What is a Clickfake Interview?



FAQs About Clickfake Interviews
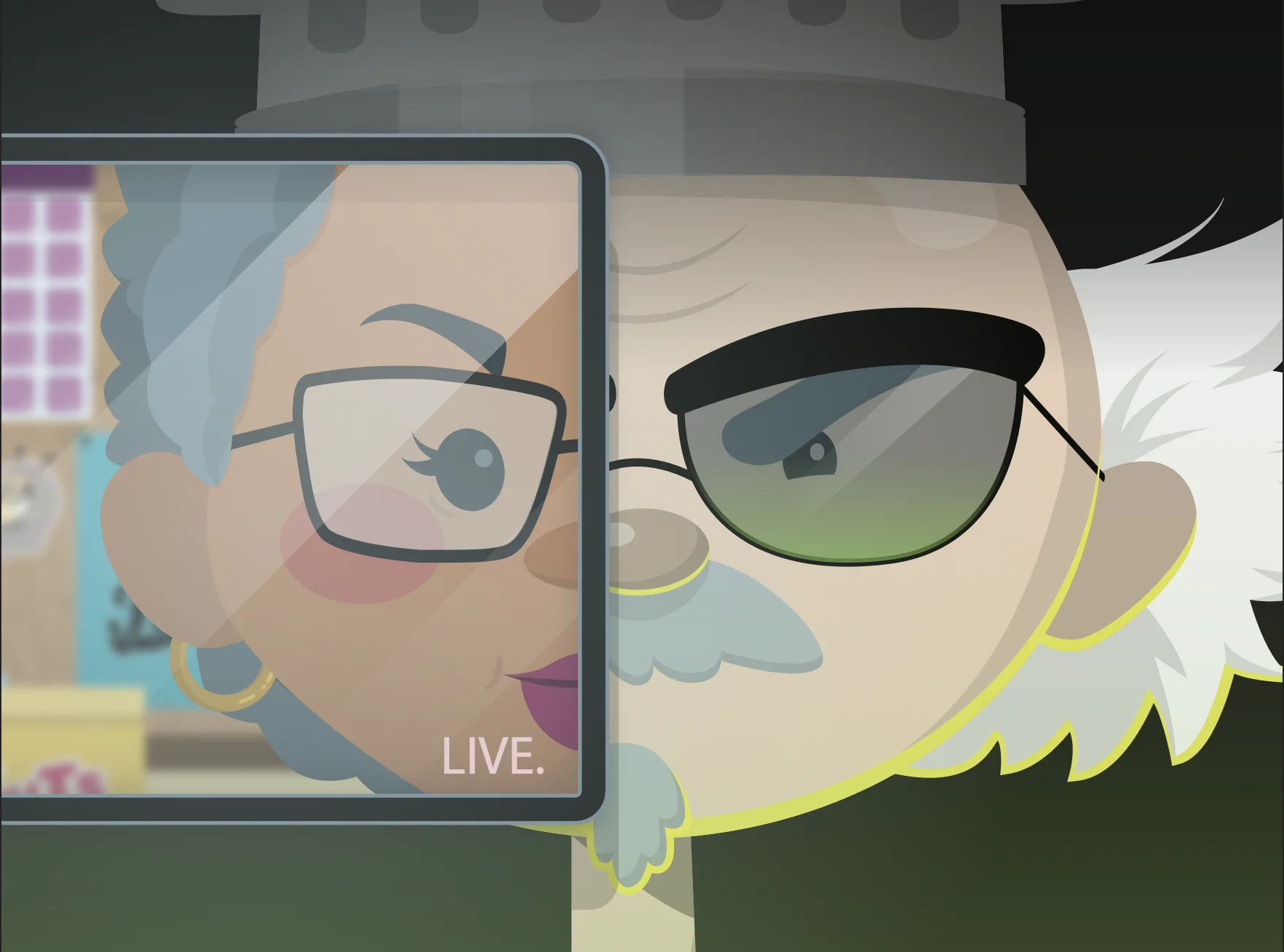
A clickfake interview is a fake job interview designed by cybercriminals to deceive targets into clicking malicious links, downloading malware, or sharing sensitive information. Think of it as a social engineering trap aimed at job seekers and companies alike.
Attackers pose as recruiters or HR reps, baiting their targets with fake interview invites. From there, they send malicious video conferencing links or files, setting the stage to do things like steal credentials, drop malware, or gather intel on the company. Sneaky, right?
Anyone can get duped, but job seekers in cybersecurity, IT, and tech are prime targets. Companies running remote interviews aren’t off the hook either. Cybercriminals capitalize on the rise of virtual hiring and weaponize urgency to catch their victims off guard. Stay sharp!
Clickfake interviews rely on fake setups to push malware or steal data.
Deepfake interviews take it next level, using AI-generated audio or visuals to impersonate someone.
Both are threats to watch out for, but clickfakes focus more on phishing tactics and interaction traps rather than advanced AI trickery.
Sketchy recruiter emails that scream "copy-paste job"
Unknown or fishy interview platforms and funky URLs
"Hey, can you download this file before we chat?" vibes
Emails riddled with typos or unprofessional language
A job pitch that doesn’t match the actual conversation
If it feels off, it probably is. Trust your gut.
Organizations, it’s time to level up your defenses. Here’s the play:
Confirm recruiter identities and interview platforms
Use security awareness training to empower your employees to sniff out phishing attempts
Equip your email and calendar tools with security fortifications
Go all-in on zero trust for remote communication tools
Being proactive beats being reactive, every time.
Absolutely. Clickfake interviews are just one piece of the growing social engineering puzzle. They can open doors to even nastier threats like phishing-as-a-service (PhaaS), credential theft, and remote access trojans (RATs). It’s an evolving attack vector, so staying vigilant is non-negotiable.