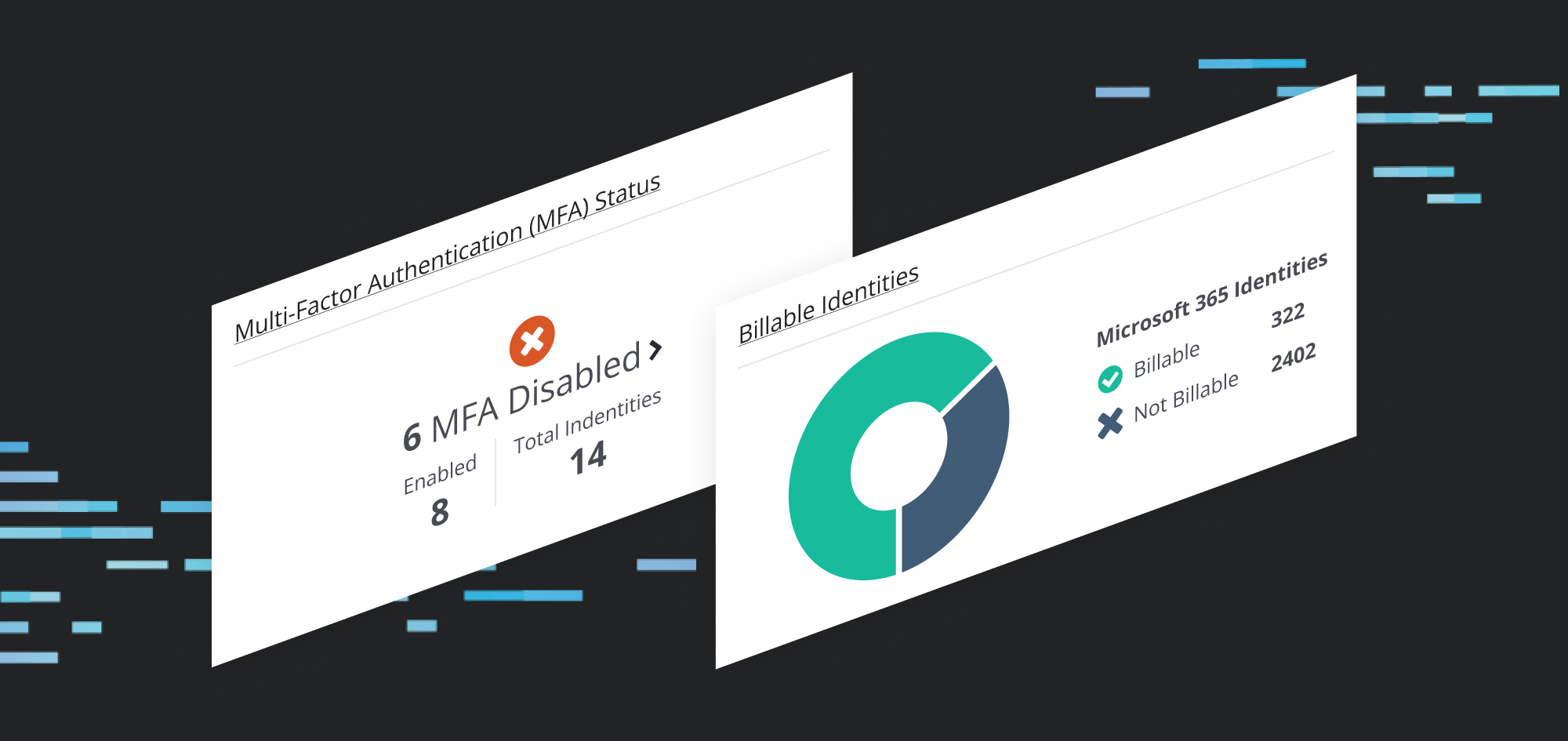
Managing identity security in the cloud is something we know many organizations are struggling with—it can feel like you can’t get your arms around the problem. You’ve told us that the main issue is that you need to know their MFA status, now it’s easy to see who has MFA turned on and who doesn’t. As a parallel to the EDR agent counter, the Billable Users shows you the scope of your coverage, upfront and center. Stay tuned for more changes to this set of data—as this offering matures, we’ll have even more new things for you.
Simplified To-Do List With the Triage Feed, Including Escalations
Remember that shortlist of things you need to take action on? We used to have the incidents as a count that you’d have to click through to find out any details, beyond the severity. If there were any escalations, they were buried several clicks deep. Well, we’ve fixed that.
Now, both of these important lists are available, as the Triage Feed, from the Command Center, putting your to-do list right at your fingertips.
