Detection Engineering —the art and science of smashing threats
Written by: Lizzie Danielson
Published: 10/3/2025



Detection engineering is the process of designing, building, and refining custom ways to spot cyber threats in real time. Instead of relying only on what vendors provide, it means rolling up your sleeves to craft and maintain security rules that actually fit your environment.
Detection engineering sits at the heart of modern cybersecurity operations. If your mission is to find threats before they explode into breaches, you need a program that moves beyond off-the-shelf alerts. Instead, you build, tune, and automate tailored detection logic that calls out what matters in your unique environment. This is where art meets science in digital defense.
In this guide, we’ll break down what it means, how it works in real companies, the role of frameworks, tools, and automation, plus tips for getting started or advancing your skills. Whether you’re prepping for a certification, onboarding a new SOC analyst, or charting a strategy from the CISO’s chair, this is your launchpad to understanding detection engineering’s value.
What is detection engineering?
Detection engineering is the practice of systematically developing, deploying, testing, and maintaining high-fidelity threat detection rules and content for security systems like Security Information and Event Management (SIEM), Endpoint Detection and Response (EDR), and Extended Detection and Response (XDR). Unlike plug-and-play solutions, detection engineering focuses on customizing detection capabilities to your organization’s unique infrastructure, risks, and threat landscape.
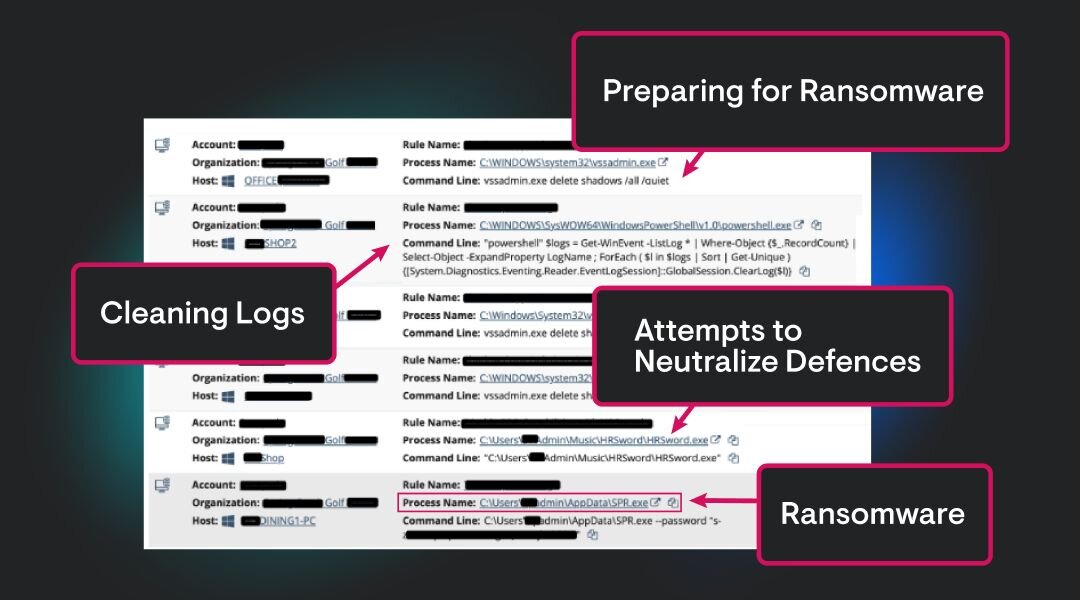
Why does detection engineering matter? Most out-of-the-box rules can’t catch everything. Attackers move fast, adapt their tactics, and know how to slip past vanilla alerts. Security detection engineering closes these gaps with targeted, context-aware rules grounded in your organization’s data, assets, and priorities.
Simply, detection engineering is about making sure your security tools tell you when something actually bad is happening, not just when any random event triggers a generic alarm.
“Detection engineering is the brain behind every effective detection and response system,” said Sasha Roshan, Sales Engineer II at Huntress. “In today’s threat landscape, detection engineering is more than just a technical function - it’s the foundation of effective cybersecurity. It’s what allows us to turn massive volumes of data into meaningful alerts, ensuring that real threats are identified before damage occurs. Too often, I have seen teams struggle with alert fatigue or gaps in coverage, which is why well-designed detection rules and continuous tuning are critical. Detection engineering isn’t just about responding to attacks; it’s about anticipating them, understanding attacker behaviour, and building resilience into every layer of your security stack.”
Detection engineering process and lifecycle
Crafting a solid defense isn’t one-and-done. The detection engineering lifecycle is iterative and collaborative, usually following these core stages:
1. Threat modeling
Work with your team to identify likely threats to your environment. Lean on frameworks like MITRE ATT&CK to map common adversary behaviors relevant to your organization.
2. Rule development
Write detection logic that targets those threats, customizing queries and scripts for your specific SIEM, EDR, or XDR platform.
3. Testing
Test new and updated detection rules in a controlled setting (ex. purple teaming). This avoids alert floods and verifies that rules work as intended without raising unnecessary noise.
4. Deployment
Roll out your detection content to production systems, ensuring proper version control and documentation for easy updates later.
5. Tuning and maintenance
Continuously monitor and tune rules to minimize false positives, cover new threats, and adapt to changes in your IT environment.
This iterative cycle is called the detection engineering lifecycle. It ensures quality, relevance, and effectiveness across every detection deployed.
Detection engineering vs threat hunting
Detection engineering focuses on creating and improving rules that spot known and emerging threats, while threat hunting is a more manual, proactive search for suspicious activity without waiting for an alert.
Both are vital, but detection engineering helps your defenders operate at scale. Successful threat hunts should yield detections, so detection engineering and threat hunting are in a feedback loop with one another.
Best practices for detection rule development
Use frameworks like MITRE ATT&CK to focus on attacker behaviors, not just technical signatures
Start simple, then iterate: Don’t aim for perfection on day one
Document everything: Easy-to-follow notes help future analysts maintain and update detections
Collaborate: Work cross-functionally with IT, data engineering, incident response, and threat intelligence
Automate where possible: Use scripting/automation to deploy, test, and version rules
Measure outcomes: Track metrics (see below) to know what’s working
Common challenges
Welcome to the “real talk” section! Detection engineering isn’t all glory. Here’s what often trips up new (and seasoned) teams:
Data access headaches: Can’t build great detections without the right logs or telemetry.
High false positive rates: Noisy rules slow down response and frustrate analysts.
Skills and resource shortages: DE expertise isn’t easy to find or develop quickly.
Tool fragmentation: Juggling rules across different SIEM and EDR systems eats up time.
Keeping up with evolving threats: The bad guys don’t sleep.
Solving these challenges is at the heart of modern detection content management.
Automation in detection engineering
Manual rule-building doesn’t scale. Automation in detection engineering reduces repetitive work, speeds up detection deployments, and helps manage massive detection libraries.
Examples include:
Automated rule deployment and testing (using CI/CD pipelines)
Alert triage and prioritization with SOAR and AI-based tools
Routine data enrichment, normalization, and tuning recommendations
AI is supercharging this trend, helping detection teams do more with less.
Measuring detection engineering impact
You can’t improve what you don’t measure. Detection engineering teams track several key metrics, including:
False positive rate: Fewer false alarms = more efficient teams
Detection coverage: Percentage of major threats you can actually spot, often mapped to frameworks like MITRE ATT&CK
Detection speed: How quickly can you deploy new rules for emerging threats
Reduction in incident response time: Do great detections help shut down breaches faster?
Detection backlog: Unbuilt or untested detections waiting in the queue
Share these numbers with leadership to prove ROI and secure that next round of investment.
Detection engineering is here to stay
Detection engineering remains a critical discipline in modern cybersecurity, addressing challenges like managing false positives and adapting to evolving attacker tactics. By leveraging these tools and staying informed, cybersecurity teams can enhance their detection capabilities and stay ahead of threats. In summary;
Detection engineering combines creativity with repeatable processes to build custom, high-impact cyber defenses.
It goes beyond default rule sets. You need targeted detection rule development, automation, and cross-team ops to keep up with modern threats.
Skilled detection engineers are essential for threat coverage, compliance, and minimizing alert fatigue.
Automation and AI are revolutionizing the detection engineering process, making detection teams more efficient and scalable.
If you’re looking to level up your cybersecurity career or capability, start exploring detection engineering frameworks, hands-on labs, and courses now.
Stay curious, keep iterating, and be the human that proves the best security isn’t out of a box.
FAQs about detection engineering
Detection engineering in cybersecurity is the process of designing, building, and improving custom detection logic to spot threats and malicious activity. This approach ensures your defenses are tuned to your unique environment and current attack trends.
Threat hunting is a proactive investigation (often manual) to find hidden threats, often before they trigger alerts. Detection engineering builds those alerts and rules that continuously scan for suspicious activity.
The toughest challenges are gaining access to quality data, managing false positives, scaling custom rule development, handling tool sprawl, and staying updated with new attacker tactics.
Look for resources from SANS Institute, MITRE ATT&CK, and CISA (cybersecurity training portal). Many industry blogs and glossary pages offer beginner-friendly tutorials too.



