What Is a Golden Ticket Attack?



FAQs about golden ticket attacks in Kerberos Authentication
A golden ticket is basically a hacker’s all-access pass to your Active Directory environment. It’s a forged Kerberos Ticket Granting Ticket (TGT), created using the krbtgt account hash (yep, the one that signs all the tickets in your domain). With this, attackers can impersonate anyone in the domain, including domain admins, and get unrestricted, long-lasting access to your network.
Here’s the gist of it:
First, the attacker grabs Domain Admin privileges or the krbtgt NTLM hash.
Then, they use a tool like Mimikatz to whip up a fake TGT.
Once created, they authenticate to any service in the domain using the forged ticket.
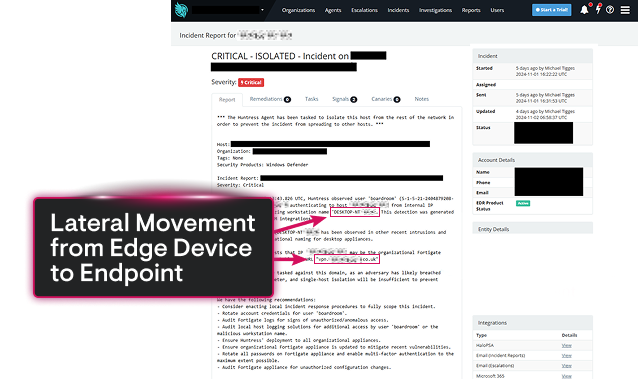
What makes this attack so sneaky? It skips over traditional login processes, making it tough to detect. Plus, attackers can customize these tickets with fake usernames or super extended lifespans for stealthy, ongoing access.
The krbtgt account is the MVP of Kerberos authentication. This built-in service account in Active Directory is used by the Key Distribution Center (KDC) to sign and encrypt TGTs. Here’s why it’s a big deal:
If attackers crack the krbtgt hash, they can sign their own TGTs, effectively becoming anyone in the domain.
To keep it safe, you’ve got to guard this credential like your IT life depends on it (because it kind of does).
Golden ticket attacks are the ninjas of the cyberattack world, but you can still catch them with the right moves. Detection methods include:
Checking for Kerberos TGTs that don’t have a matching AS-REQ (those should set off alarms).
Watching for ticket lifetimes that look off, or usernames that don’t actually exist.
Monitoring log activity for unusual patterns across Event IDs 4768, 4769, 4770, and 4771.
Using tools like Splunk, Microsoft Sentinel, or Defender for Identity to analyze behavior.
Getting alerts when privileged activity pops up on suspicious devices.
The go-to tool for golden ticket attacks? Mimikatz. This post-exploitation favorite can snatch hashes and craft fake tickets like a pro. Other heavy-hitters include:
Impacket
Rubeus
Empire
Attackers and red teamers alike use these tools to forge tickets and simulate real-world attacks.
Here’s how to take the golden ticket out of attackers’ hands:
Rotate your krbtgt account password regularly (and do it twice in a row to be extra safe).
Cut down on Domain Admin privileges and switch to a tiered administration model.
Activate protections like Credential Guard, LSASS protection, and disable WDigest.
Keep a close eye on unauthorized access attempts to domain controllers and LSASS memory.
Train your blue team to detect Kerberos persistence tricks.
Set up detection rules in SIEM and perform regular privileged access audits.
Want to keep golden ticket attackers out? Start implementing these changes now and stay one step ahead of the game.