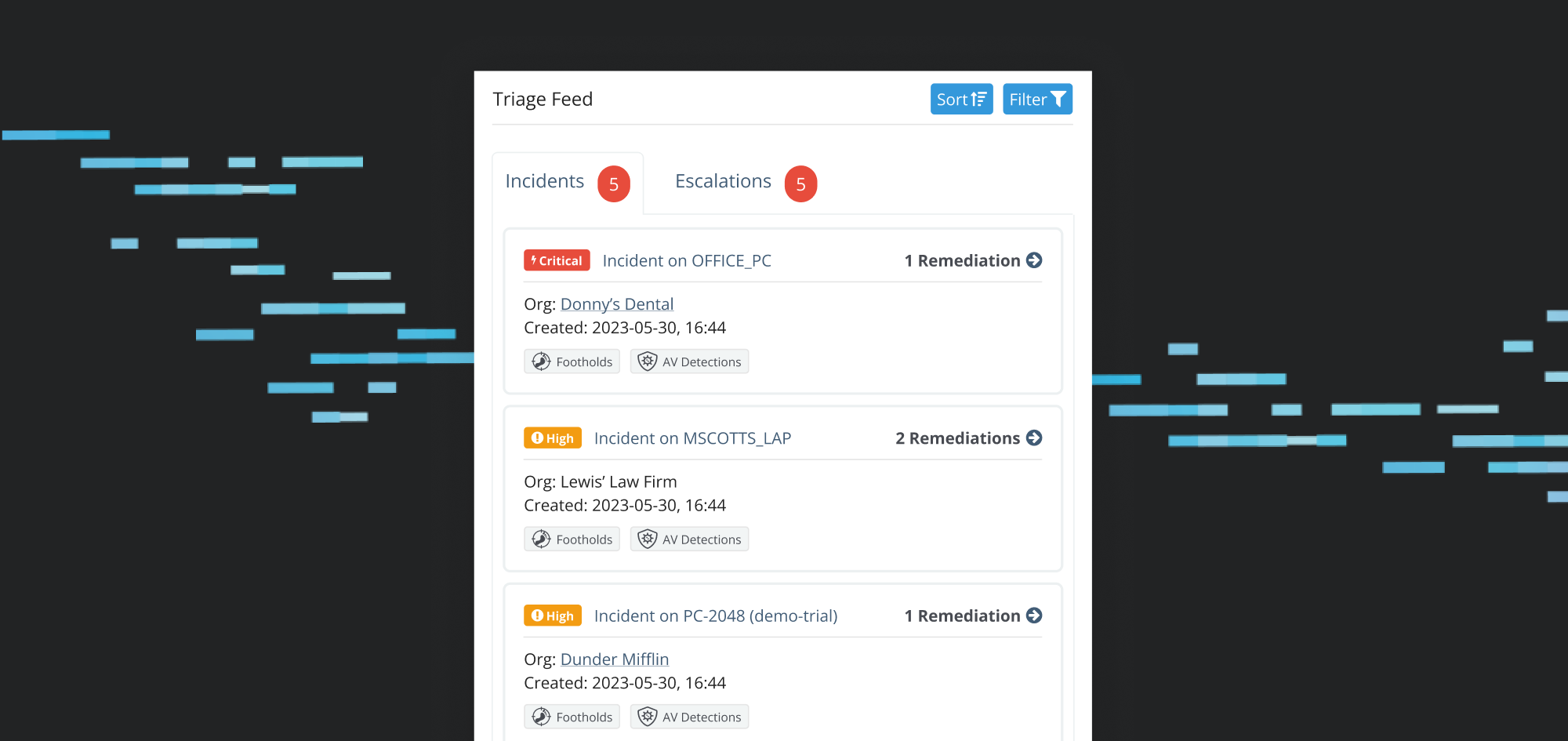
The Incidents tab shows you much more than severity—you can see the most important details and click through to the recommended remediations. And the Escalations tab makes those not-an-incident-but-still-important actions easy to find and check off.

If you’re a zero-inbox hero, you’ll find clearing your Triage Feed oh so satisfying.
The End, but Not Really
Huntress has always strived to build products that deliver the most value and put it into your hands as soon as possible. This shiny, new Command Center gives insights into the SOC, simplifies incident triage, and shows important metrics at a glance.
Thank you to all our partners and users who took the time to help guide this latest evolution of the Huntress platform. We couldn’t have done it without you.
But… our work is never done. Hackers don’t rest and neither do we. If you want to be a part of the next big thing and influence where we’re going, hit us up if you’d like to be contacted for future UX research.





















