What is an APT Group?
Written by: Lizzie Danielson
Published: 8/18/2025



FAQs
APT stands for Advanced Persistent Threat. It describes well-resourced groups that use advanced tools and techniques to maintain long-term access to a target network while achieving their malicious objectives.
No, not all APT groups are backed by nation-states. Some are operated by organized cybercriminal enterprises motivated by financial gain. However, many of the most notorious APT groups, like those tied to China, Russia, and Iran, do operate with the support of state resources.
The difference lies in sophistication, persistence, and objectives. Regular hackers often focus on fast payoffs using standard tools. APT groups, on the other hand, execute complex campaigns tailored to specific targets, often with broader objectives like espionage, disruption, or theft of critical data.
Here are a few notable APT groups and their associations:
APT1 (China): Linked to espionage targeting U.S. companies.
APT28 (Russia): Tied to election interference and government data breaches.
Lazarus Group (North Korea): Connected to financial attacks like the WannaCry ransomware.
For a comprehensive database of APT groups, visit the MITRE ATT&CK Groups page, which outlines Tactics, Techniques, and Procedures (TTPs).
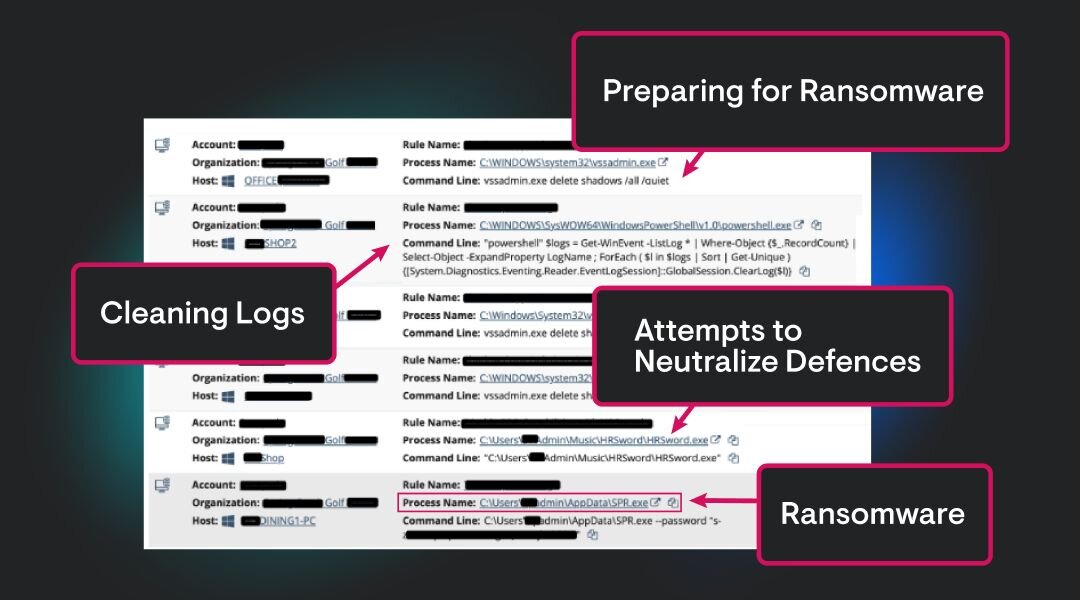
Organizations can deploy systems to monitor for:
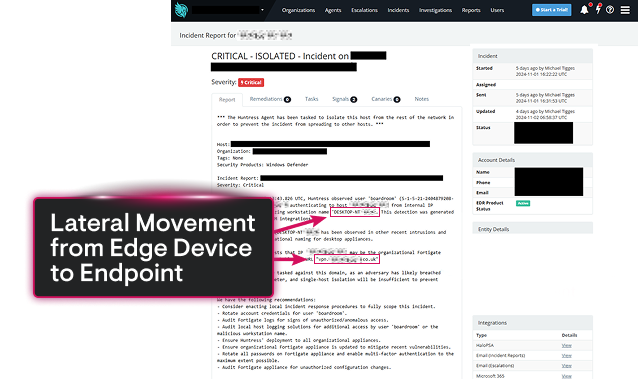
Unusual Traffic: Check activity flowing to rare or malicious domains.
Unexpected Behavior: Look for accounts accessing data they usually wouldn’t.
Endpoint Activity: Identify IoCs like unauthorized processes or connections on devices. Use frameworks like MITRE ATT&CK to map suspicious behaviors to known TTPs.
MITRE ATT&CK is a globally recognized tool that tracks APT group TTPs. It offers an extensive knowledge base to:
Map adversarial behavior.
Analyze attack patterns.
Improve detection and response strategies.
Many security teams use MITRE’s framework to model and anticipate how APT groups might act.
Absolutely. While APT groups primarily focus on high-value targets, small businesses often become collateral damage in supply chain attacks. They may also serve as initial entry points into larger networks. Small enterprises shouldn’t underestimate the need for proactive defenses.