Additional Resources
- Read more about What Is a Purple Team in CybersecurityExplore the role of purple teams in cybersecurity. Learn how they bridge red and blue team functions to enhance threat detection and improve SOC operations.
- Read more about Threat Intelligence Feeds Explained: Stay Ahead of Emerging Cyber ThreatsThreat Intelligence Feeds Explained: Stay Ahead of Emerging Cyber ThreatsThreat intelligence feeds keep your security team one step ahead. Find out how real-time threat data powers faster detection, smarter response, and stronger defenses against modern cyberattacks.
- Read more about What Are TTPs? Cybersecurity Tactics ExplainedWhat Are TTPs? Cybersecurity Tactics ExplainedLearn about TTPs (Tactics, Techniques, and Procedures) in cybersecurity. Understand their role in threat detection and defense strategies.
- Read more about Built-in Tools in CybersecurityBuilt-in Tools in CybersecurityLearn what built-in tools are and how to leverage pre-installed security utilities for effective threat detection and system protection.
- Read more about Symmetric Encryption Algorithms Explained for Cybersecurity ProsSymmetric Encryption Algorithms Explained for Cybersecurity ProsLearn how symmetric encryption algorithms work, why they matter for cybersecurity, and the best practices for key management. Expert, clear, and up-to-date.
- Read more about Managed Detection and Response (MDR) ExplainedManaged Detection and Response (MDR) ExplainedWhat is Managed Detection and Response (MDR)? It's 24/7 cybersecurity that combines technology & human expertise for threat hunting & rapid response. Learn more here!
- Read more about What is an Intrusion Detection System(IDS)?What is an Intrusion Detection System(IDS)?Learn what an Intrusion Detection System (IDS) is, how it works, and why it’s key for cybersecurity. Discover tips to protect your business. | Huntress
- Read more about What Is AI in Cybersecurity? Impact & Use CasesWhat Is AI in Cybersecurity? Impact & Use CasesLearn how artificial intelligence is transforming cybersecurity. Learn AI applications, benefits, risks, and best practices for cyber defense.
- Read more about What is NIST? Understanding Its Role in CybersecurityWhat is NIST? Understanding Its Role in CybersecurityLearn how NIST drives cybersecurity innovation, from global standards to risk management frameworks, and how it strengthens enterprises worldwide.


Protect What Matters